- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Train the Trainer / Instructor Course in Nasogastric Tube Insertion and Feeding
By Guardian Angels Training
Gain comprehensive knowledge and practical skills for safe and effective nasogastric tube insertion and feeding techniques with our "Promoting Best Practice in Nasogastric Tube Insertion and Feeding Tuition" course. Optimise patient safety, comfort, and outcomes with evidence-based best practices.

Software development training course description This three-day MTA Training course helps you prepare for Microsoft Technology Associate Exam 98-361, and build an understanding of these topics: Core programming, Object-Oriented programming, general software development, web applications, desktop applications, and databases. This course leverages the same content as found in the Microsoft Official Academic Course (MOAC) for this exam. What will you learn Describe core programming. Explain Object Oriented programming. Describe general software development. Describe Web applications. Describe desktop applications. Explain how databases work. Software development training course details Who will benefit: Anyone looking to learn the fundamentals of software. Prerequisites: None. Duration 3 days Software development training course contents Core programming Computer storage and data types How a computer stores programs and the instructions in computer memory, memory stacks and heaps, memory size requirements for the various data storage types, numeric data and textual data. Computer decision structures Various decision structures used in all computer programming languages; If decision structures; multiple decision structures, such as Ifâ¦Else and switch/Select Case; reading flowcharts; decision tables; evaluating expressions. Handling repetition For loops, While loops, Do...While loops and recursion. Understand error handling Structured exception handling. Object-oriented programming Classes Properties, methods, events and constructors; how to create a class; how to use classes in code. Inheritance Inheriting the functionality of a base class into a derived class. Polymorphism Extending the functionality in a class after inheriting from a base class, overriding methods in the derived class. Encapsulation Creating classes that hide their implementation details while still allowing access to the required functionality through the interface, access modifiers. General software development Application life cycle management Phases of application life cycle management, software testing. Interpret application specifications Application specifications, translating them into prototypes, code, select appropriate application type and components. Algorithms and data structures Arrays, stacks, queues, linked lists and sorting algorithms; performance implications of various data structures; choosing the right data structure. Web applications Web page development HTML, CSS, JavaScript. ASP.NET web application development Page life cycle, event model, state management, client-side versus server-side programming. Web hosting Creating virtual directories and websites, deploying web applications, understanding the role of Internet Information Services. Web services Web services that will be consumed by client applications, accessing web services from a client application, SOAP, WSDL. Desktop applications Windows apps UI design guideline categories, characteristics and capabilities of Store Apps, identify gestures. Console-based applications Characteristics and capabilities of console- based applications. Windows Services Characteristics and capabilities of Windows Services. Databases Relational database management systems Characteristics and capabilities of database products, database design, ERDs, normalisation concepts. Database query methods SQL, creating and accessing stored procedures, updating and selecting data. Database connection methods Connecting to various types of data stores, such as flat file; XML file; in-memory object; resource optimisation.

M.D.D COACHING FOR CEOS PACKAGE (SELF IMPROVEMENT)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
Solution-Focused Coaching Model Grow Coaching Model 0SKAR Coaching Model CLEAR Coaching Model AOR Coaching Model FUEL Coaching Model WOOP Coaching Model COACHING PROCEDURE FOR COACHING FOR CEOS: Pre-session check-in and questionnaire and assessment Mindset Analysis and introspection testing Psychological analysis Follow up for feedback and well-being and progress check-up calls Accountability Coaching Anxiety Coaching Target-driven coaching helpful for individuals with procrastination issues or issues tackling challenging career goals Leadership Coaching and Self-belief Coaching Organizational objective coaching Bring awareness to self-talk and unconscious biases 24/7 ACCESS TO YOUR COACH Coach available on Whatsapp, Phone, Zoom, and Face to Face CEO Coaching helps coach the world’s best CEOs, executives, entrepreneurs, and companies to increase revenue and grow their business. Our coaches have extensive real-world experience in overcoming the challenges, inherent in entrepreneurship and executive leadership. Consult with a CEO coach today to receive a customized business plan that will enable you to achieve extraordinary results. We work with you by understanding the business issues and strategic imperatives of the enterprise. We then use a combination of 360 feedback (including Board members) and formal assessment tools to ensure we have a clear picture of you as an individual leader and the environment in which you need to create success. We assess your team and work with you to understand where you’ve got the capability and where the team may be vulnerable. https://relationshipsmdd.com/product/coaching-for-ceos-package/

MySQL Performance & Tuning training course description This MySQL Performance & Tuning course is designed for Database Administrators, Application Developers and Technical Consultants who need to monitor and tune the performance of MySQL servers and databases. The course provides practical experience in monitoring and tuning MySQL servers and databases. Note: This MySQL Performance & Tuning course does not cover clustering (other than at overview level), replication or non-standard storage engines such as Falcon and PBXT. What will you learn Develop a monitoring and tuning plan Use server configuration and status variables. Identify and improve problem queries. Make efficient use of indexes. Monitor and size memory caches and locks. Tune the MyISAM and InnoDB storage engine. Evaluate the use of partitioning for performance. MySQL Performance & Tuning training course details Who will benefit: Anyone who wishes to monitor and tune MySQL performance. Prerequisites: Delegates must have a working knowledge of MySQL Database Administration Duration 3 days MySQL Performance & Tuning training course contents Introduction to performance tuning Tuning overview, Resolving performance issues, Recommended approach to tuning, Items to evaluate, Where to look, Planning a monitoring routine, Building a new database for performance, Tuning an existing database, Setting suitable goals. MySQL performance tuning tools Administration tools, the information schema, performance-related SHOW commands, benchmarking tools, the MySQL performance schema, MonYog. Hands on Obtaining performance information. Schema design Normalisation, de-normalisation, naming conventions, load generation, stress testing and benchmarking tools, selecting data types, data types, character sets, choosing storage engines. Hands on effects of design on performance. Statement tuning Overview of statement tuning, identifying problem queries, the optimizer, explain, explain extended. Hands on identifying problem queries and using explain. Indexes Index overview, Types of index, Index tuning, Indexes and joins. Hands on Indexes and performance. Server configuration and monitoring Server configuration variables, server status variables, table cache, multi-threading, connection issues, query cache. Hands on setting and interpreting server variables and caching. Locking Types of locking, locking and storage engines, effects of locking on performance. Hands on locking and performance. The InnoDB engine Transactions, crash recovery, locking, monitoring InnoDB, caches and buffers, configuring data files, configuring the log files. Hands on InnoDB configuration and performance. Other storage engines MyISAM engine, merge engine, archive engine, memory engine, blackhole engine, CSV engine, the Spider engine, the ColumnStore engine, the MyRocks engine, mixing sorage engines. Hands on storage engine performance. Overview of clustering and performance Advantages of performance, advantages of clustering, performance issues and clustering, the NDBCluster engine, the Galera cluster, the Percona XtraDB cluster, MySQL InnoDB cluster, the federated engine, the federatedX engine, overview of other high availability techniques. NOSQL and Mencached overview. Dumping and loading data SQL statements versus delimited data, parameters affecting dump performance, parameters affecting load performance. Hands on dump and load performance. Partitioned tables Partitioned tables concepts, range partitioning, hash partitioning, key partitioning, list partitioning, composite partitioning or subpartitioning, partition pruning. Hands on partitioned table performance.

PRINCE2 Practitioner: In-House Training
By IIL Europe Ltd
PRINCE2® Practitioner : In-House Training Projects fail for a variety of reasons including poor planning, lack of defined quality criteria, poor understanding of the business drivers, inadequate control, and lack of senior management involvement in other words, lack of a structured best practice approach to project delivery. PRINCE2® (6th Edition is the current version) is a structured, process-based approach for project management providing a methodology which can be easily tailored and scaled to suit all types of projects. It is the de facto standard for project management in the UK Government and is also used extensively in more than 150 countries worldwide with in excess of 20,000 organizations already benefitting from its powerful approach. It can be used easily in combination with PMI®'s PMBOK® Guide to provide a robust project methodology, or to augment an existing PMBOK®-based methodology with additional rigor around areas such as Quality, Organization, and Benefits Realization. The goals of this course are to take participants to the next level of understanding and application of the PRINCE2® methodology and to prepare them to sit the Practitioner exam. Using APMG provided sample exam papers and additional project case studies, participants will learn how to apply what they learned during the Foundation course and how to approach the OTE Practitioner exam, which is aimed at testing their ability to apply PRINCE2® in an actual project environment simulated via a case study provided as part of the exam. What you will Learn You'll learn how to: Tailor and apply the principles, themes, process structure, techniques, and management products of PRINCE2® within a work environment, via carefully selected case studies Define the PRINCE2® 6th Edition method at the Practitioner level Prepare for and take the Practitioner exam Getting Started Introductions Course structure Course goals and objectives Tailoring PRINCE2® Tailoring PRINCE2® Adopting PRINCE2® Tailoring PRINCE2® to suit different projects Adopting PRINCE2® in an organizational environment Controlled Start Recap management products Study business case and risk Study activities and responsibilities in: Starting up a project Initiating a project Controlled Progress Study management products and risk Study activities and responsibilities in: Getting work done Monitoring and reporting Issues and escalation Controlled Close Study Activities and Responsibilities in Closing a Project Activities and roles Roles and Responsibilities Principles Exercise Product-basedPlanning Producing a product breakdown structure (PBS) Producing a product flow diagram (PFD) Linking product breakdown structures and product flow diagrams to product descriptions

Linux training course description A Linux foundation appropriate for all flavours of Linux, focussed on getting network engineers up and running with Linux. The command line is used throughout. The course progresses from the basics of Linux commands onto useful tools such as grep, then shell features such as piping and then onto shell scripting. Administration aspects covered are the tasks network engineers are most likely to encounter such as software installation. Hands on exercises concentrate on network related tasks such as installing net-snmp and using shell scripts to provide network automation. What will you learn Use Linux commands to perform a variety of tasks from manipulating files to handling processes. Create and edit files with vi. Work with permissions. Write simple shell scripts. Install software packages. Configure base networking. Linux training course details Who will benefit: Network engineers. Prerequisites: TCP/IP Foundation Duration 5 days Linux training course contents What is Linux? Linux distributions, open source software. Getting started Logging in, changing passwords, logging out. Hands on Basics and root access. Linux basics Command structure. The Linux manuals, basic commands (who, date, tty, uname, echo, banner...). Hands on Using the CLI. Connecting to a network IP configuration, DHCP, static addressing, routing, ifconfig, ping, netstat, traceroute, dig. Hands on Network configuration and testing. Managing Software Package Concepts, Comparison of package formats, RPM, rpm Commands, Yum, Debian Packages, dpkg, apt-cache, apt-get, dselect, aptitude, Converting Between Package Formats, Dependencies and Conflicts, Startup Script Problems, Shared Libraries, Library Management Hands on Installing network packages such as nmap and net-snmp. Processes and log files ps, kill, background processes, at, exec, priorities. Managing Linux log files. Syslogd. Setting the time. Cron and cronjobs. Managing Processes, the Kernel: The First Process. Hands on Controlling daemons and services. Setting up a TFTP server. Filesystem commands Home directories, manipulating files and directories, Filesystem layout, Pathnames, hard and symbolic links. Viewing files. Hands on Exploring the filesystem, working with network device configuration files. The Linux editors ed, vi, shell escapes, .exrc. Hands on Editing network device configuration files. Extracting data from files grep, find, cut, sort and paste⦠Hands on Working with syslog files. Permissions Theory, chmod, chown, newgrp. Hands on Handling permission problems. The shell Metacharacters, piping and redirection. Hands on Running SNMP commands and working with their output. Basic shell scripting What are shell scripts? Simple scripts, control structures. Variable. Setting variables, using variables, set, scope, export, sourcing, environmental variables, read. Positional parameters: $0 to $9, $#, $* and others. shift parameter substitution. Control statements: The test command, if , while loops, for loops, the case statement. Hands on Automating network tasks. Customising your environment Environmental variables, stty, .profile and other startup files. Hands on Customising Linux. Introduction to administration The root user, su. Managing users and groups. Hands on The power of root. Archiving files Backups, tar, cpio, dd, gzip. Hands on Working with tar files. Booting Linux and Editing Files Installing Boot Loaders, GRUB Legacy, GRUB 2, Alternative Boot Loaders, the Boot Process, Boot Messages, Runlevels and the Initialization Process, Runlevel Functions, Runlevel Services, Alternative Boot Systems , Upstart, system. Hands on Installing network services on Linux.

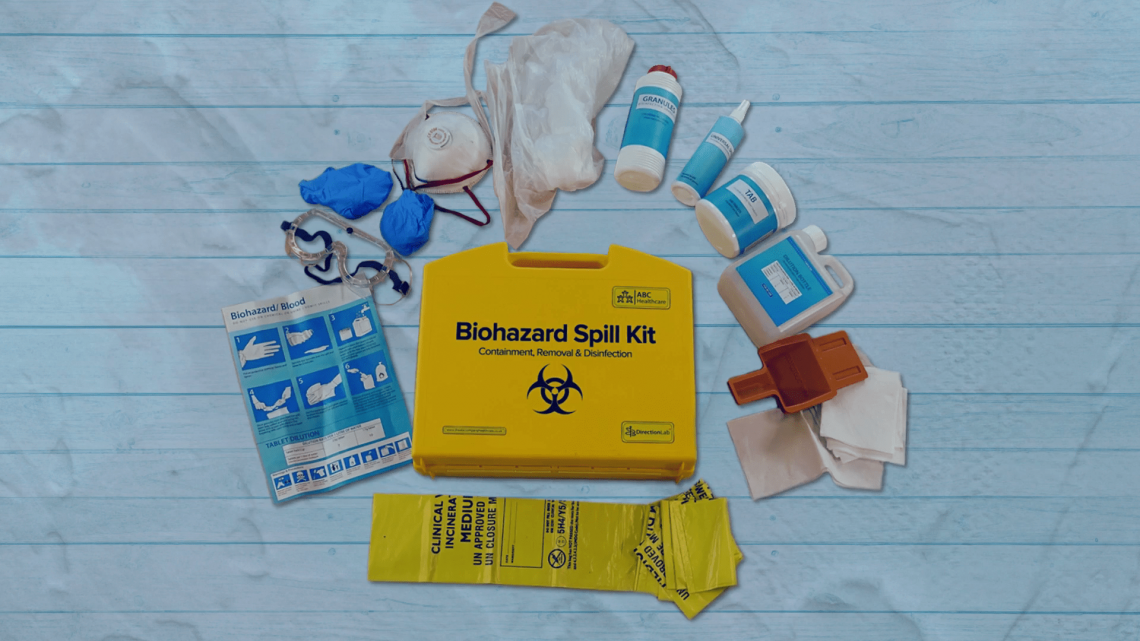
Biohazard Safety: Managing Blood and Body Fluid Spillages Instructor
By Guardian Angels Training
Gain expertise in biohazard safety with our "Biohazard Safety: Managing Blood and Body Fluid Spillages Instructor Training" course. Ideal for healthcare professionals, lab staff, and emergency responders.
M.D.D RELATIONSHIP COURSE EXPRESS PACKAGE (DATING/RELATIONSHIP COURSES)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
Learning how to have a better relationship Introspection test Learn where you are going wrong Love language testing Learn about boundaries Establishing your relationship needs Address past negative relationship patterns Learn about boundaries Relationship facets relationship course 2-hour session relationship training and 1 phone call 30 mins Coaching and relationship skills education https://relationshipsmdd.com/product/relationship-course-express-package/

An Understanding of Venepuncture (Adult or Child as applicable)
By Guardian Angels Training
Gain comprehensive knowledge and practical skills for safe and effective venepuncture procedures in adult patients with our "Understanding Adult Venepuncture Techniques" course. Perfect for healthcare professionals seeking to confidently perform venepuncture with accuracy and patient comfort.

UNIX system administration training course description This five day hands on course provides a comprehensive coverage of core UNIX administration tasks. The course covers generic UNIX and is available for any UNIX distribution required. What will you learn Administer & configure UNIX systems. Maintain UNIX by handling disk space and taking regular backups. Manage software packages. Perform basic troubleshooting. Maintain a secure UNIX system. Describe the organisation and implementation of the filesystem. UNIX system administration training course details Who will benefit: System administrators Network administrators. Prerequisites: UNIX fundamentals. Duration 5 days UNIX system administration training course contents Part 1 Exploring UNIX command-line tools Using a shell, shell configuration, environment variables, getting help, streams, redirection and pipes, processing text using filters, manipulating files, regular expressions, grep, sed. Managing software Package concepts, comparison of package formats, RPM, rpm commands, yum, dpkg, apt-cache, apt-get, dselect, aptitude, converting between package formats, dependencies and conflicts, startup script problems, shared libraries, library management, managing processes, the kernel: the first process, process lists, foreground & background processes, process priorities, killing processes. Configuring hardware Configuring firmware and hardware, RQs, I/O addresses, DMA addresses, Boot disks, coldplug and hotplug devices, configuring expansion cards and PCI cards, kernel modules, USB devices, UNIX USB crivers, configuring hard disks, partitioning systems, LVM, common layouts, creating partitions and filesystems, maintaining filesystem health, tuning, journals, checking filesystems, monitoring disk use, mounting and unmounting filesystems. Managing files File management commands, file naming and wildcards, file archiving, links, directory commands, file ownership and group, file access control, permissions, chmod, defaults, file attributes, disk quotas, enabling and setting quotas, locating files, the FHS. Booting UNIX and editing files Installing boot loaders, GRUB legacy, GRUB 2, alternative boot loaders, the boot process, boot messages, runlevels and the initialization process, runlevel functions, runlevel services, alternative boot systems, upstart, system. Part 2 Configuring the X window system Localization, configuring basic X features, X server options, methods of configuring X, X display information, X fonts, the X GUI login system, XDMCP server, using X for remote access, screen display settings, setting your time zone, your locale, configuring printing, conceptualizing the UNIX printing architecture, understanding PostScript and ghostscript, running a printing system, configuring CUPS, monitoring and controlling the print queue. Administering the system Managing users and groups, tuning user and system environments, using system log files, understanding syslogd, setting logging options, manually logging data, rotating l;og files, reviewing log file contents, maintaining the system time, UNIX time concepts, manually setting the time, using NTP, running jobs in the future, understanding the role of cron, creating system cron jobs, creating user cron jobs, using anacron, using at. Configuring basic networking TCP/IP, network hardware, network addresses, hostnames, network ports, configuring UNIX for a local network, configuring with DHCP, static IP address, configuring routing, using GUI configuration tools, ifup and ifdown, diagnosing network connections, testing connectivity, tracing a route, checking network status , examining network traffic, additional tools. Writing scripts, configuring email, and using databases The shell environment, aliases, shell configuration files, writing scripts, commands, variables, conditional expressions, loops, functions, managing email, choosing email software, securing your email server, managing data with SQL, picking a SQL package, understanding SQL basics, using MySQL. Securing your system Administering network security, super server restrictions, disabling unused servers, administering local security, securing passwords, limiting root access, setting login, process, SUID/SGID files, configuring SSH, using GPG, generating, importing and revoking keys, encrypting and decrypting data, signing messages and verifying signatures.

Search By Location
- Testing Courses in London
- Testing Courses in Birmingham
- Testing Courses in Glasgow
- Testing Courses in Liverpool
- Testing Courses in Bristol
- Testing Courses in Manchester
- Testing Courses in Sheffield
- Testing Courses in Leeds
- Testing Courses in Edinburgh
- Testing Courses in Leicester
- Testing Courses in Coventry
- Testing Courses in Bradford
- Testing Courses in Cardiff
- Testing Courses in Belfast
- Testing Courses in Nottingham