- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
20555 Other courses
Tired of searching and accumulating all the relevant courses for this specific field? It takes a substantial amount of your time and, more importantly, costs you a fortune! Well, we have just come up with the ultimate solution for you by giving this all-inclusive Human Resource: Recruitment & Selection Training mega bundle. This 33 courses mega bundle keeps you up-to-date in this field and takes you one step ahead of others. Keeping in mind the latest advancements in this ever-emerging sector, the Human Resource: Recruitment & Selection Training bundle covers all the state-of-the-art tools and techniques required to become a competent worker in this area. You will encounter specific courses relevant to the sector. We take you from the most introductory fundamentals to advance knowledge in a step-by-step manner. In addition, the Human Resource: Recruitment & Selection Training bundle also consists of courses related to some soft skills that you will need to succeed in any industry or job sector. This Human Resource: Recruitment & Selection Training Bundle consists of the following premium courses: Course 01: Recruitment Officer Diploma Course 02: HR and Recruitment Consultant Training Course 03: Employment Law Course 04: Key Performance Indicators Professional Course 05: HR and Marketing Level 4 Course 06: HR - Crisis Communication Course 07: HR Assistant Skills Certification Course 08: People Management Skills Level 3 Course 09: Team Management Course 10: Dealing With Difficult People Training Course Course 11: Virtual Interviewing for HR Course 12: Delegation Skills Course 13: Interpersonal Skills in Management Course 14: Effective Listening Skills for Leaders Course 15: Motivational Interviewing Course 16: Motivation Skills Course 17: Human Resources (HR) Audit Course 18: Payroll Management Course Course 19: Office Administration Certificate Course 20: Contract Manager Diploma Course 21: Stress Management Training Course 22: Positive Psychology Masterclass Course 23: Public Speaking and Presentation Skill Course Course 24: Emotional Intelligence and Human Behaviour Course 25: Virtual Training Masterclass Course 26: Complete Guide to HR systems Course 27: HR Practice Essentials Level 4 Course 28: Personal and Networking Skills Course 29: Performance Centered Asset Management Course 30: Office Skills and Administration Management Diploma Moreover, this bundles include 3 career-focused courses: Course 01: Career Development Plan Fundamentals Course 02: CV Writing and Job Searching Course 03: Interview Skills: Ace the Interview Our cutting-edge learning package offers top-notch digital aid and first-rate tutor support. You will acquire the crucial hard and soft skills needed for career advancement because this bundle has been thoroughly examined and is career-friendly. So don't overthink! Enrol today. Learning Outcomes This unique Human Resource: Recruitment & Selection Training mega bundle will help you to- Quench your thirst for knowledge Be up-to-date about the latest advancements Achieve your dream career goal in this sector Know the applicable rules and regulations needed for a professional in this area Acquire some valuable knowledge related to Human Resource: Recruitment & Selection Training to uplift your morale The bundle incorporates basic to advanced level skills to shed some light on your way and boost your career. Hence, you can strengthen your expertise and essential knowledge, which will assist you in reaching your goal. Moreover, you can learn from any place in your own time without travelling for classes. Certificate: PDF Certificate: Free for all 33 courses Hard Copy Certificate: Free (For The Title Course: Previously it was £10) CPD 330 CPD hours / points Accredited by CPD Quality Standards Who is this course for? The Human Resource: Recruitment & Selection Training bundle is designed to assist anyone with a curious mind, anyone looking to boost their CVs or individuals looking to upgrade their career to the next level can also benefit from the learning materials. Requirements The courses in this bundle has been designed to be fully compatible with tablets and smartphones. Career path This Human Resource: Recruitment & Selection Training bundle will give you an edge over other competitors and will open the doors for you to a plethora of career opportunities. Certificates Certificate of completion Digital certificate - Included Certificate of completion Hard copy certificate - Included You will get the Hard Copy certificate for the title course (Recruitment Officer Diploma) absolutely Free! Other Hard Copy certificates are available for £10 each. Please Note: The delivery charge inside the UK is £3.99, and the international students must pay a £9.99 shipping cost.

Tired of searching and accumulating all the relevant courses for this specific field? It takes a substantial amount of your time and, more importantly, costs you a fortune! Well, we have just come up with the ultimate solution for you by giving this all-inclusive Healthcare and Health and Safety mega bundle. This 33 courses mega bundle keeps you up-to-date in this field and takes you one step ahead of others. Keeping in mind the latest advancements in this ever-emerging sector, the Healthcare and Health and Safety bundle covers all the state-of-the-art tools and techniques required to become a competent worker in this area. You will encounter specific courses relevant to the sector. We take you from the most introductory fundamentals to advance knowledge in a step-by-step manner. In addition, the Healthcare and Health and Safety bundle also consists of courses related to some soft skills that you will need to succeed in any industry or job sector. This Healthcare and Health and Safety Bundle consists of the following premium courses: Course 01: Healthcare Assistant Course 02: English for Healthcare Course 03: Workplace Health, Safety and Welfare Course 04: Social Work Practice Course 05: Pandemics: Risk, Impact & Mitigation Course 06: Oxygen First Aid Training Course 07: Play Therapy Course 08: Journal Therapy Course 09: Childminder & Nursery Worker Course 10: Internet Safety for the children Course 11: First Aid at Work Course 12: Ayurveda: Herbal Remedies & Lifestyle Course 13: Autism Awareness Course 14: Asperger Syndrome Awareness Course 15: ADHD Awareness Course 16: Dyslexia Awareness Training Course Course 17: Bipolar Disorder Course 18: CBT (Cognitive Behavioural Therapy) Course 19: Anti Social Behaviour: Understanding & Preventing Course 20: Mental Health Care Training - MCA & DOLS Course 21: Diploma in Child Psychology and Care Course 22: Mental Capacity Assessment Course 23: Child and Adolescent Mental Health Course 24: Mental Wellbeing Practitioner Course 25: Child Immunisation Training - Level 3 Course 26: Vaccine & Vaccination Course 27: Health & Safety Training for Homeworkers Course 28: Diabetes Awareness & Care Course 29: Adult Patient Care Course 30: Occupational Therapy Diploma Level 3 Moreover, this bundles include 3 career-focused courses: Course 01: Career Development Plan Fundamentals Course 02: CV Writing and Job Searching Course 03: Interview Skills: Ace the Interview Our cutting-edge learning package offers top-notch digital aid and first-rate tutor support. You will acquire the crucial hard and soft skills needed for career advancement because this bundle has been thoroughly examined and is career-friendly. So don't overthink! Enrol today. Learning Outcomes This unique Healthcare and Health and Safety mega bundle will help you to- Quench your thirst for knowledge Be up-to-date about the latest advancements Achieve your dream career goal in this sector Know the applicable rules and regulations needed for a professional in this area Acquire some valuable knowledge related to Healthcare and Health and Safety to uplift your morale The bundle incorporates basic to advanced level skills to shed some light on your way and boost your career. Hence, you can strengthen your expertise and essential knowledge, which will assist you in reaching your goal. Moreover, you can learn from any place in your own time without travelling for classes. Certificate: PDF Certificate: Free for all 33 courses Hard Copy Certificate: Free (For The Title Course: Previously it was £10) CPD 330 CPD hours / points Accredited by CPD Quality Standards Who is this course for? The Healthcare and Health and Safety bundle is designed to assist anyone with a curious mind, anyone looking to boost their CVs or individuals looking to upgrade their career to the next level can also benefit from the learning materials. Requirements The courses in this bundle has been designed to be fully compatible with tablets and smartphones. Career path This Healthcare and Health and Safety bundle will give you an edge over other competitors and will open the doors for you to a plethora of career opportunities. Certificates Certificate of completion Digital certificate - Included Certificate of completion Hard copy certificate - Included You will get the Hard Copy certificate for the title course (Healthcare Assistant) absolutely Free! Other Hard Copy certificates are available for £10 each. Please Note: The delivery charge inside the UK is £3.99, and the international students must pay a £9.99 shipping cost.
Tired of searching and accumulating all the relevant courses for this specific field? It takes a substantial amount of your time and, more importantly, costs you a fortune! Well, we have just come up with the ultimate solution for you by giving this all-inclusive Health and Social Care mega bundle. This 33 courses mega bundle keeps you up-to-date in this field and takes you one step ahead of others. Keeping in mind the latest advancements in this ever-emerging sector, the Health and Social Care bundle covers all the state-of-the-art tools and techniques required to become a competent worker in this area. You will encounter specific courses relevant to the sector. We take you from the most introductory fundamentals to advance knowledge in a step-by-step manner. In addition, the Health and Social Care bundle also consists of courses related to some soft skills that you will need to succeed in any industry or job sector. This Health and Social Care Bundle consists of the following premium courses: Course 01: Health and Social Care - Level 3 Course 02: Social Work Practice Course 03: Human Rights Course 04: English for Healthcare Course 05: Pandemics: Risk, Impact & Mitigation Course 06: Oxygen First Aid Training Course 07: Child Immunisation Training - Level 3 Course 08: Vaccine & Vaccination Course 09: Health & Safety Training for Homeworkers Course 10: Diabetes Awareness & Care Course 11: Adult Patient Care Course 12: Occupational Therapy Diploma Level 3 Course 13: Anti Social Behaviour: Understanding & Preventing Course 14: Mental Health Care Training - MCA & DOLS Course 15: Diploma in Child Psychology and Care Course 16: Mental Capacity Assessment Course 17: Child and Adolescent Mental Health Course 18: Mental Wellbeing Practitioner Course 19: Autism Awareness Course 20: Asperger Syndrome Awareness Course 21: ADHD Awareness Course 22: Dyslexia Awareness Training Course Course 23: Bipolar Disorder Course 24: CBT (Cognitive Behavioural Therapy) Course 25: Play Therapy Course 26: Journal Therapy Course 27: Childminder & Nursery Worker Course 28: Internet Safety for the children Course 29: First Aid at Work Course 30: Ayurveda: Herbal Remedies & Lifestyle Moreover, this bundles include 3 career-focused courses: Course 01: Career Development Plan Fundamentals Course 02: CV Writing and Job Searching Course 03: Interview Skills: Ace the Interview Our cutting-edge learning package offers top-notch digital aid and first-rate tutor support. You will acquire the crucial hard and soft skills needed for career advancement because this bundle has been thoroughly examined and is career-friendly. So don't overthink! Enrol today. Learning Outcomes This unique Health and Social Care mega bundle will help you to- Quench your thirst for knowledge Be up-to-date about the latest advancements Achieve your dream career goal in this sector Know the applicable rules and regulations needed for a professional in this area Acquire some valuable knowledge related to Health and Social Care to uplift your morale The bundle incorporates basic to advanced level skills to shed some light on your way and boost your career. Hence, you can strengthen your expertise and essential knowledge, which will assist you in reaching your goal. Moreover, you can learn from any place in your own time without travelling for classes. Certificate: PDF Certificate: Free for all 33 courses Hard Copy Certificate: Free (For The Title Course: Previously it was £10) CPD 330 CPD hours / points Accredited by CPD Quality Standards Who is this course for? The Health and Social Care bundle is designed to assist anyone with a curious mind, anyone looking to boost their CVs or individuals looking to upgrade their career to the next level can also benefit from the learning materials. Requirements The courses in this bundle has been designed to be fully compatible with tablets and smartphones. Career path This Health and Social Care bundle will give you an edge over other competitors and will open the doors for you to a plethora of career opportunities. Certificates Certificate of completion Digital certificate - Included Certificate of completion Hard copy certificate - Included You will get the Hard Copy certificate for the title course (Health and Social Care - Level 3) absolutely Free! Other Hard Copy certificates are available for £10 each. Please Note: The delivery charge inside the UK is £3.99, and the international students must pay a £9.99 shipping cost.

Tired of searching and accumulating all the relevant courses for this specific field? It takes a substantial amount of your time and, more importantly, costs you a fortune! Well, we have just come up with the ultimate solution for you by giving this all-inclusive Office Management and Behaviour Management mega bundle. This 33 courses mega bundle keeps you up-to-date in this field and takes you one step ahead of others. Keeping in mind the latest advancements in this ever-emerging sector, the Office Management and Behaviour Management bundle covers all the state-of-the-art tools and techniques required to become a competent worker in this area. You will encounter specific courses relevant to the sector. We take you from the most introductory fundamentals to advance knowledge in a step-by-step manner. In addition, the Office Management and Behaviour Management bundle also consists of courses related to some soft skills that you will need to succeed in any industry or job sector. This Office Management and Behaviour Management Bundle consists of the following premium courses: Course 01: Office Management Course 02: Office Skills and Administration Level 3 Course 03: Office Admin and Reception Course 04: Stress Management Training Course 05: Positive Psychology Masterclass Course 06: Dialectical Behaviour Therapy Course 07: Emotional Intelligence and Human Behaviour Course 08: Virtual Training Masterclass Course 09: Recruitment Officer Diploma Course 10: HR and Recruitment Consultant Training Course 11: Effective Listening Skills for Leaders Course 12: Motivational Interviewing Course 13: Motivation Skills Course 14: People Management Skills Level 3 Course 15: Virtual Interviewing for HR Course 16: Contract Manager Diploma Course 17: Delegation Skills Course 18: Interpersonal Skills in Management Course 19: HR Advisor and Recruitment Training Diploma Course 20: HR and Marketing Level 4 Course 21: HR Practice Essentials Level 4 Course 22: HR - Crisis Communication Course 23: HR Assistant Skills Certification Course 24: Personal and Networking Skills Course 25: Performance Centered Asset Management Course 26: Advanced Excel Course (Formula, VLOOKUP & Power Query) Course 27: Team Management Course 28: Dealing With Difficult People Training Course Course 29: HR Management Level 3 Course 30: HR Management and Employment Law Diploma Moreover, this bundles include 3 career-focused courses: Course 01: Career Development Plan Fundamentals Course 02: CV Writing and Job Searching Course 03: Interview Skills: Ace the Interview Our cutting-edge learning package offers top-notch digital aid and first-rate tutor support. You will acquire the crucial hard and soft skills needed for career advancement because this bundle has been thoroughly examined and is career-friendly. So don't overthink! Enrol today. Learning Outcomes This unique Office Management and Behaviour Management mega bundle will help you to- Quench your thirst for knowledge Be up-to-date about the latest advancements Achieve your dream career goal in this sector Know the applicable rules and regulations needed for a professional in this area Acquire some valuable knowledge related to Office Management and Behaviour Management to uplift your morale The bundle incorporates basic to advanced level skills to shed some light on your way and boost your career. Hence, you can strengthen your expertise and essential knowledge, which will assist you in reaching your goal. Moreover, you can learn from any place in your own time without travelling for classes. Certificate: PDF Certificate: Free for all 33 courses Hard Copy Certificate: Free (For The Title Course: Previously it was £10) CPD 330 CPD hours / points Accredited by CPD Quality Standards Who is this course for? The Office Management and Behaviour Management bundle is designed to assist anyone with a curious mind, anyone looking to boost their CVs or individuals looking to upgrade their career to the next level can also benefit from the learning materials. Requirements The courses in this bundle has been designed to be fully compatible with tablets and smartphones. Career path This Office Management and Behaviour Management bundle will give you an edge over other competitors and will open the doors for you to a plethora of career opportunities. Certificates Certificate of completion Digital certificate - Included Certificate of completion Hard copy certificate - Included You will get the Hard Copy certificate for the title course (Office Management) absolutely Free! Other Hard Copy certificates are available for £10 each. Please Note: The delivery charge inside the UK is £3.99, and the international students must pay a £9.99 shipping cost.
Wet Shaving - Advanced Course
By Alan d Hairdressing Education
Learn the classic Wet Shaving in our Advanced Wet Shaving Course. Ideal for qualified barbers looking to learn a new skill and add to their services. In this 2-day course, you’ll learn shaving theory along with skin tensioning and lathering techniques.

Level 3 Certificate in Effective Coaching and Mentoring
By Harpar Qualifications Ltd
This qualification is for learners who wish to gain the knowledge, skills and confidence to effectively coach or mentor people within an organisational context. It is also an ideal qualification for those who wish to commence a career in coaching or mentoring.

SC-200T00 Microsoft Security Operations Analyst
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The Microsoft Security Operations Analyst collaborates with organizational stakeholders to secure information technology systems for the organization. Their goal is to reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders. Responsibilities include threat management, monitoring, and response by using a variety of security solutions across their environment. The role primarily investigates, responds to, and hunts for threats using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security products. Since the Security Operations Analyst consumes the operational output of these tools, they are also a critical stakeholder in the configuration and deployment of these technologies. Learn how to investigate, respond to, and hunt for threats using Microsoft Sentinel, Microsoft Defender for Cloud, and Microsoft 365 Defender. In this course you will learn how to mitigate cyberthreats using these technologies. Specifically, you will configure and use Microsoft Sentinel as well as utilize Kusto Query Language (KQL) to perform detection, analysis, and reporting. The course was designed for people who work in a Security Operations job role and helps learners prepare for the exam SC-200: Microsoft Security Operations Analyst. Prerequisites Basic understanding of Microsoft 365 Fundamental understanding of Microsoft security, compliance, and identity products Intermediate understanding of Windows 10 Familiarity with Azure services, specifically Azure SQL Database and Azure Storage Familiarity with Azure virtual machines and virtual networking Basic understanding of scripting concepts. 1 - Introduction to Microsoft 365 threat protection Explore Extended Detection & Response (XDR) response use cases Understand Microsoft Defender XDR in a Security Operations Center (SOC) Explore Microsoft Security Graph Investigate security incidents in Microsoft Defender XDR 2 - Mitigate incidents using Microsoft 365 Defender Use the Microsoft Defender portal Manage incidents Investigate incidents Manage and investigate alerts Manage automated investigations Use the action center Explore advanced hunting Investigate Microsoft Entra sign-in logs Understand Microsoft Secure Score Analyze threat analytics Analyze reports Configure the Microsoft Defender portal 3 - Protect your identities with Microsoft Entra ID Protection Microsoft Entra ID Protection overview Detect risks with Microsoft Entra ID Protection policies Investigate and remediate risks detected by Microsoft Entra ID Protection 4 - Remediate risks with Microsoft Defender for Office 365 Automate, investigate, and remediate Configure, protect, and detect Simulate attacks 5 - Safeguard your environment with Microsoft Defender for Identity Configure Microsoft Defender for Identity sensors Review compromised accounts or data Integrate with other Microsoft tools 6 - Secure your cloud apps and services with Microsoft Defender for Cloud Apps Understand the Defender for Cloud Apps Framework Explore your cloud apps with Cloud Discovery Protect your data and apps with Conditional Access App Control Walk through discovery and access control with Microsoft Defender for Cloud Apps Classify and protect sensitive information Detect Threats 7 - Respond to data loss prevention alerts using Microsoft 365 Describe data loss prevention alerts Investigate data loss prevention alerts in Microsoft Purview Investigate data loss prevention alerts in Microsoft Defender for Cloud Apps 8 - Manage insider risk in Microsoft Purview Insider risk management overview Create and manage insider risk policies Investigate insider risk alerts Take action on insider risk alerts through cases Manage insider risk management forensic evidence Create insider risk management notice templates 9 - Investigate threats by using audit features in Microsoft Defender XDR and Microsoft Purview Standard Explore Microsoft Purview Audit solutions Implement Microsoft Purview Audit (Standard) Start recording activity in the Unified Audit Log Search the Unified Audit Log (UAL) Export, configure, and view audit log records Use audit log searching to investigate common support issues 10 - Investigate threats using audit in Microsoft Defender XDR and Microsoft Purview (Premium) Explore Microsoft Purview Audit (Premium) Implement Microsoft Purview Audit (Premium) Manage audit log retention policies Investigate compromised email accounts using Purview Audit (Premium) 11 - Investigate threats with Content search in Microsoft Purview Explore Microsoft Purview eDiscovery solutions Create a content search View the search results and statistics Export the search results and search report Configure search permissions filtering Search for and delete email messages 12 - Protect against threats with Microsoft Defender for Endpoint Practice security administration Hunt threats within your network 13 - Deploy the Microsoft Defender for Endpoint environment Create your environment Understand operating systems compatibility and features Onboard devices Manage access Create and manage roles for role-based access control Configure device groups Configure environment advanced features 14 - Implement Windows security enhancements with Microsoft Defender for Endpoint Understand attack surface reduction Enable attack surface reduction rules 15 - Perform device investigations in Microsoft Defender for Endpoint Use the device inventory list Investigate the device Use behavioral blocking Detect devices with device discovery 16 - Perform actions on a device using Microsoft Defender for Endpoint Explain device actions Run Microsoft Defender antivirus scan on devices Collect investigation package from devices Initiate live response session 17 - Perform evidence and entities investigations using Microsoft Defender for Endpoint Investigate a file Investigate a user account Investigate an IP address Investigate a domain 18 - Configure and manage automation using Microsoft Defender for Endpoint Configure advanced features Manage automation upload and folder settings Configure automated investigation and remediation capabilities Block at risk devices 19 - Configure for alerts and detections in Microsoft Defender for Endpoint Configure advanced features Configure alert notifications Manage alert suppression Manage indicators 20 - Utilize Vulnerability Management in Microsoft Defender for Endpoint Understand vulnerability management Explore vulnerabilities on your devices Manage remediation 21 - Plan for cloud workload protections using Microsoft Defender for Cloud Explain Microsoft Defender for Cloud Describe Microsoft Defender for Cloud workload protections Enable Microsoft Defender for Cloud 22 - Connect Azure assets to Microsoft Defender for Cloud Explore and manage your resources with asset inventory Configure auto provisioning Manual log analytics agent provisioning 23 - Connect non-Azure resources to Microsoft Defender for Cloud Protect non-Azure resources Connect non-Azure machines Connect your AWS accounts Connect your GCP accounts 24 - Manage your cloud security posture management? Explore Secure Score Explore Recommendations Measure and enforce regulatory compliance Understand Workbooks 25 - Explain cloud workload protections in Microsoft Defender for Cloud Understand Microsoft Defender for servers Understand Microsoft Defender for App Service Understand Microsoft Defender for Storage Understand Microsoft Defender for SQL Understand Microsoft Defender for open-source databases Understand Microsoft Defender for Key Vault Understand Microsoft Defender for Resource Manager Understand Microsoft Defender for DNS Understand Microsoft Defender for Containers Understand Microsoft Defender additional protections 26 - Remediate security alerts using Microsoft Defender for Cloud Understand security alerts Remediate alerts and automate responses Suppress alerts from Defender for Cloud Generate threat intelligence reports Respond to alerts from Azure resources 27 - Construct KQL statements for Microsoft Sentinel Understand the Kusto Query Language statement structure Use the search operator Use the where operator Use the let statement Use the extend operator Use the order by operator Use the project operators 28 - Analyze query results using KQL Use the summarize operator Use the summarize operator to filter results Use the summarize operator to prepare data Use the render operator to create visualizations 29 - Build multi-table statements using KQL Use the union operator Use the join operator 30 - Work with data in Microsoft Sentinel using Kusto Query Language Extract data from unstructured string fields Extract data from structured string data Integrate external data Create parsers with functions 31 - Introduction to Microsoft Sentinel What is Microsoft Sentinel? How Microsoft Sentinel works When to use Microsoft Sentinel 32 - Create and manage Microsoft Sentinel workspaces Plan for the Microsoft Sentinel workspace Create a Microsoft Sentinel workspace Manage workspaces across tenants using Azure Lighthouse Understand Microsoft Sentinel permissions and roles Manage Microsoft Sentinel settings Configure logs 33 - Query logs in Microsoft Sentinel Query logs in the logs page Understand Microsoft Sentinel tables Understand common tables Understand Microsoft Defender XDR tables 34 - Use watchlists in Microsoft Sentinel Plan for watchlists Create a watchlist Manage watchlists 35 - Utilize threat intelligence in Microsoft Sentinel Define threat intelligence Manage your threat indicators View your threat indicators with KQL 36 - Connect data to Microsoft Sentinel using data connectors Ingest log data with data connectors Understand data connector providers View connected hosts 37 - Connect Microsoft services to Microsoft Sentinel Plan for Microsoft services connectors Connect the Microsoft Office 365 connector Connect the Microsoft Entra connector Connect the Microsoft Entra ID Protection connector Connect the Azure Activity connector 38 - Connect Microsoft Defender XDR to Microsoft Sentinel Plan for Microsoft Defender XDR connectors Connect the Microsoft Defender XDR connector Connect Microsoft Defender for Cloud connector Connect Microsoft Defender for IoT Connect Microsoft Defender legacy connectors 39 - Connect Windows hosts to Microsoft Sentinel Plan for Windows hosts security events connector Connect using the Windows Security Events via AMA Connector Connect using the Security Events via Legacy Agent Connector Collect Sysmon event logs 40 - Connect Common Event Format logs to Microsoft Sentinel Plan for Common Event Format connector Connect your external solution using the Common Event Format connector 41 - Connect syslog data sources to Microsoft Sentinel Plan for syslog data collection Collect data from Linux-based sources using syslog Configure the Data Collection Rule for Syslog Data Sources Parse syslog data with KQL 42 - Connect threat indicators to Microsoft Sentinel Plan for threat intelligence connectors Connect the threat intelligence TAXII connector Connect the threat intelligence platforms connector View your threat indicators with KQL 43 - Threat detection with Microsoft Sentinel analytics What is Microsoft Sentinel Analytics? Types of analytics rules Create an analytics rule from templates Create an analytics rule from wizard Manage analytics rules 44 - Automation in Microsoft Sentinel Understand automation options Create automation rules 45 - Threat response with Microsoft Sentinel playbooks What are Microsoft Sentinel playbooks? Trigger a playbook in real-time Run playbooks on demand 46 - Security incident management in Microsoft Sentinel Understand incidents Incident evidence and entities Incident management 47 - Identify threats with Behavioral Analytics Understand behavioral analytics Explore entities Display entity behavior information Use Anomaly detection analytical rule templates 48 - Data normalization in Microsoft Sentinel Understand data normalization Use ASIM Parsers Understand parameterized KQL functions Create an ASIM Parser Configure Azure Monitor Data Collection Rules 49 - Query, visualize, and monitor data in Microsoft Sentinel Monitor and visualize data Query data using Kusto Query Language Use default Microsoft Sentinel Workbooks Create a new Microsoft Sentinel Workbook 50 - Manage content in Microsoft Sentinel Use solutions from the content hub Use repositories for deployment 51 - Explain threat hunting concepts in Microsoft Sentinel Understand cybersecurity threat hunts Develop a hypothesis Explore MITRE ATT&CK 52 - Threat hunting with Microsoft Sentinel Explore creation and management of threat-hunting queries Save key findings with bookmarks Observe threats over time with livestream 53 - Use Search jobs in Microsoft Sentinel Hunt with a Search Job Restore historical data 54 - Hunt for threats using notebooks in Microsoft Sentinel Access Azure Sentinel data with external tools Hunt with notebooks Create a notebook Explore notebook code

Combined Certificate ISM,ISPS,MLC Maritime Auditor & ISO (International Organization for Standardization) standards (ISO 9001, ISO 14001, ISO 45001)
By International Maritime Training
Welcome to the combined course on : I. ISM (International Safety Management), /ISPS (International Ship and Port Facility Security), /MLC (Maritime Labour Convention)., II. ISO (International Organization for Standardization) standards (ISO 9001, ISO 14001, ISO 45001), This course aims to provide you with a comprehensive understanding of various maritime industry standards and regulations that play a crucial role in ensuring safety, security, environmental protection, and quality management in the maritime sector. I. ISM,ISPS,MLC Maritime Auditor The International Safety Management (ISM) Code sets guidelines for the safe operation of ships and pollution prevention. It establishes a framework for ship management and requires companies to develop and implement a Safety Management System (SMS) to ensure the safety of ships and personnel. The International Ship and Port Facility Security (ISPS) Code is a set of measures designed to enhance the security of ships and port facilities. It aims to detect security threats and take preventive measures to protect ships, ports, and the maritime supply chain from acts of terrorism, piracy, and other criminal activities. The Maritime Labour Convention (MLC) is an international labor standardthat sets out seafarers' rights and working conditions. It covers a wide rangeof issues, including employment contracts, working hours, accommodation, healthand safety, and welfare, ensuring that seafarers are treated fairly and provided with adequate working and living conditions. II. ISO (International Organization for Standardization) standards (ISO 9001, ISO 14001, ISO 45001) ISO standards, including ISO 9001 (Quality Management System), ISO 14001 (Environmental Management System), and ISO 45001 (Occupational Health and Safety Management System), provide internationally recognized frameworks for organizations to manage their quality, environmental, and occupational health and safety responsibilities. These standards help companies establish efficient processes, minimize risks, and improve their overall performance. Throughout this course, you will delve into each topic, exploring their principles, requirements, and best practices. By the end of this combined course, you will have gained valuable insights into the key aspects of maritime safety, security, labor standards, quality management, and the role of the Designated Person Ashore
Problem Solving
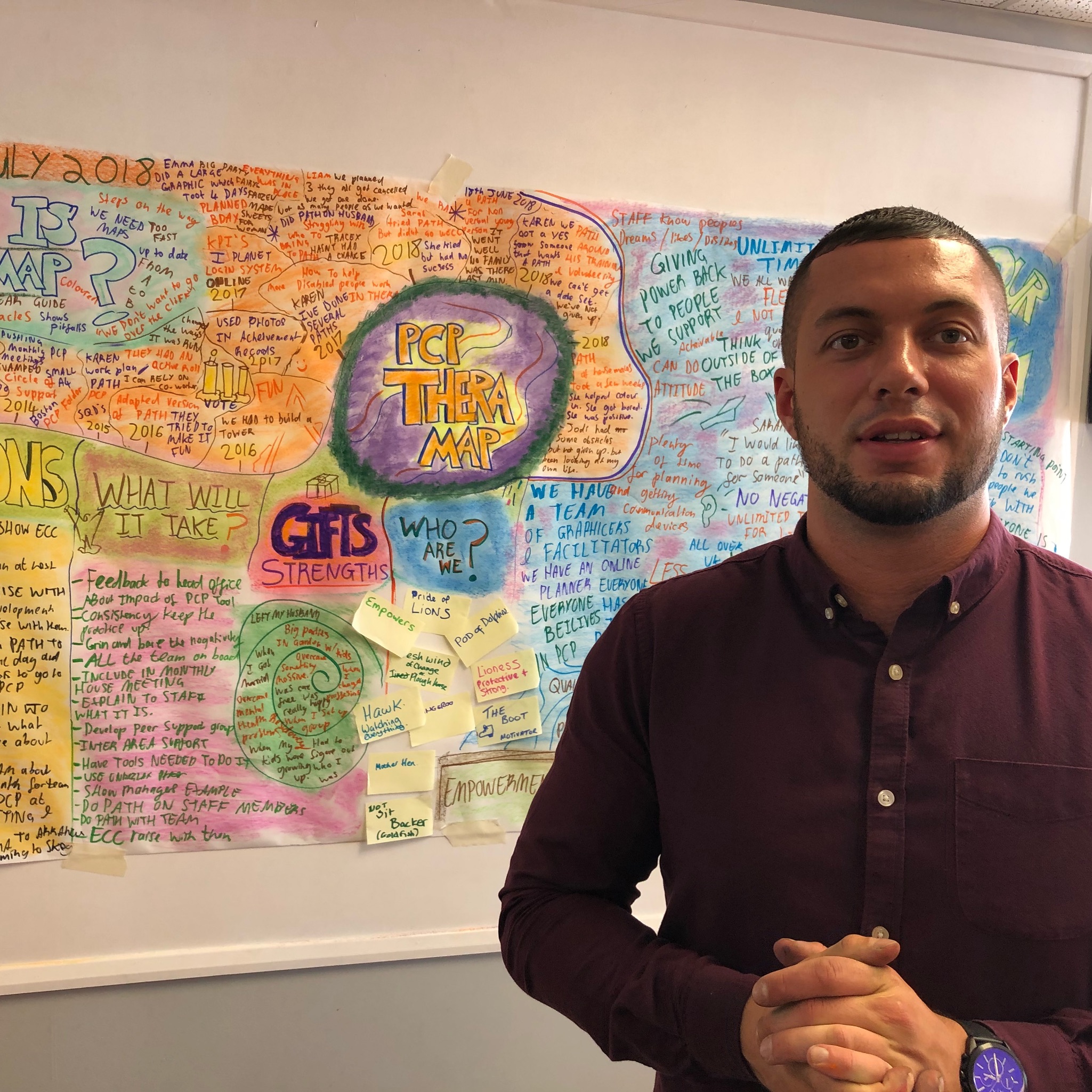
By Inclusive Solutions
We will your support your facilitation skills when learning Circle of Adults, Solution Circles and Insights and Solution Circles
Want to make a positive difference in the lives of the people? Try out teaching and guide countless individuals to achieve their individual successes! Bring the best out of them and become the hero they've all been waiting for! We've designed our Focus Awards Level 3 Award in Supporting Teaching and Learning in Schools qualification in a way that covers your unique specifications and needs. Our general teaching assistant qualification (RQF) is further improved with the addition of a distinctive SEN course so you can cater to individuals with special needs that may require more care and observation than others. This Focus Awards Level 3 Award in Supporting Teaching and Learning in Schools qualification is offered and awarded by an Ofqual-regulated Awarding Organisation called Focus Awards, ensuring that you are capable of demonstrating vital competency and then given acknowledgement from it. You will gain the necessary skills to allow yourself to make a start with a promising teaching career. More so, you will get the chance to claim a certificate for SEN by completing the free SEN course that comes with this qualification. Enrol now to seize rich opportunities to make a difference in many lives by achieving our nationally accredited certification! Qualification Summary Qualification Type: Focus Awards Level 3 Award Qualification Title: Focus Awards Level 3 Award in Supporting Teaching and Learning in Schools Level: 3 Guided Learning Hours: 80 Total Qualification Time (TQT): 120 Qualification Number (QN): 601/6103/6 Why This Qualification? Make promising advancements in your career - Our regulated qualification holds immense value, allowing you to climb up the ladder to success in no time. Upgrade your skillset - Gain the skills to become the best in your role and add more value to your current educational profile. Enhance credibility - Regulated by Ofqual and awarded by Focus Awards, value is added to your educational profile. Make changes to your career - Gain unique knowledge to transform your career. Cost-Efficient - With Apex Learning, you can enjoy savings of up to 80% on your educational investment. ****Qualification Curriculum**** **Focus Awards Level 3 Award in Supporting Teaching and Learning in Schools ** To be awarded this qualification, a learner must achieve 12 credits from the following 4 mandatory units. Communication and professional relationships with children, young people and adults Schools as Organisations Understand Child and Young Person Development Understand how to safeguard the well-being of children and young people ***FREE Courses*** Course 01: Education Management Course 02: Educational Psychology and Development Course 03: Advanced Teaching Assistant Diploma Course 04: Special Education Needs (SEN) Training - Level 2 Course 05: EYFS Teaching - Level 3 Course 06: Phonics Teaching Diploma Level 3 Course 07: Leadership in Teaching Course 08: Lesson Planning for Teaching Course 09: Remote Teaching Online Course 10: Classroom Behaviour Management Course 11: Performance Management Course 12: Work Area Organisation for Increased Office Productivity Course 13: Report Writing Course 14: Domestic Violence and Abuse Awareness - Level 2 Course 15: Child Neglect Awareness Certificate Course Course 16: Level 3 Mental Health and Adolescent Course Course 17: Safeguarding Children Level 3 Course 18: Functional Skills English Practice Level 2 Course 19: Train the Trainer Course 20: Leadership & Management Diploma Course Duration Focus Awards Level 3 Award in Supporting Teaching and Learning in Schools Total Qualification Time It is an estimate of the total amount of time anticipated that a learner would spend to demonstrate mastery of all learning outcomes to achieve the award of the qualification. The whole qualification time is defined as GLH and an estimate of the time a learner will devote to preparation, study, and assessment. It does not underlie supervision by a lecturer, supervisor, or tutor. In the case of qualification, the credit value is defined by TQT, and one credit corresponds to ten hours of learning. Guided Learning Hours for this qualification is 80. Total Qualification Time (TQT) is 120 hours. The total credit value for this qualification is 12. Focus Awards Level 3 Award in Supporting Teaching and Learning in Schools Guided Learning Hours These hours comprise all real-time contact time, hours of lectures or tutorials or supervision of a learner, tutor, trainer or other education providers. Method of Assessment Assessment is done internally and externally assured by Focus Awards. Each learner will create a portfolio of evidence demonstrating achievement of all the learning outcomes and the assessment criteria associated with each unit. The main pieces of evidence for the portfolio could include: Assessor observation - completed observational checklists on related action plans Witness testimony Learner product Worksheets Assignments / projects / reports Record of oral and written questioning Learner and peer reports Recognition of prior learning (RPL) Evidence may be drawn from actual or simulated situations where appropriate and permitted by the relevant Sector Skills Council or Sector Skills Body. Certification Successful candidates will be awarded a Level 3 Award in Teaching Assistant from Focus Awards You will also get a CPD Accredited SEN Certificate alongside this qualification. Progression Level 3 Certificate in Supporting Teaching and Learning in Schools Level 3 Certificate in Cover Supervision of Pupils in Schools Level 3 Diploma in Specialist Support for Teaching and Learning in Schools Intermediate/Advanced Level Apprenticeship in Supporting Teaching and Learning in Schools Who is this course for? Level 3 Teaching Assistant Qualification (RQF) Requirements There are no specific entry requirements for this qualification. Focus Awards does not set any other entry requirements, but training providers or colleges may have their own guidelines. Career path After receiving the Focus Awards Level 3 Award in Supporting Teaching and Learning in Schools certification, you would be eligible to function as a competent professional as: Senior Teaching Assistant Senior Learning Support Assistant Senior Special Educational Needs Assistant

Search By Location
- Other Courses in London
- Other Courses in Birmingham
- Other Courses in Glasgow
- Other Courses in Liverpool
- Other Courses in Bristol
- Other Courses in Manchester
- Other Courses in Sheffield
- Other Courses in Leeds
- Other Courses in Edinburgh
- Other Courses in Leicester
- Other Courses in Coventry
- Other Courses in Bradford
- Other Courses in Cardiff
- Other Courses in Belfast
- Other Courses in Nottingham