- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1735 Basic courses delivered Live Online
Email Etiquette
By Nexus Human
This course is intended for Beginner-Moderate exposure is recommended for this course. The topics covered are cumulative in nature, and they require minimal understanding of email applications and composition. Overview The objective of the course is to give students the information needed to create emails that are written in a succinct, effective, and user-friendly manner. Students will learn how to set up an email subject, salutation, and will then work on how to write a credible email. In this course, students will learn about e-mail policies and learn how to write professional e-mail memos that convey appropriate messages. 1 - E-mail basics E-mail characteristics Writing online versus on paper Understanding the advantages and disadvantages of e-mail Understanding the cultural significance of e-mail E-mail programs Using an e-mail program to send e-mail When to use e-mail Communicating by e-mail Understanding when to avoid using e-mail Writing an e-mail message Using the MAIL acronym 2 - E-mail policies Company policies Avoiding improper e-mail messages Ensuring employee compliance to e-mail policies Copyright laws, viruses, and liability Avoiding copyright infringement Avoiding viruses Identifying e-mail liability 3 - E-mail features and security Features of an e-mail program Using attachments Using priority labels and signature files Features of an e-mail program Using attachments Using priority labels and signature files Discussing e-mail program options Securing e-mail Using encryption and digital signatures Using passwords 4 - E-mail messages Message headers Using headers E-mail message body Including proper greeting Structuring an e-mail message Closing an e-mail message 5 - E-mail effectiveness E-mail recipients Considering the factors that determine e-mail writing Anticipating recipient reaction Message management Managing your e-mail effectively 6 - Netiquette guidelines Netiquette style Using proper tone Following formatting guidelines Emoticons and abbreviations Using emoticons and electronic abbreviations 7 - Composing online correspondence Online communication Achieving the objective of the message Language and punctuation Improving online writing style Using punctuation correctly Efficient writing habits Constructing sentences Constructing paragraphs Editing e-mail messages

CCCS Check Point Certified Cloud Specialist-Administrator
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Technical professionals who support, install, deploy, or administer Check Point products in Cloud Environments. Overview Explain the nature of the cloud environment. Describe the five pillars of cloud architecture. Explain the Basics of Cloud Infrastructure. Explain the Basics of Cloud Automation. Explain Check Point Security Management and How it Applies to CloudGuard. Describe CloudGuard Security Gateway offerings. Describe Cloud Load Balancers. Explain CloudGuard Licensing. Explain the different Deployment options and architectures for CloudGuard. Explain how and why CloudGuard is automated. Describe the functions of CloudGuard that can be automated. Describe the tools used to automate CloudGuard. Explain CloudGuard Automation Requirements. Explain basic troubleshooting techniques specific to Check Point Security Management Servers and Security Gateways. Describe the steps for Troubleshooting CloudGuard Network Installation. Explain the tools and techniques used to troubleshoot CloudGuard Network Automation. Explain the need for Cloud Security Posture Management. Describe the posture management tools available in CloudGuard. Explain methods for correcting Cloud Security Posture Management issues. Learn basic concepts and develop skills necessary to administer Check Point CloudGuard security solutions Course Outline Deploy a Security Management Server in the Cloud. Install a Security Gateway Image. Create Virtual Networks. Deploy Internal and External Load Balancers Deploy a Security Gateway Using Templates. Assign Public IP Addresses to Cloud Devices Create Web Servers in the Cloud. Configure North-South Traffic Policy. Configure East-West Traffic Policy and Routes. Troubleshoot North-South Traffic Issues. Troubleshoot East-West Traffic Issues.

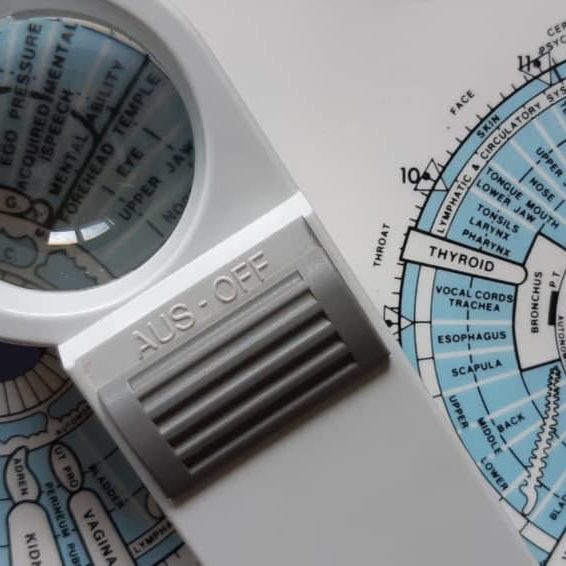
Iridology Diploma
By Plaskett International
LEARN HOW IRIDOLOGY CAN MAKE A HUGE CONTRIBUTION TO ANY COMPLEMENTARY PRACTICE A MESSAGE FROM THE AUTHOR I want to welcome you most warmly to the study of Iridology. Students of our course have taken their knowledge out into the world of practice and they have been able to see more penetratingly into the health of their patients. They have seen many truths about causes and effects in health and disease - that is what allows you to understand those extra things that make you into an even better healer. I think you are going to find this the most intriguing and absorbing study and, certainly, that is my sincere hope. As you precede, much of what you learn will amaze you and inspire wonder at the ways of the human body and mind. As you tread this very special road, I pass on to you the words that Bernard Jensen gave me years ago when I was his student, inscribed upon the inside cover of his book: “Seek the Higher Values in Life”. DR. LAWRENCE PLASKETT WHAT IS IRIDOLOGY? Iridology is the art of iris analysis. The iris is connected to the brain via the hypothalamus and can give naturopathic read outs on tissue conditions in various parts of the body. With training and practice it is possible to read signs indicative of biochemical, emotional and environmental influences that are hard to determine by other means. We can thus interpret health (and even aspects of personality) by close examination of the eyes, using suitable illumination and a magnifying glass. The close relationship between naturopathic iridology as an assessment tool and nutritional therapy and other naturopathic disciplines continues and grows closer. Now Iridology can make a huge contribution to complementary therapeutic practice and enhanced by our wonderful digital collection of eye photographs, the learning process with the Plaskett International College is a profound and exciting one. We teach Iridology quite separately from other topics and anyone who possesses, or expects to possess, a practitioner's qualification in any therapeutic discipline, may join the course. Course Duration 12 months Study Hours 200 hours Course Content 9 sections Course Fee £495 How Can Iridology Help Practitioners? Examples of how iridology can help practitioners Did you know that some iris features are so very plain that you can see them with the naked eye in ordinary social contact? You can see from two or three feet away in many cases that the person has a toxic digestive system (a strong wide dark ring around the pupil margin). You can often tell that the person has an overactive stomach (a narrow bright white ring very close to the pupil). You can tell when the skin is overlaid with toxins so that the skin's function in excreting toxins from the body is jeopardised (very narrow dark ring around the iris margin). You can tell in some people (rather advanced cases) that they suffer badly from sodium and potassium imbalance and have placed themselves at potential risk from cholesterol accumulation (the so-called corneal arcus, a white or off-white cloudy deposit, usually fairly thick, around the iris margin). Another example is the ring of spots or 'tophi' represented by the lymphatic rosary. Its mere presence tells one that there is sluggishness in the lymphatic system. When these tophi are darkly pigmented, the situation gives rise to concern for the possible generation of lymphatic illness. Using the precise positioning of iris reflex areas contained on the iris chart, one may distinguish many key points of analysis. Areas of stress and tension can be pinpointed by identifying 'contraction furrows’. Past injuries and adhesions show themselves as contortions of the normally regular and even iris fibres. You can answer questions like:- Is it the pancreas or the liver that is responsible for the trouble? Is the patient's hypertension caused by a defect of or toxic deposits in the particular brain area that is geared to control blood pressure? One of Jensen's rather dramatic illustrations is of the iris of a man who has just been shot. It shows the precise areas of tissue damage within the body and the response is very fast. The number of potential examples is almost without limit. The above may suffice to show the types of things that iridology can do for practitioners. We hope it will help you decide to study Iridology with the Plaskett International College. Course Overview The course covers the nature of iris observation, the nutritive zone, the iris chart, the chronic and acute, the intestinal and stomach zones and nerve collarette, the constitution type, respiratory system, lacunae, open lacuna, inherent weaknesses, the organs of elimination, other organs, special signs, complete diagnosis of a subject. The treatment of the topic follows the principles of Bernard Jensen in the USA. Once the basics have been learnt, the course teachings then extend considerably by bringing in the work of Dorothy Hall and of Dr Josef Deck, both of which are the subject of a special presentation during the course. The published insights of Farida Sharan and Harri Wolf, while not separately presented, also influence the presentation of the course material. Both the Australian School, (Dorothy Hall) and the German School, (Dr Deck/Harri Wolf), offer an added dimension to the study and interpretation of the constitution. PERSONALITY ASPECTS & CONSTITUTIONAL TYPES The study focuses upon the different personality aspects, which show up in different constitutional types. Dorothy Hall gives insights into what contributes to various different types of personality and their emotional and mental responses and their pre-dispositions to health or disease. Different sorts of people can have different priorities, preferences and imperatives built into their very nature from or before birth, sometimes determining the course of their entire lives and their attitudes to the world and to other people. AN EMPATHY BETWEEN PATIENT & PRACTITIONER The course teaches an understanding of these types and facilitates an empathy between patient and practitioner. It shows how people of the differing constitutional types are likely to go out of balance either mentally or emotionally and how their vulnerability to various physical ailments varies. The German School offers a very exciting and precise approach to the constitutional types, which is really quite different, but no less helpful. It highlights variations in the susceptibility to diseases of different organs and systems. THE 3 SCHOOLS OF THOUGHT It is a prime purpose of this course, not only to teach these differing positions, but also to demonstrate how it is that all three of these major schools of Iridology embody different aspects of the truth, how each is individually valuable and how a full and deep understanding of the meaning of 'constitution' can be gained through a sympathetic synthesis of the contributions from all three of these schools. BREAKDOWN OF THE COURSE SECTIONS In total there are 9 sections comprising of text, videos and iris images to study: SECTION 1 GENERAL PRACTICE AND AN ACCOUNT OF THE NUTRITIVE ZONE Areas Covered Iris colour Information that iridology can give us The structure of the eye and the iris Using the iris as an assessment tool The principle of reflex areas The Nutritive Zone Abnormality in the colon The Collarette (autonomic nerve wreath or anw) Diagnosis of the constitution based upon fibre structure Studies on images of real eyes SECTION 2 FEATURES OF THE FIBRES OUTSIDE THE COLLARETTE Areas Covered The general layout of fibres outside the collarette Inherent weaknesses First stage in further deterioration of an inherent weakness The meaning of darkness in the iris The development of discrete – open lacunae Lacunae Further notes about lightness and darkness amongst the fibres Healing lines Crypts Round the iris chart – the left iris Round the iris chart – the right iris Checking which structures and inside and which outside the collarette The organ systems The neural arc reflex SECTION 3 SPECIAL SIGNS Areas covered The corneal arcus (sodium ring, cholesterol ring, lipemic ring) The tophi (also lymphatic tophi or lymphatic rosary) Corneal Arcus The anaemia sign The catarrhal sign Acidity Grey background Scurf rim Circulatory ring Sphincter muscle (also called pupillary sphincter) Pigments (topastible or topolabile) Psoric spots Contrcation furrows Radial furrows SECTION 4 THE CONSTITUTIONS IN RELATION TO PERSONALITY TYPE AND DISEASE DISPOSITION Areas covered Very resilient Resilient average Moderately resilient Mildly resilient SECTION 5 MORE ABOUT WHITE SIGNS Areas covered Revision of distinctions between the different white signs Pictures of irises with white signs, with commentaries Further interpretation of the corneal arcus Further interpretation of the lytophi More general interpretation of the colour white SECTION 6 COLOURS IN THE IRIS AND OTHER SPECIAL SIGNS Areas Covered Yellow pigment in the iris Orange pigment Brown pigment Contraction furrows Radial furrows Psoric spots Pupillary border The “friendly fibrils” sign Summary of remedies SECTION 7 THE CONSTITUTION AND SIGNS ACCORDING TO THE GERMAN SCHOOL Areas Covered The German school of iridology Our approach to teaching the German school Introduction to the German constitutional types The lymphatic constitutions Mixed biliary constitution or biliary constitution Haematogenic (or haematogenous) constitution The way to use information on the German constitutions New signs that are specific to the German school Treatment recommendations for constitutional types SECTION 8 ADVANCED STUDIES OF THE IRIS Areas Covered Further details of the iris chart – its layout and its implications Neural arc reflex Deformation of pupil shape and position Advanced study of fibre separations, sinuosity, injuries & adhesions Lacunae of different shape and appearance The b3 bulge and the pterygium Working with genetically brown eyes SECTION 9 THE CONSULTATION & THE PRACTICALITIES Areas Covered Diagnosing pathology of individual critical organs Personality interpretations based upon the German school Conducting an iridology consultation Practical aspects of iris examination Making drawings of the iris and recording the data The uses, advantages and limitations of iris photography and its place in iridology practice Equipments and techniques of iris photography Using the computer to store and process digital images The interaction of signs Interpreting the whole iris in conjunction with the case study Pointers to treatment Carrying out case histories TESTIMONIALS Here's what students have to say about the course Emma Rubio, Health Coach Spain "As a Health Coach I decided to pursue my studies with the Plaskett College to become a Nutritional Therapist. For that, I am also studying Iridology. I am happy to have a tutor to answer my doubts and I like the flexibility that the College offers me. I love the subject of Iridology and the way it is explained, I also like having some videos of Dr Plaskett teaching Iridology as I admire him." Dr Ezequiel Lafontaine, Iridologist Puerto Rico "I LOVE IRIDOLOGY. I have over 30 iridology books, Italian, French, German, Spanish and English, plus over 4,000 photos from my own practice. I took this course for a refresher course and found the material was second to none." Mrs D. Moothy, Nutritional Therapist Mauritius “The distance learning courses have given me the opportunity to pursue my dreams through a program that was not only flexible and convenient for my schedule, but was also challenging and rewarding. I thoroughly enjoyed the readings and the assignments but most importantly, I enjoyed being able to do things at my pace. I must say that the most exciting and challenging course was the Iridology Diploma, and I am happy that I was able to do well in all the courses."
Red Hat Services Management and Automation (RH358)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Linux system administrators, site reliability engineers, and other IT professionals with some Ansible experience who are interested in learning how to manage and automate the deployment, configuration, and operation of key network services included with Red Hat Enterprise Linux 8. Overview Provide key network services using software included with Red Hat Enterprise Linux 8, including DNS with Unbound and BIND9, DHCP and DHCPv6, client e-mail transmission, printing service, NFS and SMB protocol file sharing, SQL database service with MariaDB, and web services using Apache HTTPD, nginx, Varnish, and HAProxy. Configure advanced networking for server use cases, including device teaming. Use Red Hat Ansible Engine to automate the manual deployment and configuration tasks covered in this course. Learn how to configure, manage, and scale key services used in the data center Red Hat Services Management and Automation (RH358) is designed for IT professionals with some experience managing Linux© systems and want to learn more about how to manage and deploy network services included with Red Hat© Enterprise Linux which are particularly important in the modern IT data center. You will learn how to install, configure, and manage basic configurations of these services manually, and then use Red Hat Ansible© Engine to automate your work in a scalable, repeatable manner. This course is based on Red Hat Ansible Engine 2.9 and Red Hat Enterprise Linux 8.1. 1 - Manage network services Discuss and review key tools and skills needed to manage network services. 2 - Configure link aggregation Improve the redundancy or throughput of network connections of servers by configuring Linux network teaming between multiple network interfaces. 3 - Manage DNS and DNS servers Explain the operation of DNS service, troubleshoot DNS issues, and configure servers to act as a DNS caching nameserver or as an authoritative name server. 4 - Manage DHCP and IP address assignment Explain and configure services used for IPv4 and IPv6 address assignment including DHCP, DHCPv6, and SLAAC. 5 - Manage printers and printing files Configure systems to print to a network printer that supports IPP Everywhere, as well as manage existing printer queues. 6 - Configure email transmission Discuss how mail servers operate, then configure a server to use system tools and Postfix to send email messages through an outbound mail relay. 7 - Configure MariaDB SQL databases Discuss the basic operation of SQL-based relational databases, perform basic SQL queries for troubleshooting, and be able to set up a simple MariaDB database service. 8 - Configure web servers Provide web content from Apache HTTPD or Nginx web servers, then configure them with virtual hosts and TLS-based encryption. 9 - Optimize web server traffic Improve performance of your web servers by using Varnish to cache static content being served and HAProxy to terminate TLS connections and balance load between servers. 10 - Provide file-based network storage Deliver simple file-based network shares to clients using the NFS and SMB protocols. 11 - Access block-based network storage Configure iSCSI initiators on your servers to access block-based storage devices provided by network storage arrays or Ceph storage clusters.

Cisco Unified Contact Center Enterprise Deployment v11.5 (UCCE-D)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The primary audience for this course is as follows: Cisco Unified Communications system channel partners and resellers. System and technical support engineers. Customers who are deploying and maintaining Cisco Unified CCE solution products. Overview Upon completing this course, the learner will be able to meet these overall objectives: Understand CCE solutions, architecture, solution options, deployment models, integrated features and call flow options. Understand underlying Cisco Unified CCE processes, messaging and fault tolerance schemes. Install, upgrade and make basic configurations in Cisco Unified Communications Manager. Install, create databases, integrate, and upgrade all ICM components to include the ICM Router, Logger, Administration & Data Server, Peripheral Gateways, CTI Gateway and Cisco Finesse. Install, integrate, configure, and upgrade Cisco Unified CVP components to include the CVP Call Server, Voice XML Server, Media Server, Reporting Server and Cisco VVB. Install, upgrade, and make configurations for Cisco Unified Intelligence Center and Cisco Outbound Option Agent- and IVR-based campaigns. This course will provide the student with the underlying knowledge to understand deployment design solutions, requirements for deployment, and how to install and configure all major Cisco Unified CCE components. As a part of deployment activities, the student will understand how to install and integrate Intelligent Contact Manager (ICM) with Active Directory, how to install and integrate Cisco Unified CVP components using an IOS-based voice browser and Cisco Virtualized Voice Browser (Cisco VVB), how to install and integrate Cisco Finesse, how to install and integrate Cisco Unified Intelligence Center with Active Directory and associated Data Sources for reporting purposes, and how to install and configure Agent- and IVR-based Outbound Option dialing campaigns. And finally, the student will learn how to setup and use troubleshooting tools including RTMT, System CLI, Diagnostic Framework, and ICM command-line utilities to find status information and log files, and to track a call from the point of entry to the agent desktop. Cisco Unified Contact Center Enterprise Overview Lesson 1: Presenting Cisco Unified Contact Center Enterprise Lesson 2: Cisco Unified CCE Core Components Lesson 3: Cisco Unified CCE Options Lesson 4: Basic Call Flow Models Cisco Unified CCE Protocols, Processes and Services Lesson 1: Cisco Unified CM Lesson 2: Cisco Unified CCE/Intelligent Contact Manager Lesson 3: Cisco Unified CVP Installing Cisco Unified Communications Manager Lesson 1: Installation Prerequisites Lesson 2: Cisco Unified CM Installation Lesson 3: Post-installation Configurations Lesson 4: Creating Basic Infrastructure Lesson 5: Upgrading Cisco Unified CM Installing Intelligent Contact Manager Lesson 1: Installation Requirements Lesson 2: Pre-installation Tasks Lesson 3: Install the Main Installer Lesson 4: Install the Central Controller ?Lesson 5: Install the Administration and Data Server Lesson 6: Install the Peripheral Gateway Lesson 7: Install CTI Services Installing Cisco Unified CVP Lesson 1: Installation Prerequisites Lesson 2: Install the CVP Server Lesson 3: Configure Cisco Unified CVP Components Lesson 4: Upgrading Cisco Unified CVP Upgrade Path Installing and Configuring Cisco Unified CCE Options Lesson 1: Cisco Outbound Option Lesson 2: Cisco Unified Intelligence Center Supporting Cisco Unified CCE Lesson 1: Maintenance Activities Lesson 2: UCCE Troubleshooting Tools

Designing and Building Big Data Applications
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is best suited to developers, engineers, and architects who want to use use Hadoop and related tools to solve real-world problems. Overview Skills learned in this course include:Creating a data set with Kite SDKDeveloping custom Flume components for data ingestionManaging a multi-stage workflow with OozieAnalyzing data with CrunchWriting user-defined functions for Hive and ImpalaWriting user-defined functions for Hive and ImpalaIndexing data with Cloudera Search Cloudera University?s four-day course for designing and building Big Data applications prepares you to analyze and solve real-world problems using Apache Hadoop and associated tools in the enterprise data hub (EDH). IntroductionApplication Architecture Scenario Explanation Understanding the Development Environment Identifying and Collecting Input Data Selecting Tools for Data Processing and Analysis Presenting Results to the Use Defining & Using Datasets Metadata Management What is Apache Avro? Avro Schemas Avro Schema Evolution Selecting a File Format Performance Considerations Using the Kite SDK Data Module What is the Kite SDK? Fundamental Data Module Concepts Creating New Data Sets Using the Kite SDK Loading, Accessing, and Deleting a Data Set Importing Relational Data with Apache Sqoop What is Apache Sqoop? Basic Imports Limiting Results Improving Sqoop?s Performance Sqoop 2 Capturing Data with Apache Flume What is Apache Flume? Basic Flume Architecture Flume Sources Flume Sinks Flume Configuration Logging Application Events to Hadoop Developing Custom Flume Components Flume Data Flow and Common Extension Points Custom Flume Sources Developing a Flume Pollable Source Developing a Flume Event-Driven Source Custom Flume Interceptors Developing a Header-Modifying Flume Interceptor Developing a Filtering Flume Interceptor Writing Avro Objects with a Custom Flume Interceptor Managing Workflows with Apache Oozie The Need for Workflow Management What is Apache Oozie? Defining an Oozie Workflow Validation, Packaging, and Deployment Running and Tracking Workflows Using the CLI Hue UI for Oozie Processing Data Pipelines with Apache Crunch What is Apache Crunch? Understanding the Crunch Pipeline Comparing Crunch to Java MapReduce Working with Crunch Projects Reading and Writing Data in Crunch Data Collection API Functions Utility Classes in the Crunch API Working with Tables in Apache Hive What is Apache Hive? Accessing Hive Basic Query Syntax Creating and Populating Hive Tables How Hive Reads Data Using the RegexSerDe in Hive Developing User-Defined Functions What are User-Defined Functions? Implementing a User-Defined Function Deploying Custom Libraries in Hive Registering a User-Defined Function in Hive Executing Interactive Queries with Impala What is Impala? Comparing Hive to Impala Running Queries in Impala Support for User-Defined Functions Data and Metadata Management Understanding Cloudera Search What is Cloudera Search? Search Architecture Supported Document Formats Indexing Data with Cloudera Search Collection and Schema Management Morphlines Indexing Data in Batch Mode Indexing Data in Near Real Time Presenting Results to Users Solr Query Syntax Building a Search UI with Hue Accessing Impala through JDBC Powering a Custom Web Application with Impala and Search

Securing Cisco Networks with Snort Rule Writing Best Practices (SSFRULES) v2.0
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is for technical professionals to gain skills in writing rules for Snort-based intrusion detection systems (IDS) and intrusion prevention systems (IPS). The primary audience includes: Security administrators Security consultants Network administrators System engineers Technical support personnel using open source IDS and IPS Channel partners and resellers Overview After taking this course, you should be able to: Describe the Snort rule development process Describe the Snort basic rule syntax and usage Describe how traffic is processed by Snort Describe several advanced rule options used by Snort Describe OpenAppID features and functionality Describe how to monitor the performance of Snort and how to tune rules The Securing Cisco Networks with Snort Rule Writing Best Practices (SSFRules) v2.0 course shows you how to write rules for Snort, an open-source intrusion detection and prevention system. Through a combination of expert-instruction and hands-on practice, this course provides you with the knowledge and skills to develop and test custom rules, standard and advanced rules-writing techniques, how to integrate OpenAppID into rules, rules filtering, rules tuning, and more. The hands-on labs give you practice in creating and testing Snort rules. Course Outline Introduction to Snort Rule Development Snort Rule Syntax and Usage Traffic Flow Through Snort Rules Advanced Rule Options OpenAppID Detection Tuning Snort Lab outline Connecting to the Lab Environment Introducing Snort Rule Development Basic Rule Syntax and Usage Advanced Rule Options OpenAppID Tuning Snort

Mastering Scala with Apache Spark for the Modern Data Enterprise (TTSK7520)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This intermediate and beyond level course is geared for experienced technical professionals in various roles, such as developers, data analysts, data engineers, software engineers, and machine learning engineers who want to leverage Scala and Spark to tackle complex data challenges and develop scalable, high-performance applications across diverse domains. Practical programming experience is required to participate in the hands-on labs. Overview Working in a hands-on learning environment led by our expert instructor you'll: Develop a basic understanding of Scala and Apache Spark fundamentals, enabling you to confidently create scalable and high-performance applications. Learn how to process large datasets efficiently, helping you handle complex data challenges and make data-driven decisions. Gain hands-on experience with real-time data streaming, allowing you to manage and analyze data as it flows into your applications. Acquire practical knowledge of machine learning algorithms using Spark MLlib, empowering you to create intelligent applications and uncover hidden insights. Master graph processing with GraphX, enabling you to analyze and visualize complex relationships in your data. Discover generative AI technologies using GPT with Spark and Scala, opening up new possibilities for automating content generation and enhancing data analysis. Embark on a journey to master the world of big data with our immersive course on Scala and Spark! Mastering Scala with Apache Spark for the Modern Data Enterprise is a five day hands on course designed to provide you with the essential skills and tools to tackle complex data projects using Scala programming language and Apache Spark, a high-performance data processing engine. Mastering these technologies will enable you to perform a wide range of tasks, from data wrangling and analytics to machine learning and artificial intelligence, across various industries and applications.Guided by our expert instructor, you?ll explore the fundamentals of Scala programming and Apache Spark while gaining valuable hands-on experience with Spark programming, RDDs, DataFrames, Spark SQL, and data sources. You?ll also explore Spark Streaming, performance optimization techniques, and the integration of popular external libraries, tools, and cloud platforms like AWS, Azure, and GCP. Machine learning enthusiasts will delve into Spark MLlib, covering basics of machine learning algorithms, data preparation, feature extraction, and various techniques such as regression, classification, clustering, and recommendation systems. Introduction to Scala Brief history and motivation Differences between Scala and Java Basic Scala syntax and constructs Scala's functional programming features Introduction to Apache Spark Overview and history Spark components and architecture Spark ecosystem Comparing Spark with other big data frameworks Basics of Spark Programming SparkContext and SparkSession Resilient Distributed Datasets (RDDs) Transformations and Actions Working with DataFrames Spark SQL and Data Sources Spark SQL library and its advantages Structured and semi-structured data sources Reading and writing data in various formats (CSV, JSON, Parquet, Avro, etc.) Data manipulation using SQL queries Basic RDD Operations Creating and manipulating RDDs Common transformations and actions on RDDs Working with key-value data Basic DataFrame and Dataset Operations Creating and manipulating DataFrames and Datasets Column operations and functions Filtering, sorting, and aggregating data Introduction to Spark Streaming Overview of Spark Streaming Discretized Stream (DStream) operations Windowed operations and stateful processing Performance Optimization Basics Best practices for efficient Spark code Broadcast variables and accumulators Monitoring Spark applications Integrating External Libraries and Tools, Spark Streaming Using popular external libraries, such as Hadoop and HBase Integrating with cloud platforms: AWS, Azure, GCP Connecting to data storage systems: HDFS, S3, Cassandra, etc. Introduction to Machine Learning Basics Overview of machine learning Supervised and unsupervised learning Common algorithms and use cases Introduction to Spark MLlib Overview of Spark MLlib MLlib's algorithms and utilities Data preparation and feature extraction Linear Regression and Classification Linear regression algorithm Logistic regression for classification Model evaluation and performance metrics Clustering Algorithms Overview of clustering algorithms K-means clustering Model evaluation and performance metrics Collaborative Filtering and Recommendation Systems Overview of recommendation systems Collaborative filtering techniques Implementing recommendations with Spark MLlib Introduction to Graph Processing Overview of graph processing Use cases and applications of graph processing Graph representations and operations Introduction to Spark GraphX Overview of GraphX Creating and transforming graphs Graph algorithms in GraphX Big Data Innovation! Using GPT and Generative AI Technologies with Spark and Scala Overview of generative AI technologies Integrating GPT with Spark and Scala Practical applications and use cases Bonus Topics / Time Permitting Introduction to Spark NLP Overview of Spark NLP Preprocessing text data Text classification and sentiment analysis Putting It All Together Work on a capstone project that integrates multiple aspects of the course, including data processing, machine learning, graph processing, and generative AI technologies.

Delivering Exceptional Customer Service on a Consistent Basis
By Beyond Satisfaction - Customer service Training
If you want your employees to improve their customer service skills and deliver an amazing experience to your customers, feel free to check out my Training course focusing on delivering the best customer care.

VMware vRealize Automation: Install, Configure, Manage [v8.3]
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Experienced system administrators and system integrators responsible for designing and implementing vRealize Automation Overview By the end of the course, you should be able to meet the following objectives: Describe the vRealize Automation architecture and use cases in cloud environments Manage vRealize Automation entities on VMware and third-party virtual and cloud infrastructures Configure and manage Cloud Accounts, Projects, Flavor Mappings, Image Mappings, Network Profiles, Storage Profiles, Volumes, Tags, and Services Create, modify, manage, and deploy Cloud Templates Connect to a Kubernetes Cluster and manage namespaces Customize services and virtual machines with cloudConfig Configure and manage the Service Broker Configure and manage ABX actions, custom properties, event broker subscriptions, and vRealize Orchestrator workflows Integrate with vRealize Orchestrator Install vRealize Automation with Lifecycle Configuration Manager Describe Cloud Automation Services (Cloud Assembly and Code Stream). Integrate Cloud Assembly with Terraform and SaltStack Use logs and CLI commands to monitor and troubleshoot vRealize Automation During this five-day course, you focus on installing, configuring, and managing VMware vRealize© Automation?. You learn about how vRealize Automation can be used to automate the delivery of virtual machines, applications, and personalized IT services across different data centers and hybrid cloud environments. The course covers how to manage both on-premise systems and cloud services. The course covers how vRealize Automation Service Broker can aggregate content in native formats from multiple clouds and platforms into a common catalog. This course also covers interfacing vRealize Automation with other systems using VMware vRealize© Orchestrator? and how to use vRealize Automation to manage Kubernetes systems and leverage other systems. The course also covers integrating with Terraform and using SaltStack as a configuration management tool. Course Introduction Introductions and course logistics Course objectives vRealize Automation Overview and Architecture Describe the purpose and functionality of vRealize Automation Describe the vRealize Automation architecture Describe the use of VMware Workspace ONE© AccessTM Describe the relationship between Kubernetes clusters, containers, and vRealize Automation services Describe CLI commands for vRealize Automation 8 cluster management Describe Cloud Assembly Describe Service Broker Describe Code Stream Installing vRealize Automation List the different vRealize Automation deployment types Describe the purpose of vRealize easy installer Describe the vRealize Automation installation process Authentication and Authorization Identity the steps involved in integrating Workspace One with Active Directory Describe features of Workspace One Describe the user roles available in vRealize Automation Identify the key tasks performed by each user role Define custom roles Configure branding and multitenancy Basic Initial Configuration Quickly create a basic configuration with a cloud account, cloud zone, project, flavor mapping, and image mapping. VMware Cloud Templates Configure and deploy a basic cloud template Create cloud templates that can run on any cloud Use cloudConfig to run commands, install software, and create users Use YAML for inputs, variables, and conditional deployments Tags and Storage Configuration Configure tags Describe different types of tags Manage tags Configure storage profiles Use tags and storage profiles Integrating NSX-T Data Center List the capabilities and use cases of NSX-T Data Center Describe the NSX-T Data Center architecture and components Integrate NSX-T Data Center with vRealize Automation List the supported network profiles in vRealize Automation Use NSX-T Data Center components to design a multitier application Cloud Template Identify the network and security options available in design canvas Create and manage on-demand networks and security groups Configure NSX-T day 2 actions Integrating with Public Clouds Configure and use VMware Cloud Foundation accounts Configure and use an AWS cloud account Configure and use an Azure cloud account Configure and use a Google Cloud Platform cloud account Using Service Broker for Catalog Management Release a VMware Cloud Template? Define content source and content sharing Define Service Broker policy enforcement Use custom forms for catalog items vRealize Automation Extensibility Describe Extensibility Use event topics Create a subscription Call a vRealize Orchestrator workflow Create ABX actions Using Code Stream Introduction to Code Stream The CI/CD process Integrate GitLab with Code Stream and Cloud Assembly Use Code Stream to install software Using Terraform Integrate Cloud Assembly with Terraform Use Terraform with a VMware Cloud Template Use Terraform with Code Stream Using Kubernetes Clusters Introduction to Kubernetes Connect to an existing Kubernetes Cluster Integrate VMware Tanzu? Grid Integrated Edition Create a Supervisor Namespace as a catalog item Using SaltStack for Configuration Management Introduction SaltStack with vRealize Automation Use SaltStack for software deployment Use SaltStack for configuration management Use SaltStack with event-driven orchestration vRealize Automation Troubleshooting and Integration Location of logs Using Activity Monitoring deployment history Basic troubleshooting CLI commands Collecting logs (VAMI console) Integration with VMware vRealize© Log Insight? Integration with vRealize Operations Migrating vRealize Automation 7.x to 8
![VMware vRealize Automation: Install, Configure, Manage [v8.3]](https://cademy-images-io.b-cdn.net/9dd9d42b-e7b9-4598-8d01-a30d0144ae51/4c81f130-71bf-4635-b7c6-375aff235529/original.png?width=3840)