- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
231 Spill courses
Boost Your Career By Enrolling On This House Cleaning Course To Get Through Challenging Moments! Get FREE 1 QLS Endorsed Certificate Course with 10 Additional CPDQS Accredited Bundle Courses In A Single Payment. If you wish to gain a solid and compact knowledge of House Cleaning and boost yourself for your desired career, then take a step in the right direction with this industry-standard, comprehensive Bundle designed by professionals. This bundle package includes 1 premium, The Quality Licence Scheme-endorsed course, 10 additional CPD accredited certificate courses, with expert assistance, and a FREE courses assessment included. Learn a range of in-demand technical skills to help you progress your career with 12 months of unlimited access to this bundle of courses. If you enrol in this package, you will not be charged any extra fees. This House Cleaning Bundle Package Includes: Course 01: Diploma in Housecleaning at QLS Level 4 10 Additional CPDQS Accredited Premiums Courses- Course 01: Housekeeping Training Course Course 02: Personal Hygiene Course Course 03: Infection Control Course 04: Food Safety & Hygiene Level 2 Course 05: Spill Management Training Course 06: Electrical Safety Course 07: Fire Risk Assessment with Health and Safety Training Course 08: Coronavirus Awareness Course 09: Basic First Aid Course 10: Working at Height Success becomes a lot simpler with this Bundle package, which allows you to monetise your skills. This Bundle is appropriate for both part-time and full-time students, and it can be completed at your own pace. This premium online bundle course, named House Cleaning, supports your professional growth with Quality Licence Scheme endorsement, as well as CPDQS accreditation. You'll be able to practice on your own time and at your own speed while still gaining an endorsed certificate. You'll get an unrivalled learning experience, as well as a free student ID card, which is included in the course price. This ID card entitles you to discounts on bus tickets, movie tickets, and library cards. With this high-quality Package, all students have access to dedicated tutor support and 24/7 customer service. Throughout the extensive syllabus of this package, you'll find the required assistance and also answers to all of your questions. The course materials of are designed by experts and you can access these easily from any of your smartphones, laptops, PCs, tablets etc. Master the skills to arm yourself with the necessary qualities and explore your career opportunities in relevant sectors. Why Prefer this Bundle Course? Upon successful completion of the Bundle, you will receive a completely free certificate from the Quality Licence Scheme. Option to receive 10 additional certificates accredited by CPDQS to expand your knowledge. Student ID card with amazing discounts - completely for FREE! (£10 postal charge will be applicable for international delivery) Our bundle's learning materials have engaging voiceover and visual elements for your convenience. For a period of 12 months, you will have 24/7 access to all bundle course material. Complete the Bundle, at your own pace. Each of our students gets full 24/7 tutor support After completing our Bundle, you will receive efficient assessments and immediate results. Start your learning journey straight away with this Bundle and take a step toward a brighter future! *** Course Curriculum: *** Our bundle has the following curriculum: Course 01: Diploma in Housecleaning at QLS Level 4 Module 01: Introduction to House Cleaning A Clean House Plan of Action What to Clean When The Daily Cleaning Routine Summary Module 02: Cleaning Equipment and Ingredients Cleaning Equipment Basic Cleaning Ingredients Cleaning with Essential Oils Safety Tips: Buying Retail Cleaning Products Summary Module 03: Cleaning the Kitchen Washing the Dishes The Kitchen Sink Oven Cleaners Cleaning Kitchen Surfaces Refrigerator & Freezer Rescue Cabinet Cleaner The Kitchen Floor Summary Module 04: Cleaning the Bedroom and Living Room Getting Started with Bedroom Cleaning the Living Room Natural Cleansers for Bedroom and Living Room Summary Module 05: Bathroom Cleaning Getting Started Tiles Sink Toilet Floor Natural Cleansers for Bathroom Helpful Hints for the Bathroom Summary Module 06: Cleaning and Organising a Kid's Room Organising Kids Room Cleaning Toys Cleansers Summary Module 07: Cleaning Home Office Cleaning the Computer Equipment When Cleaning Electronics Plants in the Working Space Spritz Away Burnout Fritz Clear the Air Room Spritzer Summary Module 08: Cleaning Walls Keeping Walls Clean Safe & Simple Wall Formulas The Floor-To-Ceiling Solution Helpful Hints for Cleaning Walls Summary What is the Bundle Assessment Process? We offer an integrated assessment framework to make the process of evaluation and accreditation for learners easier. You have to complete the assignment questions given at the end of the Bundle and score a minimum of 60% to pass each exam. Our expert trainers will assess your assignment and give you feedback after you submit the assignment. You will be entitled to claim a certificate endorsed by the Quality Licence Scheme after you have completed all of the Diploma in Housecleaning at QLS Level 4 exams. CPD 220 CPD hours / points Accredited by CPD Quality Standards Who is this course for? The Package training is perfect for highly motivated people who want to improve their technical skills and prepare for the career they want! This package is also ideal for those who want to learn more about this subject in-depth and stay up to date with the latest details. From the comfort of your own home, study the House Cleaning package and expand your professional skillset! Requirements The Bundle has no formal entry criteria, and everyone is welcome to enrol! Anyone with a desire to learn is welcome to this course without hesitation. All students must be over the age of 16 and have a passion for learning and literacy. You can learn online using any internet-connected device, such as a computer, tablet, or smartphone. You can study whenever it's convenient for you and finish the House Cleaning bundle package at your own speed. Career path The bundle course aims to help you get the job or even the long-awaited promotion of your dreams. With the support and guidance of our package, you will learn the skills and knowledge that are important to your career. Certificates Certificate Accredited by CPDQS Digital certificate - Included Upon passing the House Cleaning Bundle, you need to order to receive a Digital Certificate for each of the courses inside this bundle as proof of your new skills that are accredited by CPDQS. Diploma in Housecleaning at QLS Level 4 Hard copy certificate - Included Show off Your New Skills with a Certificate of Completion After successfully completing the Diploma in Housecleaning at QLS Level 4, you can order an original hardcopy certificate of achievement endorsed by the Quality Licence Scheme. The certificate will be home-delivered, with completely free of charge in this package. For Additional Courses, You have to pay the price based on the Level of these Courses Endorsed by The Quality Licence Scheme. Level 1 - £59 Level 2 - £79 Level 3 - £89 Level 4 - £99 Level 5 - £119 Level 6 - £129 Level 7 - £139 Certificate Accredited by CPDQS 29 GBP for Printed Hardcopy Certificate inside the UK 39 GBP for Printed Hardcopy Certificate outside the UK (international delivery)

Cleaning at QLS Level 7 Advanced Diploma - 12 Courses Bundle
By NextGen Learning
Are you looking to elevate your professional skills to new heights? Introducing our Advanced Diploma in Cleaning at QLS Level 7, a QLS-endorsed course bundle that sets a new standard in online education. This prestigious endorsement by the Quality Licence Scheme (QLS) is a testament to the exceptional quality and rigour of our course content. The bundle comprises 11 CPD-accredited courses, each meticulously designed to meet the highest standards of learning. This endorsement not only highlights the excellence of our courses but also assures that your learning journey is recognised and valued in the professional world. The purpose of Advanced Diploma in Cleaning at QLS Level 7 is to provide learners with a comprehensive, skill-enriching experience that caters to a variety of professional needs. Each course within the bundle is crafted to not only impart essential knowledge but also to enhance practical skills, ensuring that learners are well-equipped to excel in their respective fields. From gaining cutting-edge industry insights to mastering critical thinking and problem-solving techniques, this bundle is an amalgamation of learning experiences that are both enriching and empowering. Moreover,Advanced Diploma in Cleaning at QLS Level 7 goes beyond just online learning. Upon completion of the bundle, learners will receive a free QLS Endorsed Hardcopy Certificate & 11 CPD Accredited PDF Certificate, a tangible acknowledgement of their dedication and hard work. This certificate serves as a powerful tool in showcasing your newly acquired skills and knowledge to potential employers. So, why wait? Embark on this transformative learning journey today and unlock your potential with Advanced Diploma in Cleaning at QLS Level 7! QLS Endorsed Course: Course 01:Advanced Diploma in Cleaning at QLS Level 7 CPD QS Accredited Courses: Course 02: Housecleaning Course 03: Oven Cleaning Training Course Course 04: Organic Cleaning Products For A Clean Green Home Course 05: DIY Home Improvement Course 06: Pool Maintenance Course 07: Carpet Cleaner Course 08: Handyperson/Handyman Course 09: Spill Management Training Course 10: Personal Hygiene Course 11: Infection and Prevention Control Course 12: Online Workplace First Aid Learning Outcomes Upon completion of the bundle, you will be able to: Acquire industry-relevant skills and up-to-date knowledge. Enhance critical thinking and problem-solving abilities. Gain a competitive edge in the job market with QLS-endorsed certification. Develop a comprehensive understanding of the Cleaning industry. Master practical application of theoretical concepts. Improve career prospects with CPD-accredited courses. The Advanced Diploma in Cleaning at QLS Level 7 offers an unparalleled learning experience endorsed by the Quality Licence Scheme (QLS). This endorsement underlines the quality and depth of the courses, ensuring that your learning is recognised globally. The bundle includes 11 CPD-accredited courses, each meticulously designed to cater to your professional development needs. Whether you're looking to gain new skills, enhance existing ones, or pursue a complete career change, this bundle provides the tools and knowledge necessary to achieve your goals. The Quality Licence Scheme (QLS) endorsement further elevates your professional credibility, signalling to potential employers your commitment to excellence and continuous learning. The benefits of this course are manifold - from enhancing your resume with a QLS-endorsed certification to developing skills directly applicable to your job, positioning you for promotions, higher salary brackets, and a broader range of career opportunities. Embark on a journey of professional transformation with Advanced Diploma in Cleaning at QLS Level 7 today and seize the opportunity to stand out in your career. Enrol in Cleaning now and take the first step towards unlocking a world of potential and possibilities. Don't miss out on this chance to redefine your professional trajectory! Certificate of Achievement: QLS-endorsed courses are designed to provide learners with the skills and knowledge they need to succeed in their chosen field. The Quality Licence Scheme is a distinguished and respected accreditation in the UK, denoting exceptional quality and excellence. It carries significant weight among industry professionals and recruiters. Upon completion, learners will receive a Free Premium QLS Endorsed Hard Copy Certificate titled 'Advanced Diploma in Cleaning at QLS Level 7' & 11 Free CPD Accredited PDF Certificates. These certificates serve to validate the completion of the course, the level achieved, and the QLS endorsement. Please Note: NextGen Learning is a Compliance Central approved resale partner for Quality Licence Scheme Endorsed courses. CPD 180 CPD hours / points Accredited by CPD Quality Standards Who is this course for? The Advanced Diploma in Cleaning at QLS Level 7 bundle is ideal for: Professionals seeking to enhance their skills and knowledge. Individuals aiming for career advancement or transition. Those seeking CPD-accredited certification for professional growth. Learners desiring a QLS-endorsed comprehensive learning experience. Requirements You are cordially invited to enroll in this bundle; please note that there are no formal prerequisites or qualifications required. We've designed this curriculum to be accessible to all, irrespective of prior experience or educational background. Career path Upon completing the Advanced Diploma in Cleaning at QLS Level 7 course bundle, each offering promising prospects and competitive salary ranges. Whether you aspire to climb the corporate ladder in a managerial role, delve into the dynamic world of marketing, explore the intricacies of finance, or excel in the ever-evolving field of technology. Certificates CPD Quality Standard Certificate Digital certificate - Included Free 11 CPD Accredited PDF Certificates. QLS Endorsed Certificate Hard copy certificate - Included

Workplace Safety- Asbestos & COSHH Training
By NextGen Learning
Course Overview This comprehensive Workplace Safety – Asbestos & COSHH Training course is designed to equip learners with essential knowledge of hazardous substances, safety regulations, and risk assessment procedures. It covers critical subjects such as asbestos awareness, COSHH regulations, fire safety, and chemical spill response, empowering individuals to uphold safety standards in any professional environment. Whether you're new to workplace safety or looking to reinforce your compliance knowledge, this course ensures you understand how to identify, report, and manage potential hazards in line with UK health and safety legislation. By completing this training, learners will gain the confidence to support a safer workplace, meet employer and legal requirements, and contribute to a healthier work culture across sectors such as construction, manufacturing, education, and care. This course is also valuable for those pursuing roles with responsibility for safety assessments or compliance monitoring within their organisation. Course Description The Workplace Safety – Asbestos & COSHH Training course offers in-depth guidance on handling hazardous materials and navigating high-risk scenarios. Topics include the dangers and regulations surrounding asbestos, COSHH assessments, confined space awareness, chemical spill response, and essential workplace first aid. Additionally, learners will study broader workplace health and safety practices, ensuring a well-rounded understanding of legislative duties, hazard control, and preventative measures. Throughout the course, learners will develop the ability to interpret health and safety protocols, implement best practices, and support regulatory compliance. The training is aligned with UK industry requirements, offering insights into effective safety planning and emergency procedures. This course suits both those with responsibilities in health and safety and those looking to improve their knowledge to support safe operational standards in various workplace settings. Course Modules: Module 01: Asbestos Awareness & Safety Module 02: COSHH Training for Assessors Module 03: Working in Confined Spaces Module 04: Chemical Spill Module 05: Spill Management Training Module 06: Fire Safety Module 07: Workplace Health and Safety Diploma Module 08: First Aid at Work (See full curriculum) Who is this course for? Individuals seeking to understand health and safety obligations in the workplace. Professionals aiming to improve compliance knowledge and safety awareness. Beginners with an interest in occupational health and safety practices. Supervisors, HR personnel, and compliance officers responsible for workplace risk. Career Path Health and Safety Officer Compliance Coordinator Site Supervisor Risk Assessor Facilities Manager Warehouse or Construction Safety Personnel HR and Operations Manager

Offshore Marine Operations and HSE Management Navigating Safety and Efficiency in Offshore Operations for Oil, Gas, and Wind Sectors
By EnergyEdge - Training for a Sustainable Energy Future
Discover the key to safety and efficiency in offshore operations for oil, gas, and wind sectors with EnergyEdge's course on marine operations and HSE management.
Lifetime Access One-Time Enrolment, Lifetime Learning, Our Prime Learners will Get: Instant, Unlimited & Lifetime Access to 3000+ Courses Unlimited PDF Certificates Unlimited PDF Transcripts 1 Free Student ID card & Many More Key Highlights of the Prime Membership Lifetime Access to 3000+ Courses Get Instant Access to all courses Unlimited PDF Certificate Unlimited PDF Transcripts No Hidden Charges CPD Certification Study anytime from anywhere at your own pace 1 Free Student ID card Tutor Support Access to All Future Courses Trusted by 500+ Leading Universities and Companies Globally Some of our All Time Popular Courses: 2D Animation: Ultimate Guide to Adobe Animate Abuse Awareness & Response Training Academic and Research Skills for Business Accident Investigation Accident Investigation training – Documentation and Solution Accountancy Accounting – Income statement and Balance Sheet Accounting and Finance Accounting Skills for New Supervisors Active Listening ADHD Awareness Admin, Secretarial & PA Administrative Management Administrative Management – Meeting and Conference Adobe Acrobat 7 Adobe Acrobat 8 Pro Adobe After Effects: Learn to Use Shape Tools Advanced Diploma in Anger Management Advanced Diploma in Customer Service Advanced Diploma in Psychology Advanced Diploma in Sales Management Advanced Management Diploma Advanced Safeguarding Children (Level 2 Safeguarding) Agricultural Science Agricultural Science – Aquaculture and Permaculture Agricultural Science – Home Gardening and Animal Farming Agricultural Science – Soil Science and Plant Nutrition Airport Operations Course Level 3 Allergen Awareness – Online Training Alternative Medicine – Energy Therapies An Environmental Audit Primer Anaesthetist Training Anaphylaxis and Basic Life Support (CSTF) Animal Care Level 3 Course Animal Nutrition Animal Science Animal Science – Disease and Medicine Anti Social Behaviour Anxiety in Children and Young People during COVID-19 Arboriculture Arboriculture – Equipment and Operation Archaeology Archaeology – Excavation and Documentation Archaeology – Surveying and Feature Architectural Studies Arts Management Arts Management – Leadership and Entrepreneurship Arts Management – Marketing and Fundraising ASP.NET Core MVC Webforms – Build Real Projects Asp.Net Webforms from Scratch for Beginners Asperger Syndrome Awareness Asperger Syndrome Awareness Assessing Mental Capacity Certificate Course Assessment in Education and Training Attention Management Diploma Audiology Audiology – Acoustics and Psycho-acoustics Augmented Reality Autism Awareness Automated External Defibrillator (AED) – Online Training Aviation Law Training Ayurveda – Daily routine, Exercise & Yoga Ayurveda Diploma Course Baker Baking -Techniques and Recipes Baking & Cake Decorating Online Diploma Course Baking and Equipment for Beginner Banksman Essentials Training Basic Biology Basic Bricklaying Training Basic Business Management – Boot Camp for Business Owners Basic C# Coding Basic Cardiac (Heart) Care Basic Electricity – Voltage, Capacitance and Capacitors Basic English Masterclass Basic Fire Safety Training Basic Life Support Basic Principles of Health Care Delivery Basics of Dog Grooming Basics of Process Planning Beginner Bike Maintenance Behaviour That Challenges in Children Bicycle Training for Beginners Bicycle- Parts and Maintenance Big Data Analytics with PySpark Power BI and MongoDB Big Data Analytics with PySpark Tableau Desktop and MongoDB Biochemistry Biochemistry- Cells, Protein and Metabolism Bioinformatics Biomedical Science Biotechnology Biotechnology – Health, Industrial and Business Bipolar Disorder – Social Inclusion, Psychotherapy and Awareness Bipolar Disorder Awareness Bipolar Disorder- Mental Illness,Risk and Treatment Birth Doula Blended Learning Course for Teachers Body Language Reading Body Language as a Sales Tool Bodyguard Training Botany Brain Injury – Awareness and Prevention Branding Creating and Managing Your Corporate Brand Bread Making Bricklaying Bricklaying – Joint Finishes and Building Curved Arches British Citizeship Diploma Budgets and Managing Money Build an Amazon Affiliate E-Commerce Store from Scratch Build Animations with Adobe After Effects Building a Consulting Business Building Big Data Pipelines with PySpark MongoDB and Bokeh Building Your Own Computer Course Bullying & Harassment Training Bullying in the Workplace Business Account Manager Business Administration & Monitor Business analysis – Strategy, Planning and Monitoring Analysis Business English: Reading and Writing Business Environment Business Ethics for the Office Business Information and Effective Communication Business Intelligence Analyst Course Business Law Business Management Business Operations Business Plan Business Process Management Business Resources Maximisation Business Studies Business Team Performance C++ Programming for Absolute Beginners CAD Design – Assemblies, Modelling and Civil Drawings Cake Decorating Call Centre & Customer Service Training Course Call Centre Training Canadian Tax Accounting Candle Making Business Diploma – Level 3 Canine Communication Car Mechanic Car Mechanic Training for Beginners Carbon Literacy Knowledge Care Planning and Record Keeping | Health & Safety Online Course Career Coaching Level 3 Career Development and Passion Carpentry Carpentry – Floor, Wall, Window sand Roof Framing Cash Flow Management Basics Cat Psychology and Training Catering Management Cattery Management Causes & Spread of Infection CCTV Operator Course CDM Awareness Training Course Central Banking Monetary Policy Cerebral Palsy Awareness Cerebral Palsy- Child, Care Planning and Treatment Certificate in Teacher Training Change Management Change Management – Change and How to Deal With It Character Rigging and 2D Animation in Toon Boom Character Rigging in Toon Boom Harmony Chemical Spill Child and Adolescent Mental Health Child and Adolescent Mental Health – Problems and Treatment Child Development Child Development and Well-being Child Health & Communication Development Child Language Disorder (CLD) Child Neglect Awareness Certificate Course Child Playwork Child Protection Annual Refresher Child Protection Officer Child Sexual Exploitation and Interventions Chocolate Making Cleaning, Decontamination and Waste Management Clinical Coding – Online Course Clinical Governance Course – Level 3 Clinical Governance Fundamentals Clinical Governance in Adult Care Clinical Observation – Medicine, Health Safety and Hygiene Clinical Observations Skills Clinical Psychology Coaching and Mentoring in Care Code with Python: Learn Classes, Methods and OOP Cognitive Behavioural Therapy (CBT) Practitioner Certificate Course Commercial Law Commercial Management Commercial Management – Cash Flow, Negotiation and Agreements Communication & Information Handling in Care Communication Skills in Health and Social Care Communications for Small Business Owners Complete Communication Skills Master Class for Life Complete Microsoft SQL Server from Scratch: Bootcamp Complete Python from Scratch: Start your career in Python 3+ Compliance Management Concierge Concierge – Work Environment and Etiquettes Concussion and Brain Injury Awareness Conference and Event Management Confidence Building Training Conflict Management – Crisis and Risk Assessment Conflict Resolution Consent Training in Healthcare Course Conservation Diploma Course Construction Cost Estimation Construction Safety Consumer Rights Awareness Contemporary Issues in Education Content Management Content Management – Content Strategy and Content Marketing Continuous Improvement with Lean Control and Administration of Medicines Online Training Course Conversational Leadership Conveyancing- Online Diploma Course Copyediting & Proofreading Copywriting – Online, Press and Print Media Copywriting Copywriting for Mainstream Media Corporate Finance – Profitability in a Financial Downturn Corporate Finance: Profitability in a Financial Downturn Corporate Process & Maintenance Corporate Risk And Crisis Management – Online Course Corporate Social Responsibility (CSR) Cosmetology Cost, Revenue & Tax Counselling – Family, Children and Adolescents Counselling Counselling and Psychotherapy Couples Therapy- Affairs and Conflict Resolution Couples Therapy/Marriage Counselling Covid 19 – Psychological First Aid Covid 19- Impacts and Psychological Aid COVID-19 Critical Care: Understanding and Application COVID-19: Psychological First Aid Covid19 Awareness Diploma for Healthcare Assistant Create Amazing Daromas in Maya Create Smart Maps in Python and Leaflet Creating Children’s Room Creating Successful Staff Retreats Creative Thinking and Innovation Creative Writing Criminal Investigator Criminal Law Crisis Communication for HR Crisis Communication for HR Crisis Management Critical Thinking: Implications for Leadership Crochet for Beginners Cross-Cultural Awareness Training CSR Policies & Supply Chain Management Customer Relationship Management Customer Relationship Management (CRM) – Customer Complaints and Relationship Customer Service & Environment Customer Service Training – Managing Customer Service Cyber Law Online Course Cycling Training Dangerous Substances and Explosive Atmospheres Regulations (DSEAR) Training Data Analytics Data Entry Administrator Training Deaf Awareness Decision Making and Critical Thinking Decision Making in High Stress Situations Delivery Manager Dementia Awareness Dementia Care & Management Dental Assistant Dental Assistant Training – Radiology , Infection Control and Instruments Dermatology Dermatology – Acne and Its Remedies Develop Big Data Pipelines with R & Sparklyr & Tableau Develop Big Data Pipelines with R, Sparklyr & Power BI Develop Smart Maps with Python and Leaflet – Windows Version Developing a Lunch and Learn Program Developing a Training Needs Analysis Developing Interpersonal Skills Course Developing Quality Customer Service Skills Developing Your Executive Presence Developing Your Training Program Diabetes Awareness Diabetes Management & Balanced Diet Diet and Nutrition – Healthy and Ketogenic Diet Diet and Nutrition Diploma Diet and Nutrition for Animals Diet and Nutrition for Pregnancy, Adults and Various Groups Digital Communication and Business Digital Marketing for Business Digital Marketing Growth Hacking Techniques Online Course Digital Product Management Diploma in Alternative Medicine Diploma in Basic Chemistry Level 3 Diploma in Business Management: Corporate Behaviour Diploma in Business Proposal Writing Diploma in Effective Writing Skills Diploma in Event Management Diploma in Forex Trading Diploma in Meeting Management Diploma in Occupational Therapy Diploma in Performance Management Diploma in Personal Branding Diploma in Pharmacy Skills Diploma in Recruitment Management Diploma in Social Work Studies Diploma in Water Chemistry Diploma in Water Treatment Diploma in Workplace Safety Disability & SEN Disability Assessor Training Disability Awareness & Inclusion Training Disability Awareness: Working with people with Disability Diversity and Equality in Workplace Diversity and Equality in Workplace Level 3 Diversity Training Diversity Training – Online Course DIY Home Improvement DNA and Genealogy Course Document Control – Strategies and Instruments Dog Agility Dog Agility- Tunnels, Jumps and Agility and Health Dog Care and Grooming Dog Cleaning Dog Health Care Dog Parasite Care Domestic Appliances Repairing Course Domestic Violence – Risks and Abuses on Children Domestic Violence and Abuse Awareness Diploma Domiciliary Care Support Worker Door Supervising Drama Therapy Dream Analysis and Interpretation Driver Safety Awareness Driving Instructor Driving Instructor- Learning and Driving Large Vehicles Drugs and Alcohol Awareness Training DSE Training (Display Screen Equipment) Duty of Care & Safety Responsibilities Dyslexia Awareness Dysphagia Awareness Early Years Supervision Ecosystem and Wildlife Conservation EDI in adult care Education and Pedagogy Effective Communication with Children Effective Partnership in The Learning and Teaching Context Effective Planning and Scheduling Effective Remote Working Training EFT – Emotional Freedom Technique Egyptology Egyptology- Architecture, Government and Society Email Marketing for Beginners Email Writing Training Emergency Care Worker Emergency First Aid at Work – Annual Refresher Emotional Freedom Technique – Treating Children and Improving Life Emotional Intelligence – Mindfulness and Empathy Emotional Intelligence and Human Behaviour Emotional Intelligence, Mindfulness and Empathy Training Employee Hiring and Termination Training Employee Management Course: Millennial Onboarding End of Life Care Course English for Healthcare English Grammar – Articles & Nouns (Intermediate level) Entrepreneurship Diploma Entrepreneurship Training Environment Management Environmental Awareness Training Environmental Engineering Environmental Health Environmental Health – Climate Change and Health Environmental Law Epidemiology Epidemiology – Risk and Disease Prevention Epilepsy Awareness Equality, Diversity and Discrimination Equine Psychology Equine Psychology- Horse and Human Relationships Essentials of European Medical Device Regulations Event Management – Plan, Administrative and Post Event Activities Event Management and Planning Course Event Planner Event Planning – Catering, Waste Disposal and Security Executive and Personal Assistant Training Course EYFS Facilitation Skills Training Factors that Impact Life Chances of Children and Support Family Law Fashion and Lifestyle Blogger Fashion Law Online Course Fashion Store Assistant Financial Advisor Financial Analysis Financial Controller Training Financial Investigator Financial Management Financial Modelling Course – Learn Online Financial Wellness – Personal Money Management Financial Wellness: Managing Personal Cash Flow Fine Art FinTech Fire Extinguisher – Online Course Firefighter Training Firefighter Training – Evacuation & Safety First Aid at Work First Aid for Pets First Aid Trainer Course Floristry Food and Beverage Manager Food and Mood: Improving Mental Health Through Diet and Nutrition Food Hygiene and Safety Food Labelling Regulations Training Food Safety Knowledge – Microbiological, Allergenic Hazards & Control Measures Foot Health Practitioner Forensic Accounting Course Forestry Forestry – Ecosystem, Soil and Surveying Forex Trading – Technical Analysis and Managing Risk Forklift Training – Online Course Functional Skills English Functional Skills Maths Level 2 Fundamental of Botany Fundamental of Business Analysis Fundamentals of Domestic Violence & Abuse Fundamentals of Alternative Medicine Fundamentals of AutoCAD Fundamentals of Biotechnology Fundamentals of Business Analysis Fundamentals of CAD Design Fundamentals of Car Restoration Fundamentals of Carpentry Fundamentals of Change Management Fundamentals of Construction Management Fundamentals of Copywriting Fundamentals of Corporate Finance Fundamentals of Crochet Fundamentals of Customer Relationship Management (CRM) Fundamentals of Emotional Intelligence Fundamentals of Equine Psychology Fundamentals of Forex Trading Fundamentals of Gemology Fundamentals of Human Resource Audit Fundamentals of Journalism Fundamentals of Microbiology Fundamentals of Six Sigma Fundamentals of Spill Management Fundraising Garden Design Gas Safety GCSE English GDPR Gel Manicure and Nail Artist Gemology Gemology- Weight and Measurement Genetics Geology Getting Stuff Done – Personal Development Boot Camp Goal Setting and Accomplishment Course Gold Trading Good Manufacturing Practice (GMP) HACCP Level 2 Training Handling Sales Objections & Negotiating Course Handmade Soap Making Handyperson HAVS (Hand-Arm Vibration Syndrome) Training Course Health & Safety and Wellbeing in Care Health and Safety at Workplace Health and Safety for Homeworkers Health and safety in Care Health and Safety in Construction Environment Health and Safety Training for Managers and Supervisors Health Care & Risk Assessment Healthcare GDPR Basics Healthy Eating – Physical & Mental Health Heatwave: Health and Safety Tips Higher Technician in Cooking and Gastronomy Hiring for Success – Behavioral Interviewing Techniques Home Based Childcare Course – Level 3 Home Education – Assessment and Methods Home Improvement – Damp, Rots and Pests Homeopathy – Children and Women Homeopathy – Practice and Remedy Homeopathy Diploma Horticulture Hospitality and Revenue Management Hospitality Management Level 2 Hotel Revenue Management – Pricing and Forecasting Hotel Revenue Management – Strategy and Overbooking Practice Housecleaning HR Audit – Reporting, Training and Development Process HR Management: Employee Motivation HTML and CSS Coding for Beginners Human Growth and Development Human Microbial Diseases Human Resources Training – HR for the Non-HR Manager Human Rights Hydroponics Gardening Online Course Hydrotherapy Hydrotherapy – Shoulder and Lower Limb IELTS Test Preparation Import/Export https://tilcareerb2b.wpenginepowered.com/course/improving-intelligibility-in-apraxia-and-dysarthria/ Inclusive Teaching and Learning Approaches Individual & Group Learning Infection Control Infection Control & Medicine Handling Infection Prevention and Control Training Infection Spread by Person-to-Person and Sexual Contact Awareness Influence and Persuasion Information Management Information Management- Strategy and Data Protection Initial Training of Community Health Agents Inspirational Leadership Skills: Practical Motivational Leadership Insurance Agent Training Intelligence Analyst Certification Course Intermediate Economics Level 3 Intermediate Python Coding International Development Studies International Healthcare Policy International Law International Relations Interrogations And Confessions Psychology Intrapreneurship Introduction to Accident Investigation Introduction to Administrative Management Introduction to After Effects Introduction to Agricultural Science Introduction to Airport Management Introduction to Animal Science Introduction to Arboriculture Introduction to Archaeology Introduction to Arts Management Introduction to Audiology Introduction to Ayurveda Introduction to Banking – Revised Introduction to Basic Electricity Introduction to Catering Management Introduction to Cerebral Palsy Introduction to Clinical Observation Introduction to Commercial Management Introduction to Concierge Introduction to Conservation Introduction to Content Management Introduction to Counselling Introduction to Customer Relationship Management Basic Dermatology Introduction to Dermatology Introduction to Diet and Nutrition Introduction to Digital and Emerging Technologies Introduction to Diversity in Workplace Introduction to Document Control Introduction to Dog Agility Introduction to Dog Breeds and Basic Anatomy Introduction to Egyptology Introduction to Emotional Freedom Technique(EFT) Introduction to Environmental Health Introduction to Epidemiology Introduction to Event Management Introduction to Event Planning Introduction to Facility Management Introduction to Firefighter Training Introduction to Food Allergen Awareness Training Introduction to Food Hygiene and Safety Introduction to Genetics Introduction to Health Economics and Health Technology Assessment Introduction to Home Improvement Introduction to Homeopathy Introduction to Hotel Revenue Management Introduction to Hydrotherapy Introduction to Investment Banking Introduction to Kitchen Gardening Introduction to Landscape Architecture Introduction to Lean Process Introduction to Leisure Management Introduction to Maps in Folium and Python Introduction to Maps in R Shiny and Leaflet Introduction to Marriage Counselling Introduction to Medieval History Introduction to Midwifery Certificate Introduction to Minute Writing Introduction to Modern Human Resource Management – Revised Introduction to Mushroom Cultivation Introduction to Neuro Linguistic Programming Introduction to Neurology Introduction to Oil and Gas Management Introduction to Pain Management Introduction to Party Planning Introduction to Pedagogy Introduction to Podcasting Introduction to Purchasing and Procurement Introduction to Safeguarding Vulnerable Adults Introduction to Soap Making Introduction to Social Work Introduction to Social Work Introduction to Statistics Introduction to Toon Boom: Create Your First Character Introduction to Transport Management Introduction to Urology Introduction to Vaccination Introduction to VAT Introduction to Warehouse Safety Introduction to Wedding Planning Introduction to Workplace First Aid Introduction to Zoology Inventory Management – The Nuts and Bolts Investment Investment Banking Investment Banking – Merger and Acquisition Islamic Finance IT Security Basics IT skills for business Job Search Skills – Cover Letter, Personal Development and Networking Journal Therapy Journalism Journalism- Newspaper, Radio and Television Key Account Management Course Kids Party Planner Diploma Kitchen Gardening Kitchen Gardening – Soil, Bed and Planting Kitchen Gardening and Eco-Friendly Pest Management Kitchen Manager Know Your Customer (KYC) KS1 and KS2 Teaching Assistant- Complete Bundle Land Management Land Surveying Landscape Architecture Large Goods Vehicle (LGV) Lead Awareness Training Leadership and Management Course Leadership and Management Essential Skill Leadership and People Management Diploma Leadership in Teaching Leadership Skills for Supervisors – Communication, Coaching, and Conflict Leadership Skills for The Future Leading and Managing Remote Team Lean Process and Value Stream Mapping Learn 2D Animation with Adobe Animate Learn CSS Coding from Scratch Learn MySQL from Scratch for Data Science and Analytics Learning Support Assistant Learning Support Assistant Legal Advisor Training Legal Secretary and Office Skills Diploma Leisure Management Leisure Management – Planning and Marketing Lesson Planning for Teaching Level 1 Health and Safety in a Construction Environment Level 2 Certificate in Workplace Management: Civility Level 2 Certificate in Workplace Management: Harassment Level 2 Certificate in Workplace Management: Violence Level 2 Health and Safety in the Workplace Level 3 Diploma in Anatomy and Physiology of Human Body Level 3 Diploma in Business Etiquette Level 3 Diploma in Coaching & Mentoring Level 3 Diploma in Marketing Level 3 Diploma in Six Sigma & Lean Process Level 3 Diploma in Supply Chain Management Level 3 Diploma in Time Management Level 3: Public Speaking Diploma Course Library and Information Science Library and Information Science Diploma Life Coaching | Online Course Lifeguard Training Lifeguard Training – Cardiac Emergencies, First Aid & Injury Prevention Lifeguard Training Fundamentals Lifting Operations and Lifting Equipment Regulations (LOLER) Training Line Management Logistic Management Logistics and Supply Chain Management Lone Worker Safety Lone Worker Training Machine Learning for Predictive Maps in Python and Leaflet Make Money with Blogging Make Money With YouTube Management Training: How to Be a Better Boss Managing Personal Cash Flow Managing Quality and Service Delivery Managing the Virtual Workplace Manual Handling Marine Biology Course – Online Diploma Market Research & Analysis Marketing Marketing & CRM Marketing and Sales Marketing Strategies for Small Business Marriage and Family Therapy Marriage Counselling – Apology and Forgiveness Master JavaScript with Data Visualization Mastering Organizational Chaos Material Management Maternity Care Assistant Course Maximising Personal Productivity Course Maya for Absolute Beginners Mechanical Engineering Media and Public Relations Diploma Media Studies Medical & Clinical Administration Diploma Medical Law Medical Law Medical Terminology Training Medical Transcription Medical Writing Medication Awareness Training for Care Medieval History Medieval History – Art and Architecture Medieval History – Life and Means of Living Mental Health Disorders & Medication Mental Health First Aid Certification Mentee and Mentor Merchandising Meteorology Microbiology – Prokaryote and Eukaryote Diversity Microsoft Excel 2016 Part One Microsoft Excel 2016 Part Three Microsoft Excel 2016 Part Two Microsoft Excel 2016 PowerPivot Microsoft SQL Server Bootcamp 2022 Military History Minute Writing – Role and Responsibility Montessori Teaching – Fundamental Concepts & Principles Mortgage Adviser Course Motivating, Performance Managing and Maintaining Team Culture in a Remote Team Motivational Interviewing Mushroom Growing Course Mushroom Spawning and Compost Nanny Care Worker Negotiation Skills Certificate Neonatal Nursing Neurology Neurology – Assessment and Spinal Cord Disorder NLP Tools for Real Life Noise and Hearing Protection Training Novel Writing and Publishing Nursery Assistant Certificate Nursing Assistant Nutrition and Hydration Nutritional Therapy Observation Skills for Carers OCD Awareness OCD Awareness Office Administration Office Facility Management Oil and Gas Management Oil and Gas Management- Health and Safety Online Fire Safety Course Online Meeting Management Online Meeting Management Essentials Online Veterinary Medicine Course Organisation & People Management Organisational Change & Effective Planning Organisational Skills Course for Administrator Ornithology Oven Cleaning Training Course Oxygen First Aid Training – Online Course Paediatric Vaccination Paediatrician Pain Management Pain Management – Back and Neck Pain Paramedicine Paramedicine Study Parapsychology Parapsychology Parenting Skills Training Course Particle Physics Partnership in Adult Care Party Planner Pathological Demand Avoidance Patient Customer Service Training Payroll Management Course Pension UK Performance Coaching Performance Cycling Performance Management Level 3 Person-centered Practice in Adult Care Pet First Aid Pet Sitting and Dog Walking Pharmacology Phlebotomist Training Phone-Based Customer Service Phonics Teaching and English Phonology Physiotherapy Assistant Course Planning, Delivery and Assessment in Teaching Plant Genetics – Ecology, Gymnosperms, Angiosperms and Palaeobotany Play Therapy PLUMBING Podcasting – Tools, Voice Coaching and Marketing Podcasting Essentials Poetry Writing Politics Pool Maintenance Positive Attachments for Children Positive Behaviour in Children and Youth Positive Handling in Schools Power Cutting Tools and How to Use Them PPE PR : Public Relation Practical Advice For Converting To A Takeaway Kitchen Primary Teacher Principle of Business Principles of Administrative Service and Business Documentation Principles of Digital Marketing Principles of Infection Prevention and Control Principles of Information & Digital Technology Printing Worker Private Detective Training Process Improvement with Gap Analysis Product Management Professional Development and Personal Well-being Professional Diploma in Project Management Professional Diploma in Stress Management Professional Plumbing Professional Supervisor Training Course Professional Telephone Receptionist Course Professional Waiter Diploma Project Management Promoting Child and Young Person Development Provision and Use of Work Equipment Regulations (PUWER) Psychology of Anxiety and Stress Public Health Public Healthcare Purchase Ledger Purchasing and Procurement Basics Python Programming for Kids and Beginners Quality Assurance Quality Management Quality Management Fundamentals Quantity Surveyor Diploma Radiography Recovering from a Job Loss in Technology Recruitment & Onboarding Process Recruitment and Social Media Course Reflective Practice Remote Teaching Online Remote Team Management Bundle Report Writing Reporting of Injuries, Diseases and Dangerous Occurrences Regulations (RIDDOR) Training Research in Adult Care Research in Health and Social Care Residential Childcare Residential Childcare for Children with Disabilities Residential Property Sales Residential Surveyor Resilience Training Resourcing and Managing Talent Course Respirable Crystalline Silica Awareness Responsibilities of Care Manager Restaurant Management Restful API Web Services with PHP and MySQL: Bootcamp Retail Industry and Buyer Behaviours Revamp Your Closet Risk Assessment & Management Diploma Risk Management Risk Management in Adult Care Role of Nutrition in Human Health Roles and Responsibilities in Education and Training Rugby First Aid Rule of Law Safe Handling of Medicines Safeguarding and Protection of Children and Young People Safeguarding Children From Abuse Safeguarding Children: Internet Safety Safeguarding for Taxi Drivers Safeguarding Small Business During Pendemic Safeguarding Vulnerable Adults – Communication, Sharing Information & Reporting Safeguarding Vulnerable Adults Training (Level 1) Safer Recruitment Training Safety & Precautions in Medication Management Sales Skills Sales Skills Security Guard Self Esteem and Assertiveness Skills Course Self Isolation and Self Distancing during COVID 19 Self-Leadership SEO and Social Media Marketing Setting Up Your Dog Grooming Business Sewing Diploma Sexual Harassment in the Workplace Training for Managers and Supervisors (SHWT) Sharps Training Site Management Safety Training Scheme (SMSTS) Six Sigma Entering the Dojo Skills for Positive Working Relationships Skills for the Administrative Assistant Skin Care Treatment Course Smart Meter Installer Training Smartphone Photography Online Course Soap Making – Equipment and Special Soap Recipes Soap Making – Tips, Tricks and Precautions Social Care Social Inclusion Officer Training Course Social Media in Business Social Media in Healthcare Social Media Marketing Course – The Step by Step Guide Social Science – Online Diploma Course Sous Chef Spatial Data Visualisation and Machine Learning in Python Speaking And Writing English Effectively Speed Reading Spill Management Training Spill Management: Clean-Up, Prevention and Best Practices Spiritual Life Coaching Diploma Course Sports Agent Sports Injuries Sports Medicine Fundamentals Sports Psychology Sports Therapy Stakeholder Management Start Up Start Up Performance Management Starting a Business or Social Enterprise – The Stone Soup Way Statistical Analysis Statistics Essentials Stock Trading Store Assistant Strategic Business Management – Online Diploma Course Strategic Planning and Analysis for Marketing Strategic Planning and Analysis for Marketing Strategic Planning for Organisation Strategies & Skills for Recruitment – Online Course Stress Awareness Training Structure and Overview of the Health and Social Care Sector Study Skills for Healthcare Substance Misuse Awareness Online Certification Course Super Learning Supervision in Adult Care Supervisor Training Supply Chain Management Supply Chain Management – Analysing and Reducing Risk Supply Chain Management – Efficiency and Accuracy Supporting a Grieving Employee: A Manager’s Guide Supporting Your Mental Health While Working from Home Supporting Your Team’s Health And Wellbeing Remotely Surveying Basics Sustainable Living Talent Management Course Tax Accounting Teaching English as Foreign Language (TEFL) Certificate Teaching Students with Learning Disabilities Team Building Diploma Team Leader in Health Care Team Management Level 5 Team Management Level 5 Telemarketing – Using the Telephone as a Sales Tool The 5S System – Lean Methodology on Workplace Optimization and Housekeeping The Complete MySQL Server from Scratch: Bootcamp The Complete SQL from Scratch: Bootcamp The Manager: Management and Leadership Development Programme The Professional Supervisor The Secrets of Body Language Town Planning Traffic Marshal Training & Learning for Carer Transport Manager Travel Agent and Consultant Training Travel Blogger TV Presenter Online Course Unconscious Bias Training Course Understanding Mediterranean and Okinawa Diets Urology Urology – Diseases and Treatment Using Activities to Make Training Fun Verbal and Non-Verbal Business Communications Verification of Death Training for Nurses Virtual Assistant Virtual Interviewing for HR Virtual Team Building and Management Course Voice Disorders Voiceover artist online course Vulnerability, Abuse & Safeguarding Warehouse Safety Warehouse Safety – Hazard and Safety Management Web GIS Application Development with C# ASP.NET CORE MVC and Leaflet Web GIS Application Development with Java Spring Boot MVC and Leaflet Web Scraping and Mapping Dam Levels in Python and Leaflet Wedding Planner Wedding Planning – Themes, Food and Photography Welding Basics and Safety Whistleblowing Training | Online Certification Course Wildlife Rescue and Rehabilitation Working from Home Essentials Working in Confined Spaces Basic Training Health and Social Care Workplace Communication Management Workplace Confidentiality Workplace First Aid Level 3 Workplace First Aid Level 4 Workplace First Aid Training – Breathing Problems, CPR & Fractures Workplace Performance Management Workplace Productivity Training Workplace Stress Management Workplace Team Networking Diploma Workplaces Rights and Responsibilities Write and Publish a Research Paper: Complete Guide Youth Work Certificate Level 2 Zoology Zoology – Diseases and Health Care Mini MBA Level 3 Diploma in Health & Social Care Care Certificate Course – 15 Standards Cyber Security Workplace First Aid Online Training Course Electrician Complete Training Certificate In Residential Surveying Certificate In Electrician Electrical Safety Certificate In Quantity Surveying Diploma In Veterinary Physiology & Psychotherapy Politics Diploma In Construction Management Introduction to Petroleum Engineering and Exploration Diploma In HR and Payroll Management Recruitment Consultant Diploma In Criminology and Police Investigations Professional Photography Project Management Product management HTML & CSS CODING for beginners Coding with Python 3 Intermediate Cybersecurity Information Technology Management Business Analysis Data Analysis Health care management and care courses Digital Marketing Level 3 Diploma in health & social care Cyber security incident Handling Rigging and lifting Plumber - Professional Plumbing Quantity Surveyor Diploma Nursing Assistant Diploma Master Herbalist Diploma Mental Health Awareness Diploma Construction Management Construction Site Management Electric Circuits for Electrical Engineering Teaching Assistant Level 3 Vehicle Mechanic Bundle (Car Maintenance, Motorbike Maintenance, Bicycle Maintenance) Special Educational Needs Teaching Assistant Diploma Sports Coaching Diploma Diploma in Poultry Farming Veterinary Physiology & Psychotherapy Spiritual Life Coaching Public Speaking Training Wedding and Event Management Public Speaking and Presentations Veterinary Medicine Fitness Business - Sell Products, Training & Coaching Online HR (Human Resources) Data Analyst: Data Analysis in Excel Google Data Studio: Data Analytics Hospitality Management Digital Marketing for Beginners to Advanced Sales Training: Master Your Sales Pitch Agile Scrum Master Business analysis & Scrum with JIRA Real Estate Investor Training ChatGPT for Marketing and Productivity with AI Tools Real Estate Broker Hotel Management with Hotel Receptionist and Hospitality Management Graphic Design

Module 1: Dangers of Hydrofluoric Acid (HF) Understanding HF What is hydrofluoric acid? Its industrial and laboratory uses. Why HF is Dangerous Unique hazards: deep tissue penetration, systemic toxicity. Routes of exposure: inhalation, skin contact, ingestion. Effects on the Body Localized burns and systemic toxicity (calcium and magnesium binding). Signs and symptoms of HF exposure. Module 2: Precautions When Using Hydrofluoric Acid Personal Protective Equipment (PPE) Essential PPE: gloves, goggles, face shields, and lab coats. How to inspect and wear PPE correctly. Safe Handling Practices Using fume hoods and proper ventilation. Step-by-step HF handling protocols. Avoiding common mistakes. Storage Guidelines Safe storage requirements: compatible materials, labeling, and segregation. Emergency spill kits and their contents. Module 3: First Aid Treatments for Hydrofluoric Acid Burns Immediate First Aid Removing contaminated clothing and thoroughly flushing the area with water for 15 minutes. Importance of acting quickly to minimize damage. Using Calcium Gluconate Proper application of calcium gluconate gel to affected areas. Monitoring for pain and repeated application if necessary. When to Seek Medical Attention Indicators for professional medical intervention. Providing medical staff with details about HF exposure.

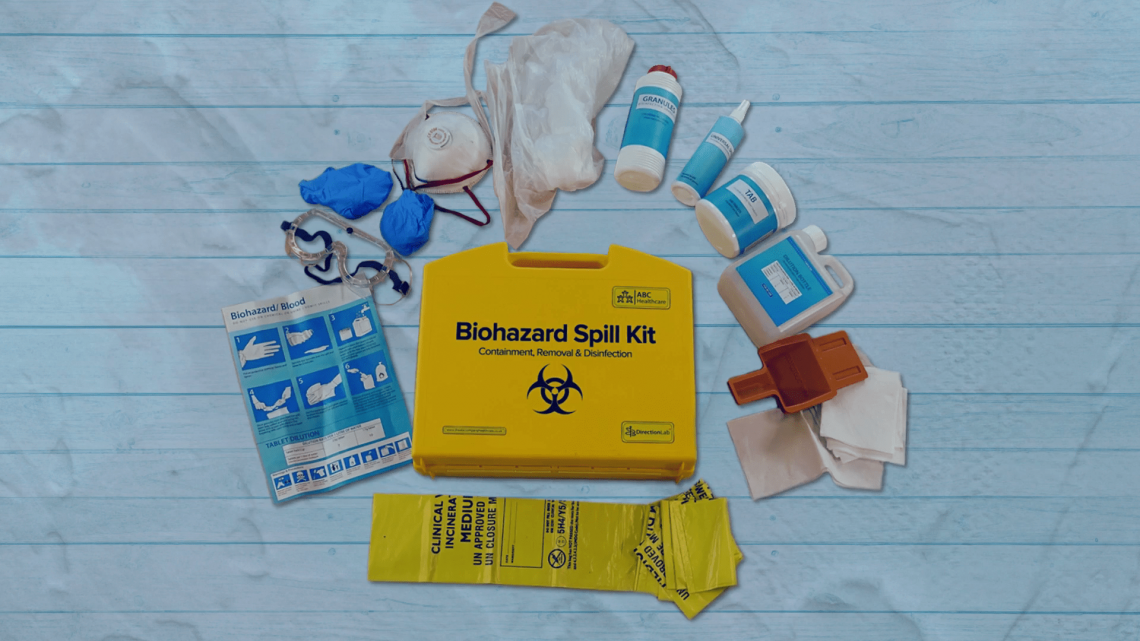
Biohazard Safety: Managing Blood and Body Fluid Spillages Instructor
By Guardian Angels Training
Gain expertise in biohazard safety with our "Biohazard Safety: Managing Blood and Body Fluid Spillages Instructor Training" course. Ideal for healthcare professionals, lab staff, and emergency responders.
Environmental awareness and management (In-House)
By The In House Training Company
A flexible, modular-based, programme to heighten participants' awareness of ways in which their operations can affect the environment, the principles of environmental management and the practical steps they need to take as individuals and as an organisation to improve environmental performance. Depending on the course modules selected, this programme will give participants: Increased awareness of relevant environmental issues A greater understanding of, and commitment to, the organisation's environmental management programme Preparation for any responsibilities they may have under an Environmental Management System Further benefits according to options chosen 1 Environmental awareness Definition of 'the environment' Key environmental issuesGlobal warmingOzone depletionAcid rainAir qualityWater pollutionContaminated landLand take and green belt shrinkageResource usageHabitat destruction and species extinctions. Option: This module can be used to explain the key environmental issues related to the activities of your own organisation. Diagrams, photos, pictures, examples and statistics relevant to your own organisation are used where possible to illustrate the points being made. 2 Environmental legislation Key elements of environmental legislation affecting the activities of your organisation - including international, European and UK legislation. Legislation of particular relevance to your organisation - how it affects the operations of your organisation Option: Legislation can be dealt with according to which aspect of the environment it protects (eg, air, water, waste) or which part of your organisation's activities it affects Consequences of breaching legislation 3 Environmental management systems Overview of what an environmental management system isHow is an Environmental Management System (EMS) designed and put together?Key elements (emphasising Plan - Do - Check - Review cycle)The need to continually improve Pros and consReasons for having an EMSBenefits of an EMSConsequences of not managing the environmentCosts of installing an EMS Explanation of ISO 14001 and EMAS standards and guidance as applicable to the EMSs of your organisationOverview of your organisation's EMSHow it was set up / is being developed / operatesWho is responsible for itKey parts of system (eg, environmental policy, objectives and targets) identified and discussedEMS documentation - what and where it is. Workshop option: Brainstorm 'Pros and cons' with the participants, come up with all their ideas for good and bad things about EMS and demonstrate that the 'good' list is longer than the 'bad' 4 Environmental consequences Define what an environmental impact is and discuss how they are determined, with reference to the EMS Identify why we want to determine the environmental consequences of operations and activities; how they are used in the EMS for planning, and reducing the impact on the environment Establish key environmental consequences of construction and operational activities on the site; discuss significance ranking and the control measures in place in your organisation. Workshop option: In small groups, participants are asked to identify the impact on the environment of your organisation's activities or a part of their activities. They are then asked to rank these impacts in terms of their significance, using guidelines provided to help them be aware of the contributing factors (eg, frequency, severity). For a selected number of the impacts, the participants are asked to identify what control measures there are and which of these they play a part in. All stages can be discussed with trainers as a whole group at various stages during the workshop. 5 Protected species, nature conservation and invasive weeds Nature conservation, landscape and visual issues in the planning process - overview of key nature UK wildlife legislation, EIA, appropriate timing of surveys, Hedgerow regulations and landscape and visual impact issues Ecological issues - ecological legislation, significant species, hedgerows Archaeology in the development process - why archaeology is important, organisation in the UK, legislation and planning guidance Construction phase issues and consents - major environmental issues during construction, including water resources and land drainage consents, discharges to land or water, water abstraction, public rights of way, tree protection, waste management, Special waste, noise, good practice pollution control and Environmental Audits Identification and management of invasive weeds - including legal position regarding management 6 Chemicals and fuels handling and storage How health and safety management is closely linked to environmental management of materials Planning - what mechanisms are in place for planning materials use; legislation, guidance and policies which define how to manage materials Materials storage - what are the considerations for storing materials, covering:Labels: what are the different types and what do they tell us?Storage facilities: what are the requirements for safe storage of materials (eg, signs, secondary containment, access, segregation, lids/covers)Handling: safe handling for protecting the environment, organisational procedures, high risk situations (eg, decanting, deliveries), how to reduce the risks (eg, use of funnels, proper supervision, training)COSHH and MSDS: brief explanation of legislation and its role in environmental control of hazardous materials, how to use the information provided by COSHH assessments Option: These sessions can be illustrated with photographs/pictures and examples of good and bad storage and handling practices Workshop Options: Labelling Quiz - quick-fire quiz on what different labels tell us; Build a Storage Facility - participants are asked to consider all the environmental requirements for building a safe storage facility for their organisation 7 On-site control measures Overview of the legislation associated with nuisance issues on site and mitigating problems when they arise Examples of bad practice, including fuel storage tanks and mobile equipment - costs involved with prosecution of fuel spills, remediation costs, management costs, legal fees, bad PR coverage Identification and management of contaminated land and relevant legislation Workshop option: Participants are provided with a site plan containing information on site features, environmental conditions and indications of potential issues 8 Waste management Why worry about waste? - a look at how waste disposal can impact on the environment, illustrated by examples of waste-related incidents, statistics on waste production on national, industry-wide and organisational levels, landfill site space, etc Legislation - overview of the relevant legislation, what the main requirements of the regulations are, what penalties there are, and the associated documentation (waste transfer notes) Waste classification - a more in-depth look at how waste is classified under legislation according to hazardous properties, referring to Environment Agency guidance Handling and storage requirements - what are the requirements of the applicable waste legislation and how are they covered by organisational procedures? Examples of good and bad environmental practice associated with handling and storing waste. Workshop option: 'Brown bag' exercise - participants pass round a bag containing tags each with a different waste printed on. They are asked to pick out a tag and identify the classification and the handling, storage and disposal requirements for the waste they select Waste minimisation - overview of the waste minimisation 'ladder' and its different options (elimination, reduction, reuse and recycling), benefits of waste minimisation, examples of waste minimisation techniques Workshop option: Participants are asked to identify opportunities that actually exist within the organisation for minimising production of waste that are not currently being taken advantage of 9 Auditing Requirements for environmental auditing of operations Auditing the EMS Types of internal and external audits Requirements EMS standards (ISO 14001 and EMAS) Carrying out internal audits and being prepared for external audits Workshop options:Mock audit 'Brown Bag' - can be used either for trainers to test participants as if they were in an audit situation, or for the participants to test each other and practice their auditing technique. The bag contains tags each with a different topic printed on (eg, waste skips); participants pass the bag round and select a tag; they are then questioned by the trainer or another participant about that topic as if they were in an audit situation. If the participants are auditing each other, they will be provided with a set of guidelines to keep in mind during the workshop.Virtual auditing - a more practical workshop where participants review photographs of situations/activities relevant to the organisation's operations. They are asked to identify all the good and bad environmental practices that are occurring in the situations. 10 Incident response What should you do when an incident does happen? What should be in a spill kit? When should you call in the experts? When should you inform the Environment Agency or Environmental Health Officer? Workshop option: The participants are provided with some incident scenarios and asked to develop a response to the incident 11 Monitoring and reporting Environmental monitoring programmes and procedures Monitoring and reporting as control measures for environmental consequences Monitoring and environmental 'STOP' card systems - personal and behavioural monitoring and reporting

Search By Location
- Spill Courses in London
- Spill Courses in Birmingham
- Spill Courses in Glasgow
- Spill Courses in Liverpool
- Spill Courses in Bristol
- Spill Courses in Manchester
- Spill Courses in Sheffield
- Spill Courses in Leeds
- Spill Courses in Edinburgh
- Spill Courses in Leicester
- Spill Courses in Coventry
- Spill Courses in Bradford
- Spill Courses in Cardiff
- Spill Courses in Belfast
- Spill Courses in Nottingham

