- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
416 Courses in Cardiff delivered Live Online
CPD Accredited, Interactive Short Course 2 hr session Make sure that everyone knows what to do in case a member of staff or the public gets an asthma attack Better still, learn how to prevent an asthma attack from occurring in the first place! Course Contents What is asthma How many people have asthma How it affects a person's lungs The severity of the condition Triggers for an asthma attack Signs & Symptoms of an asthma attack Medication First Aid for a person having an asthma attack What it is like to live with asthma Benefits of this Short Course: In the UK, 5.4 million people (12.35% of the population) have asthma, 200,000 severely. Every day, three of those people die from an asthma attack Every 20 minutes, someone is admitted to hospital due to their asthma, and every 8 minutes, that is a child Learning from home is a good way to keep one's skills and knowledge up to date With the knowledge you'll pick up from this course, you could potentially save someone's life!
Definition of Safeguarding Legislation & agreed ways of working Definition of Safeguarding Legislation & agreed ways of working Every child matters guidance Myths and statistics Effects on young people Leadership/worker skills Common indicators of abuse Reporting of abuse and potential abuse Barriers to reporting abuse Understanding the types of abuse Recognising acts, signs and symptoms of abuse Who is vulnerable / at risk The role of dignity in safeguarding Legislation and policies and procedure What to do should you have a concern Overview of prevent How to respond to an individual should they disclose a concern

IP security training course description Connection to the Internet is becoming an essential business tool. This course looks at firewalls, digital certificates, encryption and other essential topics for e-commerce sites. A generic course that looks at firewalls and VPNs. Hands on sessions include using hacking tools and configuring firewalls. What will you learn Describe: Basic security attacks RADIUS SSL IPSec VPNs Implement digital certificates Deploy firewalls to protect Web servers and users. Secure Web servers and clients. IP security training course details Who will benefit: Network administrators. Network operators. Security auditors Prerequisites: TCP/IP foundation for engineers Duration 2 days IP security training course contents TCP/IP review Brief overview of the relevant headers. Hands on Download software for course, use analyser to capture passwords on the wire. Security review Policies, Types of security breach, denial of service, data manipulation, data theft, data destruction, security checklists, incident response. Security exploits The Internet worm, IP spoofing, SYN attack, hijacking, Ping o' Death⦠keeping up to date with new threats. Hands on Use a port scanning tool, use a 'hacking' tool. Firewalls Products, Packet filtering, DMZ, content filtering, stateful packet inspection, Proxies, firewall architectures, Intrusion Detection Systems, Viruses. Hands on Set up a firewall and prevent attacks. NAT NAT and PAT, Why use NAT, NAT-ALG, RSIP. Encryption Encryption keys, Encryption strengths, Secret key vs Public key, algorithms, systems, SSL, SSH, Public Key Infrastructures. Hands on Run a password-cracking program. Authentication Types of authentication, Securid, Biometrics, PGP, Digital certificates, X.509 v3, Certificate authorities, CRLs, PPP authentication, RADIUS. Hands on Using certificates. Web client and server security Cookies, browser certificates, censorship, PICS. Operating system security, Web server user authentication, Restricting access, Logging, Securing CGI scripts. Hands on Browser security. VPNs and IPSec What is a VPN, tunnelling, L2F, PPTP, L2TP, IPSec, AH, ESP, transport mode, tunnel mode.

SC-400T00 Administering Information Protection and Compliance in Microsoft 365
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The information protection administrator translates an organization?s risk and compliance requirements into technical implementation. They are responsible for implementing and managing solutions for content classification, data loss prevention (DLP), information protection, data lifecycle management, records management, privacy, risk, and compliance. They also work with other roles that are responsible for governance, data, and security to evaluate and develop policies to address an organization's risk reduction and compliance goals. This role assists workload administrators, business application owners, human resources departments, and legal stakeholders to implement technology solutions that support the necessary policies and controls. Learn how to protect information in your Microsoft 365 deployment. This course focuses on data lifecycle management and information protection and compliance within your organization. The course covers implementation of data loss prevention policies, sensitive information types, sensitivity labels, data retention policies, Microsoft Purview Message Encryption, audit, eDiscovery, and insider risk among other related topics. The course helps learners prepare for the Microsoft Information Protection Administrator exam (SC-400). Prerequisites Foundational knowledge of Microsoft security and compliance technologies. Basic knowledge of information protection concepts. Understanding of cloud computing concepts. Understanding of Microsoft 365 products and services. 1 - Introduction to information protection and data lifecycle management in Microsoft Purview Know your data Protect your data Prevent data loss Govern your data 2 - Classify data for protection and governance Data classification overview Classify data using sensitive information types Classify data using trainable classifiers Review sensitive information and label usage Explore labeled and sensitive content Understand activities related to your data 3 - Create and manage sensitive information types Compare built-in versus custom sensitive information types Create and manage custom sensitive information types Describe custom sensitive information types with exact data match Implement document fingerprinting Create keyword dictionary 4 - Understand Microsoft 365 encryption Learn how Microsoft 365 data is encrypted at rest Understand service encryption in Microsoft Purview Explore customer key management using Customer Key Learn how data is encrypted in-transit 5 - Deploy Microsoft Purview Message Encryption Implement Microsoft Purview Message Encryption Implement Microsoft Purview Advanced Message Encryption Use Microsoft Purview Message Encryption templates in mail flow rules 6 - Protect information in Microsoft Purview Information protection overview Configure sensitivity labels Configure sensitivity label policies Configure auto-labeling policies Manage, monitor, and remediate information protection 7 - Apply and manage sensitivity labels Apply sensitivity labels to Microsoft Teams, Microsoft 365 groups, and SharePoint sites Plan on-premises labeling Configure on-premises labeling for the Unified Labeling Scanner Apply protections and restrictions to email and files Monitor label performance using label analytics 8 - Prevent data loss in Microsoft Purview Data loss prevention overview Identify content to protect Define policy settings for your DLP policy Test and create your DLP policy Prepare Endpoint DLP Manage DLP alerts in the Microsoft Purview compliance portal View data loss prevention reports Implement the Microsoft Purview Extension 9 - Configure DLP policies for Microsoft Defender for Cloud Apps and Power Platform Configure data loss prevention policies for Power Platform Integrate data loss prevention in Microsoft Defender for Cloud Apps Configure policies in Microsoft Defender for Cloud Apps Manage data loss prevention violations in Microsoft Defender for Cloud Apps 10 - Manage data loss prevention policies and reports in Microsoft 365 Configure data loss prevention for policy precedence Implement data loss prevention policies in test mode Explain data loss prevention reporting capabilities Manage permissions for data loss prevention reports Manage and respond to data loss prevention policy violations 11 - Manage the data lifecycle in Microsoft Purview Data Lifecycle Management overview Configure retention policies Configure retention labels Configure manual retention label policies Configure auto-apply retention label policies Import data for Data Lifecycle Management Manage, monitor, and remediate Data Lifecycle Management 12 - Manage data retention in Microsoft 365 workloads Explain retention in Exchange Online Explain retention in SharePoint Online and OneDrive Explain retention in Microsoft Yammer Activate archive mailboxes in Microsoft Exchange Apply mailbox holds in Microsoft Exchange Recover content in Microsoft Exchange 13 - Manage records in Microsoft Purview Records management overview Import a file plan Configure retention labels Configure event driven retention Manage, monitor, and remediate records 14 - Explore compliance in Microsoft 365 Plan for security and compliance in Microsoft 365 Plan your beginning compliance tasks in Microsoft Purview Manage your compliance requirements with Compliance Manager Examine the Compliance Manager dashboard Analyze the Microsoft Compliance score 15 - Search for content in the Microsoft Purview compliance portal Explore Microsoft Purview eDiscovery solutions Create a content search View the search results and statistics Export the search results and search report Configure search permissions filtering Search for and delete email messages 16 - Manage Microsoft Purview eDiscovery (Standard) Explore Microsoft Purview eDiscovery solutions Implement Microsoft Purview eDiscovery (Standard) Create eDiscovery holds Search for content in a case Export content from a case Close, reopen, and delete a case 17 - Manage Microsoft Purview eDiscovery (Premium) Explore Microsoft Purview eDiscovery (Premium) Implement Microsoft Purview eDiscovery (Premium) Create and manage an eDiscovery (Premium) case Manage custodians and non-custodial data sources Analyze case content 18 - Manage Microsoft Purview Audit (Standard) Explore Microsoft Purview Audit solutions Implement Microsoft Purview Audit (Standard) Search the audit log Export, configure, and view audit log records Use audit log searching to investigate common support issues 19 - Prepare Microsoft Purview Communication Compliance Plan for communication compliance Identify and resolve communication compliance workflow Case study--Configure an offensive language policy Investigate and remediate communication compliance alerts 20 - Manage insider risk in Microsoft Purview Insider risk management overview Create and manage insider risk policies Investigate insider risk alerts Take action on insider risk alerts through cases Manage insider risk management forensic evidence Create insider risk management notice templates 21 - Implement Microsoft Purview Information Barriers Explore Microsoft Purview Information Barriers Configure information barriers in Microsoft Purview Examine information barriers in Microsoft Teams Examine information barriers in OneDrive Examine information barriers in SharePoint 22 - Manage regulatory and privacy requirements with Microsoft Priva Create and manage risk management policies Investigate and remediate risk management alerts Create rights requests Manage data estimate and retrieval for rights requests Review data from rights requests Get reports from rights requests 23 - Implement privileged access management Case study--Implementing privileged access management 24 - Manage Customer Lockbox Manage Customer Lockbox requests

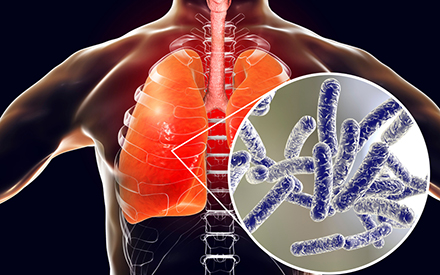
Legionella Responsible Person Course Online
By Airborne Environmental Consultants Ltd
Legionella Responsible Person Online is suitable for any persons wanting to gain an understanding of Legionella and how to prevent or control the risk of exposure to Legionella bacteria.
M.D.D SAVE MY MARRIAGE PACKAGE (COUPLES)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
7 sessions 2 separately 5 sessions with coach Marriage counselling Resolve arguments and problems Strengthen marriage One growth arena per session Emotional intelligence training Love, respect, communication training Trust and loyalty strengthening Couples improvement programme MDD Modern EFT techniques Prevent a breakup Enhance love and satisfaction in your relationship 1 hour x 5 https://relationshipsmdd.com/product/save-my-marriage-package/

STGO Awareness, Abnormal Loads & Escort Vehicles Course - Online - September 2025
By Total Compliance
STGO Abnormal Loads

Leading People through Change: In-House Training
By IIL Europe Ltd
Leading People through Change: In-House Training Research shows that 70% of change initiatives fail in large organizations. The largest factor contributing to this failure rate is leadership - the inability to plan and lead people through change. In many change situations, tremendous focus is put on strategy, processes, and systems, while the issue of changing people's behavior is assumed it will 'just happen'. In this interactive course, you will learn why the people side of change is crucial. We will begin by understanding why and how people resist change, and how important it is to become strong and effective change champions. Next, we will focus on critical change management practices - creating our vision of the future state, planning for acceptance in our change audience and stakeholders, mitigating threats, and capitalizing on opportunities. We will use metrics to plan, show progress, and confirm success. Lastly, we will focus on the need to reinforce and sustain change, and to prevent relapse to old ways and methods. What you will Learn At the end of this program, you will be able to: Realize the nature of change and describe how resistance manifests in people Compare prevalent change models and categorize their similarities Identify and rate the skills, traits, and behaviors of effective change champions Envision the future state and assess stakeholders Plan for change communication, training, and risks Evaluate change effectiveness using feedback and metrics Develop reinforcement practices for benefits and communication Foundation Concepts What is Change? Resistance to Change Common Change Management Theories Becoming a Change Champion Plan Envisioning the future state Planning for people Change management plan Do Change communication Training Piloting Risks Study Feedback Metrics Variance analysis Act Benefits realization Change sustainment Reinforcement messaging and communications

ICA International Diploma in Governance, Risk and Compliance
By International Compliance Association
ICA International Diploma in Governance, Risk and Compliance New technologies are changing the role of a compliance professional. Fintech and Regtech are now embedded in compliance lexicon, but what do the terms mean, and what are the practical impacts, both positive and negative, that we need to understand and manage? The ICA International Diploma in Governance, Risk and Compliance helps you to answer these questions and apply the answers directly within your organisation. Gain a broad understanding of the regulatory environment as well as the specialist skills and knowledge to be able to identify and manage key regulatory risks today and in the future. Get to grips with the nuances of the regulatory environment and the impact to your organisation. Understand why promoting a positive compliance culture is not just good for compliance but good for business. Explore how to maximise the benefits of emerging technologies. Develop your inter-personal skills so you can be the best Compliance Manager. Learn from the experiences of compliance professionals from other firms and sectors and share ideas. This governance, risk and compliance course is awarded in association with Alliance Manchester Business School, the University of Manchester. Benefits of studying with ICA: Flexible learning solutions that are suited to you Our learner-centric approach means that you will gain relevant practical and academic skills and knowledge that can be used in your current role Improve your career options by undertaking a globally recognised qualification that hiring managers look for as part of their hiring criteria Many students have stated that they have received a promotion and/or pay rise as a direct result of gaining their qualification The qualifications ensure that you are enabled to develop strategies to help manage and prevent risk within your firm, thus making you an invaluable asset within the current climate Completion of this training course will provide participants with the following professional qualification: ICA Diploma in Governance, Risk and Compliance. In addition, participants will be entitled to use the following designation 'Dip (Comp).' These qualifications are awarded in association with Alliance Manchester Business School, the University of Manchester. What will you learn? Understanding governance, risk and regulatory compliance Why we need to understand the regulated environment Why are governance and culture essential for effective regulatory compliance risk management? The role of the compliance department and the compliance professional Risk management as the key to effective compliance Case Studies

Legionella Awareness Course
By Airborne Environmental Consultants Ltd
Legionella awareness is suitable for any persons wanting to gain an understanding of Legionella and how to prevent or control the risk of exposure to Legionella bacteria. The main subject areas of the course are: What Legionella is Obligations under current Health & Safety legislation and ACoP L8 System hygiene Assessing and managing risk Outbreaks Hot and cold water systems Risks in other types of water systems Multiple choice test (if required).