- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Influencing with Behavioural Styles
By Ei4Change
How to inspire others and build successful relationships. This course is designed to support professionals in business to develop communication skills through understanding and applying knowledge of personality and behaviour in the workplace. It is based upon the book "The Authority Guide to Behaviour in Business: How to Inspire Others and Build Successful Relationships" by Robin Hills (ISBN: 1912300087).
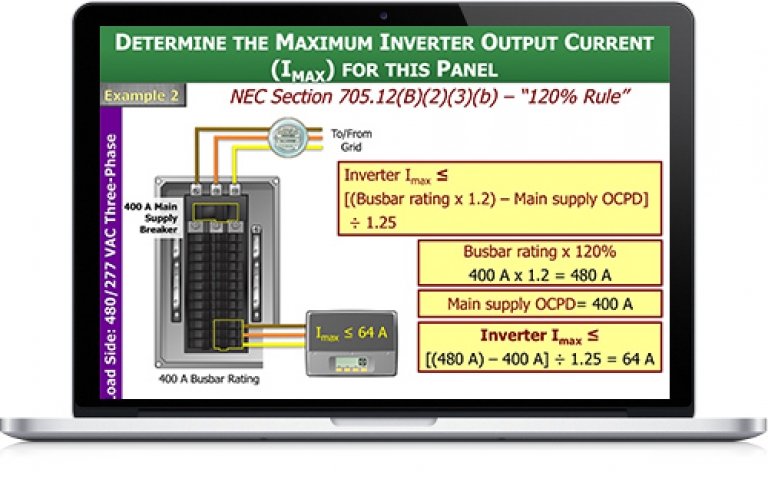
PVOL202: Solar Training - Advanced PV System Design and the NEC (Grid-Direct) - Online
By Solar Energy International (SEI)
Students who complete PVOL202 will be able to: Define the purpose of the National Electrical Code (NEC®) and NEC® terminology for PV equipment Determine procedures for proper installation of equipment and conductors, including minimum requirements for working space Examine methods for PV wire management and determine where expansion fittings are required Describe and identify electrical services, including split-phase and three-phase Wye (Y) and Delta (â) Evaluate electrical service details to collect and record during solar site evaluation Identify options for NEC®-compliant PV system interconnection to the utility grid and determine whether a supply side, load side, or additional service connection is appropriate Identify code-compliant methods for connecting an inverter to an existing AC feeder Calculate PV module voltage based on temperature to ensure compatibility with system components and NEC® Section 690.7, and explore other options for maximum PV system DC voltage calculations Identify NEC® requirements and sizing of disconnects and overcurrent protection devices (OCPDs) in grid-direct PV systems Define inverter grounding configurations Evaluate inverter choices and system configurations, including string inverters, central inverters, and module level power electronics (MLPE) Identify requirements for equipment grounding, equipment grounding conductors (EGC), and grounding electrode conductors (GEC), and size the conductors according to the NEC® Identify common causes of ground-faults and arc-faults Describe ground-fault and arc-fault protection devices Describe benefits and appropriate locations of surge protection devices (SPD) Demonstrate the use of sun charts and perform calculations to determine row spacing and minimize inter-row shading Identify how Codes detailing access for first responders impact PV array roof layout Examine fire classifications that affect racking and module selection Detail NEC rapid shutdown requirements and options for implementation Identify load and structural considerations for low- and steep-slope roof-mounted PV systems Calculate wind uplift force and select appropriate lag bolts Review issues related to planning, design, and installation of ground-mount PV arrays Review PV system circuit terminology, definitions, and conductor types Calculate minimum overcurrent protection device (OCPD) size and conductor ampacity using appropriate adjustment and correction factors Calculate voltage drop and verify system operation within acceptable limits Examine requirements for PV system labeling Calculate the maximum and minimum number of modules per PV source circuit, and number of PV source circuits per inverter Determine size of residential grid-direct PV system based on site and customer-specific considerations including the number and wiring layout of modules, conductor and OCPD sizes, and the AC interconnections Determine the size of a large, multiple inverter, grid-direct PV system based on site and customer-specific considerations, including the quantity and layout of modules and inverters and the AC interconnection Define large-scale PV and review associated NEC® allowances and requirements Describe importance of Data Acquisition Systems (DAS) Identify common DAS equipment and hardware Review DAS design, installation, and commissioning processes and common problems associated with DAS Show how reports can be generated and utilized to remotely assess health of system
This is a fabulous gift to a friend or for a friendship! Invite a trusted companion to a SoulCollage session and let me join you in your creative space via Zoom. You will come to know each other and yourselves in a whole new way and have a new activity to share. apply to request a date and we can organise the details. From £105 for two hours including a pack of images to a UK address (and by quotation for shipping elsewhere).

Description CDD is an ongoing process and, as such, a critical element for effectively managing the risks posed by existing clients, thus protecting the organization against their possible dubious actions. This course outlines basic CDD procedures requires to assess customer risk and a legal requirement to comply with Anti-Money Laundering (AML) and Counter-Terrorist Financing (CFT) laws. Effective CDD involves ongoing monitoring of customers' business activities, identifying and mitigating the AML/CFT risk a business relationship may pose to a regulated entity. Training Duration This course may take up to two (2) hours to complete. Keep in mind, however, that actual study time varies based on each learner's training pace. Who Should Enrol? This course is addressed to all individuals who practice AML such as compliance and/or AML managers in banks, investment firms, investment funds, ASPs, trust service corporate providers, and lawyers. Training Method The course is offered online using a self-paced approach. The learning units consist of video presentations and reading material. Learners may start, stop, and resume their training at any time. At the end of the training, participants take a quiz to complete their learning and earn a Certificate of Completion. Accreditation and CPD Recognition The syllabus is verified by external subject matter experts and can be accredited by regulators and other bodies for two (2) CPD units that approve education in financial regulation. The course may be also approved for CPD units by institutions that approve general financial training such as CISI and ACAMS. Eligibility criteria and CPD units are verified directly by your association, regulator, or other any other body for which you hold membership. Registration and Access To register for this course, click on the button above to pay online and receive instant access. If you are purchasing this course on behalf of others, please be advised that you will need to create or use their personal profile before finalising your payment. Access to the course is valid for 180 days. If you wish to receive an invoice instead of paying online, please email us at info@lgca.uk. Also, please get in touch if you'd like to discuss special corporate group rates.
Introduction to Know Your Client (KYC) and Customer Due Diligence (CDD)
5.0(4)By LGCA | London Governance and Compliance Academy
Description KYC/CDD is a critical element for effectively managing the risks posed by potential clients, thus protecting the organization against criminals, terrorists, and Politically Exposed Persons (PEPs) who might present a higher risk, and possible dubious actions by existing customers that need to be regularly reassessed. This course provides an introduction to KYC and CDD procedures, both key tools in assessing customer risk and a legal requirement to comply with Anti-Money Laundering (AML) and Counter-Terrorist Financing (CFT) laws. Training Duration This course may take up to two (2) hours to complete. Keep in mind, however, that actual study time varies based on each learner's training pace. Who Should Enrol? This course is addressed to all individuals who practice AML such as compliance and/or AML managers in banks, investment firms, investment funds, ASPs, trust service corporate providers, and lawyers. Training Method The course is offered online using a self-paced approach. The learning units consist of video presentations and reading material. Learners may start, stop, and resume their training at any time. At the end of the training, participants take a quiz to complete their learning and earn a Certificate of Completion. Accreditation and CPD Recognition The syllabus is verified by external subject matter experts and can be accredited by regulators and other bodies for two (2) CPD units that approve education in financial regulation. The course may be also approved for CPD units by institutions that approve general financial training such as CISI and ACAMS. Eligibility criteria and CPD units are verified directly by your association, regulator, or other any other body for which you hold membership. Registration and Access To register for this course, click on the button above to pay online and receive instant access. If you are purchasing this course on behalf of others, please be advised that you will need to create or use their personal profile before finalising your payment. Access to the course is valid for 180 days. If you wish to receive an invoice instead of paying online, please email us at info@lgca.uk. Also, please get in touch if you'd like to discuss special corporate group rates.
Get to enter the field of education and training with the most in-demand skill set! The Level 3 Award in Education and Training (RQF) qualification will be your surefire way to achieve more incredible things in your professional life. Level 3 Award in Education and Training (RQF) qualification has all the extensive and all-embracing resources developed by industry experts and education enthusiasts. It will introduce you to various essential teaching topics, allowing you to begin building a successful teaching career. Furthermore, you will gain a globally recognised certificate that will add immense value to your personal and professional growth. The Level 3 Award in Education and Training (RQF) is a level 3 Award in Education and Training AET (previously PTLLS) that has been regulated by the UK government and granted by Focus, the UK's fastest-growing awarding organisation. Focus is a well-known awarding body controlled by Ofqual, ensuring professionalism and respect for the qualifications. Enrol today and grab this once-in-a-lifetime opportunity. Qualification Summary Qualification type: Focus Level 3 Award Qualification title: Focus Level 3 Award in Education and Training (RQF) Accreditation status: Accredited Level: 3 Guided Learning Hours (GLH): 48 Total Qualification Time (TQT): 120 Qualification number (QN): 601/6099/8 ****Qualification Curriculum**** **Level 3 Award in Education and Training (RQF)** Unit 1: Understanding Roles, Responsibilities and Relationships in Education and Training Unit 2: Understanding and Using Inclusive Teaching and Learning Approaches in Education and Training Unit 5: Understanding Assessment in Education and Training Course Duration Total Qualification Time This is an estimate of the total length of time it is expected that a learner will typically take to achieve and demonstrate the level of attainment necessary for the award of the qualification i.e. to achieve all learning outcomes. Total Qualification Time is GLH and an estimate of the number of hours a learner is likely to spend in preparation, study, or any other learning including assessment, which takes place as directed by, but not under the supervision of a lecturer, supervisor, or tutor. The credit value, where given, for qualification, is determined by TQT, as one credit corresponds to 10 hours of learning. Total Qualification Time for this qualification is 120 hours. Guided Learning Hours These hours are made up of all contact time, guidance, or supervision of a learner by a lecturer, supervisor, tutor, trainer, or other appropriate provider of education or training. Guided Learning Hours for this qualification is 48. Assessment Unit 1: Understanding Education and Training Roles, Responsibilities, and Relationships You will be required to submit a written assignment that demonstrates your understanding of legal duties, equality and diversity, individual learning requirements, keeping a safe and helpful learning environment, and your position as a teacher and superior. Unit 2: Using and understanding comprehensive teaching and learning strategies in the classroom You must provide a written assignment that demonstrates your knowledge and comprehension of inclusive teaching and learning, as well as your grasp of your own role's strengths and limitations, how to inspire learners, ground rules, and teaching and learning resources. You'll need to do a 15-minute to one-hour micro-teach (which will be filmed and uploaded to your online learning account) teaching a session of your choosing to a group of at least three people. Unit 5 - Education and Training Assessment You will be required to submit a written assignment demonstrating your awareness of the goal of assessment, different assessment kinds, how to conduct assessments, understanding learner involvement in assessment, reasons for constructive feedback, and good assessment recording keeping. Video Assessment You have to plan many things, such as observation, questioning/ professional discussion, and inspection of supporting work product evidence. Detailed assignment instructions will be made available to you in the 'Guidance for Achieving the Unit' section of your learning portal with a careful and clear explanation. You have to submit all your assignments via the online portal. Certification Successful candidates will be awarded a Level 3 Award in Education and Training (RQF) from Focus Awards Limited. Progression Level 4 Certificate in Education and Training Level 5 Diploma in Education and Training Level 3 Award in Understanding the Principles and Practices of Assessment Level 3 Award in Assessing Competence in the Work Environment Level 3 Award in Assessing Vocational Related Achievement Level 3 Certificate in Assessing Vocational Achievement Level 4 Award in Understanding the Internal Quality Assurance of Assessment Processes and Practice Level 4 Award in the Internal Quality Assurance of Assessment Processes and Practice Level 4 Certificate in Leading the Internal Quality Assurance of Assessment Processes and Practice Level 4 Award in Learning and Development Level 4 Diploma in Learning and Development Who is this course for? Those who have already worked in the teaching profession The aspiring professionals who want to add new skills to their CV Individuals who want to start their career as a teaching assistant Requirements Level 3 Award in Education & Training (RQF) qualification does not have any specific entry requirements for students. However, you must be at least 19 years old or above to register and undergo an initial assessment. Career path Level 3 Award in Education & Training (RQF) You will have the ability to accomplish a lot of things with this certificate. Here are just a few examples: Primary School Teacher Secondary School Teacher Private Tutor Freelance Teacher/ Trainer Consultant Job hunters & School leavers Educational Psychologist Office clerk & Administration Assistant College or University Student

PRINCE2® Foundation and Practitioner
By Underscore Group
Learn the processes, practices and principles of project management described in the PRINCE2® approach and prepare for the Foundation and Practitioner examinations on this accredited programme. Duration: 5 days (32.5 hours) Our PRINCE2® Foundation and Practitioner Qualification course is designed to teach the processes, practices and principles of project management described in the PRINCE2® approach and to prepare delegates for the Foundation and Practitioner examinations, held as part of the course. This course is designed for existing and potential Project and Team Managers who would like to gain a comprehensive understanding of the PRINCE2® method of managing projects and will provide those responsible for planning and managing projects with a structure that will help, without imposing inflexible processes or stifling creative thinking. The PRINCE2® Foundation and Practitioner Course is based on the “Managing Successful Projects with PRINCE2® 7th Edition”, which describes the structured project management method. These are intensive modules and require delegates to undertake some evening work in their own time. Objectives By the end of the course you will be able to be: Describe the background, principles, structure and terminology used in the PRINCE2® 7th Edition project management method Prepare for and take both the PRINCE2® Foundation and Practitioner Exams Please note that examinations are the responsibility of the examination board, PEOPLECERT and must be organised separately by each person attending. Content Introduction Introduction to projects and project management Structure Of PRINCE2® 7th Edition The seven Principles –the basis of what defines a PRINCE2 project People – leading successful change, teams and communication The seven Practices – to be addressed throughout the project The seven Processes - the activities to direct, manage and deliver a project successfully Practices Business case – establishing mechanisms to decide whether project is desirable, viable and achievable Organizing – establishing accountabilities and responsibilities Quality – defining mechanisms to ensure that products are fit for purpose Plans – the product based approach to planning Risk – identifying, assessing and controlling uncertainty Issues – identifying, assessing and controlling changes to the baseline and other issues Progress – monitoring actual achievements against estimate and controlling deviations Processes Starting up a Project - is there a viable and worthwhile project Directing a Project – enabling key decision making by the Project Board Initiating a Project – establishing solid foundations Controlling a Stage –assigning and monitoring work and keeping within stage tolerance Managing Product Delivery – controlling the link between the Project Manager and Team Manager(s) Managing a Stage Boundary – current stage review and next stage planning Closing a Project – confirmation of acceptance and project review Tailoring PRINCE2® - to the project environment Foundation Examination and results Practitioner Workshop and Examination PRINCE2® Practitioner Examination Objectives and Guidance PRINCE2® Review PRINCE2® Practitioner Examination Workshops PRINCE2® Practitioner Examination PRINCE2® Foundation and Practitioner Examinations The PRINCE2® Foundation Exam is of 1 hour duration and consists of 60 multiple choice questions. A Pass is 36 correct answers, 60%. The PRINCE2® Practitioner Exam is a written paper of 2.5 hours duration. There are 70 Objective Test style questions to be answered in the 2.5 hours and the candidate may use an annotated manual. The candidate must score 42/70 to be successful, 60%. Presented in association with aims4change, a PEOPLECERT Accredited Training Organisation. PRINCE2® is a Registered Trade Mark of AXELOS Limited.
AWS Cloud Practitioner Essentials
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for Sales Legal Marketing Business analysts Project managers AWS Academy students Other IT-related professionals Overview Summarize the working definition of AWS Differentiate between on-premises, hybrid-cloud, and all-in cloud Describe the basic global infrastructure of the AWS Cloud Explain the six benefits of the AWS Cloud Describe and provide an example of the core AWS services, including compute, network, databases, and storage Identify an appropriate solution using AWS Cloud services with various use cases Describe the AWS Well-Architected Framework Explain the shared responsibility model Describe the core security services within the AWS Cloud Describe the basics of AWS Cloud migration Articulate the financial benefits of the AWS Cloud for an organization?s cost management Define the core billing, account management, and pricing models Explain how to use pricing tools to make cost-effective choices for AWS services This course is for individuals who seek an overall understanding of the Amazon Web Services (AWS) Cloud, independent of specific technical roles. You will learn about AWS Cloud concepts, AWS services, security, architecture, pricing, and support to build your AWS Cloud knowledge. This course also helps you prepare for the AWS Certified Cloud Practitioner exam. Prerequisites General IT technical knowledge, General IT business knowledge 1 - Introduction to Amazon Web Services Summarize the benefits of AWS Describe differences between on-demand delivery and cloud deployments Summarize the pay-as-you-go pricing model 2 - Compute in the Cloud Describe the benefits of Amazon Elastic Compute Cloud (Amazon EC2) at a basic level Identify the different Amazon EC2 instance types Differentiate between the various billing options for Amazon EC2 Describe the benefits of Amazon EC2 Auto Scaling Summarize the benefits of Elastic Load Balancing Give an example of the uses for Elastic Load Balancing Summarize the differences between Amazon Simple Notification Service (Amazon SNS) and Amazon Simple Queue Services (Amazon SQS) Summarize additional AWS compute options 3 - Global Infrastructure and Reliability Summarize the benefits of the AWS Global Infrastructure Describe the basic concept of Availability Zones Describe the benefits of Amazon CloudFront and Edge locations Compare different methods for provisioning AWS services 4 - Networking Describe the basic concepts of networking Describe the difference between public and private networking resources Explain a virtual private gateway using a real life scenario Explain a virtual private network (VPN) using a real life scenario Describe the benefit of AWS Direct Connect Describe the benefit of hybrid deployments Describe the layers of security used in an IT strategy Describe which services are used to interact with the AWS global network 5 - Storage and Databases Summarize the basic concept of storage and databases Describe benefits of Amazon Elastic Block Store (Amazon EBS) Describe benefits of Amazon Simple Storage Service (Amazon S3) Describe the benefits of Amazon Elastic File System (Amazon EFS) Summarize various storage solutions Describe the benefits of Amazon Relational Database Service (Amazon RDS) Describe the benefits of Amazon DynamoDB Summarize various database services 6 - Security Explain the benefits of the shared responsibility model Describe multi-factor authentication (MFA) Differentiate between the AWS Identity and Access Management (IAM) security levels Describe security policies at a basic level Explain the benefits of AWS Organizations Summarize the benefits of compliance with AWS Explain primary AWS security services at a basic level 7 - Monitoring and Analytics Summarize approaches to monitoring your AWS environment Describe the benefits of Amazon CloudWatch Describe the benefits of AWS CloudTrail Describe the benefits of AWS Trusted Advisor 8 - Pricing and Support Understand AWS pricing and support models Describe the AWS Free Tier Describe key benefits of AWS Organizations and consolidated billing Explain the benefits of AWS Budgets Explain the benefits of AWS Cost Explorer Explain the primary benefits of the AWS Pricing Calculator Distinguish between the various AWS Support Plans Describe the benefits of AWS Marketplace 9 - Migration and Innovation Understand migration and innovation in the AWS Cloud Summarize the AWS Cloud Adoption Framework (AWS CAF) Summarize six key factors of a cloud migration strategy Describe the benefits of various AWS data migration solutions, such as AWS Snowcone, AWS Snowball, and AWS Snowmobile Summarize the broad scope of innovative solutions that AWS offers Summarize the five pillars of the AWS Well-Architected Framewor 10 - AWS Certified Cloud Practitioner Basics Determine resources for preparing for the AWS Certified Cloud Practitioner examination Describe benefits of becoming AWS Certified

Grateful Leadership - Using the Power of Acknowledgment to Engage All Your People and Achieve Superior Results (On-Demand)
By IIL Europe Ltd
Grateful Leadership™ - Using the Power of Acknowledgment® to Engage All Your People and Achieve Superior Results (On-Demand) Grateful Leaders can tap into the power of personal commitment and dedication by acknowledging people in an authentic and heartfelt manner. Those leaders who model true acknowledgment behavior will inspire others to do the same and to want to dramatically increase their levels of contribution to the organization, making the power of acknowledgment transformational. What you will Learn You'll learn how to: Understand and develop the capability to act upon the need for Grateful Leadership to create a culture of appreciation in the workplace Understand the potentially huge benefits of Grateful Leadership in the workplace Overcome the barriers to using acknowledgment Demonstrate the language and subtleties of authentic and heartfelt acknowledgement behavior Describe the Seven Principles of Acknowledgment for 'High-Interest Benefits' in the context of participant's personal leadership style Describe how to coach teams, managers, and other corporate stakeholders in using Grateful Leadership to produce breakthrough results Getting Started Introductions Course goals and objectives Introspection on the practice of Grateful Leadership The Workforce Engagement Sustainability Challenge Employees who are engaged, not engaged, and actively disengaged The costs of non-engagement Meeting the workforce engagement challenge Acknowledgment, Engagement, and Leadership Acknowledgment and its benefits Recognition versus acknowledgment 'Challenging people' case study Blanchard, Covey, Keith (Servant Leadership): how acknowledgment fits into these leadership models Leadership and acknowledgment The 5 C's - Consciousness, Courage, Choice, Communication, Commitment Employing the Power of Acknowledgment Overcoming barriers to acknowledgment The Seven High-Interest Benefits Principles of Acknowledgment Exploring the acknowledgment process Applying the Principles of Acknowledgment within the Context of Your Personal Leadership Style Case study The ROI of Grateful Leadership Creating your Grateful Leadership Personal Action Plan™ Creating a Vision Statement for your organization that incorporates Grateful Leadership into your corporate culture The 360° Grateful Leadership Competency Assessment

Education & Training- Level 4 CET & Educational Psychology
By Kingston Open College
Premium Bundle of all Time | Ofqual Regulation + NCFE Awards + QLS Endorsement | Assessment & Tutor Support Included
