- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
12 Spill courses delivered Live Online
The UK's first and only Level 4 qualification in Phlebotomy (equivalent to Ireland Level 6) FDSc (Foundation Degree Level) qualification Nationally Recognised certificate Dually accredited: Open College Network and CPD Covers both aspirated and evacuated systems Covers specialised blood collection systems & methods Classroom or Virtual Classroom learning options Comprehensive Training Kit is provided when booking our Virtual Classroom option (yours to keep) Complete your training from beginner to advanced level This course either follows on from our Introduction to Phlebotomy Course or can be combined with our introductory course as part of a course package (see below) Available to candidates who have completed (or are currently enrolled to complete) our Introduction to Phlebotomy Course or have previous phlebotomy practical experience.

Spill Management Training
By NextGen Learning
Spill Management Training Course Overview This Spill Management Training course provides a comprehensive understanding of how to effectively manage and respond to spill incidents in various settings. Covering a range of topics, from hazardous substances and pollution response planning to spill clean-up and prevention, the course prepares learners to handle spill incidents with confidence. Through clear guidelines and site-specific solutions, the course ensures that learners are equipped to minimise environmental impact, reduce risks, and comply with relevant regulations. Learners will gain valuable skills in spill management, safety practices, and regulatory compliance, ensuring a safer work environment. Course Description The Spill Management Training course delves deeper into key areas essential for spill management, including hazardous substances identification, response strategies, and effective clean-up methods. Learners will explore pollution incident response planning, spill management techniques for different environments, and site-specific pollution control options. Each module is designed to offer valuable insights into best practices for spill prevention and control, while encouraging a culture of responsibility and environmental awareness. By the end of the course, learners will have the skills to manage spills efficiently, ensuring safety and compliance within their workplace. Spill Management Training Curriculum Module 01: Introduction to Spill Management Module 02: Hazardous Substances Module 03: Pollution Incident Response Planning Module 04: Managing a Spill Module 05: Spill Clean-Up Guideline Module 06: Spills on a Road or Highway Module 07: Diesel Spillages: An Overview Module 08: Site-Specific Pollution Control Options Module 09: Spill Prevention & Control Checklist Module 10: Ways to Encourage Best Practice (See full curriculum) Who is this course for? Individuals seeking to enhance their environmental safety skills. Professionals aiming to specialise in spill management or environmental protection. Beginners with an interest in pollution control and safety procedures. Organisations requiring staff training in spill management and compliance. Career Path Environmental Health and Safety Officer Spill Response Coordinator Environmental Consultant Pollution Control Specialist Health and Safety Manager

Chemical Spill Management Training Online
By NextGen Learning
Chemical Spill Management Training Online Course Overview This Chemical Spill Management Training Online course provides comprehensive knowledge essential for understanding, preventing, and managing chemical spills safely and effectively. Learners will explore the nature of hazardous chemicals, their impact on human health, and the procedures necessary for prompt spill response and cleanup. Emphasising compliance with UK safety legislation, this course equips learners with the skills to minimise risks in various workplace environments. Upon completion, participants will be confident in recognising chemical hazards, implementing preventive measures, and managing spill incidents responsibly, enhancing workplace safety and environmental protection. Course Description This course delves into the critical aspects of chemical spill management, starting from recognising hazardous substances to detailed spill response techniques. Learners will study how chemicals affect the human body and the environment, understand the types of common hazardous substances, and examine methods to prevent spills. The curriculum covers spill containment, appropriate cleanup methods, and legal requirements specific to the UK. Additionally, learners will gain insight into hazardous waste treatment and the management of oil spills. Designed for clarity and thoroughness, the course offers a structured learning experience to develop essential skills in managing chemical spill risks, ensuring safety, regulatory compliance, and environmental stewardship. Chemical Spill Management Training Online Curriculum: Module 01: Introduction To Hazardous Chemicals Module 02: Hazardous Chemicals And The Human Body Module 03: Common Hazardous Substances Module 04: Chemical Spills Module 05: Preventing Spills Module 06: Spill Response Module 07: Spill Cleanup Module 08: Hazardous Waste Treatment And Disposal Module 09: Oil Spills Module 10: Legislations Regarding Hazardous Chemicals In The UK (See full curriculum) Who is this course for? Individuals seeking to enhance workplace safety knowledge related to chemicals. Professionals aiming to improve their emergency response capabilities in chemical management. Beginners with an interest in environmental safety and chemical hazard control. Safety officers, facility managers, and environmental compliance staff. Career Path Environmental Health and Safety Officer Chemical Safety Coordinator Compliance and Risk Management Specialist Facility Manager in Industrial or Manufacturing Sectors Environmental Consultant Emergency Response Team Member

Seismic Uncertainty Evaluation
By EnergyEdge - Training for a Sustainable Energy Future
About this training The Seismic Uncertainty Evaluation (SUE) course has evolved after a number of years of work experience in the sub-surface domain. A common question closely related to well planning is the quantification and qualification of depth uncertainty and robust estimation of the volumetric ranges, and this course addresses these topics. Training Objectives Upon completion of this course, participants will be able to: Define a structured approach toward seismic depth uncertainty analysis Construct data analytics on seismic products (well logs, velocities, and seismic) Classify advance vertical ray tomography on FWI models to assure a drill ready depth seismic, faults, surfaces, and logs Interpret probabilistic volumetric and automatic spill point control, amplitude conformance closures De-risk the depth uncertainty by providing drilling and completion with a risking score card Target Audience This course is intended for individuals who needs to understand the basic theory and procedures for assessment/ quantification/qualification of all drill-ready products (seismic, faults, horizons, etc.) Geologist Geophysicist Reservoir engineer Drilling engineer Course Level Intermediate Trainer Your expert course leader is a cross-functional Geoscientist and Published Author with 27 years of international experience working in Upstream Petroleum Exploration and Production for Oil and Gas Companies in Australia, India, Singapore, Saudi Arabia, and Oman. During his career he actively supported field development, static & dynamic reservoir modelling & well planning, 3D Seismic data acquisition with Schlumberger & SVUL, 3D seismic data processing with CGG & interpretation, Q.I. and field development with Woodside, Applied Geoscience, and Reliance. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

Platelet-rich Plasma (PRP) treatments Nationally Recognised Qualification No previous experience or qualifications needed Open College Network Accreditation Level 4 (as required for minimally invasive procedures) Covers standards set by HEE Employed (salon) or Self-Employed opportunities Basic understanding of English language required OPEN TO ALL APPLICANTS

Workplace Safety- Asbestos & COSHH Training
By NextGen Learning
Course Overview This comprehensive Workplace Safety – Asbestos & COSHH Training course is designed to equip learners with essential knowledge of hazardous substances, safety regulations, and risk assessment procedures. It covers critical subjects such as asbestos awareness, COSHH regulations, fire safety, and chemical spill response, empowering individuals to uphold safety standards in any professional environment. Whether you're new to workplace safety or looking to reinforce your compliance knowledge, this course ensures you understand how to identify, report, and manage potential hazards in line with UK health and safety legislation. By completing this training, learners will gain the confidence to support a safer workplace, meet employer and legal requirements, and contribute to a healthier work culture across sectors such as construction, manufacturing, education, and care. This course is also valuable for those pursuing roles with responsibility for safety assessments or compliance monitoring within their organisation. Course Description The Workplace Safety – Asbestos & COSHH Training course offers in-depth guidance on handling hazardous materials and navigating high-risk scenarios. Topics include the dangers and regulations surrounding asbestos, COSHH assessments, confined space awareness, chemical spill response, and essential workplace first aid. Additionally, learners will study broader workplace health and safety practices, ensuring a well-rounded understanding of legislative duties, hazard control, and preventative measures. Throughout the course, learners will develop the ability to interpret health and safety protocols, implement best practices, and support regulatory compliance. The training is aligned with UK industry requirements, offering insights into effective safety planning and emergency procedures. This course suits both those with responsibilities in health and safety and those looking to improve their knowledge to support safe operational standards in various workplace settings. Course Modules: Module 01: Asbestos Awareness & Safety Module 02: COSHH Training for Assessors Module 03: Working in Confined Spaces Module 04: Chemical Spill Module 05: Spill Management Training Module 06: Fire Safety Module 07: Workplace Health and Safety Diploma Module 08: First Aid at Work (See full curriculum) Who is this course for? Individuals seeking to understand health and safety obligations in the workplace. Professionals aiming to improve compliance knowledge and safety awareness. Beginners with an interest in occupational health and safety practices. Supervisors, HR personnel, and compliance officers responsible for workplace risk. Career Path Health and Safety Officer Compliance Coordinator Site Supervisor Risk Assessor Facilities Manager Warehouse or Construction Safety Personnel HR and Operations Manager

Environmental awareness and management (In-House)
By The In House Training Company
A flexible, modular-based, programme to heighten participants' awareness of ways in which their operations can affect the environment, the principles of environmental management and the practical steps they need to take as individuals and as an organisation to improve environmental performance. Depending on the course modules selected, this programme will give participants: Increased awareness of relevant environmental issues A greater understanding of, and commitment to, the organisation's environmental management programme Preparation for any responsibilities they may have under an Environmental Management System Further benefits according to options chosen 1 Environmental awareness Definition of 'the environment' Key environmental issuesGlobal warmingOzone depletionAcid rainAir qualityWater pollutionContaminated landLand take and green belt shrinkageResource usageHabitat destruction and species extinctions. Option: This module can be used to explain the key environmental issues related to the activities of your own organisation. Diagrams, photos, pictures, examples and statistics relevant to your own organisation are used where possible to illustrate the points being made. 2 Environmental legislation Key elements of environmental legislation affecting the activities of your organisation - including international, European and UK legislation. Legislation of particular relevance to your organisation - how it affects the operations of your organisation Option: Legislation can be dealt with according to which aspect of the environment it protects (eg, air, water, waste) or which part of your organisation's activities it affects Consequences of breaching legislation 3 Environmental management systems Overview of what an environmental management system isHow is an Environmental Management System (EMS) designed and put together?Key elements (emphasising Plan - Do - Check - Review cycle)The need to continually improve Pros and consReasons for having an EMSBenefits of an EMSConsequences of not managing the environmentCosts of installing an EMS Explanation of ISO 14001 and EMAS standards and guidance as applicable to the EMSs of your organisationOverview of your organisation's EMSHow it was set up / is being developed / operatesWho is responsible for itKey parts of system (eg, environmental policy, objectives and targets) identified and discussedEMS documentation - what and where it is. Workshop option: Brainstorm 'Pros and cons' with the participants, come up with all their ideas for good and bad things about EMS and demonstrate that the 'good' list is longer than the 'bad' 4 Environmental consequences Define what an environmental impact is and discuss how they are determined, with reference to the EMS Identify why we want to determine the environmental consequences of operations and activities; how they are used in the EMS for planning, and reducing the impact on the environment Establish key environmental consequences of construction and operational activities on the site; discuss significance ranking and the control measures in place in your organisation. Workshop option: In small groups, participants are asked to identify the impact on the environment of your organisation's activities or a part of their activities. They are then asked to rank these impacts in terms of their significance, using guidelines provided to help them be aware of the contributing factors (eg, frequency, severity). For a selected number of the impacts, the participants are asked to identify what control measures there are and which of these they play a part in. All stages can be discussed with trainers as a whole group at various stages during the workshop. 5 Protected species, nature conservation and invasive weeds Nature conservation, landscape and visual issues in the planning process - overview of key nature UK wildlife legislation, EIA, appropriate timing of surveys, Hedgerow regulations and landscape and visual impact issues Ecological issues - ecological legislation, significant species, hedgerows Archaeology in the development process - why archaeology is important, organisation in the UK, legislation and planning guidance Construction phase issues and consents - major environmental issues during construction, including water resources and land drainage consents, discharges to land or water, water abstraction, public rights of way, tree protection, waste management, Special waste, noise, good practice pollution control and Environmental Audits Identification and management of invasive weeds - including legal position regarding management 6 Chemicals and fuels handling and storage How health and safety management is closely linked to environmental management of materials Planning - what mechanisms are in place for planning materials use; legislation, guidance and policies which define how to manage materials Materials storage - what are the considerations for storing materials, covering:Labels: what are the different types and what do they tell us?Storage facilities: what are the requirements for safe storage of materials (eg, signs, secondary containment, access, segregation, lids/covers)Handling: safe handling for protecting the environment, organisational procedures, high risk situations (eg, decanting, deliveries), how to reduce the risks (eg, use of funnels, proper supervision, training)COSHH and MSDS: brief explanation of legislation and its role in environmental control of hazardous materials, how to use the information provided by COSHH assessments Option: These sessions can be illustrated with photographs/pictures and examples of good and bad storage and handling practices Workshop Options: Labelling Quiz - quick-fire quiz on what different labels tell us; Build a Storage Facility - participants are asked to consider all the environmental requirements for building a safe storage facility for their organisation 7 On-site control measures Overview of the legislation associated with nuisance issues on site and mitigating problems when they arise Examples of bad practice, including fuel storage tanks and mobile equipment - costs involved with prosecution of fuel spills, remediation costs, management costs, legal fees, bad PR coverage Identification and management of contaminated land and relevant legislation Workshop option: Participants are provided with a site plan containing information on site features, environmental conditions and indications of potential issues 8 Waste management Why worry about waste? - a look at how waste disposal can impact on the environment, illustrated by examples of waste-related incidents, statistics on waste production on national, industry-wide and organisational levels, landfill site space, etc Legislation - overview of the relevant legislation, what the main requirements of the regulations are, what penalties there are, and the associated documentation (waste transfer notes) Waste classification - a more in-depth look at how waste is classified under legislation according to hazardous properties, referring to Environment Agency guidance Handling and storage requirements - what are the requirements of the applicable waste legislation and how are they covered by organisational procedures? Examples of good and bad environmental practice associated with handling and storing waste. Workshop option: 'Brown bag' exercise - participants pass round a bag containing tags each with a different waste printed on. They are asked to pick out a tag and identify the classification and the handling, storage and disposal requirements for the waste they select Waste minimisation - overview of the waste minimisation 'ladder' and its different options (elimination, reduction, reuse and recycling), benefits of waste minimisation, examples of waste minimisation techniques Workshop option: Participants are asked to identify opportunities that actually exist within the organisation for minimising production of waste that are not currently being taken advantage of 9 Auditing Requirements for environmental auditing of operations Auditing the EMS Types of internal and external audits Requirements EMS standards (ISO 14001 and EMAS) Carrying out internal audits and being prepared for external audits Workshop options:Mock audit 'Brown Bag' - can be used either for trainers to test participants as if they were in an audit situation, or for the participants to test each other and practice their auditing technique. The bag contains tags each with a different topic printed on (eg, waste skips); participants pass the bag round and select a tag; they are then questioned by the trainer or another participant about that topic as if they were in an audit situation. If the participants are auditing each other, they will be provided with a set of guidelines to keep in mind during the workshop.Virtual auditing - a more practical workshop where participants review photographs of situations/activities relevant to the organisation's operations. They are asked to identify all the good and bad environmental practices that are occurring in the situations. 10 Incident response What should you do when an incident does happen? What should be in a spill kit? When should you call in the experts? When should you inform the Environment Agency or Environmental Health Officer? Workshop option: The participants are provided with some incident scenarios and asked to develop a response to the incident 11 Monitoring and reporting Environmental monitoring programmes and procedures Monitoring and reporting as control measures for environmental consequences Monitoring and environmental 'STOP' card systems - personal and behavioural monitoring and reporting

MS-102T00 Microsoft 365 Administrator Essentials
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for persons aspiring to the Microsoft 365 Administrator role and have completed at least one of the Microsoft 365 role-based administrator certification paths. This course covers the following key elements of Microsoft 365 administration: Microsoft 365 tenant management, Microsoft 365 identity synchronization, and Microsoft 365 security and compliance. In Microsoft 365 tenant management, you learn how to configure your Microsoft 365 tenant, including your organizational profile, tenant subscription options, component services, user accounts and licenses, security groups, and administrative roles. You then transition to configuring Microsoft 365, with a primary focus on configuring Office client connectivity. Finally, you explore how to manage user-driven client installations of Microsoft 365 Apps for enterprise deployments. The course then transitions to an in-depth examination of Microsoft 365 identity synchronization, with a focus on Microsoft Entra Connect and Connect Cloud Sync. You learn how to plan for and implement each of these directory synchronization options, how to manage synchronized identities, and how to implement password management in Microsoft 365 using multifactor authentication and self-service password management. In Microsoft 365 security management, you begin examining the common types of threat vectors and data breaches facing organizations today. You then learn how Microsoft 365?s security solutions address each of these threats. You are introduced to the Microsoft Secure Score, as well as to Microsoft Entra ID Protection. You then learn how to manage the Microsoft 365 security services, including Exchange Online Protection, Safe Attachments, and Safe Links. Finally, you are introduced to the various reports that monitor an organization?s security health. You then transition from security services to threat intelligence; specifically, using Microsoft 365 Defender, Microsoft Defender for Cloud Apps, and Microsoft Defender for Endpoint. Once you have this understanding of Microsoft 365?s security suite, you then examine the key components of Microsoft 365 compliance management. This begins with an overview of all key aspects of data governance, including data archiving and retention, Microsoft Purview message encryption, and data loss prevention (DLP). You then delve deeper into archiving and retention, paying particular attention to Microsoft Purview insider risk management, information barriers, and DLP policies. You then examine how to implement these compliance features by using data classification and sensitivity labels. Prerequisites Completed a role-based administrator course such as Messaging, Teamwork, Security, Compliance, or Collaboration. A proficient understanding of DNS and basic functional experience with Microsoft 365 services. A proficient understanding of general IT practices. A working knowledge of PowerShell. 1 - Configure your Microsoft 365 experience Explore your Microsoft 365 cloud environment Configure your Microsoft 365 organizational profile Manage your tenant subscriptions in Microsoft 365 Integrate Microsoft 365 with customer engagement apps Complete your tenant configuration in Microsoft 365 2 - Manage users, licenses, and mail contacts in Microsoft 365 Determine the user identity model for your organization Create user accounts in Microsoft 365 Manage user account settings in Microsoft 365 Manage user licenses in Microsoft 365 Recover deleted user accounts in Microsoft 365 Perform bulk user maintenance in Microsoft Entra ID Create and manage guest users Create and manage mail contacts 3 - Manage groups in Microsoft 365 Examine groups in Microsoft 365 Create and manage groups in Microsoft 365 Create dynamic groups using Azure rule builder Create a Microsoft 365 group naming policy Create groups in Exchange Online and SharePoint Online 4 - Add a custom domain in Microsoft 365 Plan a custom domain for your Microsoft 365 deployment Plan the DNS zones for a custom domain Plan the DNS record requirements for a custom domain Create a custom domain in Microsoft 365 5 - Configure client connectivity to Microsoft 365 Examine how automatic client configuration works Explore the DNS records required for client configuration Configure Outlook clients Troubleshoot client connectivity 6 - Configure administrative roles in Microsoft 365 Explore the Microsoft 365 permission model Explore the Microsoft 365 admin roles Assign admin roles to users in Microsoft 365 Delegate admin roles to partners Manage permissions using administrative units in Microsoft Entra ID Elevate privileges using Microsoft Entra Privileged Identity Management Examine best practices when configuring administrative roles 7 - Manage tenant health and services in Microsoft 365 Monitor the health of your Microsoft 365 services Monitor tenant health using Microsoft 365 Adoption Score Monitor tenant health using Microsoft 365 usage analytics Develop an incident response plan Request assistance from Microsoft 8 - Deploy Microsoft 365 Apps for enterprise Explore Microsoft 365 Apps for enterprise functionality Explore your app compatibility by using the Readiness Toolkit Complete a self-service installation of Microsoft 365 Apps for enterprise Deploy Microsoft 365 Apps for enterprise with Microsoft Configuration Manager Deploy Microsoft 365 Apps for enterprise from the cloud Deploy Microsoft 365 Apps for enterprise from a local source Manage updates to Microsoft 365 Apps for enterprise Explore the update channels for Microsoft 365 Apps for enterprise Manage your cloud apps using the Microsoft 365 Apps admin center 9 - Analyze your Microsoft 365 workplace data using Microsoft Viva Insights Examine the analytical features of Microsoft Viva Insights Explore Personal insights Explore Team insights Explore Organization insights Explore Advanced insights 10 - Explore identity synchronization Examine identity models for Microsoft 365 Examine authentication options for the hybrid identity model Explore directory synchronization 11 - Prepare for identity synchronization to Microsoft 365 Plan your Microsoft Entra deployment Prepare for directory synchronization Choose your directory synchronization tool Plan for directory synchronization using Microsoft Entra Connect Plan for directory synchronization using Microsoft Entra Connect cloud sync 12 - Implement directory synchronization tools Configure Microsoft Entra Connect prerequisites Configure Microsoft Entra Connect Monitor synchronization services using Microsoft Entra Connect Health Configure Microsoft Entra Connect cloud sync prerequisites Configure Microsoft Entra Connect cloud sync 13 - Manage synchronized identities Manage users with directory synchronization Manage groups with directory synchronization Use Microsoft Entra Connect Sync Security Groups to help maintain directory synchronization Configure object filters for directory synchronization Explore Microsoft Identity Manager Troubleshoot directory synchronization 14 - Manage secure user access in Microsoft 365 Manage user passwords Enable pass-through authentication Enable multifactor authentication Enable passwordless sign-in with Microsoft Authenticator Explore self-service password management Explore Windows Hello for Business Implement Microsoft Entra Smart Lockout Implement conditional access policies Explore Security Defaults in Microsoft Entra ID Investigate authentication issues using sign-in logs 15 - Examine threat vectors and data breaches Explore today's work and threat landscape Examine how phishing retrieves sensitive information Examine how spoofing deceives users and compromises data security Compare spam and malware Examine account breaches Examine elevation of privilege attacks Examine how data exfiltration moves data out of your tenant Examine how attackers delete data from your tenant Examine how data spillage exposes data outside your tenant Examine other types of attacks 16 - Explore the Zero Trust security model Examine the principles and components of the Zero Trust model Plan for a Zero Trust security model in your organization Examine Microsoft's strategy for Zero Trust networking Adopt a Zero Trust approach 17 - Explore security solutions in Microsoft 365 Defender Enhance your email security using Exchange Online Protection and Microsoft Defender for Office 365 Protect your organization's identities using Microsoft Defender for Identity Protect your enterprise network against advanced threats using Microsoft Defender for Endpoint Protect against cyber attacks using Microsoft 365 Threat Intelligence Provide insight into suspicious activity using Microsoft Cloud App Security Review the security reports in Microsoft 365 Defender 18 - Examine Microsoft Secure Score Explore Microsoft Secure Score Assess your security posture with Microsoft Secure Score Improve your secure score Track your Microsoft Secure Score history and meet your goals 19 - Examine Privileged Identity Management Explore Privileged Identity Management in Microsoft Entra ID Configure Privileged Identity Management Audit Privileged Identity Management Control privileged admin tasks using Privileged Access Management 20 - Examine Azure Identity Protection Explore Azure Identity Protection Enable the default protection policies in Azure Identity Protection Explore the vulnerabilities and risk events detected by Azure Identity Protection Plan your identity investigation 21 - Examine Exchange Online Protection Examine the anti-malware pipeline Detect messages with spam or malware using Zero-hour auto purge Explore anti-spoofing protection provided by Exchange Online Protection Explore other anti-spoofing protection Examine outbound spam filtering 22 - Examine Microsoft Defender for Office 365 Climb the security ladder from EOP to Microsoft Defender for Office 365 Expand EOP protections by using Safe Attachments and Safe Links Manage spoofed intelligence Configure outbound spam filtering policies Unblock users from sending email 23 - Manage Safe Attachments Protect users from malicious attachments by using Safe Attachments Create Safe Attachment policies using Microsoft Defender for Office 365 Create Safe Attachments policies using PowerShell Modify an existing Safe Attachments policy Create a transport rule to bypass a Safe Attachments policy Examine the end-user experience with Safe Attachments 24 - Manage Safe Links Protect users from malicious URLs by using Safe Links Create Safe Links policies using Microsoft 365 Defender Create Safe Links policies using PowerShell Modify an existing Safe Links policy Create a transport rule to bypass a Safe Links policy Examine the end-user experience with Safe Links 25 - Explore threat intelligence in Microsoft 365 Defender Explore Microsoft Intelligent Security Graph Explore alert policies in Microsoft 365 Run automated investigations and responses Explore threat hunting with Microsoft Threat Protection Explore advanced threat hunting in Microsoft 365 Defender Explore threat analytics in Microsoft 365 Identify threat issues using Microsoft Defender reports 26 - Implement app protection by using Microsoft Defender for Cloud Apps Explore Microsoft Defender Cloud Apps Deploy Microsoft Defender for Cloud Apps Configure file policies in Microsoft Defender for Cloud Apps Manage and respond to alerts in Microsoft Defender for Cloud Apps Configure Cloud Discovery in Microsoft Defender for Cloud Apps Troubleshoot Cloud Discovery in Microsoft Defender for Cloud Apps 27 - Implement endpoint protection by using Microsoft Defender for Endpoint Explore Microsoft Defender for Endpoint Configure Microsoft Defender for Endpoint in Microsoft Intune Onboard devices in Microsoft Defender for Endpoint Manage endpoint vulnerabilities with Microsoft Defender Vulnerability Management Manage device discovery and vulnerability assessment Reduce your threat and vulnerability exposure 28 - Implement threat protection by using Microsoft Defender for Office 365 Explore the Microsoft Defender for Office 365 protection stack Investigate security attacks by using Threat Explorer Identify cybersecurity issues by using Threat Trackers Prepare for attacks with Attack simulation training 29 - Examine data governance solutions in Microsoft Purview Explore data governance and compliance in Microsoft Purview Protect sensitive data with Microsoft Purview Information Protection Govern organizational data using Microsoft Purview Data Lifecycle Management Minimize internal risks with Microsoft Purview Insider Risk Management Explore Microsoft Purview eDiscovery solutions 30 - Explore archiving and records management in Microsoft 365 Explore archive mailboxes in Microsoft 365 Enable archive mailboxes in Microsoft 365 Explore Microsoft Purview Records Management Implement Microsoft Purview Records Management Restore deleted data in Exchange Online Restore deleted data in SharePoint Online 31 - Explore retention in Microsoft 365 Explore retention by using retention policies and retention labels Compare capabilities in retention policies and retention labels Define the scope of a retention policy Examine the principles of retention Implement retention using retention policies, retention labels, and eDiscovery holds Restrict retention changes by using Preservation Lock 32 - Explore Microsoft Purview Message Encryption Examine Microsoft Purview Message Encryption Configure Microsoft Purview Message Encryption Define mail flow rules to encrypt email messages Add organizational branding to encrypted email messages Explore Microsoft Purview Advanced Message Encryption 33 - Explore compliance in Microsoft 365 Plan for security and compliance in Microsoft 365 Plan your beginning compliance tasks in Microsoft Purview Manage your compliance requirements with Compliance Manager Examine the Compliance Manager dashboard Analyze the Microsoft Compliance score 34 - Implement Microsoft Purview Insider Risk Management Explore insider risk management Plan for insider risk management Explore insider risk management policies Create insider risk management policies Investigate insider risk management activities and alerts Explore insider risk management cases 35 - Implement Microsoft Purview Information Barriers Explore Microsoft Purview Information Barriers Configure information barriers in Microsoft Purview Examine information barriers in Microsoft Teams Examine information barriers in OneDrive Examine information barriers in SharePoint 36 - Explore Microsoft Purview Data Loss Prevention Examine Data Loss Prevention Explore Endpoint data loss prevention Examine DLP policies View DLP policy results Explore DLP reports 37 - Implement Microsoft Purview Data Loss Prevention Plan to implement Microsoft Purview Data Loss Protection Implement Microsoft Purview's default DLP policies Design a custom DLP policy Create a custom DLP policy from a template Configure email notifications for DLP policies Configure policy tips for DLP policies 38 - Implement data classification of sensitive information Explore data classification Implement data classification in Microsoft 365 Explore trainable classifiers Create and retrain a trainable classifier View sensitive data using Content explorer and Activity explorer Detect sensitive information documents using Document Fingerprinting 39 - Explore sensitivity labels Manage data protection using sensitivity labels Explore what sensitivity labels can do Determine a sensitivity label's scope Apply sensitivity labels automatically Explore sensitivity label policies 40 - Implement sensitivity labels Plan your deployment strategy for sensitivity labels Examine the requirements to create a sensitivity label Create sensitivity labels Publish sensitivity labels Remove and delete sensitivity labels Additional course details: Nexus Humans MS-102T00: Microsoft 365 Administrator training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the MS-102T00: Microsoft 365 Administrator course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

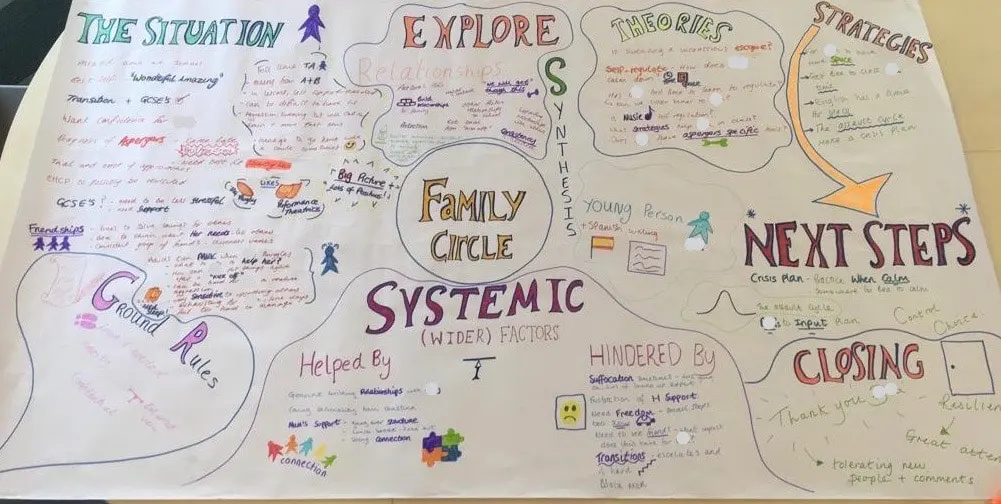
FAMILY CIRCLES
By Inclusive Solutions
Click to read more about this training, in which we demonstrate a live problem solving approach which is based on the active participation of family members. Course Category Inclusion Parents and Carers Behaviour and relationships Problem Solving Description In this training we demonstrate a live problem solving approach which is based on the active participation of family members. ‘Family Circles’ is an evolving new approach to problem solving with families and is based on our years of family work and the development and use of the Circle of Adults process. Inspired by our own Parent Solutions work and the Circle of Adults process as well as Family Group Conferencing and other Restorative Interventions we bring you Family Circles. Essentially the approach involves gathering a family together for a process that is facilitated but majors on the family members offering each other their wisdom and ideas. The approach is capacity focused, person centred approach to working with families rather than the dominant deficit oriented and ‘medical model’ of viewing and planning for or doing things to families. This training can be modelled with a group of professionals or better still with a family. In our work with families we develop the importance of naming stories or theories and seeking linkages and synthesis between what is found out and explored about the family situation and its history. We like participants to sit with the uncertainty, to reflect on the question ‘why’ but without judgement of each other. Deeper reflections may span a whole range of perspectives from ‘within person’ considerations, to situational or systemic possibilities. Health or emotional issues can be reflected on alongside organisational or transactional aspects of what is going on for the family. The better the shared understanding the better the strategy or actions which emerge from these meetings. Quality hypotheses with a close fit to reality lead to more effective implementation in the real world. We encourage ‘loose’ thinking, a search for connections, deeper listening, an ‘open mind’, speculation and exploration without moral judgements. From this stance self-reflection as well as reflection on the situation can produce remarkable insights. The quality of theories or new stories generated is directly influenced by family members’ experiences and the models of learning, behaviour and emotion, systems, educational development, change and so on that they have been exposed to. Learning Objectives To provide opportunities for: Shared problem solving in a safe exploratory climate in which the family will find its own solutions. Individuals to reflect on their own actions and strategies An exploration of whole-family processes and their impact Emotional support and shared understandings of issues at a child, parent, family, school and community level. Feed back to each other on issues, ideas and strategies that are agreed to be worth sharing with them. Who Is It For? Anyone interested in working with families in a way that builds and makes use of their capacities rather than focus on their challenges and difficulties. Social Care teams School staff Community organisers Educational Psychologists Course Content True family empowerment Deepening shared stories and understandings Facilitating groups Problem solving process Handling family group communication Allowing direct feedback and challenge between participants in a safe way Building relationships Process: Family members are welcomed: Introductions are carried out, ground rules and aims clarified whilst coffee is drunk. A recap from the last session is carried out: To follow up developments and reflections after the last meeting. One issue is selected for the main focus Issue presentation: The family member who raised the concern is asked questions to tell the ‘story’ of the issue or problem. Additional questions/information from the group about the problem are gathered: Ground rules may need to be observed carefully here. Individual participants need to be kept focused and prevented from leaping to premature conclusions or to making ‘helpful’ suggestions about strategy. Relationship aspects to the problem are explored. Metaphors and analogies are invited. How would a fly on the wall see your relationship? If you were alone together on a desert island, what would it be like? Impact of previous relationships/spillage from one relationship to another are explored. Eg what situation they are reminded of? For instance, does this situation remind you of any of those angry but helpless feelings you had with your other son when he was an adolescent? This provides opportunities to reflect on how emotions rub off on other people. The parent feels really frustrated, and on reflection we can see that so does the child System/Organisation factors (Family system/school and community systems and so on): What aspects help or hinder the problem? For instance, does the pastoral system of the local school provide space, or time and skilled personnel able to counsel this young person and work actively with their parents? Synthesis. At this stage the Graphic facilitator summarises what they have heard. They then go on to describe linkages and patterns in what they have heard. This can be very powerful. The person doing the graphic work has been able to listen throughout the presentation process and will have been struck by strong messages, emotions and images as they have arisen. The story and meaning of what is happening in the situation may become a little clearer at this point. Typical links may be ‘mirrored emotions’ strong themes such as loss and separation issues, or repeated processes such as actions triggering rejection. This step provides an excellent grounding for the next process of deepening understanding. What alternative strategies/interventions are open to be used? Brainstormed and recorded. ’Either/ors’ need to be avoided at this time also. This needs to be a shared session in which the family member who is presenting the concern contributes as much as anyone. Care is needed to ensure that this person is not overloaded with other people’s strategies. The final selection of strategy or strategies from the brainstormed list is the problem presenter’s choice. Strategies might include: a special time for the young person, a meeting with the child’s parents to explore how she is being managed at home and to share tactics, a home-school diary, counselling, or an agreed action plan that all are aware of, agreed sanctions and rewards and so forth. Strategies may productively involve processes of restitution and restoration, when ‘sorry’ is not enough. Making it right, rather than punishments or rewards, may then becomes the focus. First Steps. The problem presenter is finally asked to agree one or two first steps which they can carry out over the next 3-7 days. It can help to assign a ‘coach’ who will check in with them to ensure they have carried out the action they have named. This is a time to be very specific. Steps should be small and achievable. The person is just ‘making a start’. A phone call, or making an agreement with a key other person not present at the meeting would be ideal examples. Final reflections. Sometimes referred to as a ‘round of words’ help with closure for all involved. Reflections are on the process not the problem. In large families this is best done standing in a circle. In smaller groups all can remain sitting. Passing around a ‘listening stick’ or something similar such as a stone or light heighten the significance of the process ending and improve listening. Finally the problem presenter is handed the ‘Graphic’ this is their record of the meeting and can be rolled and presented ceremoniously by the facilitators for maximum effect! If you liked this course you may well like: Parent Solutions