- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Total H.248 training course description A course focusing purely on the H.248 protocol. Anyone working through the ITU standards documents can testify to the need of a training course to explain how H.248 really works. This course already assumes knowledge of other VoIP protocols and starts by positioning H.248 in relation to the other protocols. The course then looks at H.248 architectures and concepts before analysing H.248 messages and call flows. What will you learn Describe what H.248 is Recognise where H.248 fits in relation to other VoIP protocols. Explain how H.248 works. Analyse H.248 packets Total H.248 training course details Who will benefit: Technical staff working with H.248 Prerequisites: Voice Over IP. Duration 2 days Total H.248 training course contents What is H.248? Review of VoIP protocols: RTP, RTCP, SIP, SDP, H.323. The PSTN and SS7. Where H.248 fits into the picture. H.248 history. MGCP. The IETF. Megaco. ITU standards. H.248v1, v2, v3. H.248 architectures Media Gateways, Media Gateway Controllers, Gateway Control functions, Signalling Gateways. Reference architectures: IMS/TISPAN: IBCF, IWF, I-BGF, SPDF. MSF: S-SBG-NC, D-SBG-NC. GSMA: IPX Proxy. Softswitches. H.248 concepts The connection model, terminations, streams, contexts. Termination properties: descriptors, context properties. Events, signals, packages. H.248 messages Protocol stack, UDP, TCP. Message structure. Transactions, actions, commands. Requests, replies, acknowledgements. Sample message flows. Binary encoding, ASN syntax, Text encoding. H.248 commands Termination manipulation: Add, Subtract, Move, Modify. Event reporting: Notify. Management: AuditCapability, AuditValue, ServiceChange. H.248 Descriptors What are descriptors? Relationship with messages and commands. Basic descriptors, Descriptors composed of other descriptors. The 19 descriptors. Defaults. H.248 Transactions Groups of commands, transaction Ids, relationship with actions and commands. Requests and replies. H.248 wrap up What is a package? Basic packages. H.248 security. H.248 - SIP interoperation. H.248 interoperation with other protocols.

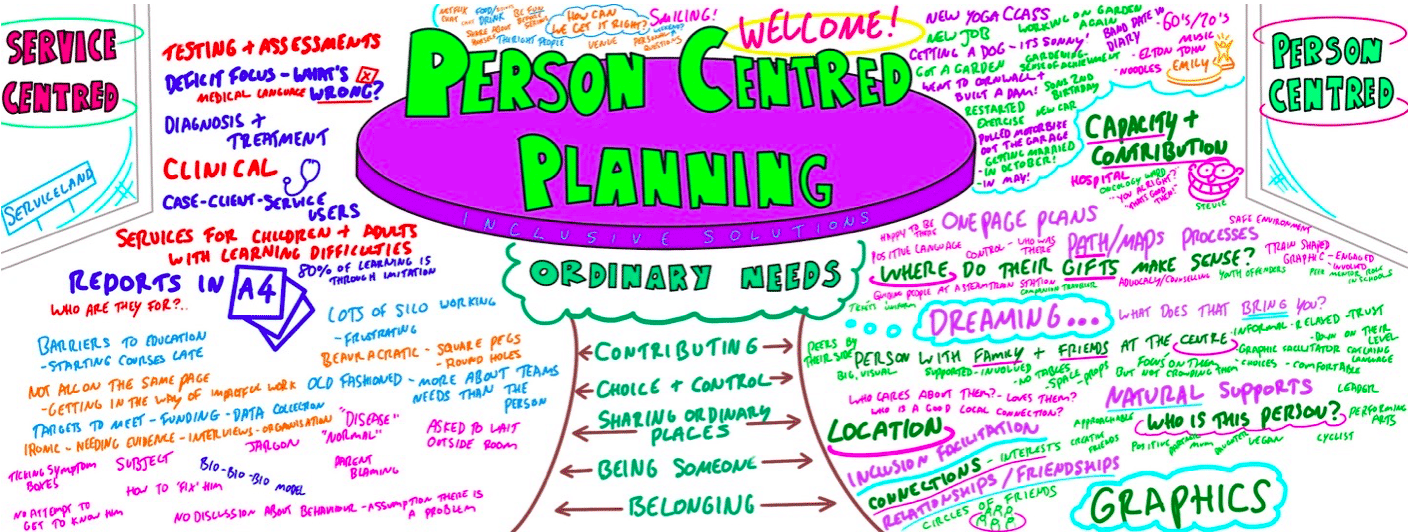
Person Centred Planning using PATH and MAPs
By Inclusive Solutions
What is Person Centred Planning? How is it different to any other kind of meeting or planning? On this day all will become clear… Give your team the opportunity to pause and reflect on what matters most to them about the work they do. The act of listening to each other creates relationship and strengthens trust and inclusion within the team – in creating a shared vision, groups of people build a sense of commitment together. They develop images of ‘the future we want to create together’, along with the values that will be important in getting there and the goals they want to see achieved along the way. Unfortunately, many people still think ’vision’ is the top leader’s job. In schools, the ‘vision task’ usually falls to the Headteacher and/or the governors or it comes in a glossy document from the local authority or the DfES. But visions based on authority are not sustainable. Making inclusive action plans using full participation and graphic facilitation Drawing on the planning tools MAPS and PATH (Pearpoint, Forest and O’Brien 1997) and other facilitation sources we use both process and graphic facilitation to enable the group to build their picture of what they would love to see happening within their organisation/community in the future and we encourage this to be a positive naming, not just a list of the things they want to avoid. Jack Pearpoint, Marsha Forest and John O’Brien developed these innovative approaches in North America and they are being used successfully in many parts of the UK. The planning can focus on an individual, group or organisation and provides a powerful problem solving opportunity, which is flexible and robust enough for many occasions. Tell the story, find the dream, touch the nightmare, and explore who you are, what are the gifts and strengths of the person or group, what are the needs of those present and what is the action plan for the future? Learning objectives Participants understand Person Centred Planning and its values and applications Participants have skills and confidence to facilitate PATH/MAP processes Participants learn graphic as well as process facilitation skills Strengthens practitioners inclusive practice Provides additional tools for those involved in inclusive work in schools and the community Further develop problem solving and planning skills Course Content The course answers the questions: Need to find new ways to bring Pathway Planning alive? Bored with annual reviews, transition plans and review meetings? Want to find a way of making meetings and planning feel more real and engaging? Need an approach, which engages a young person respectfully together with his or her family and friends? Want the ultimate visual record of the process of a meeting, which will help everyone, keep track? Want to problem solve and plan for the future of a small or large group, service or organisation up to the size of an LA? Inclusive Solutions offer an introductory day to person centred planning or a 3 – 10 session course which is practical as well as values based. Participants will receive direct individualised coaching and training. We will cover: The person being at the centre Family members and friends being full partners Planning reflecting the person’s capacities, what is important to the person and specifying the support they require to make a full contribution to their community Planning building a shared commitment to action that will uphold the person’s rights Planning leading to continual listening, learning and action and helping the person get what they want out of life. Essential Lifestyle Planning, PATH MAPS Personal Futures Planning.
Python training course description This Python course focusses on teaching Python for use in network automation and network DevOps. We focus on getting delegates up and running with Python and network automation as quickly as possible rather than making them great programmers. In other words we concentrate on enabling delegates to use network automation libraries such as netmiko, NAPALM and Nornir, and APIs such as NETCONF and RESTCONF rather than enabling delegates to produce object oriented programs. Hands on sessions use Cisco and Juniper devices. What will you learn Run Python programs. Read Python programs. Write Python programs. Debug Python programs. Automate network tasks with Python programs. Configure network devices with Python. Collect data from network devices with Python. Python training course details Who will benefit: Network engineers. Prerequisites: TCP/IP Foundation Duration 5 days Python training course contents What is Python? Programming languages, Why Python? Python in interactive mode, Python scripts, ipython, Python version 2 versus version 3. A simple Python script. Comments. Hands on Installing Python, Hello world. A network example On box vs off box Python. telnet, ssh, NETCONF, HTTP, APIs, manufacturers and API support, analysis of a simple telnetlib program. Hands on Using Python to retrieve the configuration from a network device. Using wireshark to analyse the actions. Python basics I/O, operators, variables and assignment, types, indentation, loops and conditionals. Hands on Modifying the telnet program, changing configurations on a network devices. Functions, classes and methods What are functions, calling functions, builtin functions, useful builtin functions, file handling, classes, objects, creating instances. Hands on Storing configurations in files, configuring devices from files, using an inventory file to work on multiple devices. Libraries and modules Modules, files and packages, import, from-import, Python standard library, other packages, pip install, executing other programs. Managing python libraries. Hands on Using pip, installing and using ipaddress, subprocess to access netsnmp. For the more advanced, using the sockets library. Paramiko and netmiko SSH, enabling SSH on devices, keys. Paramiko versus netmiko, example scripts. pexpect. Hands on Configuring VLANs from Python. pySNMP Gathering facts using previous methods, SNMP review, pySNMP GET, pySNMP and SNMPv3. easySNMP library. Hands on Walking a MIB from Python. NETCONF What is NETCONF? Enabling NETCONF on devices, A first ncclient script, device handlers, get_config, edit_config, copy_config, delete_config, commit, validate, pyEZ, utils_config, utils.sw. Hands on Configuration using ncclient and PyEZ. This session is expanded for those interesting in JunOS automation. Manipulating configuration files Builtin functions, string handling. Unicode. Sequences, strings, lists, tuples. Dictionaries. TextFSM. Regular expressions. JSON, YAML, XML, YANG, Jinja2, templates. Hands on Jinja2 templating with Python to configure network devices. NAPALM Getters, configuration operations, supported devices, NAPALM transport, Config-replace, Config-merge, Compare config, Atomic changes, rollback. Example NAPLAM scripts. Hands on Using NAPALM to gather facts, Using NAPALM for configuration management REST and RESTCONF What is REST, HTTP methods, GET, POST, cURL, Postman, Python requests library. RESTCONF, a RESTCONF example. Hands on Modifying a configuration using RESTCONF. Scapy What is scapy, Scapy in interactive mode, Scapy as a module. Hands on Packet crafting from Python. Warning Errors and exceptions, Exception handling, try, except. Memory management. Garbage collection. Context management, With. Hands on Improving Python code. Nornir What is Nornir? A network automation framework, inventories, connection management and parallelization. Nornir architecture and other libraires. Hands on Setting up nornir, nornir fact gathering, nornir tasks. Optional Writing your own functions, Writing your own classes. pyntc. Hands on Writing reusable code.

BUILDING RESILIENCE IN STAFF TEAMS
By Inclusive Solutions
New Covid 19 inspired course to deepen participants understanding of stress, trauma and anxiety. We will work with them to strengthen them and build resilience. This work is particularly relevant to school and other teams returning to school post Covid-19 lock down experiences or similar. The training can be delivered virtually on Teams or Zoom or face to face safely. Course Category Team Building Leadership Emotional needs Description In this course we deepen participants understanding of stress, trauma and anxiety and will work with them to strengthen them and build resilience. This work is particularly relevant to school and other teams returning to school post Covid-19 lock down experiences or similar. The training can be delivered virtually on Teams or Zoom or face to face safely. Learning Objectives Participants will: Deepen their understanding of stress, trauma and anxiety Develop creative resources for self-care Experience a reflective space in which they feel heard and validated Share narratives and strategies and develop solidarity Create a shared vision for achieving resilience within teams Who Is It For? Any team that is returning to workplace following Covid-19 lockdown or other traumatic events Any team that wants to build strength and resilience Course Content Overview of session, goals and ground rules Confidential listening: story so far… experiences shared – opportunity for mutual support. All shared in strictest confidence unless serious or dangerous. What we know about staying strong and resilient – taught input with short activities covering: Understanding anxiety and stress and how to manage/process both – what’s there already/what’s needed – building a resilience toolkit. What to do about eating, sleeping and worrying? The nature of change and chaos Building trust in each other – with activity The impact of trauma Empowering cooperative teamwork Importance of nurture and inclusion The long view – the power of individual people in our lives who really care and the impact we each make on young people Share collective ideas and resources for building strength Shared vision for a strong, resilient staff – teams that are abiding, constant, durable, established, fast, firm, lasting, firm but flexible, reliable, secure, sound, steadfast, strong, sturdy, sure and well-founded.

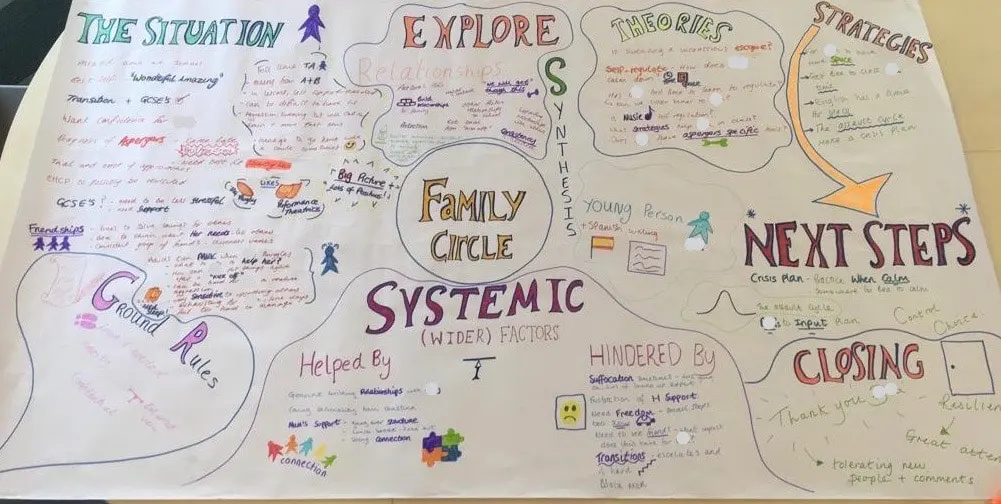
FAMILY CIRCLES
By Inclusive Solutions
Click to read more about this training, in which we demonstrate a live problem solving approach which is based on the active participation of family members. Course Category Inclusion Parents and Carers Behaviour and relationships Problem Solving Description In this training we demonstrate a live problem solving approach which is based on the active participation of family members. ‘Family Circles’ is an evolving new approach to problem solving with families and is based on our years of family work and the development and use of the Circle of Adults process. Inspired by our own Parent Solutions work and the Circle of Adults process as well as Family Group Conferencing and other Restorative Interventions we bring you Family Circles. Essentially the approach involves gathering a family together for a process that is facilitated but majors on the family members offering each other their wisdom and ideas. The approach is capacity focused, person centred approach to working with families rather than the dominant deficit oriented and ‘medical model’ of viewing and planning for or doing things to families. This training can be modelled with a group of professionals or better still with a family. In our work with families we develop the importance of naming stories or theories and seeking linkages and synthesis between what is found out and explored about the family situation and its history. We like participants to sit with the uncertainty, to reflect on the question ‘why’ but without judgement of each other. Deeper reflections may span a whole range of perspectives from ‘within person’ considerations, to situational or systemic possibilities. Health or emotional issues can be reflected on alongside organisational or transactional aspects of what is going on for the family. The better the shared understanding the better the strategy or actions which emerge from these meetings. Quality hypotheses with a close fit to reality lead to more effective implementation in the real world. We encourage ‘loose’ thinking, a search for connections, deeper listening, an ‘open mind’, speculation and exploration without moral judgements. From this stance self-reflection as well as reflection on the situation can produce remarkable insights. The quality of theories or new stories generated is directly influenced by family members’ experiences and the models of learning, behaviour and emotion, systems, educational development, change and so on that they have been exposed to. Learning Objectives To provide opportunities for: Shared problem solving in a safe exploratory climate in which the family will find its own solutions. Individuals to reflect on their own actions and strategies An exploration of whole-family processes and their impact Emotional support and shared understandings of issues at a child, parent, family, school and community level. Feed back to each other on issues, ideas and strategies that are agreed to be worth sharing with them. Who Is It For? Anyone interested in working with families in a way that builds and makes use of their capacities rather than focus on their challenges and difficulties. Social Care teams School staff Community organisers Educational Psychologists Course Content True family empowerment Deepening shared stories and understandings Facilitating groups Problem solving process Handling family group communication Allowing direct feedback and challenge between participants in a safe way Building relationships Process: Family members are welcomed: Introductions are carried out, ground rules and aims clarified whilst coffee is drunk. A recap from the last session is carried out: To follow up developments and reflections after the last meeting. One issue is selected for the main focus Issue presentation: The family member who raised the concern is asked questions to tell the ‘story’ of the issue or problem. Additional questions/information from the group about the problem are gathered: Ground rules may need to be observed carefully here. Individual participants need to be kept focused and prevented from leaping to premature conclusions or to making ‘helpful’ suggestions about strategy. Relationship aspects to the problem are explored. Metaphors and analogies are invited. How would a fly on the wall see your relationship? If you were alone together on a desert island, what would it be like? Impact of previous relationships/spillage from one relationship to another are explored. Eg what situation they are reminded of? For instance, does this situation remind you of any of those angry but helpless feelings you had with your other son when he was an adolescent? This provides opportunities to reflect on how emotions rub off on other people. The parent feels really frustrated, and on reflection we can see that so does the child System/Organisation factors (Family system/school and community systems and so on): What aspects help or hinder the problem? For instance, does the pastoral system of the local school provide space, or time and skilled personnel able to counsel this young person and work actively with their parents? Synthesis. At this stage the Graphic facilitator summarises what they have heard. They then go on to describe linkages and patterns in what they have heard. This can be very powerful. The person doing the graphic work has been able to listen throughout the presentation process and will have been struck by strong messages, emotions and images as they have arisen. The story and meaning of what is happening in the situation may become a little clearer at this point. Typical links may be ‘mirrored emotions’ strong themes such as loss and separation issues, or repeated processes such as actions triggering rejection. This step provides an excellent grounding for the next process of deepening understanding. What alternative strategies/interventions are open to be used? Brainstormed and recorded. ’Either/ors’ need to be avoided at this time also. This needs to be a shared session in which the family member who is presenting the concern contributes as much as anyone. Care is needed to ensure that this person is not overloaded with other people’s strategies. The final selection of strategy or strategies from the brainstormed list is the problem presenter’s choice. Strategies might include: a special time for the young person, a meeting with the child’s parents to explore how she is being managed at home and to share tactics, a home-school diary, counselling, or an agreed action plan that all are aware of, agreed sanctions and rewards and so forth. Strategies may productively involve processes of restitution and restoration, when ‘sorry’ is not enough. Making it right, rather than punishments or rewards, may then becomes the focus. First Steps. The problem presenter is finally asked to agree one or two first steps which they can carry out over the next 3-7 days. It can help to assign a ‘coach’ who will check in with them to ensure they have carried out the action they have named. This is a time to be very specific. Steps should be small and achievable. The person is just ‘making a start’. A phone call, or making an agreement with a key other person not present at the meeting would be ideal examples. Final reflections. Sometimes referred to as a ‘round of words’ help with closure for all involved. Reflections are on the process not the problem. In large families this is best done standing in a circle. In smaller groups all can remain sitting. Passing around a ‘listening stick’ or something similar such as a stone or light heighten the significance of the process ending and improve listening. Finally the problem presenter is handed the ‘Graphic’ this is their record of the meeting and can be rolled and presented ceremoniously by the facilitators for maximum effect! If you liked this course you may well like: Parent Solutions
Definitive Nagios training course description Nagios is an open source application designed to provide system and network monitoring. This hands on course gives a comprehensive coverage of using Nagios to provide monitoring of Linux, Windows and network devices. The course is based on Nagios core but contact us if you would like Nagios XI. What will you learn Install Nagios. Configure Nagios. Monitor Windows, Linux and Cisco (and other network equipment) using Nagios. Configure notifications Definitive Nagios training course details Who will benefit: Technical staff working with Nagios. Prerequisites: None. Duration 2 days Definitive Nagios for engineers Nagios architecture Downloading Nagios, Installing Nagios, Nagios core, plugins, frontends, addons. Nagios XI. Nagios Fusion. Hands on Installing Nagios. Getting started with Nagios Nagios files, nagios.cfg, minimal.cfg. Starting and stopping Nagios. Hands on Controlling Nagios. Using Nagios Nagios web interface. Maps, Hosts, host groups, services, service groups, problems. Reports. Configuration. Hands on Using the web interface. Monitoring Linux systems SSH, NRPE. Hands on Monitoring Linux system health. Monitoring Windows systems Installing NSClient++, Configuring NSClient++, check_nt plugin, monitoring uptime, CPU, memory, disks, services, processes. Hands on Monitoring Windows system health. Monitoring network devices SNMP architecture, MIBs. Polling. Hands on Configuring Nagios for SNMP. Agents Configuring Cisco devices for SNMP support, communities, traps, syslog. Hands on Monitoring network devices. Nagios alerts and notifications SNMP traps. Email notifications, SMS alerts other messaging

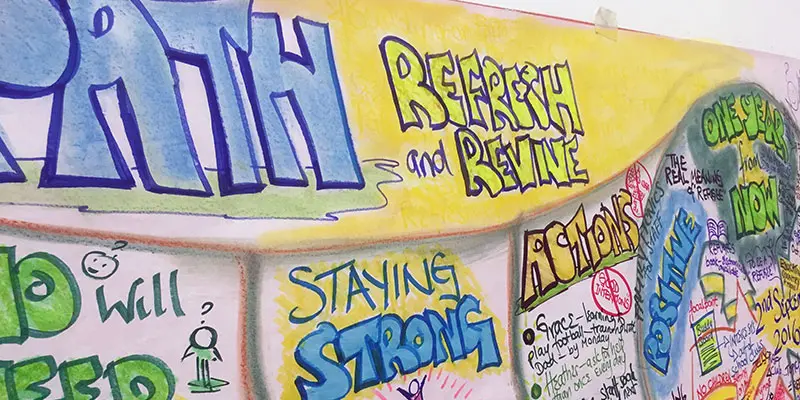
School Improvement Planning
By Inclusive Solutions
Give your team the opportunity to pause and reflect on what matters most to them about the work they do. The act of listening to each other creates relationship and strengthens trust and inclusion within the team – in creating a shared vision, groups of people build a sense of commitment together. Using the PATH or MAP processes of group facilitation and the creating of a large wall sized graphic we will provide a School Improvement Plan to be proud of! Course Category Visioning and Problem Solving Person Centred Planning Strategic Work Team Building and Leadership Description There is an old Japanese proverb, “Vision without action is a daydream. Action without vision is a nightmare” “There is no power for change greater than a community discovering what it cares about” MARGARET WHEATLEY – ‘TURNING TO ONE ANOTHER’ (2002) Give your team the opportunity to pause and reflect on what matters most to them about the work they do. The act of listening to each other creates relationship and strengthens trust and inclusion within the team – in creating a shared vision, groups of people build a sense of commitment together. They develop images of ‘the future we want to create together’, along with the values that will be important in getting there and the goals they want to see achieved along the way. Unfortunately, many people still think ’vision’ is the top leader’s job. In schools, the ‘vision task’ usually falls to the Headteacher and/or the governors or it comes in a glossy document from the local authority or the DfES. But visions based on authority are not sustainable. Drawing on the planning tools MAPS and PATH (Pearpoint, Forest and O’Brien 1997) and other facilitation sources we use both process and graphic facilitation to enable the group to build their picture of what they would love to see happening within their organisation/community in the future and we encourage this to be a positive naming, not just a list of the things they want to avoid. ??Let us join you to explore your vision and the ‘roadblocks’ to your vision. Testimonials “Thank you so much for the work you did with us yesterday – I have since been in 2 schools today and have spoken to an number of other colleagues who were present – all were totally overwhelmed by the session – they loved it.” “I was totally blown away, so nice to reflect and realise what a long way we have come” “That was so powerful and motivational” “Our Primary is now an OFSTED rated ‘Outstanding School’ – we were in Special Measures – the Visioning and Planning using the PATH process for 3 years has seriously contributed to this”. Learning Objectives To create a far reaching and shared vision of the future for the school team/group you are working with and ensure that each person present contributes to this To create a visual representation (a graphic) of the vision and use this to plan future actions and to inform school improvement and development plans To facilitate the group in thinking through what some of the barriers to achieving their vision are and to begin work on how these can be removed To build a sense of commitment, common purpose and trust within the team/group Who Is It For ? Headteachers School managers EIP Managers Whole staff – including everyone Course Content The facilitation of a shared vision can be delivered as a full or a half day but, unlike our other training days this day depends on your and your team’s needs and the time you have available The course will cover: Creating the vision The Story So Far Headline Themes Naming the Nightmare A Year from Now Naming Roadblocks and Barriers Building strength Who will we need to take with us on the journey towards the vision Who are we? – Gifts, Strengths and Talents Charting Specific Actions
Network forensics training course description This course studies network forensics-monitoring and analysis of network traffic for information gathering, intrusion detection and legal evidence. We focus on the technical aspects of network forensics rather than other skills such as incident response procedures etc.. Hands on sessions follow all the major sections. What will you learn Recognise network forensic data sources. Perform network forensics using: Wireshark NetFlow Log analysis Describe issues such as encryption. Network forensics training course details Who will benefit: Technical network and/or security staff. Prerequisites: TCP/IP foundation for engineers. Duration 3 days Network forensics training course contents What is network forensics? What it is, host vs network forensics, purposes, legal implications, network devices, network data sources, investigation tools. Hands on whois, DNS queries. Host side network forensics Services, connections tools. Hands on Windows services, Linux daemons, netstat, ifoconfig/ipconfig, ps and Process explorer, ntop, arp, resource monitor. Packet capture and analysis Network forensics with Wireshark, Taps, NetworkMiner. Hands on Performing Network Traffic Analysis using NetworkMiner and Wireshark. Attacks DOS attacks, SYN floods, vulnerability exploits, ARP and DNS poisoning, application attacks, DNS ANY requests, buffer overflow attacks, SQL injection attack, attack evasion with fragmentation. Hands on Detecting scans, using nmap, identifying attack tools. Calculating location Timezones, whois, traceroute, geolocation. Wifi positioning. Hands on Wireshark with GeoIP lookup. Data collection NetFlow, sflow, logging, splunk, splunk patterns, GRR. HTTP proxies. Hands on NetFlow configuration, NetFlow analysis. The role of IDS, firewalls and logs Host based vs network based, IDS detection styles, IDS architectures, alerting. Snort. syslog-ng. Microsoft log parser. Hands on syslog, Windows Event viewer. Correlation Time synchronisation, capture times, log aggregation and management, timelines. Hands on Wireshark conversations. Other considerations Tunnelling, encryption, cloud computing, TOR. Hands on TLS handshake in Wireshark.

Search By Location
- Other Courses in London
- Other Courses in Birmingham
- Other Courses in Glasgow
- Other Courses in Liverpool
- Other Courses in Bristol
- Other Courses in Manchester
- Other Courses in Sheffield
- Other Courses in Leeds
- Other Courses in Edinburgh
- Other Courses in Leicester
- Other Courses in Coventry
- Other Courses in Bradford
- Other Courses in Cardiff
- Other Courses in Belfast
- Other Courses in Nottingham
