- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
807 Health courses in Biggleswade
An Understanding of Physiological Observations
By Guardian Angels Training
Gain essential knowledge and practical skills to accurately monitor and interpret physiological parameters in patients with our "An Understanding of Physiological Observations" course. Learn to conduct and interpret various observations to support informed clinical decision-making.

Windows certificates training course description A hands-on training course concentrating solely on PKI using Windows certificates. What will you learn Explain how PKI works. Install windows certificates. Configure windows certificates. Troubleshoot windows certificates. Windows certificates training course details Who will benefit: Technical security staff. Prerequisites: Windows server. Duration 3 days Windows certificates training course contents PKI Symmetric encryption, asymmetric encryption, authentication, digital signing, hashing, certificates, Certification Authorities, Root CA, Intermediate CA, policy CA, Issuing CA, Certificate Revocation Lists. Hands on Inspecting a certificate. Policies and PKI Security policy, certification policy. CA hierarchy Impact of CAs on Active Directory, CA architecture, number of tiers, issuing CA organisation, CA configuration files. CA security. Hands on CA installation PKI health tool, monitoring. Certificate revocation When to revoke, OCSP. Hands on Revoking certificates. Certificate validation Discovery, validation, checks, revocation checking, certificate chains, certification publication. Hands on Event viewer. Certificate templates Version 1, version 1, default, modifying templates. Hands on Template management. Roles Criteria roles, CA administrator, Certificate manager, Backup operator, Auditor. Other PKI management roles. Disaster recovery Backups, recovery. Hands on certutil. Issuing certificates The certificate enrolment process, enrolment methods, manual enrolment, automatic enrolment. Trust between organisations Creating Trust, CTLs, common root CA, cross certification, bridge CA. Web servers and certificates SSL encryption, certificate authentication. Hands on Web servers. VPN Hands on Certificate deployment for VPN. WiFi Hands on 802.1X

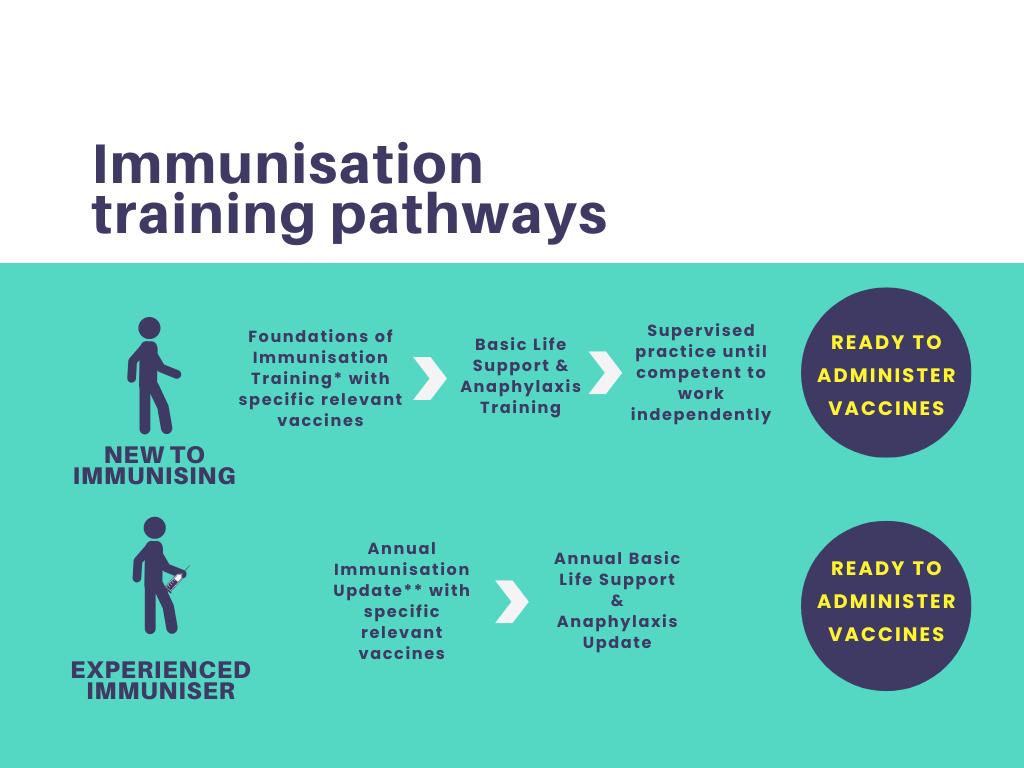
Foundations of Immunisation and Vaccines for Non-Registered Practitioners
By Guardian Angels Training
The "Foundations of Immunisation and Vaccines for Non-Registered Practitioners" course is fully compliant with the National Minimum Standards and Core Curriculum for Immunisation Training and is designed to equip non-registered healthcare professionals with a solid understanding of immunisation concepts, vaccine administration, and the importance of vaccination in public health.
Management of Risk (M_o_R) Practitioner: In-House Training
By IIL Europe Ltd
Management of Risk (M_o_R®) Practitioner: In-House Training The M_o_R® Practitioner course has been designed to provide learners with the opportunity to practice the practical application of the M_o_R method and covers the twelve M_o_R principles: Approach, Process and the basic techniques essential to managing risks using the M_o_R guidance. The purpose of the M_o_R Practitioner qualification is to confirm that the learner has achieved sufficient understanding of how to apply and tailor M_o_R in a scenario situation. What you will Learn At the end of the M_o_R Practitioner course, learners will gain competencies in: M_o_R framework (principles, approach based on risk documentation, process steps, and embedding and reviewing M_o_R principles Outline of M_o_R approach documents (including policy, process guide, and risk communications plan) Risk identification, assessment, and control Embedding and reviewing M_o_R M_o_R organizational perspectives (strategic, program, project, operational) Benefits The M_o_R Practitioner course offers a wide-ranging set of guidelines that will help in the management of risk in a project or program environment. It will help prepare learners for the M_o_R Practitioner Exam. They will feel more confident in approaching risk management after attending the course and will be aware of the use of different techniques that can assist in this task, including: Improved basis for effective strategy formation Reduced time spent fire-fighting and fewer unwelcome surprises Increased likelihood of successful change initiative outcomes Closer internal focus on doing the right things properly Increase in efficient use of resources waste and fraud Better management of contingency resources M_o_R roles and responsibilities M_o_R health check M_o_R maturity model Risk specialisms (including business continuity management) Introduction Introduction to the course What is a risk? What is risk management? Why is risk management so important? Basic risk definitions The development of knowledge about risk management Corporate governance and internal control Where and when should risk management be applied? M_o_R Principles The purpose of M_o_R principles Aligns with objectives Fits the context Engages stakeholders Provides clear guidance Informs decision-making Facilitates continual improvement Creates a supportive culture Achieves measurable value Risk management maturity models M_o_R Approach Relationship between the documents Risk management policy Risk management process guide Risk management strategy Risk register Issue register Risk response plan Risk improvement plan Risk communications plan M_o_R Process Common process barriers Identify - contexts Identify - the risks Assess - estimate Assess - evaluate Plan Implement Communication throughout the process M_o_R Perspectives Strategic perspective Programme perspective Project perspective Operational perspective Risk Specialisms Business continuity management Incident and crisis management Health and Safety management Financial risk management Environmental risk management Reputational risk management Contract risk management

Supporting Microsoft SharePoint course description A concise hands on course enabling delegates to manage and administer a SharePoint site. What will you learn Perform initial farm configuration. Use stsadm commands. Manage content. Secure SharePoint. Customise SharePoint search. Monitor and performance tune SharePoint. Supporting Microsoft SharePoint server course details Who will benefit: Anyone working with Microsoft SQL server Prerequisites: SharePoint Administrators. Duration 2 days Supporting Microsoft SharePoint course contents SharePoint Introduction A SharePoint installation. Initial farm configuration. Creating a site collection. Administering SharePoint Stsadm commands, automation with PowerShell. Managing content Lists, libraries, items and documents Security SecureStore, Users and groups, roles and role assignments. Permission levels. SharePoint search Configure search, refine search. SharePoint performance Diagnostic logging, logging levels, Health anaylzer, performance bottlenecks.

Accident Investigation
By Inovra Group
Overview This one day Accident Investigation course will give participants the necessary information and skills to enable them to carry out a thorough and effective accident investigation. Description This course will provide attendees with the necessary information and skills, to reach the right conclusions, make effective, practical recommendations and thereby make a significant contribution to improving workplace health and safety. Topics covered: Accidents & Accident Causation – If an organisation does not properly control risks, the outcome of an accident often depends on chance. Because the outcome of an accident cannot be accurately predicted, the only way to effectively reduce accidents is by controlling the underlying causes of all the different accident types. Accident Reporting Process – Reporting of Injuries, Diseases & Dangerous Occurrences Regulations 1995 (RIDDOR) The Process – You have 2 top priorities when you are first notified of an accident. The first is to the injured person to ensure that appropriate medical attention is available. The second priority is then to ensure that the area is made safe to ensure no other persons are injured Accident Investigation – Every employer has a Moral, Legal & Economic obligation to protect the health and safety of employees while at work The Cause of Accidents – During an accident investigation you will be looking for the unsafe acts and the unsafe conditions which contributed to the accident. If you carry out the investigation effectively, then you will find the root cause or causes of the accident Facts to be Collated – When you conduct an accident investigation you should be seeking to obtain information on unsafe acts, unsafe conditions, immediate failures and latent failures. To find out these various elements of the accident you need to ask the questions who, where, when, and what, which will give you details of the event Reaching Conclusion – Identifying all the failure modes, satisfy all the answers to what, where, why, who etc., and thus identify all the causes of the accident Review of Session – Creating an action plan to embed learning. Who should attend Managers, leaders, trainers, health and safety officers and anyone involved in health and safety training and/or procedures. Requirements for Attendees None.

Dancing the Wheel of Your Life 2023/24
By Leo Rutherford
Part 1, October 27th -29th, 2023 @ Clophill The Spiral continues – Four modules going around the cardinal directions West Direction – October 27th – 29th, 2023 With Leo Rutherford & Ruth Humming Ford Mother Earth – Life, Death and the Dance! This module is focussed on the Earth and our connection to everything physical – in other words, every-THING! This includes our own body which is our spirit's 'Vehicle of-Experience' for this life on earth. The shamanic path is about developing our personal sovereignty, our right to Real-ise our True Self. Our movement West is towards our fitness to navigate our way through this life and into the beyond. The shamans say that all sickness starts in the spiritand only later becomes physical. Using tools including shamanic journeying and dancing we will seek access to the beyond and to whatever healing is needed to bring us health and fitness both individually and collectively. Overcoming fear of death is a key to daring to live fully with heart. It is by committing to ourself that we will live fully, live to our best, put our whole self into whatever we have chosen to pursue…. that the most stunning results come to be achieved. And it is from that experience of daring to to go full-on that the greatest insight and development happens. Through Shamanic Journeying, ceremony, dance, we disappear into spirit, detaching from life’s ordinary challenges, able to let go and see through and past everyday issues to deeper patterns. We enter parallel realities where hidden patterns can be experienced and solutions to seemingly unsolvable problems can be accessed. 'Thank you very much for these past months & the journey round the wheel. I gained much from this and the group and it has been lovely to reconnect with you.... In deep appreciation of what you bring & gratitude for what these months have brought me. I do hope you will keep in touch.' ------------------------------------------------------------------------------------ October 27th -29th 10am – 6pm Saturday, 10am – 5pm Sunday At Clophill Centre, Shefford Road, Clophill, Beds MK45 4BT. Residence (not included, book separately) available at Clophill or local B&B/ AirB&B etc. Bring small share for light lunches. Booking:ruth@talkingtree.co.uk orleorutherford@eagleswing.co.uk £215 standard, £180 supported, £235 gifting. Bkg Dep £50BACS Ruth Ford 59568986 / 60-83-71 or https://www.paypal.com/paypalme/hummingruth/50

M.D.D WELLNESS COACHING PACKAGE (SELF IMPROVEMENT)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
The Wellness Coaching Package is inclusive of the following services: Health and Wellness Coaching Personalized Wellness Plan Mind-Body Connection Holistic Wellness Healthy Habits Overcoming Obstacles Nutrition Education Balanced Lifestyle Achieving Optimal Health Personal Growth 3 x 1 hour sessions https://relationshipsmdd.com/product/wellness-coaching-package/

CWDP training course description The CWDP course consists of instructor-led training applicable to the design of wireless LANs using the latest technologies including 802.11n and 802.11ac. The course goes in-depth into the design process and provides attendees with the knowledge needed to plan, deploy and test modern 802.11-based networks. It also prepares students for the CWDP examination. Students who complete the course will acquire the necessary skills for preparing, planning performing and documenting site surveys and wireless LAN design procedures. What will you learn Design enterprise WiFi networks. Select appropriate antennas and Access points. Perform site surveys. Describe the security requirements required for enterprise networks. Test, validate and troubleshoot installations. CWDP training course details Who will benefit: Anyone looking for the skills to analyze, troubleshoot, and optimize any enterprise level Wi-Fi network, no matter which brand of equipment your organization deploys. Anyone looking to become a CWNP. Prerequisites: CWNA Duration 5 days CWDP training course contents WLAN design overview Importance of good design, Impact of bad design, Design process, Design skills, Design toolkit. Requirements analysis Pre-planning, Customer interaction, Requirements gathering, Discovering existing systems, Documenting the environment, Defining constraints, Creating documentation. Designing for clients and applications Client Device types, Application types, Application-specific design, High density design issues. Designing for industry Standard corporate networks, Industry-specific designs, Government, Healthcare, Hospitality, Retail, Public hotspots, Transportation, Mobile offices, Outdoor and mesh, Remote networks and branch offices, Last-miles / ISP and bridging. Vendor selection processes Defining vendor issues, Operational planes, Design models, Understanding architectures. Radio Frequency (RF) planning RF spectrum, RF behaviors, Modulation and coding schemes, RF accessories, Throughput factors. WLAN hardware selection Antennas, 802.11n and antennas, Choosing Aps, Powering Aps. Site surveys Site survey tools, Site survey preparation, Predictive site surveys, Manual site surveys, Site survey principles and processes. Designing for Quality of Service (QoS) QoS overview, QoS application points, Roaming support. Designing for security Bad security, Authentication solutions, Encryption solutions, Security best practices, Intrusion prevention. Installation testing, validation and troubleshooting Network health status, Troubleshooting and validation process, Troubleshooting and validation tools, Common problems. Hands-on lab exercises Hands-on labs depend on the audience and can include use of: Spectrum analyzers, Protocol analyzers, Site Survey software, Diagramming software, Various wireless access points, Various wireless adapters and antennas.

CentOS training course description This three day hands on course provides a comprehensive coverage of core Linux administration tasks on CentOS Linux. What will you learn Administer & configure Linux systems. Maintain Linux by handling disk space and taking regular backups. Manage software packages. Perform basic troubleshooting. Maintain a secure Linux system. Describe the organisation and implementation of the filesystem. CentOS training course details Who will benefit: System administrators. Network administrators. Prerequisites: Linux fundamentals Duration 3 days CentOS training course contents Managing software Package Concepts, RPM, rpm Commands, Yum, Dependencies and Conflicts, Startup Script Problems, Shared Libraries, Library Management, Managing Processes, the Kernel: The First Process, Process Lists, Foreground & Background Processes, Process Priorities, Killing Processes. Configuring hardware Configuring Firmware and Hardware, IRQs, I/O Addresses, DMA Addresses, Boot Disks, Coldplug and Hotplug Devices, Configuring Expansion Cards and PCI Cards, Kernel Modules, USB Devices, Linux USB Drivers, Configuring Hard Disks, Partitioning Systems, LVM, Common Layouts, Creating Partitions and Filesystems, Maintaining Filesystem Health, Tuning, Journals, Checking Filesystems, Monitoring Disk Use, Mounting and Unmounting Filesystems. Managing files File Management Commands, File Naming and Wildcards, File Archiving, Links, Directory Commands, File Ownership and Group, File access control, Permissions, chmod, Defaults, File Attributes, Disk Quotas, Enabling and setting Quotas, Locating Files, The FHS. Booting Linux and editing files Installing Boot Loaders, GRUB Legacy, GRUB 2, Alternative Boot Loaders, the Boot Process, Boot Messages, Runlevels and the Initialization Process, Runlevel Functions, Runlevel Services, Alternative Boot Systems , Upstart, system. Administering the system Managing Users and Groups, Tuning User and System Environments, Using System Log Files, Understanding syslogd , Setting Logging Options, Manually Logging Data, Rotating Log Files, Reviewing Log File Contents, Maintaining the System Time, Linux Time Concepts, Manually Setting the Time, Using NTP, Running Jobs in the Future, Understanding the Role of cron, Creating System cron Jobs, Creating User cron Jobs, Using anacron, Using at. Configuring basic networking TCP/IP, Network Hardware, Network Addresses, Hostnames, Network Ports, Configuring Linux for a Local Network, Configuring with DHCP, Static IP Address, Configuring Routing, Using GUI Configuration Tools, ifup and ifdown, Diagnosing Network Connections, Testing Connectivity, Tracing a Route, Checking Network Status , Examining Network Traffic, Additional Tools. Securing your systems Administering Network Security, Super Server Restrictions, Disabling Unused Servers, Administering Local Security, Securing Passwords, Limiting root Access, Setting Login, Process, SUID/SGID Files, Configuring SSH, Using GPG, Generating, Importing and Revoking Keys, Encrypting and Decrypting Data, Signing Messages and Verifying Signatures.

Search By Location
- Health Courses in London
- Health Courses in Birmingham
- Health Courses in Glasgow
- Health Courses in Liverpool
- Health Courses in Bristol
- Health Courses in Manchester
- Health Courses in Sheffield
- Health Courses in Leeds
- Health Courses in Edinburgh
- Health Courses in Leicester
- Health Courses in Coventry
- Health Courses in Bradford
- Health Courses in Cardiff
- Health Courses in Belfast
- Health Courses in Nottingham