- Professional Development
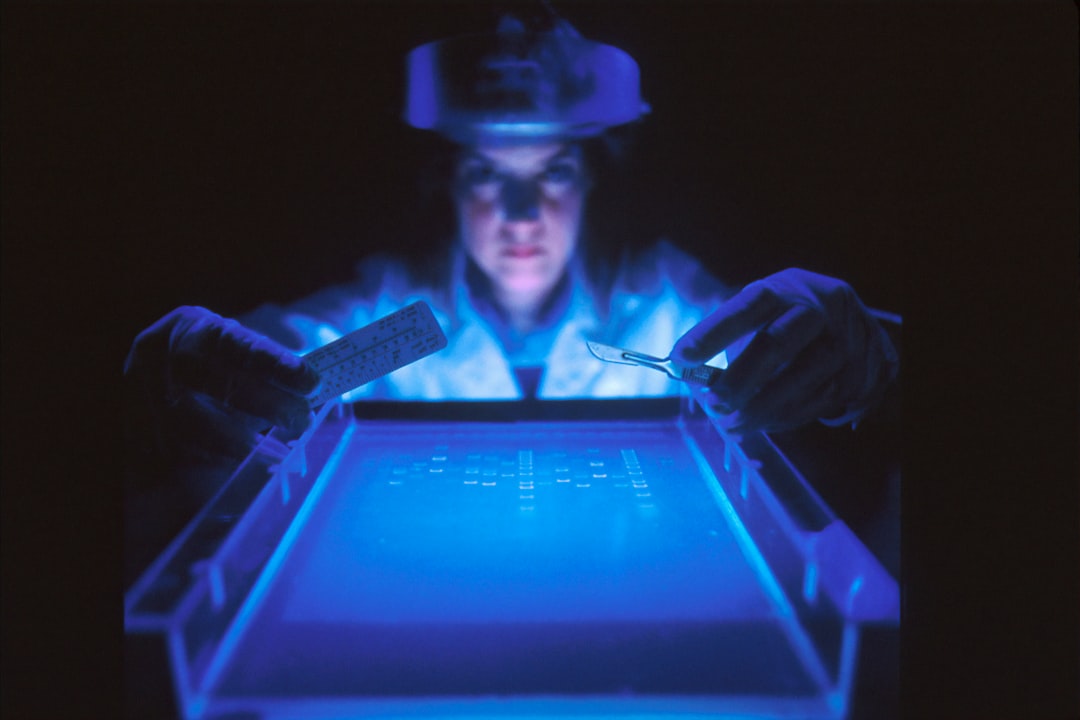
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
19370 Health courses
The NEBOSH National Diploma is designed to provide the underpinning knowledge for a professional career in health and safety. The course is suitable for both newly appointed safety practitioners and those with substantial experience who wish to obtain Chartered Membership of IOSH. It equips holders to advise on effective management of risk across the range of employment sectors.

Understanding Safe Clinical Practice Professional Development and Competence/Resilience/Mental Health and Wellbeing Interprofessional Communication Reflective Practice Health Promotion and Motivational Interviewing Clinical Skills and Chronic Disease-Asthma COPD/B12/Wound Care/Diabetes/Cardiovsacular/ECG's

Become a Mental Health First Aid Champion Mental Health First Aid (MHFA) is an internationally recognised training course, which teaches people how to spot the signs and symptoms of mental ill health and to provide help on a first aid basis. This course is designed for people who want to promote and positively affect attitudes on mental health in the workplace.

CHC43415 CERTIFICATE IV IN LEISURE AND HEALTH
By National College Australia RTO Id 91000
Leisure and Health is a vital part of the broader health care sector. Participating in recreational activities is a wonderful way for older people to engage, interact, learn and maintain a level of enjoyment for life.

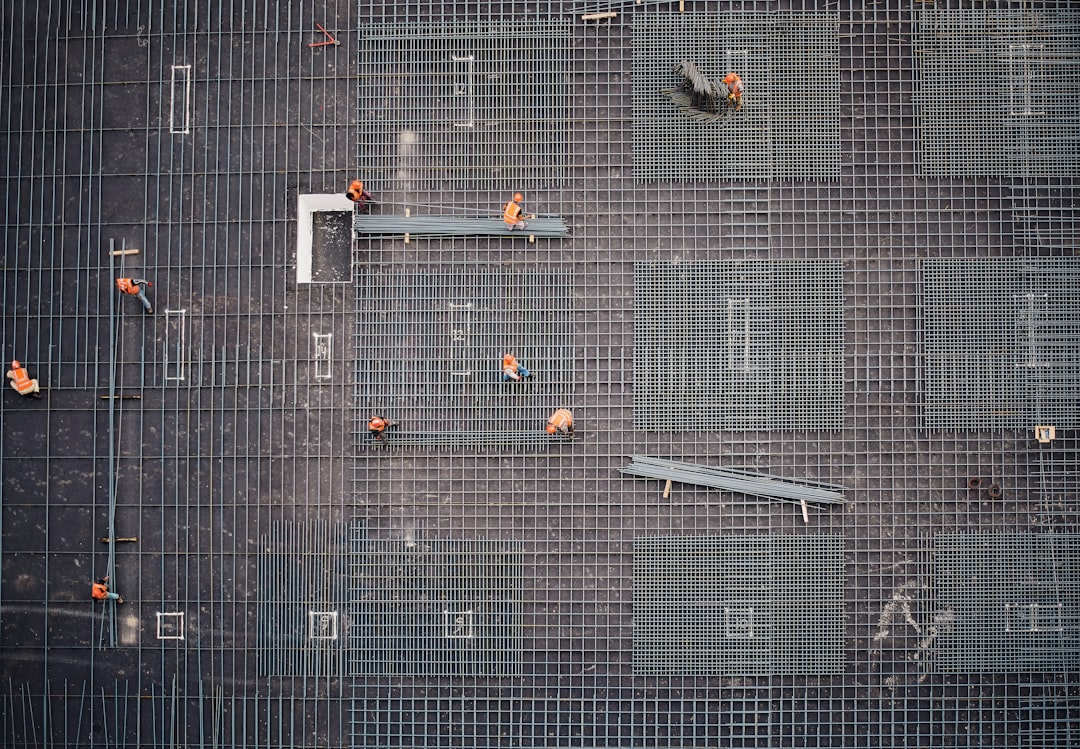
NEBOSH Health and Safety Management for Construction (UK) is guided by legislation but focussed on best practice. With an emphasis on practical application, successful learners will be able to: • Recognise, assess and control a range of common construction hazards • Develop safe systems of work • Take part in incident investigations • Advise on the roles, competencies and duties under construction legislation • Positively influence health and safety culture • Confidently challenge unsafe behaviours • Help manage contractors.
QA Level 2 Award In Health And Safety In The Workplace (RQF) Health and Safety Training Courses QA Level 2 Award In Health And Safety In The Workplace (RQF) Course Contents: Roles and responsibilities of employers and employees Health and safety laws Risk assessments and risk control hierarchy Identifying and controlling risks from common workplace hazards, including: Slips, Trips and Falls Manual Handling Fire Working from Height Electricity Hazardous Substances Workplace conditions Ergonomics Equipment Noise and vibration Transport and vehicles Violence Smoking, alcohol and drugs Stress Procedures for responding to accidents and incidents Recording incidents, accidents and ill health Benefits of this course: In 2023/24, 1.7 million people suffered from a work-related illness 600,000 sustained a non-fatal injury 138 People lost their lives 776,000 Workers suffered from work-related stress, depression or anxiety The estimated cost of injuries and ill health last year was £21.6 billion 33.7 million working days, or 140,417 working years, were lost due to work-related illnesses and injuries It is an employer's duty to protect the health, safety and welfare of their employees and other people who might be affected by their business. This includes providing sufficient information, instruction and training of employees, so they can work in a way that does not put themselves or others at risk This QA Level 2 Award in Health and Safety in the Workplace (RQF) course helps employees gain an understanding of health and safety issues and their own role within that Accredited, Ofqual regulated qualification: This Health and Safety Training Course is a nationally recognised, Ofqual regulated qualification accredited by Qualsafe Awards. This means that you can be rest assured that your Health and Safety Certificate fulfils the legal requirements and is an excellent way to make sure you and your employees are trained in Health and Safety. The Ofqual Register number for this course is 603/2687/6

Mental Health First Aid (MHFA) awareness is a short course, designed to provide delegates with a basic understanding of mental health and an introduction to Mental Health First Aid. This course raises awareness of mental health issues in the workplace. Learning objectives: What mental health is and how to challenge stigma. A basic knowledge of some common mental health issues. An introduction to looking after your own mental health and maintaining wellbeing. Confidence to support someone in distress or who may be experiencing a mental health issue

The Nebosh General Certificate gives individuals the skills and know-how to complete their health & safety responsibilities within their working environment. It can also be used as a first step in a career within Health & Safety.
Maritime Mental Health Awareness Training: Modules 1 & 2
4.2(46)By International Seafarers' Welfare and Assistance Network
Improve your awareness of mental health and the challenges faced by seafarers, in ISWAN's Maritime Mental Health Awareness training.

Driver CPC - Accidents, Incidents and Breakdowns, Vehicle Marshal & Banksman - August 2025
By Total Compliance
Description Our comprehensive course combines " Accidents, Incidents, and Breakdowns and Vehicle Marshal and Banksman Training combines 2 aspects: Road safety measures to handle accidents, incidents, and breakdowns and essentials of critical health and safety responsibilities. Accidents, Incidents, and Breakdowns Training Content: Recognizing risks and potential incidents, including breakdowns, collisions, and other scenarios. Duty of care, taking preventative measures, and handling incidents. Understanding health and safety regulations and related statistics. Prevention strategies and appropriate responses in case of an incident. Personal safety and actions to be taken during a vehicle collision. Steps to follow when facing a breakdown, including monitoring gauges and risk assessments. Ensuring the safety of other road users and cooperating with emergency services and recovery operators. Handling bridge strikes, including prevention and actions in case of an incident. Vehicle Marshal and Banksman Learn critical health and safety responsibilities Maneuvering vehicles safely during loading and unloading operations The safe use of work equipment Best practices for guiding vehicles as a Banksman Join us to enhance your knowledge of road safety preparedness. Register today to ensure your drivers are well-versed in the rules of the road and equipped to handle unexpected challenges on their journeys. Please review our Terms and Conditions for more information.

Search By Location
- Health Courses in London
- Health Courses in Birmingham
- Health Courses in Glasgow
- Health Courses in Liverpool
- Health Courses in Bristol
- Health Courses in Manchester
- Health Courses in Sheffield
- Health Courses in Leeds
- Health Courses in Edinburgh
- Health Courses in Leicester
- Health Courses in Coventry
- Health Courses in Bradford
- Health Courses in Cardiff
- Health Courses in Belfast
- Health Courses in Nottingham