- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
19502 Health courses
Build Up Good Habits
By Compete High
Overview With the ever-increasing demand for Build Up Good Habits in personal & professional settings, this online training aims at educating, nurturing, and upskilling individuals to stay ahead of the curve - whatever their level of expertise in Build Up Good Habits may be. Learning about Build Up Good Habits or keeping up to date on it can be confusing at times, and maybe even daunting! But that's not the case with this course from Compete High. We understand the different requirements coming with a wide variety of demographics looking to get skilled in Build Up Good Habits. That's why we've developed this online training in a way that caters to learners with different goals in mind. The course materials are prepared with consultation from the experts of this field and all the information on Build Up Good Habits is kept up to date on a regular basis so that learners don't get left behind on the current trends/updates. The self-paced online learning methodology by compete high in this Build Up Good Habits course helps you learn whenever or however you wish, keeping in mind the busy schedule or possible inconveniences that come with physical classes. The easy-to-grasp, bite-sized lessons are proven to be most effective in memorising and learning the lessons by heart. On top of that, you have the opportunity to receive a certificate after successfully completing the course! Instead of searching for hours, enrol right away on this Build Up Good Habits course from Compete High and accelerate your career in the right path with expert-outlined lessons and a guarantee of success in the long run. Who is this course for? While we refrain from discouraging anyone wanting to do this Build Up Good Habits course or impose any sort of restrictions on doing this online training, people meeting any of the following criteria will benefit the most from it: Anyone looking for the basics of Build Up Good Habits, Jobseekers in the relevant domains, Anyone with a ground knowledge/intermediate expertise in Build Up Good Habits, Anyone looking for a certificate of completion on doing an online training on this topic, Students of Build Up Good Habits, or anyone with an academic knowledge gap to bridge, Anyone with a general interest/curiosity Career Path This Build Up Good Habits course smoothens the way up your career ladder with all the relevant information, skills, and online certificate of achievements. After successfully completing the course, you can expect to move one significant step closer to achieving your professional goals - whether it's securing that job you desire, getting the promotion you deserve, or setting up that business of your dreams. Course Curriculum Module 01 - Understanding Self Journal Understanding Self Journal 00:00 Module 02 - Setting SMART Goals Setting SMART Goals 00:00 Module 03 - Small but Mighty Changes Small but Mighty Changes 00:00 Module 04 - Cooking and Meal Plan Cooking and Meal Plan 00:00 Module 05 - Mind and Body Mind and Body 00:00 Module 06 - Exercise Exercise 00:00

High Ticket Sales Training
By Compete High
Overview With the ever-increasing demand for High Ticket Sales Training in personal & professional settings, this online training aims at educating, nurturing, and upskilling individuals to stay ahead of the curve - whatever their level of expertise in High Ticket Sales Training may be. Learning about High Ticket Sales Training or keeping up to date on it can be confusing at times, and maybe even daunting! But that's not the case with this course from Compete High. We understand the different requirements coming with a wide variety of demographics looking to get skilled in High Ticket Sales Training . That's why we've developed this online training in a way that caters to learners with different goals in mind. The course materials are prepared with consultation from the experts of this field and all the information on High Ticket Sales Training is kept up to date on a regular basis so that learners don't get left behind on the current trends/updates. The self-paced online learning methodology by compete high in this High Ticket Sales Training course helps you learn whenever or however you wish, keeping in mind the busy schedule or possible inconveniences that come with physical classes. The easy-to-grasp, bite-sized lessons are proven to be most effective in memorising and learning the lessons by heart. On top of that, you have the opportunity to receive a certificate after successfully completing the course! Instead of searching for hours, enrol right away on this High Ticket Sales Training course from Compete High and accelerate your career in the right path with expert-outlined lessons and a guarantee of success in the long run. Who is this course for? While we refrain from discouraging anyone wanting to do this High Ticket Sales Training course or impose any sort of restrictions on doing this online training, people meeting any of the following criteria will benefit the most from it: Anyone looking for the basics of High Ticket Sales Training , Jobseekers in the relevant domains, Anyone with a ground knowledge/intermediate expertise in High Ticket Sales Training , Anyone looking for a certificate of completion on doing an online training on this topic, Students of High Ticket Sales Training , or anyone with an academic knowledge gap to bridge, Anyone with a general interest/curiosity Career Path This High Ticket Sales Training course smoothens the way up your career ladder with all the relevant information, skills, and online certificate of achievements. After successfully completing the course, you can expect to move one significant step closer to achieving your professional goals - whether it's securing that job you desire, getting the promotion you deserve, or setting up that business of your dreams. Course Curriculum Chapter 1_ Basics of High Tickets Basics of High Tickets 00:00 Chapter 2_ Examples of High Ticket Products Examples of High Ticket Products 00:00 Chapter 3_ Packaging a High Ticket Coaching Product Packaging a High Ticket Coaching Product 00:00 Chapter 4_ Content Creation and Length Content Creation and Length 00:00 Chapter 5_ Selling Your Product Selling Your Product 00:00 Chapter 6_ Extra Tools and Tips Extra Tools and Tips 00:00

DIPLOMA IN TROWEL OCCUPATIONS (CONSTRUCTION)
By Oscar Onsite
REFERENCE CODE 610/0501/0 COURSE LEVEL NVQ Level 3 THIS COURSE IS AVAILABLE IN Course Overview Qualification mandatory units (Mandatory – Credits: 144 Minimum, 144 Maximum) A/650/0295 (VR40V3) Erecting Masonry Structures in the Workplace Level: 2 Credits: 31 D/650/0296 (VR41V3) Setting out to form Masonry Structures in the Workplace Level: 2 Credits: 23 T/650/0293 (VR42V3) Erecting Masonry Cladding in the Workplace Level: 2 Credits: 24 A/503/2772 (209v2) Confirming Work Activities and Resources for an Occupational Work Area in the Workplace Level: 3 Credits: 10 Y/650/1392 (210V3) Developing and maintaining good occupational working relationships in the workplace Level: 3 Credits: 8 R/503/2924 (211v2) Confirming the Occupational Method of Work in the Workplace Level: 3 Credits: 11 A/503/1170 (641) Conforming to General Health, Safety and Welfare in the Workplace Level: 1 Credits: 2 T/650/1391 (49V3) Erecting masonry to form architectural and decorative structures in the workplace Level: 3 Credits: 35 Qualification optional units (Optional – Credits: 19 Minimum, 19 Maximum) H/650/0298 (VR44V3) Erect Thin Joint Masonry Structures in the Workplace Level: 2 Credits: 24 Y/650/0294 (VR50V3) Repairing and Maintaining Masonry Structures in the Workplace Level: 3 Credits: 25 R/650/0292 (VR639V3) Installing Drainage in the Workplace Level: 2 Credits: 19 F/650/0297 (VR810V1) Installing and forming specialist masonry elements in the workplace Level: 3 Credits: 21

Fatigue Reset: Crack pacing once and for all
By Pamela Rose - Fatigue Coach
Fatigue Reset: Crack Pacing once and for all! Module One: Your fatigue experience is about to get easier! Welcome to your Fatigue Reset! Here you will find everything you need to know about how you too can Crack pacing once and for all with my unique pacing method. Pacing often isn’t enough in itself to help someone achieve full recovery - attention to other healthy protocols is usually important too. But pacing is the way to make life feel easier, soon, and as well as helping to control your symptoms it gives your body the stability it needs to do whatever restorative work is needed. In short, pacing is vital - so I’m delighted you’ve signed up for this course. Welcome 4 mins483 MB What is pacing? 187 KB Why you need this course 6 mins753 MB How to get the most from this course 4 mins490 MB About my own Fatigue Recovery journey 202 KB Module Two: The importance of getting into the right mindset. Tackling life with extreme fatigue can be difficult emotionally, not just physically. This module talks about a very important mindset shift that will help to ensure you adapt to pacing as quickly as possible. Although it’s a technique that’s often discussed, I hope my way of explaining it will encourage you to really try it. Why finding acceptance is so important 6 mins868 MB A simple technique to help you find acceptance5 mins662 MB Some more reframing examples 190 KB Module Three: My pacing method. This module contains step by step tutorials about my pacing method, including how to complete the different templates provided. If viewing on a small screen, you may wish to print the templates off first so that you can look at them clearly as I'm explaining the different sections. A brief introduction before we get started 3 mins343 MB Step 1 - Creating a master task list 24 mins612 MB Task List MASTER.pdf 51.1 KB Task List MASTER.xlsx 19.4 KB Step 2 - Pacing your week 11 mins311 MB Weekly plotter MASTER.pdf 46.5 KB Weekly plotter MASTER.xlsx 17.4 KB Step 3 - Planning your day 15 mins398 MB Daily scheduler MASTER.pdf 291 KB Daily scheduler MASTER.xlsx 22 KB Step 3a - Carrying out a daily review 7 mins261 MB How to put it all into practice 6 mins753 MB Getting started guide 224 KB Module Four: Further guidance to help you make this a success. The support and guidance in this module is here to help you as you start to put my pacing method into practice. Updates will be made each month and you will be alerted when new content is available. My support for you 2 mins210 MB Frequently asked questions and answers 334 KB Quick tips for re-sizing tasks 202 KB Some more examples of delegating and outsourcing tasks 182 KB Using your baseline 190 KB How to rest 9 mins1.26 GB Resting factsheet (summary points) 16.5 KB Module Five: Moving to a more sustainable pacing approach. When the time is right, this lighter approach to pacing will help you stick to your baseline while enjoying carrying out each day with a little less structure and up-front planning. Why I feel moving to a simplified approach is important 3 mins337 MB My 'Guardrails' approach to pacing 9 mins1.29 GB A guide to my Guardrails approach 170 KB The End I'm so pleased you've made it this far, and I wish you all the very best with your ongoing fatigue rescue journey. A few final words 3 mins371 MB

Professional Chef Training Level 1 Embark on your culinary journey and become a skilled Professional Chef with our Level 1 course in Chef Training. Dive into the world of gastronomy as you learn the essentials of food safety and hygiene. Master culinary techniques that are the hallmark of a great chef, and explore the rich traditions of British cooking. Learning Outcomes: Introduce the foundations of professional chef training. Prioritize food safety and hygiene practices. Master essential culinary techniques for chefs. Explore the art of traditional British cooking. Refine baking and pastry skills for chefs. More Benefits: LIFETIME access Device Compatibility Free Workplace Management Toolkit Professional Chef Training Level 1 Course Syllabus Chef Training Intro: Gain a foundational understanding of the culinary world and the role of a professional chef in the food industry. Food Safety and Hygiene: Master essential food safety and hygiene practices crucial for maintaining a safe and sanitary kitchen environment as a Professional Chef. Culinary Techniques for a Chef: Develop proficiency in fundamental culinary techniques, from knife skills to food preparation and presentation. Traditional British Cooking: Explore the rich tradition of British cuisine, learning to prepare classic dishes that showcase the country's culinary heritage. Baking and Pastry Techniques: Acquire the Chef skills and knowledge needed to excel in baking and pastry, from crafting delectable pastries to creating mouthwatering desserts.

Ignite your culinary passion with our Chef Training course. Master the art of professional cooking, explore traditional and continental cuisines, and delve into advanced kitchen management. This comprehensive course equips you with the culinary techniques and career development skills to excel in the culinary world.

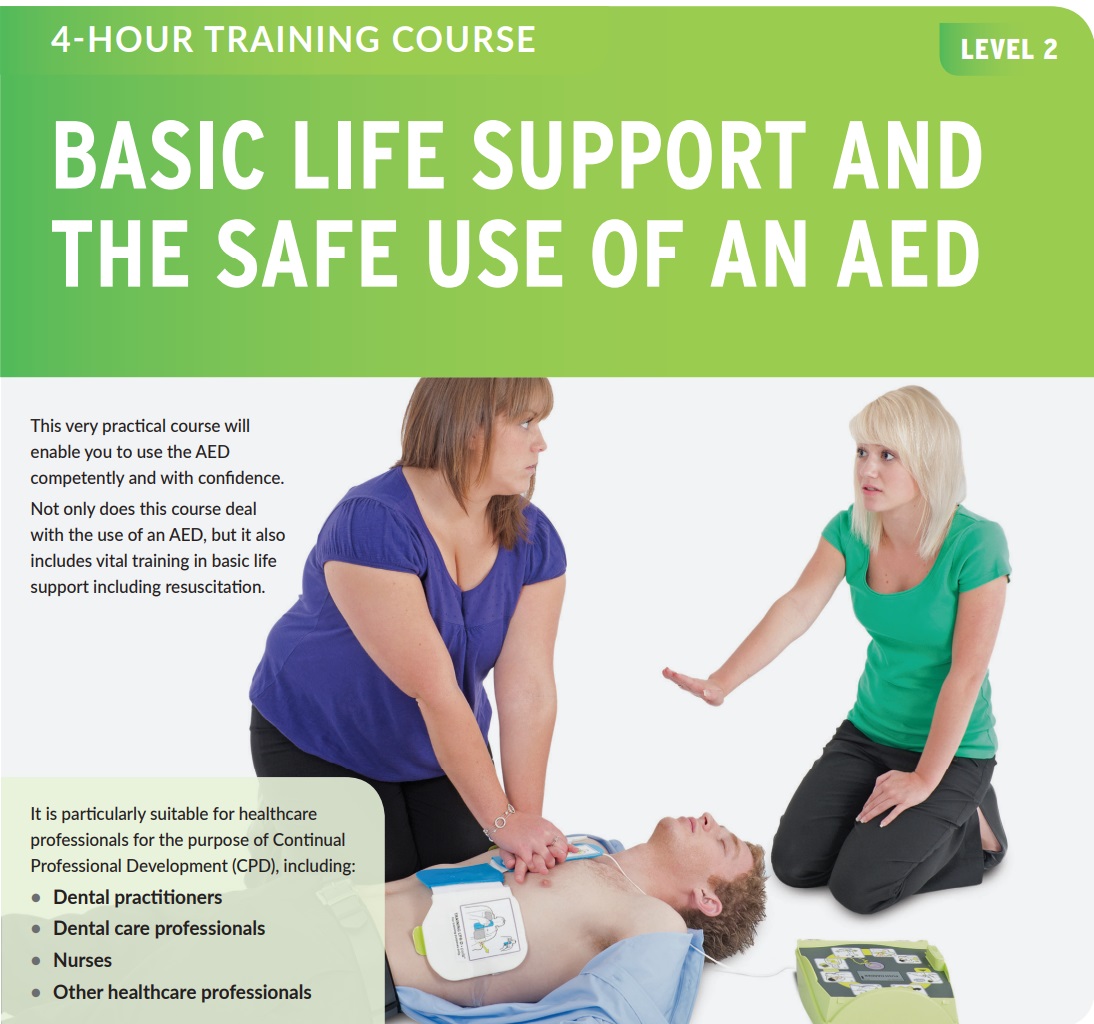
Basic Life Support (BLS) & AED (RQF)
By Emergency Medics
Basic Life Support (BLS) and Safe use of AED training
Blood drawing is a fascinating career prospect in healthcare! Our blood taking course goes beyond the fundamentals, covering everything from blood circulation to precise collection procedures. This course is your ticket to a successful career, regardless of whether you're an enthusiastic newbie or a healthcare professional trying to improve your abilities. Get knowledge and skills that'll make you an indispensable part of healthcare, leading to the welfare of people and communities. Our blood taking courses are designed to help you gain the needed skills, knowledge, and abilities to become a professional in blood-taking. You will grasp the basics of blood circulation and composition, and get hands-on expertise in routine venipuncture blood draw order, dermal puncture, and special blood collection techniques through our course for taking blood. You'll be able to learn about phlebotomy equipment, quality assurance, infection control and risk management, ensuring that you become skilled at collecting blood. Our taking blood course will help you play a vital role in the healthcare diagnostics setting. Learn how to recognise and handle challenges while also figuring out pre-examination aspects with us. This learn to take blood course will strengthen your capabilities in relevant aspects so you can establish yourself as a trained and reliable professional. This course is ideal for both newbies and professionals, as it lays the groundwork for a fulfilling healthcare career. Take our training course to take blood effortlessly and equip yourself with expertise and insights to make a significant difference in the field of diagnostics! Learning Outcomes of Blood Taking Course After finishing this blood taking course, you will be able to: Gain fundamental knowledge about phlebotomy and how to use phlebotomy equipment properly. Acquire skills and techniques for routine and special blood collection procedures. Discover the complexities of blood composition, circulation, and functions. Gain competence in dermal puncture procedures and pre-examination factors. Implement risk management and infection control strategies. Acknowledge the basic concepts of quality assessment and ensure infection control risk assessment. Who is this Course for? This blood taking course is perfect for anyone passionate about working in the healthcare setting. This training accommodates a wide range of knowledge and abilities. It's ideal for people looking to expand their skill set, offer in-demand services, and provide people with high-quality assistance. This can be considered as blood taking course for nurses also. Medical Assistants Lab Technicians Nursing Assistants Pre-Med students Healthcare Students or Professionals Nursing Students Aspiring Phlebotomist Anyone seeking a career in clinical laboratories Entry Requirements No prerequisite knowledge or experience is needed for this blood taking course. This qualification is open to individuals with an intense interest in healthcare and a desire to become proficient in drawing blood. However, you need to be aged 16 or over to undertake the qualification and have a good understanding of the English language, numeracy and ICT. Certification You will acquire an accredited certificate after successfully finishing our course for taking blood. This globally recognised CPD certification assures you mastery in the sector. The certificate in PDF format costs £9, while the hard copy costs £15. However, you can get the certificate in both printed and PDF format for only £22. Career path Competency in efficiently drawing blood is an appealing ability that will make you an invaluable asset in the healthcare environment. This blood taking course can open doors for you to new possibilities in healthcare settings, research facilities, and medical diagnostic centres. You will be able to become a vital member of a medical team. Course Duration The blood taking course adapts to diverse schedules and offers flexibility, which allows you to learn at your own pace. It takes an average of 5 hours to complete. However, you will be able to access the course materials for up to one year. Course Curriculum Blood Taking Module 01: Introduction to Phlebotomy 00:20:00 Module 02: Blood Circulation, Function and Composition 00:31:00 Module 03: Phlebotomy Equipment 00:18:00 Module 04: Routine Venipuncture 00:26:00 Module 05: Venipuncture Complications and Pre-Examination Variables 00:28:00 Module 06: Dermal Puncture 00:16:00 Module 07: Quality Assessment and Management in Phlebotomy 00:21:00 Module 08: Special Blood Collection Procedure 00:17:00 Module 09: Infection Control and Risk Management 00:21:00 Venepuncture Module 01: Venepuncture: A Method of Phlebotomy 00:10:00 Module 02: Anatomy and Physiology 00:09:00 Module 03: Before Venepuncture 00:21:00 Module 04: During Venepuncture 00:09:00 Module 05: After Venepuncture 00:09:00 Module 06: Venepuncture for Blood Donation 00:16:00 Module 07: Glossary 00:18:00 Module 08: Appendix 00:11:00 Certificate and Transcript Order Your Certificates or Transcripts 00:00:00

Search By Location
- Health Courses in London
- Health Courses in Birmingham
- Health Courses in Glasgow
- Health Courses in Liverpool
- Health Courses in Bristol
- Health Courses in Manchester
- Health Courses in Sheffield
- Health Courses in Leeds
- Health Courses in Edinburgh
- Health Courses in Leicester
- Health Courses in Coventry
- Health Courses in Bradford
- Health Courses in Cardiff
- Health Courses in Belfast
- Health Courses in Nottingham

