- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1431 Installation courses
ECS Card Health & Safety Course Kent
By MJ Electrical Training
ECS Health & Safety Course with MJ Electrical Training. Available every week, use this course to complete the application process when applying for an ECS Labourers Card.

"Explore the future of sustainable energy with our Renewable Energy Engineering course. Dive into solar, wind, bioenergy, geothermal, hydroelectric, and ocean energy technologies. Learn about energy storage and integration for a cleaner, greener tomorrow. Join us to become a skilled engineer shaping the world's renewable energy landscape.

Overview This comprehensive course on CompTIA A+ (220-1002) will deepen your understanding on this topic. After successful completion of this course you can acquire the required skills in this sector. This CompTIA A+ (220-1002) comes with accredited certification from CPD, which will enhance your CV and make you worthy in the job market. So enrol in this course today to fast track your career ladder. How will I get my certificate? You may have to take a quiz or a written test online during or after the course. After successfully completing the course, you will be eligible for the certificate. Who is This course for? There is no experience or previous qualifications required for enrolment on this CompTIA A+ (220-1002). It is available to all students, of all academic backgrounds. Requirements Our CompTIA A+ (220-1002) is fully compatible with PC's, Mac's, Laptop, Tablet and Smartphone devices. This course has been designed to be fully compatible with tablets and smartphones so you can access your course on Wi-Fi, 3G or 4G. There is no time limit for completing this course, it can be studied in your own time at your own pace. Career Path Course Curriculum 22 sections • 106 lectures • 14:51:00 total length •CompTIA A+ 2019 Core 2 (220-1002) Course Introduction: 00:02:00 •What is the CompTIA A+: 00:02:00 •Why Get A+ Certified?: 00:03:00 •What is on the CompTIA A+ Core 2 (220-1002) Exam?: 00:04:00 •How to Pass the CompTIA A+ Exam: 00:04:00 •How to use this Video Course: 00:03:00 •Professional Communication Part 1: 00:06:00 •Professional Communication Part 2: 00:07:00 •Physical Safety: 00:07:00 •What is an Operating System?: 00:09:00 •Users and Super Users: 00:05:00 •Why Windows?: 00:08:00 •Windows Editions and Versions: 00:12:00 •Touring the macOS: 00:06:00 •Touring Linux: 00:08:00 •32-Bit vs. 64-Bit Processing: 00:12:00 •Virtual Memory: 00:06:00 •Power Protection: 00:10:00 •Understanding Partitioning: 00:04:00 •MBR Partitioning: 00:12:00 •GPT Partitioning: 00:09:00 •Understanding File Systems: 00:12:00 •Popular File Systems: 00:07:00 •Formatting in Action: 00:11:00 •Dynamic Disks: 00:09:00 •Software RAID in Storage Spaces: 00:10:00 •Encrypting Mass Storage: 00:09:00 •Boot from Everything: 00:12:00 •Installing Windows: 00:12:00 •Post-Installation Tasks: 00:12:00 •Windows Installation options: 00:07:00 •What is the Registry?: 00:11:00 •Processes: 00:07:00 •Services: 00:04:00 •Your Windows Toolset: 00:08:00 •Windows 7 Task Manager: 00:09:00 •Windows 10 Task Manager: 00:06:00 •Information and Configuration Tools: 00:11:00 •Performance Monitor: 00:12:00 •Event Viewer: 00:07:00 •Tools for Programmers: 00:08:00 •Introduction to Users and Groups: 00:06:00 •Managing Users and Groups: 00:12:00 •NTFS Permissions: 00:08:00 •Linux and macOS Permissions: 00:05:00 •File Explorer: 00:14:00 •Sharing Resources: 00:11:00 •Security Policies: 00:08:00 •Patch Management: 00:11:00 •Working with Disks: 00:06:00 •Working with Applications: 00:07:00 •System Restore: 00:05:00 •Backing up Your Files: 00:07:00 •Task Scheduler: 00:07:00 •Understanding the CLI: 00:11:00 •Navigating the CLI: 00:14:00 •Working with Folders: 00:07:00 •Working with Files: 00:11:00 •Working with Drives: 00:13:00 •Super Copy Commands: 00:09:00 •Advanced Windows Command Line: 00:08:00 •Advanced Linux Commands: 00:13:00 •Command-Line Permissions: 00:08:00 •Introduction to Scripting: 00:10:00 •Interpreted Languages: 00:12:00 •Windows Recovery Environment: 00:05:00 •Advanced Windows Startup Options: 00:07:00 •Troubleshooting Boot Problems: 00:10:00 •Troubleshooting at the GUI: 00:11:00 •Troubleshooting Applications: 00:07:00 •Kernel Panic: 00:05:00 •Resolutions and Aspect Ratios: 00:06:00 •Multiple Monitors: 00:05:00 •Network Card Troubleshooting: 00:09:00 •Working with Connections: 00:09:00 •Working with Workgroups: 00:08:00 •Working with Active Directory: 00:14:00 •Windows Sharing with Mac and LInux: 00:07:00 •Net Command: 00:04:00 •Firewall Configuration: 00:11:00 •Windows Firewall: 00:08:00 •Port Forwarding: 00:07:00 •Wireless Encryption: 00:11:00 •Enterprise Wireless: 00:16:00 •Telnet and SSH: 00:07:00 •Remote Desktop Connections: 00:06:00 •The World Wide Web: 00:09:00 •Troubleshooting Internet Connections: 00:07:00 •Power Management: 00:11:00 •Mobile Device Security: 00:08:00 •Mobile Security Troubleshooting: 00:06:00 •Mobile Device Troubleshooting: 00:10:00 •Threats: 00:10:00 •Physical Security: 00:08:00 •Passwords and Authentication: 00:14:00 •Malware: 00:14:00 •Anti-Malware: 00:11:00 •Social Engineering: 00:06:00 •Licensing: 00:10:00 •Incident Response: 00:05:00 •Environmental Controls: 00:06:00 •Documents You Need to Know: 00:09:00 •Data You Need to Know: 00:04:00 •Change Management: 00:06:00 •The Zen of Backup: 00:11:00 •Recycling and Data Destruction: 00:07:00
Overview This comprehensive course on The Complete Microsoft OneDrive Course will deepen your understanding on this topic. After successful completion of this course you can acquire the required skills in this sector. This The Complete Microsoft OneDrive Course comes with accredited certification from CPD, which will enhance your CV and make you worthy in the job market. So enrol in this course today to fast track your career ladder. How will I get my certificate? At the end of the course there will be an online written test, which you can take either during or after the course. After successfully completing the test you will be able to order your certificate, these are included in the price. Who is This course for? There is no experience or previous qualifications required for enrolment on this The Complete Microsoft OneDrive Course. It is available to all students, of all academic backgrounds. Requirements Our The Complete Microsoft OneDrive Course is fully compatible with PC's, Mac's, Laptop, Tablet and Smartphone devices. This course has been designed to be fully compatible with tablets and smartphones so you can access your course on Wi-Fi, 3G or 4G. There is no time limit for completing this course, it can be studied in your own time at your own pace. Career Path Learning this new skill will help you to advance in your career. It will diversify your job options and help you develop new techniques to keep up with the fast-changing world. This skillset will help you to- Open doors of opportunities Increase your adaptability Keep you relevant Boost confidence And much more! Course Curriculum 12 sections • 83 lectures • 05:21:00 total length •The Complete Microsoft OneDrive Course -Mastering OneDrive Promo: 00:01:00 •Quick Reminder - You Can Ask Me Anytime: 00:01:00 •Another Quick Reminder: You Facebook Group: 00:01:00 •Quick Win - Create a Folder and Rename It: 00:01:00 •Another Quick Quick Win - Share and Collaborate: 00:01:00 •What's OneDrive: 00:03:00 •OneDrive Free and Paid Plans: 00:04:00 •OneDrive Sign up: 00:05:00 •OneDrive Personal Vault: 00:02:00 •OneDrive PC folder Backup: 00:02:00 •OneDrive Desktop App Download and Installation: 00:02:00 •OneDrive Mobile App Download and Installation: 00:04:00 •Quick Win - Change the View of Displayed Files and Folder: 00:01:00 •Another Quick Win Create a New Album: 00:01:00 •Complete OneDrive Environment: 00:06:00 •Upload and Download in OneDrive: 00:03:00 •Creating New File and Folder in OneDrive: 00:02:00 •Selecting Files and Folder in OneDrive: 00:01:00 •Sharing and collaborating files and folder in OneDrive: 00:04:00 •Other options in top bar of the files and folder: 00:04:00 •Other options in top bar of the files and folder part 2: 00:08:00 •Picture options in OneDrive: 00:03:00 •Right Click options in OneDrive: 00:01:00 •Personals Valid in OneDrive: 00:02:00 •Personals Valid Options in OneDrive: 00:03:00 •Shared Folder in OneDrive: 00:02:00 •OneDrive Settings - Storage Management: 00:03:00 •OneDrive Settings (cont.): 00:04:00 •Microsoft OneDrive Mobile Version: 00:07:00 •Complete Microsoft Word Environment: 00:05:00 •Ribbon Guide: 00:01:00 •Menu and Groups Guide: 00:02:00 •Learn Functions and Options Then Projects: 00:01:00 •Microsoft Word Home Menu Tools: 00:17:00 •Microsoft Word Home Reviewing and Viewing Mode: 00:02:00 •Microsoft Word File Menu: 00:05:00 •Microsoft Word Insert Menu - Page Break and Table: 00:08:00 •Microsoft Word Insert Picture Menu: 00:05:00 •Microsoft Word Word Inserting Header and Footer, symbol and emoji: 00:05:00 •Microsoft Word Layout Menu: 00:02:00 •Microsoft OneDrive References Menu: 00:04:00 •Microsoft Word Review Menu: 00:04:00 •Microsoft Word View and Help: 00:02:00 •Timetable Making in Microsoft Word: 00:06:00 •Bill System in Microsoft Word: 00:06:00 •Microsoft Excel In OneDrive Environment: 00:03:00 •Microsoft Excel Home (Part 1): 00:11:00 •Microsoft Excel Number Formats: 00:03:00 •Microsoft Excel Conditional Format: 00:03:00 •Microsoft Excel Formatting a Table: 00:07:00 •Microsoft One Drive Insert: 00:06:00 •Microsoft Data, Review and View: 00:04:00 •Salary Table in Microsoft Excel: 00:06:00 •Salary Table in Microsoft Excel (cont.): 00:07:00 •Microsoft PowerPoint Environment: 00:02:00 •Microsoft PowerPoint Home and Insert Menu: 00:06:00 •Microsoft PowerPoint Insert and Design Menu: 00:05:00 •Microsoft Power Point Animation and Transition and More: 00:04:00 •Projects of PowerPoint: 00:12:00 •OneNote in OneDrive: 00:04:00 •Forms Survey in OneDrive: 00:03:00 •Plain Text in OneDrive: 00:01:00 •OneDrive Profile Management: 00:05:00 •Account OneDrive Settings: 00:03:00 •Quick Win - Create Unknown Password: 00:01:00 •Security Is Everything!!!: 00:01:00 •Quick Win - Insecurity Is Coming from You and Others: 00:01:00 •Understand Security Type or Category: 00:02:00 •Life Savers - You Should Know These: 00:04:00 •Have Proper Password - Start Securing You Now: 00:03:00 •Don't Use the Same Password Anymore: 00:02:00 •Should You Use Longer Password or Complicated!: 00:03:00 •The Best and Only Solution to Make and Keep Password Un-Crack-Able: 00:08:00 •Last-pass Setup and Configure: 00:10:00 •Last-Pass Options Part 1: 00:03:00 •Last-Pass Options Part 2: 00:04:00 •Last-Pass Option Part 3: 00:04:00 •2FA Makes You Even Stronger in Password: 00:05:00 •Last-Pass & Authy Mobile App: 00:02:00 •Security Is Everything, Keep Secured Your Devices: 00:07:00 •Security on Your Data and Privacy: 00:08:00 •Congratulations - You Are Now a Master of OneDrive: 00:01:00 •Assignment -The Complete Microsoft OneDrive Course: 00:00:00

Minimal API Development with ASP.NET Core
By Packt
Learn to build a RESTful API using ASP.NET Core Minimal API, entity framework, and employ enterprise-level development practices and patterns. We will implement various support tools for data validations, logging, documentation, and security. You will learn everything you need to know about building a Minimal API using .NET 6 (or .NET 7 preview).
Learn how to design the interior like a pro and earn about £40K per year. Interior design is a fascinating career option. It involves creating aesthetically pleasing and functional spaces within a building or home. It is a creative field that requires technical knowledge and artistic flair. Interior designers must have a keen eye for detail, think outside the box, and have excellent communication skills. A career in interior design can be rewarding and challenging. Interior designers visualise how a space will look and feel and create a plan that meets the client's needs. They must be able to work with various materials, such as fabrics, wallpapers, paint, and furniture. They must also be able to work with contractors and other professionals to ensure that the project is completed on time and within budget. This is an excellent course for people of all skill levels who want to learn more about Interior design or dream of entering this industry. Enrol in this Interior Design to advance your career. Along with this Interior Design course, you will get 10 premium courses, an original hardcopy, 11 PDF Certificates (Main Course + Additional Courses) Student ID card as gifts. This Diploma of Interior Design and Decoration (Online) Bundle Consists of the following Premium courses: Course 01: Interior Design Professional Diploma Course 02: Advanced Diploma in Architectural & Interior Design Course 03: Carpentry: Furniture Restoration and Refurbishment Course 04: Home Decoration and Refurbishment Course Course 05: Mastering Colour-Architectural Design & Interior Decoration Course 06: Visual Merchandising Course 07: Level 2 Adobe Graphics Design Course Course 08: Drawing and Illustration Level 2 Course 09: Rendering AutoCAD Drawings in Photoshop Course 10: DIY Home Improvement Course 11: Workplace Safety Course What Will You Learn from Diploma of Interior Design and Decoration (Online)? Meeting with the client to discuss their needs, preferences, and budget. Conducting a site survey to assess the space and gather information about the structure and existing features. Developing an Interior Design concept and presenting it to the client for approval. Colour-Architectural Design & Interior Design, including DIY. Creating a detailed design plan that includes drawings, specifications, and materials lists. Managing the Interior Design project through to completion, including ordering materials, coordinating with contractors, and overseeing the installation. Deep knowledge of Interior Design tools and software. Enrol now in Interior Design to advance your career, and use the premium study materials from Apex Learning. Diploma of Interior Design and Decoration (Online) The Interior Design bundle incorporates basic to advanced level skills to shed some light on your way and boost your career. Hence, you can strengthen your Interior Designexpertise and essential knowledge, which will assist you in reaching your goal. Certificate: PDF Certificate: Free (Previously it was £6*11 = £66) Hard Copy Certificate: Free (For The Title Course: Previously it was £10) CPD 110 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Diploma of Interior Design and Decoration (Online) Beginners Interior design enthusiasts Interior design students Those preparing for a home renovation Requirements Diploma of Interior Design and Decoration (Online) This Interior Design course has been designed to be fully compatible with tablets and smartphones. Career path Diploma of Interior Design and Decoration (Online) Having this knowledge will boost the value of your CV and allow you to apply for jobs in a variety of industries, such as, Home Decorating Consultant Home Decorator Home Organiser Home Stager Home Staging Consultant Interior Design Consultation And many more. Certificates Certificate of completion Digital certificate - Included Certificate of completion Hard copy certificate - Included You will get the Hard Copy certificate for the title course (Interior Design) absolutely Free! Other Hard Copy certificates are available for £10 each. Please Note: The delivery charge inside the UK is £3.99, and the international students must pay a £9.99 shipping cost.

Comprehensive PostgreSQL Administration
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This class is intended for DBAs and IT Professionals who are responsible for administration and maintenance of PostgreSQL, and want to increase proficiency and learn best practices. Targeted at: DBAs and Architects, and appropriate for Analysts, Support Engineers, and other IT professionals Overview Please refer to overview This is an immersive 5-day class that offers hands-on labs and combines the core topics from Foundations of Postgres Administration and Advanced PostgreSQL Administration into a one-week class, with significant savings over list price. Upon course completion, you will be prepared to manage mission critical PostgreSQL installations, and perform core administration tasks with confidence and skill. Course Outline 1 - POSTGRES SYSTEM ARCHITECTURE 2 - INSTALLATION AND GETTING STARTED 3 - CONFIGURATION, CREATING, MANAGING DATABASES 4 - USER TOOLS ? USING PSQL 5 - GUI TOOLS - USING PGADMIN 4 6 - SECURITY BASICS 7 - SQL PRIME BACKUP AND RECOVERY 8 - ROUTINE MAINTENANCE 9 - POSTGRES DATA DICTIONARY 10 - MOVING DATA 11 - SQL TUNING 12 - PERFORMANCE TUNING 13 - STREAMING REPLICATION 14 - TABLE PARTITIONING 15 - EXTENSION MODULES 16 - MONITORING 17 - UPGRADING BEST PRACTICES

VMware vRealize Network Insight: Install, Configure, Manage [v6.1]
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Network professionals and who design, build, operate, manage, and troubleshoot software-defined networking and security, and application owners who need visibility across multi-cloud environments Overview By the end of the course, you should be able to meet the following objectives: Explain the features and architecture of vRealize Network Insight Describe the vRealize Network Insight installation processes and requirements Navigate the vRealize Network Insight GUI Describe major use cases for vRealize Network Insight and their benefits Deploy vRealize Network Insight Use vRealize Network Insight to monitor, operate, analyze, and troubleshoot the infrastructure supporting your applications This two-day, hands-on course gives you the skills to deploy and use VMware vRealize© Network Insight? to ensure an optimized, highly available, and secure infrastructure for your applications. You will learn the features, components, architecture, and benefits of vRealize Network Insight and how to use it to simplify daily operation and troubleshooting tasks. Course Introduction Introductions and course logistics Course objectives Introduction to vRealize Network Insight Identify the use cases for vRealize Network Insight Access the vRealize Network Insight Home page View vRealize Network Insight entity data Perform searches for specific entity data Create entity search queries Find and use event data vRealize Network Insight Architecture and Components Identify the components of vRealize Network Insight Describe the function of each component and how the components interact Check the health of vRealize Network Insight components vRealize Network Insight Installation Deploy vRealize Network Insight components Configure the pairing relationship between the platform VM and the collector VM Troubleshoot platform VM and collector VM configuration problems Explain how data sources export flow information Add VMware vCenter Server© to vRealize Network Insight Add a VMware NSX-T© data source to vRealize Network Insight Configure IPFIX Distinguish between the mechanisms used to scale vRealize Network Insight Select the appropriate scaling mechanism for your environment Describe how clusters are expanded Integrate VMware vRealize© Operations? with vRealize Network Insight Import a vRealize Network Insight instance into VMware vRealize© Suite Lifecycle Manager? vRealize Network Insight Use Cases Explain use cases for vRealize Network Insight Create vRealize Network Insight applications Perform application discovery Plan and optimize micro-segmentation and security for applications Explain the use of flow analytics Use flow information from physical devices in security planning Generate virtual machine path topologies between entities using flows Extract useful information from path topologies Validate NSX-T and NSX for vSphere deployments Monitor and troubleshoot NSX-T events Operations and Troubleshooting Common Issues Perform vRealize Network Insight operations by using VMware vSphere© tags Use the flow analytics dashboards to perform flow analysis Set and configure thresholds to identify aberrations in the behavior of entities Use vRealize Network Insight tools to troubleshoot common problems Additional course details:Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware vRealize Network Insight: Install, Configure, Manage [v6.1] training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware vRealize Network Insight: Install, Configure, Manage [v6.1] course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
![VMware vRealize Network Insight: Install, Configure, Manage [v6.1]](https://cademy-images-io.b-cdn.net/9dd9d42b-e7b9-4598-8d01-a30d0144ae51/4c81f130-71bf-4635-b7c6-375aff235529/original.png?width=3840)
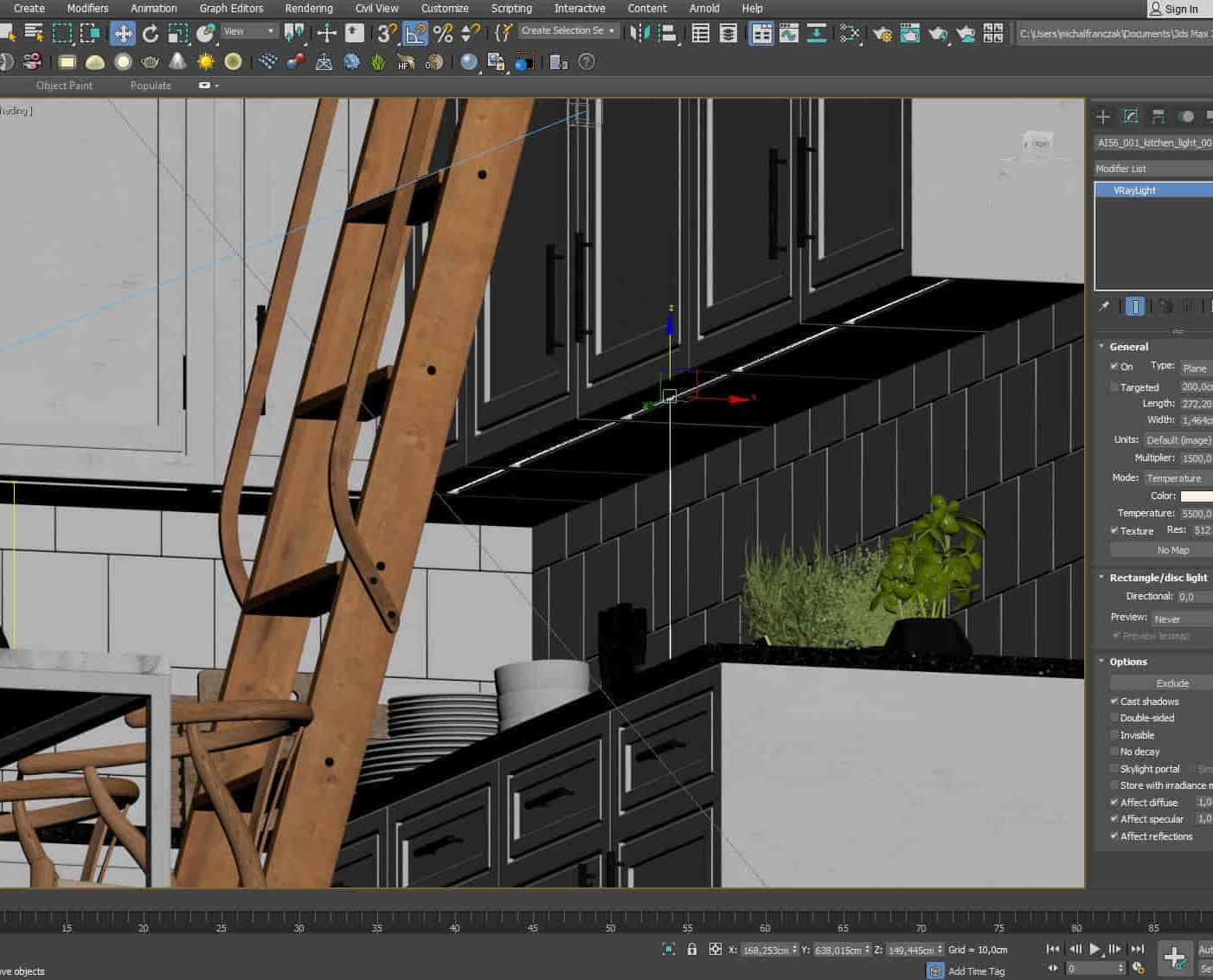
3D Studio Max and CAD Courses 1 on 1
By ATL Autocad Training London
These courses are designed for aspiring 3D artists, students, graduates, creative professionals, CAD designers, and anyone passionate about 3D art. Whether you're looking to launch a career, enhance existing skills, or explore new creative avenues, our courses provide comprehensive training tailored to various skill levels and interests. Check our Website Duration: 16 hours Method: 1-on-1 and Tailored content Dates and Times: Select your preferred hour from Monday to Saturday, available between 9 am and 7 pm. CAD and 3D Studio Max Training Course Duration: 16 hours Course Outline: Introduction to AutoCAD Familiarizing yourself with the AutoCAD interface Navigating the drawing environment Mastering fundamental 2D geometry creation Exploring essential drawing tools and commands Introduction to blocks and symbols for efficient design Advanced AutoCAD Techniques Delving into advanced drawing methods Proficiently manipulating and editing 2D geometry Crafting custom symbols and blocks for enhanced productivity Working with text and annotations for clear communication Utilizing layers and line types for organized design 3D Modeling in AutoCAD Venturing into the world of 3D modeling Precision crafting of 3D solids and surfaces Seamless modification and manipulation of 3D geometry Crafting custom materials and textures for realistic designs Effective utilization of AutoCAD's lighting and camera systems Introduction to 3ds Max Embracing the 3ds Max interface and configuring the workspace Proficiency in navigating within 3ds Max Understanding the viewport for optimized design Exploring basic 3D modeling techniques in 3ds Max Materials and Textures in 3ds Max Application and modification of textures for enhanced designs Mastering the art of UVW mapping for precise texturing Utilizing the material editor for creative freedom Crafting custom materials aligned with your design vision Harnessing the power of Vray materials for lifelike renders Lighting in 3ds Max Introduction to various lighting techniques Grasping light properties for impactful designs Strategic setup of lights to enhance scenes Illuminating scenes with Vray lights Cameras in 3ds Max Mastery of camera systems in 3ds Max Exploring camera properties for cinematic effects Creating animations with cameras for dynamic scenes Utilizing Vray cameras for stunning renders Rendering in 3ds Max Unveiling the art of rendering Utilizing Vray Global Illumination for realistic lighting Leveraging Vray Physical Cameras for precise control Enhancing scenes with Vray HDRI Lighting Following a Vray Rendering Workflow for professional results Advanced Modeling Techniques Proficiency in crafting complex geometry Utilizing modifiers for intricate designs Exploring polygonal modeling for versatile creations Creating both organic and inorganic models with expertise Unleashing the potential of advanced modeling techniques Projects Application of acquired skills to create real-world scenes Designing a detailed interior scene with meticulous attention Crafting a visually impactful exterior scene Creating a complex scene featuring multiple objects and materials Course Requirements: A computer with AutoCAD and 3ds Max installed Basic knowledge of computer operations A keen interest in 2D and 3D modeling and design Course Goals: Upon course completion, you will possess a comprehensive understanding of AutoCAD and 3ds Max, enabling you to craft intricate 3D scenes enriched with advanced materials, textures, lighting, and rendering. These newfound skills empower you to advance your capabilities in both 2D and 3D modeling and rendering. Upon successful completion of this comprehensive AutoCAD and 3ds Max training, participants will attain the following skills: AutoCAD Proficiency: Mastery of 2D geometry, drawing tools, and symbols. Advanced AutoCAD Techniques: Expertise in editing, custom blocks, text, and layers. 3D Modeling in AutoCAD: Competence in crafting 3D solids, textures, and lighting. Introduction to 3ds Max: Proficient navigation of the interface and fundamental 3D modeling. Materials and Textures: Application and customization of textures using Vray. Lighting and Cameras: Mastery of lighting and camera systems within 3ds Max. Rendering: Production of high-quality renders through Vray. Advanced Modeling: Proficiency in handling complex geometry and creating organic models. Real-World Projects: Capability to design interiors, exteriors, and intricate scenes. Skills Acquired: Mastering 3D Modeling Techniques in 3D Studio Max Advanced Texturing and Material Application Skills Proficiency in Lighting and Rendering Techniques Expertise in Animation and Keyframe Techniques Comprehensive Scene Composition and Camera Setup Knowledge Career Opportunities: Senior 3D Modeler Experienced CAD Designer Lighting and Rendering Specialist Animation Director Architectural Visualization Expert Upon completing our 3D Studio Max and CAD Courses, students will acquire advanced 3D modeling, animation, and CAD design skills, paving the way for rewarding careers in roles such as Senior 3D Modeler, CAD Designer, Lighting Specialist, Animation Director, and Architectural Visualization Expert. You will gain access to the following benefits: An Autocad and 3ds Max Certificate of Attendance. A comprehensive PDF training guide for 3ds Max and CAD. Real-time feedback during sessions, with the option to record them as video archives. We offer the following advantages: Price guarantee to ensure the best value for your investment. Personalized one-on-one training for focused learning. Flexible scheduling options available seven days a week, from 9 am to 7 pm. Lifetime email and phone support for ongoing assistance. Assistance with software installation and computer setup. Referral discounts and special offers on group training courses.
Essentials of UNIX Administration with FreeBSD 12.1
By Packt
This video course will get you started with UNIX and will give you in-depth and hands-on information on UNIX administration. From installing and updating FreeBSD to using UNIX commands to managing UNIX servers, you'll learn it all in this video course.
Search By Location
- Installation Courses in London
- Installation Courses in Birmingham
- Installation Courses in Glasgow
- Installation Courses in Liverpool
- Installation Courses in Bristol
- Installation Courses in Manchester
- Installation Courses in Sheffield
- Installation Courses in Leeds
- Installation Courses in Edinburgh
- Installation Courses in Leicester
- Installation Courses in Coventry
- Installation Courses in Bradford
- Installation Courses in Cardiff
- Installation Courses in Belfast
- Installation Courses in Nottingham