- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
5051 Security courses
IT Technician Training - Job Ready Program + Career Support & Money Back Guarantee
4.5(3)By Studyhub UK
Start Your Journey to Becoming an IT Expert Today, and Make Up to •65,000 The IT field is growing rapidly, and there is a high demand for qualified IT Technicians. With our IT Technician Training, you can learn the skills you need to succeed in this exciting field. We will help you until you find a job, so you won't have to worry about a thing. Just gain knowledge and learn skills, getting you a job is our duty. Enrol today and take your career to the next level! With our program, we go above and beyond traditional training. We understand that landing a job isn't just about having the right skills-it's about having the right support system by your side. That's why we are committed to being with you every step of the way, from your job search to your ultimate success. Our mission is simple: to be your trusted partner and assist you every step of the way until you land the job of your dreams. Why Choose Us Here's what makes our IT Technician Training Program stand out from the crowd: Personalised Job Search Assistance: We're in this together! Our dedicated team will work tirelessly to support your entire job searching process. From crafting a standout resume to submitting it to top companies, we'll ensure you have a compelling application that gets noticed. Expertly Crafted CV: Your resume is your ticket to the interview room. Our professional resume writers will create a customised CV highlighting your unique skills and experiences. This will maximise your chances of standing out among the competition. Strategic Placement: We understand the power of casting a wide net. We'll strategically submit your CV to various platforms and networks, expanding your reach and connecting you with valuable opportunities that align with your career goals. One-On-One Consultation Sessions with Industry Experts: Gain invaluable insights and guidance from seasoned professionals who have thrived in the IT field. Our consultation sessions provide you with insider tips, tricks, and advice, empowering you to navigate the industry with confidence and finesse. Comprehensive Skill Development: Our program is designed to equip you with the most sought-after skills in the IT sector. From mastering cutting-edge tools to honing your IT prowess, we'll ensure you have the knowledge and expertise to excel in any IT-driven environment. Ongoing Support: We understand that the journey to landing your dream job doesn't end with placement. That's why our commitment to your success extends well beyond your initial training. Our support team will be available to answer your questions, provide guidance, and assist you as you progress in your career. Here are the 6 courses we will provide once you enrol in the program: Course 01 : IT Support Technician Course 02 : Network Security and Risk Management Course 03 : CompTIA Network Course 04 : Information Management Course 05 : Web Application Penetration Testing Course Course 06 : CompTIA Cloud+ (CV0-002) These courses will help you to develop your knowledge and skills to become a successful IT Technician. The Program is completed in 5 easy steps: Step 1 - Enrol in the program and start learning from the courses we provide After you enrol in this IT Technician Training Program, you will get lifetime access to 6 premium courses related to IT. These courses will teach you the knowledge and skills required to become a successful IT Technician. Our customer service team will help you and keep in contact with you every step of the way. Step 2 - Complete your courses and get certifications After learning from the courses, you must obtain certificates for each course. There will be exams for every course, and you have to pass them to get your certificate. To pass successfully, you must get 90% marks for the first course and 80% for the rest relevant courses. Once you pass the exams, you will receive hardcopy certificates. These certificates will prove that you're an expert in the subject. Step 3 - Get a consultation session from a professional IT Technician Take your IT skills to new heights with a one-on-one consultation session led by a seasoned professional. Gain invaluable insights, expert tips, and tailored advice that will propel your career forward. Step 4 - Complete the CV and attend the interview Once you've successfully obtained the certifications, our team of professionals will build you a compelling CV and LinkedIn profile. With these powerful tools in hand, you'll be fully prepared to tackle job interviews confidently. Kickstart your IT career with a starting salary ranging from •25,000 to •40,000 annually. Step into the IT industry with the assurance of a promising future. Step 5 - We will not leave you until you find a job Our commitment to your success goes above and beyond. We won't stop until you land that dream job. With personalised support, expert guidance, and unwavering dedication, we'll be by your side until you secure the perfect opportunity. Your job search becomes our mission, ensuring you have the best chance at a successful career in IT. Don't let your dream career as an IT Technician remain out of reach. You just have to learn and gain knowledge and skills. Finding a job is our task! We will remove most of your worries and help you focus on only developing your skills. So join our IT Technician Training Program today, and let us be your trusted partner on your journey to success. CPD 100 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Individuals who are passionate about technology and eager to pursue a career in IT. Those who want to kickstart their journey as an IT technician with comprehensive training and support. Job seekers looking for a competitive edge in the IT job market. Professionals seeking to transition into the IT field and require specialised training. Individuals who value personalised guidance and mentorship throughout their career development. Requirements No experience required. Just enrol & start learning. Career path Our IT Technician Training program opens doors to a range of exciting career paths. Start as an IT Support Technician and progress to roles like Network Administrator, Systems Administrator, IT Security Specialist, IT Project Manager, or IT Consultant. With each step, you'll gain valuable experience and opportunities for salary growth. Your journey in the IT industry starts here. Certificates CPD Accredited e-Certificate Digital certificate - Included CPD Accredited Framed (Hardcopy) Certificate Hard copy certificate - Included Enrolment Letter Digital certificate - Included Student ID Card Digital certificate - Included

Cisco Understanding Cisco Cybersecurity Operations Fundamentals v1.0 (CBROPS)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for individuals seeking a role as an associate-level cybersecurity analyst and IT professionals desiring knowledge in Cybersecurity operations or those in pursuit of the Cisco Certified CyberOps Associate certification including Students pursuing a technical degree Current IT professionals Recent college graduates with a technical degree Overview After taking this course, you should be able to Explain how a Security Operations Center (SOC) operates and describe the different types of services that are performed from a Tier 1 SOC analyst's perspective. Explain Network Security Monitoring (NSM) tools that are available to the network security analyst. Explain the data that is available to the network security analyst. Describe the basic concepts and uses of cryptography. Describe security flaws in the TCP/IP protocol and how they can be used to attack networks and hosts. Understand common endpoint security technologies. Understand the kill chain and the diamond models for incident investigations, and the use of exploit kits by threat actors. Identify resources for hunting cyber threats. Explain the need for event data normalization and event correlation. Identify the common attack vectors. Identify malicious activities. Identify patterns of suspicious behaviors. Conduct security incident investigations. Explain the use of a typical playbook in the SOC. Explain the use of SOC metrics to measure the effectiveness of the SOC. Explain the use of a workflow management system and automation to improve the effectiveness of the SOC. Describe a typical incident response plan and the functions of a typical Computer Security Incident Response Team (CSIRT). Explain the use of Vocabulary for Event Recording and Incident Sharing (VERIS) to document security incidents in a standard format. The Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) v1.0 course teaches you security concepts, common network and application operations and attacks, and the types of data needed to investigate security incidents. This course teaches you how to monitor alerts and breaches, and how to understand and follow established procedures for response to alerts converted to incidents. Through a combination of lecture, hands-on labs, and self-study, you will learn the essential skills, concepts, and technologies to be a contributing member of a cybersecurity operations center (SOC) including understanding the IT infrastructure, operations, and vulnerabilities. This course helps you prepare for the Cisco Certified CyberOps Associate certification and the role of a Junior or Entry-level cybersecurity operations analyst in a SOC. Course Outline Defining the Security Operations Center Understanding Network Infrastructure and Network Security Monitoring Tools Exploring Data Type Categories Understanding Basic Cryptography Concepts Understanding Common TCP/IP Attacks Understanding Endpoint Security Technologies Understanding Incident Analysis in a Threat-Centric SOC Identifying Resources for Hunting Cyber Threats Understanding Event Correlation and Normalization Identifying Common Attack Vectors Identifying Malicious Activity Identifying Patterns of Suspicious Behavior Conducting Security Incident Investigations Using a Playbook Model to Organize Security Monitoring Understanding SOC Metrics Understanding SOC Workflow and Automation Describing Incident Response Understanding the Use of VERIS Understanding Windows Operating System Basics Understanding Linux Operating System Basics Additional course details: Nexus Humans Cisco Understanding Cisco Cybersecurity Operations Fundamentals v1.0 (CBROPS) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Cisco Understanding Cisco Cybersecurity Operations Fundamentals v1.0 (CBROPS) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

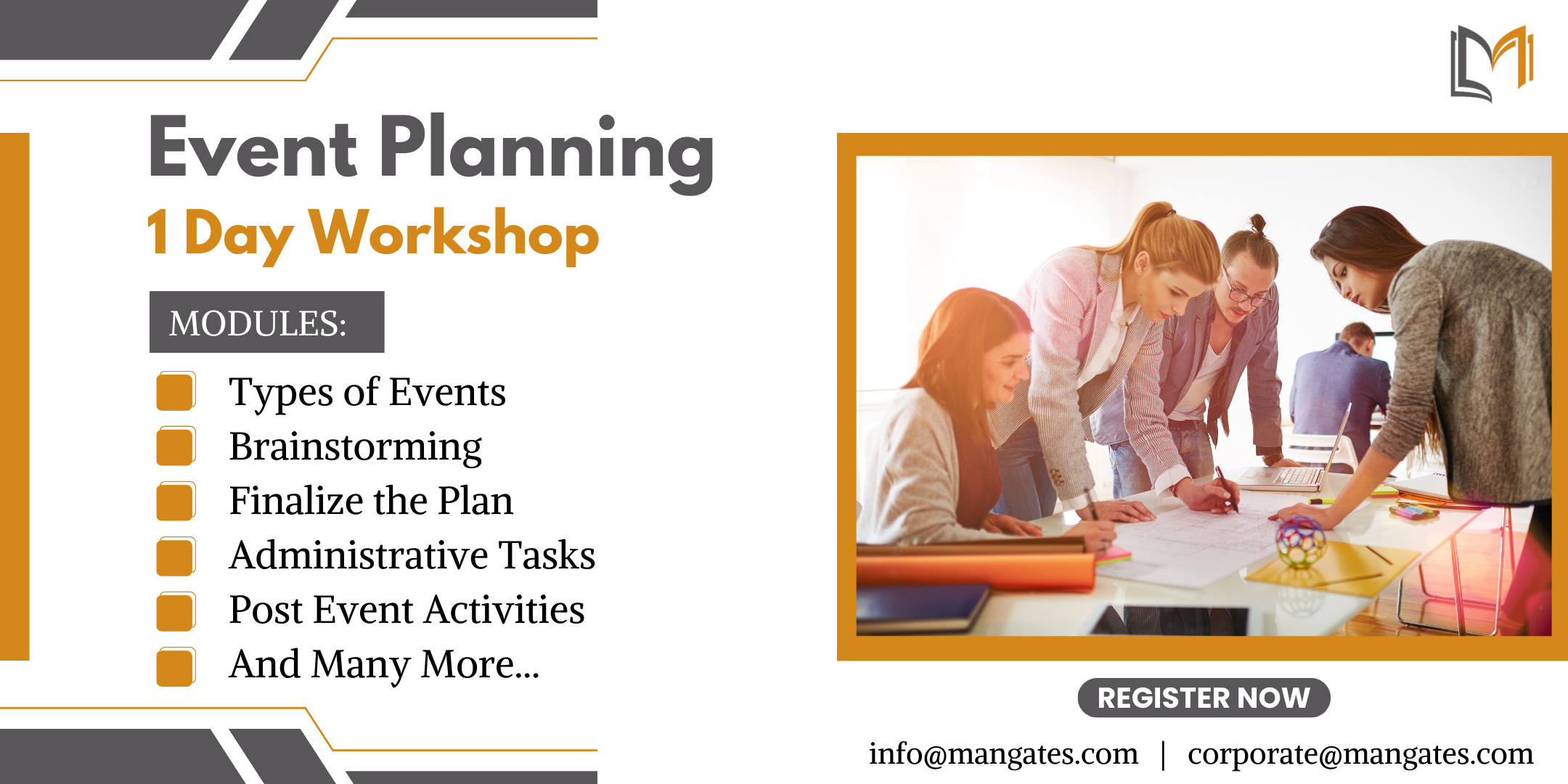
The Ultimate Guide to Event Planning - 1 Day Workshop in Brighton
By Mangates
Event Planning 1 Day Training in Brighton
Overview This comprehensive course on Door Supervisor will deepen your understanding on this topic. After successful completion of this course you can acquire the required skills in this sector. This Door Supervisor comes with accredited certification from CPD, which will enhance your CV and make you worthy in the job market. So enrol in this course today to fast track your career ladder. How will I get my certificate? You may have to take a quiz or a written test online during or after the course. After successfully completing the course, you will be eligible for the certificate. Who is this course for? There is no experience or previous qualifications required for enrolment on this Door Supervisor. It is available to all students, of all academic backgrounds. Requirements Our Door Supervisor is fully compatible with PC's, Mac's, Laptop, Tablet and Smartphone devices. This course has been designed to be fully compatible with tablets and smartphones so you can access your course on Wi-Fi, 3G or 4G. There is no time limit for completing this course, it can be studied in your own time at your own pace. Career path Learning this new skill will help you to advance in your career. It will diversify your job options and help you develop new techniques to keep up with the fast-changing world. This skillset will help you to- Open doors of opportunities Increase your adaptability Keep you relevant Boost confidence And much more! Course Curriculum 11 sections • 10 lectures • 04:01:00 total length •Definition and Importance of Security: 00:16:00 •Career Prospect of Security Guard in the UK: 00:11:00 •Security Risk Analysis and Risk Reduction: 00:25:00 •Physical and Information Security Protection: 00:36:00 •Response to Immediate Crisis: 00:26:00 •The Use of Technology for Managing Security: 00:25:00 •General Patrol Tactics and Techniques: 00:25:00 •Public Relations and Traffic Control: 00:21:00 •Violence in the Workplace: 00:27:00 •Laws and Regulations: 00:29:00

CWNA training course description A hands-on course focusing on the technical support of WiFi. Wireless LANs are often seen as simple communications that are simply installed and then left alone to work. This course ensures that delegates will be able to install WiFi networks which work but also enable the delegates to troubleshoot WiFi when it does go wrong. What will you learn Compare 802.11 standards. Configure WiFi networks. Troubleshoot WiFi networks using spectrum analysers, Wireshark and other tools. Implement 802.11 security. Perform RF surveys. CWNA training course details Who will benefit: Technical staff working with WiFi networks. Anyone wishing to pass the CWNA exam. Prerequisites: Intro to data communications & networking Duration 5 days CWNA training course contents Introduction History, standards. RF fundamentals What is RF? Wavelength, Frequency, Amplitude, Phase. Wave behaviour. RF components. Watts, mW, dB, SNR, Link budgets. Hands on Spectrum analysis. Listing WiFi networks. WiFi connection. inSSIDer. Antennas Radiation envelopes, polar charts, gain, Antenna types. Line of Sight, MIMO. Hands on Connecting, installing, changing antennae. RSSI values. 802.11 802.11-2007, 802.11 post 2007, 802.11 drafts. 802.11 b/g/n. Hands on WiFi performance measurement. Spread Spectrum RF frequency bands, FHSS, DSSS, OFDM. Channels. Hands on Configuring channels. Topologies Mesh, Access points, distribution systems, SSID. Hands on AP configuration. Client connection profiles. 802.11 MAC CSMA/CA, Management frames, control frames, data frames. Passive scanning, active scanning. Open system authentication. Shared Key authentication. Association. RTS/CTS. Power management. Hands on Capturing frames, analysing frames. WiFi architecture WiFi client, WLAN architecture: Autonomous, Centralised, distributed. WiFi bridges. WiFi routers. PoE. Hands on WLAN controllers. Troubleshooting RF interference, multipath, adjacent channels, low SNR, mismatched power. Coverage, capacity. 802.11 Security Basics, Legacy security: WEP, MAC filters, SSID cloaking. PSK, 8021.X/EAP, WPA/WPA2. TKIP/ CCMP encryption. Guest WLANs. Wireless attacks, intrusion monitoring. Hands on WEP cracking, WPA2 configuration. RADIUS. RF Site surveys Protocol and spectrum analysis, coverage analysis. Site survey tools. Hands on Performing a site survey.

Register on the The Complete Ethical Hacking Course today and build the experience, skills and knowledge you need to enhance your professional development and work towards your dream job. Study this course through online learning and take the first steps towards a long-term career. The course consists of a number of easy to digest, in-depth modules, designed to provide you with a detailed, expert level of knowledge. Learn through a mixture of instructional video lessons and online study materials. Receive online tutor support as you study the course, to ensure you are supported every step of the way. Get an e-certificate as proof of your course completion. The The Complete Ethical Hacking Course is incredibly great value and allows you to study at your own pace. Access the course modules from any internet-enabled device, including computers, tablet, and smartphones. The course is designed to increase your employability and equip you with everything you need to be a success. Enrol on the now and start learning instantly! What You Get With The The Complete Ethical Hacking Course Receive a e-certificate upon successful completion of the course Get taught by experienced, professional instructors Study at a time and pace that suits your learning style Get instant feedback on assessments 24/7 help and advice via email or live chat Get full tutor support on weekdays (Monday to Friday) Course Design The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of Video lessons Online study materials Certification Upon successful completion of the course, you will be able to obtain your course completion e-certificate free of cost. Print copy by post is also available at an additional cost of £9.99 and PDF Certificate at £4.99. Who Is This Course For: The course is ideal for those who already work in this sector or are an aspiring professional. This course is designed to enhance your expertise and boost your CV. Learn key skills and gain a professional qualification to prove your newly-acquired knowledge. Requirements: The online training is open to all students and has no formal entry requirements. To study the The Complete Ethical Hacking Course, all your need is a passion for learning, a good understanding of English, numeracy, and IT skills. You must also be over the age of 16. Course Content Introduction to Ethical Hacking What is an Ethical Hacker 00:07:00 Terminology Crash Course pt. 1 00:09:00 Terminology Crash Course pt. 2 00:14:00 Terminology Crash Course pt. 3 00:08:00 Legal Considerations 00:11:00 Reconnaissance - Surveying the Attack Surface Surveying the Attack Surface 00:10:00 Recon Types 00:08:00 Passive Recon Part 1 00:07:00 Passive Recon Part 2 00:10:00 Active Recon 00:15:00 Recon Walkthrough Tools Summary 00:14:00 Maltego Demo 00:07:00 FOCA Demo 00:05:00 DEMO - Harvester 00:02:00 Scanning and Enumeration - Getting Down to Business Scanning & enumeration 00:08:00 Identifying Active Hosts pt. 1 00:10:00 Identifying Active Hosts pt. 2 00:13:00 Identifying Active Services 00:18:00 OS and Services Fingerprinting 00:15:00 Network Mapping 00:10:00 Final Thoughts 00:05:00 DEMO - Nmap Syntax pt. 1 00:14:00 DEMO - Nmap Syntax pt. 2 00:16:00 DEMO - Nmap Hosts Discovery 00:12:00 DEMO - Nmap Service Discovery 00:17:00 DEMO - Nmap Scripts 00:11:00 DEMO - Masscan 00:11:00 Network Presence Network Insecurity 00:04:00 Sniffing and Spoofing 00:13:00 Sniffing Tools 00:09:00 Spoofing, Crypto and Wifi 00:15:00 DEMO - tcpdump 00:11:00 DEMO - Wireshark 00:11:00 DEMO - Ettercap 00:13:00 DEMO - Burp Suite 00:15:00 DEMO - Scapy 00:10:00 Attacking Security Overview pt. 1: Windows Architecture 00:18:00 Security Overview pt. 2: Credentials Security 00:16:00 Security Overview pt. 3: Memory Corruption and Exploitation 00:16:00 Windows Hacking Basics 00:20:00 Local Access and Privilege Escalation 00:20:00 Dumping Hashes and Cracking Passwords 00:18:00 Linux Attacking Basics pt. 1 00:13:00 Linux Attacking Basics pt. 2 00:14:00 References 00:08:00 DEMO - Windows MSF Exploit pt. 1 00:13:00 DEMO - Windows MSF Exploit pt. 2 00:15:00 DEMO - Post Exploitation Activities 00:13:00 DEMO - Mimikatz 00:07:00 DEMO - Hashcat 00:08:00 DEMO - Konboot 00:13:00 DEMO - Post Exploitation Windows CMD 00:14:00 DEMO - Post Exploitation Windows Powershell 00:13:00 DEMO - Attacking Linux targets pt. 1aa 00:10:00 DEMO - Attacking Linux targets pt. 1 00:13:00 Web Hacking Introduction to Web Hacking 00:03:00 Web Security Architecture Overview pt. 1 00:17:00 Web Security Architecture Overview pt. 2 00:12:00 Attacking the Web Server pt. 1 00:10:00 Attacking the Web Server pt. 2 00:11:00 Attacking the Platform pt. 1 00:19:00 Attacking the Platform pt. 2 00:08:00 Attacking the Technology pt. 1 00:21:00 Attacking the Technology pt. 2 00:17:00 OWASP Top 10 pt. 1 00:09:00 OWASP Top 10 pt. 2 00:21:00 Attacking the Business Logic pt. 1 00:11:00 Attacking the Business Logic pt. 2 00:15:00 Tools and Methodology 00:20:00 References 00:05:00 DEMO - OWASP Mutillidae 00:09:00 SQLI 00:07:00 SQL Map Intro 00:08:00 SQL Map 00:25:00 DEMO - Burpsuite 00:37:00 DEMO - Burpsuite XSS Hunter 00:16:00 DEMO - mitmproxy 00:10:00 DEMO - Skipfish pt.1 00:05:00 DEMO - Skipfish pt.2 00:05:00 Social Engineering - Hacking Humans Social Engineering Basics 00:15:00 Social Engineering Methods 00:16:00 Tools and Techniques pt. 1 00:15:00 Tools and Techniques pt. 2 00:12:00 Tools and Techniques pt. 3 00:09:00 Physical Security Considerations 00:13:00 Final Thoughts99 00:11:00 DEMO - Credential harvesting 00:02:00 DEMO - Website cloning 00:06:00 DEMO - Automating an attack 00:03:00 DEMO - Anti-virus evasion pt. 1 00:08:00 DEMO - Anti-virus evasion pt. 2 00:12:00 Frequently Asked Questions Are there any prerequisites for taking the course? There are no specific prerequisites for this course, nor are there any formal entry requirements. All you need is an internet connection, a good understanding of English and a passion for learning for this course. Can I access the course at any time, or is there a set schedule? You have the flexibility to access the course at any time that suits your schedule. Our courses are self-paced, allowing you to study at your own pace and convenience. How long will I have access to the course? For this course, you will have access to the course materials for 1 year only. This means you can review the content as often as you like within the year, even after you've completed the course. However, if you buy Lifetime Access for the course, you will be able to access the course for a lifetime. Is there a certificate of completion provided after completing the course? Yes, upon successfully completing the course, you will receive a certificate of completion. This certificate can be a valuable addition to your professional portfolio and can be shared on your various social networks. Can I switch courses or get a refund if I'm not satisfied with the course? We want you to have a positive learning experience. If you're not satisfied with the course, you can request a course transfer or refund within 14 days of the initial purchase. How do I track my progress in the course? Our platform provides tracking tools and progress indicators for each course. You can monitor your progress, completed lessons, and assessments through your learner dashboard for the course. What if I have technical issues or difficulties with the course? If you encounter technical issues or content-related difficulties with the course, our support team is available to assist you. You can reach out to them for prompt resolution.

Safety, Security & Situational Awareness for Women (S3AW)
By Stirling Defence
Be prepared, not paranoid! Course curriculum What are we going to teach you? 1 Instructions for this course Enrollment Process Trouble Shooting 2 Welcome to Safety, Security & Situational Awareness for Women How to use the course player 3 Let's get started! The Why Lesson 1 - Introduction to Safety, Security, Situational Awareness for Women Lesson 2 - Principles of Real-time Behaviour Lesson 3 - How to Recognise Threats through Behaviour Observation Test Lesson 4 - The Predator Mindset Lesson 5- The Dynamics of the Brain Lesson 6 - Indicators of Spiking, Common Date Rape Narcotics and their Effects. Lesson 7 - Colour Coded Risk Evaluation Final Assessment Training and Evaluation Feedback Form 4 Next Steps... Before you go... Recommended Reading List

IT Security & Computer Maintenance Training
By Wise Campus
IT Security & Computer Maintenance Training Open up your IT passion by unlocking our IT Security & Computer Maintenance Training course! Do you want to begin a career as a professional in IT security? Do you want to expand your knowledge about IT security? With the help of this IT Security & Computer Maintenance Training course, you'll be more determined than ever to advance your professional career and broaden your knowledge in this IT security area. Although they sound similar, information security and IT security refer to different types of security. Information security refers to the practices and tools used to prevent unauthorised access to sensitive corporate data, whereas IT security is the protection of digital data through computer network security. Even though maintaining IT security may be expensive, a significant breach may cost a company far more. This IT Security & Computer Maintenance Training Course will provide you with a solid foundation so that you can develop the confidence to become an expert in IT Security and acquire more sophisticated skills to fill in the gaps for increased effectiveness and productivity. If you think you have what it takes to enter this IT security field, an IT security course can help you with your initial training and job preparation. IT Security is ready with all the necessary data that is meant to instruct and direct people in the requirements for this position. Don't wait any longer. Enrol in our IT Security & Computer Maintenance Training course to become a certified IT security professional. IT Security & Computer Maintenance Training Course This Criminology and IT Security & Computer Maintenance Training Course includes a FREE PDF Certificate. Lifetime access to this IT Security & Computer Maintenance Training Course Instant access to this Criminology and IT Security & Computer Maintenance Training Course Get FREE Tutor Support to this IT Security & Computer Maintenance Training Course IT Security & Computer Maintenance Training Ignite your passion with our IT Security & Computer Maintenance Training course! Ready to start a career in IT Security & Computer Maintenance Training? This course equips you with foundational skills to secure digital data and network systems, essential for preventing costly breaches. You’ll learn the critical distinctions between information security and IT Security & Computer Maintenance Training, gaining advanced tools for productivity and effectiveness. Develop the confidence to excel as a certified professional in IT Security & Computer Maintenance Training. Don’t miss out—enrol today and set yourself up for success in this vital field! Who is this course for? IT Security & Computer Maintenance Training Anyone who wants to work in the IT industry can take our IT Security & Computer Maintenance Training course. Requirements IT Security & Computer Maintenance Training To enrol in this IT Security & Computer Maintenance Training Course, students must fulfil the following requirements: Good Command over English language is mandatory to enrol in our IT Security & Computer Maintenance Training Course. Be energetic and self-motivated to complete our IT Security & Computer Maintenance Training Course. Basic computer Skill is required to complete our IT Security & Computer Maintenance Training Course. If you want to enrol in our IT Security & Computer Maintenance Training Course, you must be at least 15 years old. Career path IT Security & Computer Maintenance Training Many doors in the job market will be made available by the IT Security & Computer Maintenance Training course. For instance, an IT technician, a cyber security analyst, or a penetration tester. The average salary for IT Security & Computer Maintenance Training professionals in the UK ranges between £60,000 and £100,000 per annum.

IPsec training course description This hands on course focuses on IPsec VPNs. Rather than focusing on one implementation this course concentrates on the technologies and protocols of IPsec. Starting with an overview of the complete IPsec architecture the course then moves onto ESP packet analysis along with encryption and authentication provided. IKEv1 and IKEv2 are both covered in detail. Having covered IPsec with pre shared keys the course then moves onto IPsec with certificates followed by IPsec issues. The course is vendor neutral with hands on with both Cisco and Microsoft implementations. What will you learn Explain how IPsec works. Explain the role of AH, ESP and IKE. Configure IPsec. Troubleshoot IPsec. IPsec training course details Who will benefit: Technical staff working with IPsec. Prerequisites: Definitive IP VPNs for engineers. Duration 3 days IPsec training course contents What is IPsec? How to spell IPsec, IPsec is IP security, confidentiality, integrity, authenticity, replay protection, what is a VPN? Network layer security, IPsec and IPv4, IPsec and IPv6, the suite of protocols, the standard, IPsec RFCs, IPsec history. Hands on Analysis of 'normal' IP packets. IPsec architecture The IPsec protocols, AH vs ESP, Why two headers? transport mode, tunnel mode, Remote access VPNs, site to site VPNs, security associations, SA database, Security Parameters Index, implementations: Host tack, Bump in the Stack, Bump in the Wire. Hands on Configuring IPsec. AH What AH does, the stack, The AH header, What is authenticated? Device authentication. AH in transport mode, AH in tunnel mode. Hands on AH packet analysis. ESP What ESP does, the ESP header, ESP in transport mode, ESP in tunnel mode, ESP and SA, ESP and SPI. Hands on ESP packet analysis, policy configuration. IPsec encryption IPsec is a framework, standard algorithms, ESP keys, the role of IKE, key lifetimes, how IKE generates the keys, DES, 3DES, AES, cipher block chaining, counter mode, other encryption. Hands on Encryption configuration. IPsec authentication Authentication types, IPsec authentication, Authentication algorithms: MD5, keyed SHA-1, HMAC-MD5, HMAC-SHA-1, HMAC-RIPEMD, other authentication algorithms. Hands on Authentication configuration. IKE Internet Key Exchange, IKE and the SAD, the two phase negotiation, ISAKMP, ISAKMP header, pre shared keys, digital signatures, public key encryption, Diffie Hellman, proposals, counter proposals, nonces, identities, phase 1 negotiation: main mode, aggressive mode, base mode. Phase 2 negotiation: quick mode, new group mode. Hands on IKE packet analysis. More IKE PFS, IKE and dynamic addresses, XAUTH, hybrid authentication, CRACK, ULA, PIC. User level authentication. IKE renegotiation, heartbeats. Hands on Troubleshooting IPsec. IKEv2 The IKEv2 exchange, IKE_SA_INIT, IKE_AUTH, CREATE_CHILD_SA, IKEv2 packets, the informational exchange. Comparing IKev1 vs IKE v2. Hands on IKEv2 configuration and analysis. PKI What is PKI?, Digital certificates, Certificate authorities, CA servers, RA, VA, certificates, CA hierarchy, CRLs, certificate formats. Hands on installing and configuring certificate servers. IPsec issues NAT, IPsec overhead and fragmentation. Summary IPsec strengths and weaknesses. Where to get further information.

Cyber Security-CPD & IIRSM Approved
By BAB Business Group
Employees, managers and directors should all have a good understanding of the threat posed by cyber-attacks and the importance of guarding against data breaches. This short course will explain why cyber attacks and data breaches happen and provide practical advice on how to set up effective defences. First, the course will identify potential 'cyber threat actors' who initiate cybercrime, along with looking at the main motivations behind cyber-attacks on individuals and organisations. On a more practical level, you'll learn how to recognise and deal effectively with phishing attempts. The course will highlight the importance of keeping passwords secure and cover security for devices, such as smartphones, laptops, tablets or desktop computers. You'll learn how to report a suspected cyber attack, and what to do if you genuinely make a mistake. Finally, we'll underline the importance of cooperation and show how working closely together helps overcome a wide range of cybersecurity issues

Search By Location
- Security Courses in London
- Security Courses in Birmingham
- Security Courses in Glasgow
- Security Courses in Liverpool
- Security Courses in Bristol
- Security Courses in Manchester
- Security Courses in Sheffield
- Security Courses in Leeds
- Security Courses in Edinburgh
- Security Courses in Leicester
- Security Courses in Coventry
- Security Courses in Bradford
- Security Courses in Cardiff
- Security Courses in Belfast
- Security Courses in Nottingham