- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
48092 Learning courses
Admin, Secretarial & PA Online Course
By Compete High
ð Unlock Your Potential with the Admin, Secretarial & PA Online Course! ð Are you ready to embark on a journey towards a rewarding career in administration, secretarial work, or personal assistance? Look no further! Our comprehensive Admin, Secretarial & PA Online Course is designed to equip you with the essential skills and knowledge needed to thrive in today's fast-paced business world. ð What to Expect: Our course covers a wide range of topics essential to excel in administrative roles. From mastering communication techniques to honing your organizational skills, you'll delve into the intricacies of office management, time management, and effective multitasking strategies. Gain proficiency in industry-standard software applications, learn the art of professional correspondence, and understand the importance of confidentiality and discretion in your role. With our engaging multimedia content, interactive quizzes, and practical exercises, you'll absorb the material effortlessly and apply your newfound knowledge with confidence. Whether you're a seasoned professional looking to refresh your skills or a newcomer to the field, our course is tailored to meet your needs and elevate your career prospects. ð Benefits of Taking the Admin, Secretarial & PA Online Course: Flexibility: Study at your own pace, from anywhere in the world, and fit your learning around your busy schedule. No need to sacrifice your current commitments - our online platform allows you to access course materials 24/7. Relevance: Stay up-to-date with the latest industry trends and best practices. Our course content is regularly updated to reflect the evolving demands of the administrative landscape, ensuring you're equipped with the most relevant skills employers are seeking. Career Advancement: Enhance your employability and unlock new career opportunities. Whether you're seeking entry-level positions or aiming for senior administrative roles, the skills acquired through our course will set you apart from the competition and open doors to advancement. Networking: Connect with like-minded professionals and industry experts through our online community. Exchange ideas, seek advice, and build valuable relationships that can propel your career forward. Increased Efficiency: Streamline your workflow and boost productivity with proven time management techniques and organizational strategies. Learn how to prioritize tasks, manage deadlines effectively, and optimize your workflow for maximum efficiency. Who is this for? ð¯ Our Admin, Secretarial & PA Online Course is perfect for: Aspiring administrative professionals seeking to kickstart their careers. Current administrative staff looking to enhance their skills and advance their careers. Individuals interested in pursuing roles in secretarial work or personal assistance. Entrepreneurs and small business owners seeking to improve their office management skills. Career Path ð£ï¸ Upon completion of our course, you'll be equipped to pursue a variety of exciting career paths, including: Administrative Assistant Executive Assistant Office Manager Personal Assistant Secretary Receptionist Virtual Assistant And more! Don't let your potential go untapped - enroll in our Admin, Secretarial & PA Online Course today and take the first step towards a fulfilling and prosperous career in administration! ð FAQ (Frequently Asked Questions) - Admin, Secretarial & PA Online Course Q1: What is the Admin, Secretarial & PA Online Course about? A1: The Admin, Secretarial & PA Online Course is a comprehensive program designed to equip individuals with the necessary skills and knowledge to excel in administrative roles, including secretarial and personal assistant positions. This course covers a wide range of topics, including office management, communication skills, time management, and organizational techniques. Participants will learn how to efficiently manage administrative tasks, handle correspondence, schedule appointments, and provide effective support to executives and teams. Q2: Who is this course suitable for? A2: This course is suitable for anyone interested in pursuing a career in administration, secretarial work, or personal assistance. Whether you're a recent graduate looking to enter the workforce or a professional seeking to enhance your skills and advance your career, this course provides valuable insights and practical techniques applicable across various industries and sectors. Additionally, entrepreneurs and small business owners can benefit from learning essential administrative skills to efficiently manage their operations. Q3: What are the key benefits of taking this online course? A3: By enrolling in the Admin, Secretarial & PA Online Course, participants can expect to gain a comprehensive understanding of administrative principles and practices. Some key benefits include: Acquiring essential skills in office management, communication, and organization. Learning effective time management techniques to optimize productivity. Developing proficiency in handling administrative tasks such as correspondence, scheduling, and document management. Enhancing interpersonal skills for effective communication with colleagues, clients, and stakeholders. Increasing employability and career advancement opportunities in administrative roles across various industries. Q4: How is the course structured, and what learning materials are provided? A4: The course is structured into modules, each focusing on specific aspects of administration, secretarial duties, and personal assistance. Participants will have access to comprehensive learning materials, including video lectures, reading materials, practical exercises, and quizzes. Additionally, interactive elements such as discussion forums and case studies are incorporated to facilitate engagement and application of knowledge. Learners can progress at their own pace, with flexibility to accommodate individual schedules and learning preferences. Q5: Is there any prerequisite for enrolling in this course? A5: No specific prerequisites are required for enrollment in the Admin, Secretarial & PA Online Course. This program is designed to cater to individuals with varying levels of experience and educational backgrounds. Whether you're a beginner seeking to enter the field of administration or an experienced professional looking to refine your skills, this course offers valuable insights and practical knowledge to support your career goals. Course Curriculum Module 1-Overview for the New Administrative Assistant Overview for the New Administrative Assistant 00:00 Module 2-Daily Routine Daily Routine 00:00 Module 3-Telephone Usage Telephone Usage 00:00 Module 4-Meetings Meetings 00:00 Module 5-Keeping Accurate Records Keeping Accurate Records 00:00 Module 6- Office Equipment Office Equipment 00:00

Ultimate Facial Training
By Compete High
ð Unlock the secrets to radiant, flawless skin with our groundbreaking course: Ultimate Facial Training! ð Are you ready to embark on a journey towards mastering the art of skincare and facial treatments? Look no further! Our comprehensive course is designed to equip you with the skills and knowledge needed to become a proficient skincare specialist. Whether you're a seasoned esthetician looking to enhance your expertise or a budding enthusiast eager to delve into the world of facial therapy, this course is tailor-made for you! ð©âð Why Choose Ultimate Facial Training? Enrolling in our Ultimate Facial Training course offers a plethora of benefits that will propel your career in the skincare industry to new heights. Here's what you can expect: Expert Guidance: Learn from industry professionals with years of experience in skincare and facial therapy. Our instructors are passionate about sharing their knowledge and will provide you with invaluable insights every step of the way. Hands-On Experience: Get hands-on experience with state-of-the-art equipment and techniques used in professional skincare clinics. Practice your skills in a supportive environment under the guidance of our seasoned instructors. Comprehensive Curriculum: Our curriculum covers everything from the fundamentals of skincare to advanced facial treatments. Whether you're interested in basic facials, chemical peels, or microdermabrasion, we've got you covered! Flexible Learning Options: We understand that everyone has different schedules and commitments. That's why we offer flexible learning options, including online courses and in-person workshops, so you can learn at your own pace. Career Advancement: Upon completion of the course, you'll be armed with the skills and certification needed to pursue exciting career opportunities in the skincare industry. Whether you dream of working in a high-end spa, medical clinic, or starting your own skincare business, the possibilities are endless! ð©âð¼ Who is this for? Ultimate Facial Training is perfect for: Estheticians looking to expand their skill set Beauty enthusiasts eager to learn the art of skincare Individuals considering a career change into the booming skincare industry No matter your background or experience level, our course is designed to accommodate learners of all levels and backgrounds. ð Career Path Upon completing Ultimate Facial Training, you'll be well-equipped to pursue various exciting career paths, including: Licensed Esthetician: Become a licensed esthetician and work in a spa, salon, or skincare clinic, providing a wide range of facial treatments to clients. Skincare Specialist: Specialize in skincare treatments and offer personalized skincare solutions to clients based on their individual needs and concerns. Entrepreneur: Launch your own skincare business and offer facial treatments, skincare products, and consulting services to clients in your community. Medical Aesthetician: Work alongside dermatologists and plastic surgeons to provide advanced skincare treatments in medical settings, such as dermatology clinics or cosmetic surgery centers. Don't miss out on this incredible opportunity to kickstart your career in the lucrative skincare industry! Enroll in Ultimate Facial Training today and take the first step towards becoming a skincare expert. Your journey to radiant, glowing skin starts here! ⨠ð Frequently Asked Questions (FAQs) ð 1. Is Ultimate Facial Training suitable for beginners? Absolutely! Ultimate Facial Training is designed to accommodate learners of all levels, from beginners to experienced estheticians. Our comprehensive curriculum covers the fundamentals of skincare, making it perfect for those who are new to the field. 2. How long does it take to complete the course? The duration of Ultimate Facial Training varies depending on the learning option you choose and your individual pace. Our online courses typically range from a few weeks to several months, while in-person workshops may span over a weekend or several days. 3. Will I receive a certification upon completion of the course? Yes, upon successfully completing Ultimate Facial Training, you will receive a certification that demonstrates your proficiency in skincare and facial treatments. This certification will enhance your credibility and open up exciting career opportunities in the skincare industry. 4. Can I enroll in Ultimate Facial Training if I'm already a licensed esthetician? Absolutely! Many licensed estheticians choose to enroll in Ultimate Facial Training to expand their skill set and stay up-to-date with the latest trends and techniques in skincare. Our course offers advanced modules that cater to experienced professionals looking to enhance their expertise. 5. Are there any prerequisites for enrolling in Ultimate Facial Training? There are no specific prerequisites for enrolling in Ultimate Facial Training. Whether you're a complete novice or have some experience in skincare, you're welcome to join our course and embark on your journey towards mastering the art of facial treatments. 6. Can I access course materials after completing the training? Yes, upon completing Ultimate Facial Training, you will have access to course materials and resources to review and reinforce your learning. We believe in supporting our students even after they've completed the course to ensure their continued success in the skincare industry. 7. What sets Ultimate Facial Training apart from other skincare courses? Ultimate Facial Training stands out for its comprehensive curriculum, expert instructors, hands-on learning experience, and flexible learning options. Our goal is to provide students with the knowledge, skills, and confidence they need to excel in the skincare industry and pursue rewarding career opportunities. Don't hesitate to reach out if you have any further questions or concerns. We're here to support you on your journey towards becoming a skincare expert! ⨠Course Curriculum Module 1_ Introduction to Facial Anatomy and Muscles. Introduction to Facial Anatomy and Muscles. 00:00 Module 2_ Facial Exercises for Anti-Aging and Relaxation. Facial Exercises for Anti-Aging and Relaxation. 00:00 Module 3_ Facial Exercises for Toning and Lifting. Facial Exercises for Toning and Lifting. 00:00 Module 4_ Facial Yoga. Facial Yoga. 00:00 Module 5_ Facial Massage and Acupressure. Facial Massage and Acupressure. 00:00

Primary Teaching Training
By Compete High
ð Welcome to the gateway to your dream career in education! Introducing our groundbreaking course: 'Primary Teaching Training' - your ultimate ticket to becoming a proficient and empowered primary school educator. ð In today's competitive educational landscape, acquiring the right skills and knowledge is essential for anyone aspiring to make a significant impact in the lives of young learners. Our comprehensive training program is meticulously designed to equip you with the essential tools, techniques, and insights needed to excel in the dynamic world of primary education. ð¼ ð Benefits of Primary Teaching Training Course: Expert Guidance: Learn from seasoned educators who bring years of experience to the table, offering valuable insights and practical advice. Cutting-edge Strategies: Stay ahead of the curve with the latest teaching methodologies and innovative approaches to classroom management and student engagement. Hands-on Experience: Put theory into practice with immersive teaching practicums and real-world classroom simulations, honing your skills in a supportive environment. Personalized Support: Receive individualized feedback and guidance tailored to your unique strengths and areas for growth, ensuring maximum development and confidence. Networking Opportunities: Connect with fellow aspiring educators, mentors, and industry professionals, building a strong support network for your future career endeavors. Credential Enhancement: Boost your resume and professional credibility with a recognized certification in primary teaching, opening doors to diverse career opportunities. Lifelong Learning: Cultivate a passion for continuous professional development, equipping yourself with the skills and knowledge needed to thrive in an ever-evolving educational landscape. ð©âð« Who is this for? This course is perfect for aspiring primary school teachers who are passionate about making a positive impact on young minds. Whether you're a recent graduate looking to kickstart your career in education or a career changer seeking a fulfilling vocation, our training program provides the ideal foundation for success. Additionally, this course is suitable for current educators seeking to enhance their teaching skills or transition into primary education from other educational levels. ð¤ï¸ Career Path Upon completion of our Primary Teaching Training course, you'll be equipped with the knowledge, skills, and confidence to embark on a rewarding career journey in primary education. Your career path may include roles such as: Primary School Teacher: Take on the role of an inspiring educator, shaping the minds of young learners and fostering their academic, social, and emotional development. Special Education Teacher: Make a difference in the lives of students with diverse learning needs, providing tailored support and guidance to help them reach their full potential. Curriculum Developer: Contribute to the design and implementation of effective teaching strategies and educational programs, ensuring optimal learning outcomes for students. Educational Consultant: Share your expertise with schools, educational organizations, and policymakers, providing valuable insights and recommendations to enhance teaching and learning practices. School Administrator: Pursue leadership roles such as principal or vice-principal, overseeing the daily operations of a primary school and fostering a positive learning environment for students and staff alike. Don't let your dreams of becoming a successful primary school teacher remain just dreams. Enroll in our Primary Teaching Training course today and take the first step towards a fulfilling and impactful career in education! ðð ð Frequently Asked Questions (FAQs) Q: Is prior teaching experience required to enroll in the Primary Teaching Training course? A: No, prior teaching experience is not mandatory. Our course is designed to cater to individuals at various stages of their teaching journey, from beginners to experienced educators seeking to enhance their skills or transition into primary education. Q: What qualifications do I need to participate in the course? A: While specific qualifications may vary depending on the institution offering the course, most programs require a minimum of a high school diploma or equivalent. Some programs may also have additional requirements such as proficiency in certain subjects or passing an entrance exam. Q: How long does the Primary Teaching Training course typically last? A: The duration of the course can vary depending on factors such as the program structure, delivery format (full-time, part-time, online), and any additional requirements such as practicum hours. On average, however, most courses range from several months to a year in duration. Q: Can I work while taking the course? A: It depends on the program's flexibility and your personal schedule. Many courses offer part-time or online options to accommodate working professionals. However, it's essential to consider the time commitment required for coursework, assignments, and practicum experiences to ensure a manageable balance between work and study. Q: Will I receive a certification upon completion of the course? A: Yes, upon successfully completing the Primary Teaching Training course, you will typically receive a certification or diploma indicating your achievement. This credential demonstrates your commitment to professional development and may enhance your prospects for employment in the field of primary education. Q: Are there opportunities for financial aid or scholarships? A: Some institutions offering the Primary Teaching Training course may provide financial aid options such as scholarships, grants, or tuition assistance programs. It's recommended to research and inquire about available financial aid opportunities directly with the institution or through external sources such as government agencies or private foundations. Q: What support services are available to students during the course? A: Most programs offer a range of support services to students, including academic advising, tutoring, counseling, and access to resources such as libraries, online databases, and professional development workshops. Additionally, instructors and mentors are typically available to provide guidance and support throughout your learning journey. Course Curriculum Module 1_ Introduction to Primary Teaching. Introduction to Primary Teaching. 00:00 Module 2_ Child Development and Psychology. Child Development and Psychology. 00:00 Module 3_ Planning and Assessment. Planning and Assessment. 00:00 Module 4_ Classroom Management and Behaviour. Classroom Management and Behaviour. 00:00 Module 5_ Literacy Development. Literacy Development. 00:00

Artisan Pastries and Deserts for Beginners Course
By Xpert Learning
About Course The Ideal Pastry Baking Course to Start Mastering Desserts - Bake Chocolate Brownies, Doughnuts, Tart Pastries & More Learn the art of baking delicious pastries and desserts with this comprehensive course taught by French Artisan Baker Marceau Dauboin. This course is perfect for beginners of all skill levels, and covers everything you need to know to get started, from the basics of baking to more advanced techniques. You will learn how to make a variety of classic pastries and desserts, including: Chocolate Brownies Apple Tart (Pâte Sablée) Doughnuts (Chocolate & Cinnamon) Stroopwafels Cinnamon Rolls Tarte Tatin (Puff Pastry) All recipes can be made with either traditional rising agents or your own sourdough starter, which you will learn how to make from scratch. The course also includes a free e-book containing all of the pastry recipes, ingredients, and instructions for quick and easy reference. All baking temperatures and measurements are provided in both metric and imperial units. Whether you are a complete beginner or simply want to improve your baking skills, this course is the perfect way to learn how to make delicious pastries and desserts at home. Enroll today and start your baking journey! Target Audience: Beginners of all skill levels who are interested in learning how to bake delicious pastries and desserts Benefits: Learn from a French Artisan Baker with over 900 successful students Learn both traditional and sourdough baking techniques Receive a free e-book containing all of the pastry recipes, ingredients, and instructions All baking temperatures and measurements are provided in both metric and imperial units Enroll today and start your baking journey! What Will You Learn? How to bake your favorite Pastries & Desserts from the comfort of your own home How to easily create and maintain a powerful Sourdough Starter completely from scratch Learn & Master how to use Sourdough Starter in Pastry & Desserts The techniques used to develop Perfect Tart Baking Success Chocolate Brownies - Apple Tart - Doughnuts Stroopwafels - Cinnamon Rolls - Tarte Tatin Course Content Course Introduction Course Introduction Sourdough Starter Introduction Make Your Sourdough Starter From Scratch Chocolate Brownies Chocolate Brownie - Introduction Chocolate Brownie - Melting Chocolate _ Butter Chocolate Brownie - Batter Mix Chocolate Brownie - Bake Your Brownies Chocolate Brownie - Conclusion Apple Tart - Pâte Sablée Apple Tart - Introduction Apple Tart - Pate Sablee Dough Mix Apple Tart - Bake Your Pate Sablee Apple Tart - Peeling _ Cutting your Apples Apple Tart - Creating your Puree Apple Tart - Preparing your Apple Slices Apple Tart - Tarte Assembly Apple Tart - Bake Your Tart Apple Tart - Apple Tart Conclusion Doughnuts - Chocolate & Cinnamon Doughnuts - Introduction Doughnuts - Doughnut Dough Mix Doughnuts - Stretch _ Folds Doughnuts - Doughnut Dough Preparation Doughnuts - Fry Your Doughnuts Doughnuts - Doughnut Toppings Doughnuts - Artisan Doughnut Conclusion Stroopwafels Stroopwafel - Introduction Stroopwafel - Stroopwafel Dough Mix Stroopwafel - Stretch _ Folds Stroopwafel - Shape Your Waffles Stroopwafel - Cooking your Waffles Stroopwafel - Lets make Syrup! Stroopwafel - Stroopwafel assembly _ Conclusion Cinnamon Rolls Cinnamon Roll - Introduction Cinnamon Roll - Cinnamon Roll Dough Mix Cinnamon Roll - Stretch _ Folds Cinnamon Roll - Cinnamon Roll Dough Preparation Cinnamon Rolls - Prepare Your Icing Cinnamon Rolls - Bake Your Cinnamon Rolls Conclusion Tarte Tatin - Puff Pastry Tarte Tatin - Introduction Tarte Tatin - Puff Pastry Dough Mix Tarte Tatin - Stretch _ Folds Tarte Tatin - Dough Shaping Tarte Tatin - Create a Beurrage Tarte Tatin - Dough _ Butter Folds Tarte Tatin - Peeling _ Cutting your Apples Tarte Tatin - Making Your Caramel Tarte Tatin - Bake Your Tart Tarte Tatin - Tarte Tatin Conclusion Bonus Section: Sourdough & Beyond! Pastry _ Desserts Course Conclusion A course by Marceau Dauboin RequirementsAccess to Baking Ingredients & KitchenwareAccess to an Oven & FridgeAccess to a Clean Work Surface Audience Complete beginners looking to take their first steps in their Artisan Baking Journey Sourdough enthusiasts looking to discover exciting new recipes Intermediate bakers looking to explore pastries & desserts Audience Complete beginners looking to take their first steps in their Artisan Baking Journey Sourdough enthusiasts looking to discover exciting new recipes Intermediate bakers looking to explore pastries & desserts

ChatGPT for Marketing and Productivity with AI Tools
By IOMH - Institute of Mental Health
Overview of ChatGPT for Marketing and Productivity with AI Tools Visualise a world where artificial intelligence drives your marketing initiatives and AI tools revolutionise your business productivity. That's no longer just a fantasy; it's a reality you can be part of with our ChatGPT for Marketing and Productivity with AI Tools course. This industry has witnessed an explosion of opportunities, where those equipped with the knowledge to harness the power of artificial intelligence in marketing and productivity are at a significant advantage. Join us and become well-versed in using ChatGPT, one of the most sophisticated AI tools available. Learn how to seamlessly integrate Artificial Intelligence (AI) into your marketing strategies and enhance your productivity using AI tools. With this course, you are following the trend and becoming a trendsetter in the Artificial Intelligence (AI) marketing and productivity landscape. Join us and leap into the future with ChatGPT. This ChatGPT for Marketing and Productivity with AI Tools Course will help you to learn: Learn strategies to boost your workplace efficiency. Hone your skills to help you advance your career. Acquire a comprehensive understanding of various topics and tips. Learn in-demand skills that are in high demand among UK employers This course covers the topic you must know to stand against the tough competition. The future is truly yours to seize with this ChatGPT for Marketing and Productivity with AI Tools. Enrol today and complete the course to achieve a certificate that can change your career forever. Details Perks of Learning with IOMH One-To-One Support from a Dedicated Tutor Throughout Your Course. Study Online - Whenever and Wherever You Want. Instant Digital/ PDF Certificate. 100% Money Back Guarantee. 12 Months Access. Process of Evaluation After studying the course, an MCQ exam or assignment will test your skills and knowledge. You have to get a score of 60% to pass the test and get your certificate. Certificate of Achievement Certificate of Completion - Digital / PDF Certificate After completing the ChatGPT for Marketing and Productivity with AI Tools course, you can order your CPD Accredited Digital / PDF Certificate for £5.99. Certificate of Completion - Hard copy Certificate You can get the CPD Accredited Hard Copy Certificate for £12.99. Shipping Charges: Inside the UK: £3.99 International: £10.99 Who Is This Course for? This ChatGPT for Marketing and Productivity with AI Tools is suitable for anyone aspiring to start a career in relevant field; even if you are new to this and have no prior knowledge, this course is going to be very easy for you to understand. On the other hand, if you are already working in this sector, this course will be a great source of knowledge for you to improve your existing skills and take them to the next level. This course has been developed with maximum flexibility and accessibility, making it ideal for people who don't have the time to devote to traditional education. Requirements There is no prerequisite to enrol in this course. You don't need any educational qualification or experience to enrol in the ChatGPT for Marketing and Productivity with AI Tools course. Do note: you must be at least 16 years old to enrol. Any internet-connected device, such as a computer, tablet, or smartphone, can access this online course. Career Path The certification and skills you get from this ChatGPT for Marketing and Productivity with AI Tools Course can help you advance your career and gain expertise in several fields, allowing you to apply for high-paying jobs in related sectors. Course Curriculum Section 01: The AI Marketing Playbook Unit 01: Start an Account with ChatGPT 00:02:00 Unit 02: What the Company OpenAI Say About Itself 00:02:00 Unit 03: What OpenAI Say About The Limitations of the Chatbot 00:02:00 Unit 04: Chatbot Prompt Examples Given By Open AI 00:02:00 Unit 05: Will Chat GPT Be a Paid Application 00:01:00 Unit 06: Chat GPT Idea Generation 00:02:00 Unit 07: Chat GPT - Idea Qualification and Accuracy 00:03:00 Unit 08: ChatGPT - Accuracy and Citations 00:02:00 Unit 09: Chat GPT - Creating HTML Instances 00:01:00 Unit 10: Chat GPT - How to Solve Specific Business Problems 00:02:00 Unit 11: Chat GPT - Statistical Verification of Information 00:01:00 Unit 12: Chat GPT - Rewrite Content for Different Contexts 00:02:00 Unit 13: ChatGPT - Content Checked With AI 00:02:00 Unit 14: ChatGPT - Simplifying Information 00:01:00 Unit 15: ChatGPT - How to Ask the Chatbot about Context 00:01:00 Unit 16: ChatGPT - How to Cross-Post Queries 00:01:00 Unit 17: ChatGPT - How to Narrow Down the Context of Your Query 00:02:00 Unit 18: ChatGPT - How to Solve a Business Process 00:02:00 Unit 19: ChatGPT - Developing a Methodology From Experts 00:01:00 Unit 20: The Future of ChatGPT 00:01:00 Section 02: How to Use ChatGPT and AI for Marketing Unit 01: Autonous AI Agents 00:01:00 Unit 02: Connecting to Open AI 00:01:00 Unit 03: Getting an OpenAI Key 00:01:00 Unit 04: Agent GPT - Autonomous AI 00:02:00 Unit 05: GoalGPT - Autonomous Agents 00:01:00 Unit 06: Cognosis - Autonomous AI 00:02:00 Unit 07: Aomni - Autonomous Agent 00:01:00 Unit 08: Durable - Build a Website with AI 00:01:00 Unit 09: Eightify Summaries 00:02:00 Unit 10: Genei - Do Higher Quality Research with AI 00:01:00 Unit 11: Ellicit - Do Higher Quality Research with AI 00:01:00 Unit 12: Inciteful - Do Higher Quality Research with AI 00:02:00 Unit 13: SciteAI Determine the Credibility of Your Research 00:01:00 Unit 14: Eleven Labs - Voice Cloning 00:02:00 Unit 15: AgentGPT - Wrap Up and Return 00:01:00 Unit 16: Cognosys - Wrap Up and Return 00:01:00 Unit 17: Aomni - Wrap Up and Return 00:01:00 Unit 18: Goal GPT - Wrap Up and Return 00:01:00 Unit 19: Uploading Research Reports to Summarization Applications 00:01:00 Unit 20: Perspective on The Future of AI 00:01:00 Section 03: Productivity with AI Tools Unit 01: Meta Search Sites 00:02:00 Unit 02: SMMRY for Summarzing 00:01:00 Unit 03: ChatGPT Plugins Waitlist 00:01:00 Unit 04: Using Microsoft Bing Search 00:02:00 Unit 04: Using Microsoft Bing Search 00:02:00 Unit 06: Microsoft Word Speech To Text 00:01:00 Unit 07: Transcribe Audio in Microsoft Word 00:02:00 Unit 08: Speechify 00:02:00 Unit 09: Exact Image Creation 00:01:00 Unit 10: AI Design Tools 00:02:00 Unit 11: Learn How to Prompt 00:01:00 Unit 12: Content Improvement 00:01:00 Unit 13: Idea Generation 00:01:00 Unit 14: Audio Enhancement with Adobe 00:02:00 Unit 15: Clean up Audio With Cleaanvoice 00:01:00 Unit 16: Notion-AI 00:01:00 Unit 17: Pictory 00:01:00 Unit 18: Lex 00:01:00 Unit 19: ChatPDF 00:01:00 Unit 20: Conclusion and the Future of Generatie AI - Searchie 00:01:00

Addiction and Mental Health - Dual Diagnosis
By IOMH - Institute of Mental Health
Overview of Addiction and Mental Health - Dual Diagnosis Join our Addiction and Mental Health - Dual Diagnosis course and discover your hidden skills, setting you on a path to success in this area. Get ready to improve your skills and achieve your biggest goals. The Addiction and Mental Health - Dual Diagnosis course has everything you need to get a great start in this sector. Improving and moving forward is key to getting ahead personally. The Addiction and Mental Health - Dual Diagnosis course is designed to teach you the important stuff quickly and well, helping you to get off to a great start in the field. So, what are you looking for? Enrol now! This Addiction and Mental Health - Dual Diagnosis Course will help you to learn: Learn strategies to boost your workplace efficiency. Hone your skills to help you advance your career. Acquire a comprehensive understanding of various topics and tips. Learn in-demand skills that are in high demand among UK employers This course covers the topic you must know to stand against the tough competition. The future is truly yours to seize with this Addiction and Mental Health - Dual Diagnosis. Enrol today and complete the course to achieve a certificate that can change your career forever. Details Perks of Learning with IOMH One-To-One Support from a Dedicated Tutor Throughout Your Course. Study Online - Whenever and Wherever You Want. Instant Digital/ PDF Certificate. 100% Money Back Guarantee. 12 Months Access. Process of Evaluation After studying the course, an MCQ exam or assignment will test your skills and knowledge. You have to get a score of 60% to pass the test and get your certificate. Certificate of Achievement Certificate of Completion - Digital / PDF Certificate After completing the Addiction and Mental Health - Dual Diagnosis course, you can order your CPD Accredited Digital / PDF Certificate for £5.99. Certificate of Completion - Hard copy Certificate You can get the CPD Accredited Hard Copy Certificate for £12.99. Shipping Charges: Inside the UK: £3.99 International: £10.99 Who Is This Course for? This Addiction and Mental Health - Dual Diagnosis is suitable for anyone aspiring to start a career in relevant field; even if you are new to this and have no prior knowledge, this course is going to be very easy for you to understand. On the other hand, if you are already working in this sector, this course will be a great source of knowledge for you to improve your existing skills and take them to the next level. This course has been developed with maximum flexibility and accessibility, making it ideal for people who don't have the time to devote to traditional education. Requirements There is no prerequisite to enrol in this course. You don't need any educational qualification or experience to enrol in the Addiction and Mental Health - Dual Diagnosis course. Do note: you must be at least 16 years old to enrol. Any internet-connected device, such as a computer, tablet, or smartphone, can access this online course. Career Path The certification and skills you get from this Addiction and Mental Health - Dual Diagnosis Course can help you advance your career and gain expertise in several fields, allowing you to apply for high-paying jobs in related sectors. Course Curriculum Promotional Video Promotional 5 minute video 00:06:00 SAMHI Dual Diagnosis Intro video SAMHI Dual Diagnosis Intro video and downloadable worksheet PowerPoint slides 00:04:00 Module 1 - Drugs and Effects Module 1 - Drugs and Effects: VIDEO PART 1 (content part 1 - 4) 00:16:00 Module 1 - Drugs and Effects: VIDEO PART 2 (content part 5 - 6) 00:19:00 Module 1 - Drugs and Effects: VIDEO PART 3 (content part 7 - 8) 00:20:00 Module 1 - Drugs and Effects: VIDEO PART 4 (content part 9) 00:15:00 Module 1 - Drugs and Effects: VIDEO PART 5 (content part 10) 00:10:00 Module 1 - Drugs and Effects: VIDEO PART 6 (content 10 - 12) 00:18:00 Module 1 - Drugs and Effects: VIDEO PART 7 (content part 13) 00:13:00 Module 1 - Drugs and Effects: VIDEO PART 8 (content part 14) 00:20:00 Module 1 - Drugs and Effects: VIDEO PART 9 (content part 14) 00:20:00 Module 1 - Drugs and Effects: VIDEO PART 10 (content part 15 - 18) 00:19:00 Module 2 - Addictions & Mental Health Module 2 Addictions & Mental Health: VIDEO PART 1 content part 1 - 2 00:16:00 Module 2 Addictions & Mental Health: VIDEO PART 2 content part 3 - 5 00:18:00 Module 2 Addictions & Mental Health: VIDEO PART 3 content part 6 - 7 00:13:00 Module 2 Addictions & Mental Health: VIDEO PART 4 content part 00:17:00 Module 2 Addictions & Mental Health: VIDEO PART 5 content part 00:18:00 Module 2 Addictions & Mental Health: VIDEO PART 6 content part 00:20:00 Module 2 Addictions & Mental Health: VIDEO PART 7 content part 00:14:00 Module 2 Addictions & Mental Health: VIDEO PART 8 content part 00:12:00 Module 2 Addictions & Mental Health: VIDEO PART 9 content part 00:20:00 Module 2 Addictions & Mental Health: VIDEO PART 10 content part 00:13:00 Module 3 - Harm Minimisation & Optimal Health Module 3 Harm Minimisation & Optimal Health VIDEO PART 1 content part 00:23:00 Module 3 Harm Minimisation & Optimal Health VIDEO PART 2 content part 00:17:00 Module 3 Harm Minimisation & Optimal Health VIDEO PART 3 content part 00:09:00 Module 3 Harm Minimisation & Optimal Health VIDEO PART 4 content part 00:18:00 Module 3 Harm Minimisation & Optimal Health VIDEO PART 5 content part 00:17:00 Module 3 Harm Minimisation & Optimal Health VIDEO PART 1 content part 6 00:11:00 Module 3 Harm Minimisation & Optimal Health VIDEO PART 7 content part 7 00:12:00 Module 4 - Brain Works - Neurophysiology Module 4 Brain Works - Neurophysiology 00:17:00 Module 4 Brain Works - Neurophysiology VIDEO PART 1 content part 00:10:00 Module 4 Brain Works - Neurophysiology VIDEO PART 2 content part 00:17:00 Module 4 Brain Works - Neurophysiology VIDEO PART 3 content part 00:19:00 Module 4 Brain Works - Neurophysiology VIDEO PART 4 content part 00:16:00 Module 4 Brain Works - Neurophysiology VIDEO PART 5 content part 00:11:00 Module 5 - Trauma Model & Keys to Treatment Module 5 Trauma Model & Keys to Treatment VIDEO PART 1 content part 1 - 2a - 2f 00:20:00 Module 5 Trauma Model & Keys to Treatment VIDEO PART 2 content part 2g 00:15:00 Module 5 Trauma Model & Keys to Treatment VIDEO PART 3 content part 2h - 2i 00:15:00 Module 5 Trauma Model & Keys to Treatment VIDEO PART 4 content part 3 00:13:00 Module 5 Trauma Model & Keys to Treatment VIDEO PART 5 content part 4 00:12:00 Module 5 Trauma Model & Keys to Treatment VIDEO PART 6 content part 5 - 7 00:18:00 Module 5 Trauma Model & Keys to Treatment VIDEO PART 7 content part 8 00:17:00 Module 5 Trauma Model & Keys to Treatment VIDEO PART 7 content partVIDEO PART 8 00:16:00 Module 5 Trauma Model & Keys to Treatment VIDEO PART 9 content part 11 00:16:00 Module 5 Trauma Model & Keys to Treatment VIDEO PART 10 content part 12 00:19:00 Module 6 - Brief & Early Intervention and Tripod of Support Module 6 Brief & Early Intervention and Tripod of Support VIDEO 1 content part 1 00:18:00 Module 6 Brief & Early Intervention and Tripod of Support VIDEO 2 content part 2 00:20:00 Resources - Addiction & Mental Health (Dual Diagnosis) Integrative 12hrs Resources - Addiction & Mental Health (Dual Diagnosis) Integrative 12hrs 00:00:00

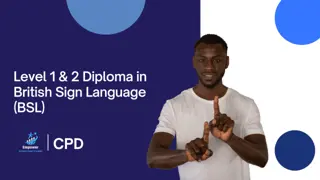
Level 1 & 2 Diploma in British Sign Language (BSL) - CPD Certified
5.0(1)By Empower UK Employment Training
Expand your communication skills with our British Sign Language Level 2 course. Dive deeper into BSL with advanced fingerspelling, personal information exchange, and specialized topics like family, weather, and transport. Embrace inclusivity and enhance your linguistic abilities now.
Pre-Primary Ballet
By M & L School of Performing Arts
Every Saturday at 11:10 – 11:55 Step into the enchanting world of our Pre-Primary syllabi, where the dance floor becomes a canvas for young imaginations to soar. This carefully curated program is designed to sculpt the physical prowess, endurance, creative flair, expressive power, and musical sensitivity of our students, all set to the rhythm of captivating musical styles and sounds. It’s here that the foundational steps of ballet blend with the joy of exploration, creating a nurturing yet exhilarating learning atmosphere. Crafted with love, each exercise is a melody of gentle movements, guiding little dancers through the basics of ballet technique within a realm of creativity and play. Our classrooms are alive with a kaleidoscope of props, each playing its part in enriching the learning experience across all dimensions. From the whisper of a scarf in motion to the soft thud of a rhythmic beanbag, every prop tells a story, unlocking new dimensions of movement and imagination. Beyond the steps and stretches, our class holds a treasure trove of opportunities, including the chance for our young dancers to shine in class awards. It’s an invitation to step into the spotlight, not just to showcase their budding talents but to celebrate their journey in dance, expression, and self-discovery. Join us in this magical adventure, where every plié and pirouette is a step towards creating artful expressions, lifelong memories, and a deep-seated love for the beautiful world of ballet. Book first lesson here: https://mandlschoolofperformingarts.com/book-first-lesson/

Search By Location
- Learning Courses in London
- Learning Courses in Birmingham
- Learning Courses in Glasgow
- Learning Courses in Liverpool
- Learning Courses in Bristol
- Learning Courses in Manchester
- Learning Courses in Sheffield
- Learning Courses in Leeds
- Learning Courses in Edinburgh
- Learning Courses in Leicester
- Learning Courses in Coventry
- Learning Courses in Bradford
- Learning Courses in Cardiff
- Learning Courses in Belfast
- Learning Courses in Nottingham

