- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
BGP training course description A detailed study of BGP, from the basics of how it works through to advanced issues such as route reflectors, policy, filtering, route selection and routing registries. The course culminates with a study of an industrial strength BGP template illustrating important issues such as bogon filtering. Practical hands on with routers follow the major sessions to reinforce the theory. A multiple choice exam, leading to the LAIT III certification, is available after the course. The exam consists of 60 questions and lasts 2 hours. What will you learn Connect enterprises to the Internet, and ISPs to each other. Describe how BGP works. List, describe and configure the main BGP attributes. Implement and troubleshoot BGP. Work with route aggregation and calculate CIDR prefixes in seconds. Influence traffic paths with BGP. BGP training course details Who will benefit: Anyone who will be working with BGP. Prerequisites: TCP/IP Foundation for engineers Definitive IP routing for engineers. Duration 5 days BGP training course contents Basic BGP IGPs, EGPs, What's BGP? BGP RIB, in/out process, tables peers, adding routes. Hands on Simple configuration and troubleshooting. The Internet and peering ASs, AS numbers, Internet structure, ISP types, ISP network design, IXs, peering vs. transit, public/ private peering, bi/multi-lateral peering. Hands on AS information gathering. How BGP works Incremental updates, Path vector protocols, BGP protocol stack, the BGP header, message types, NLRI, withdrawn routes, route refresh, route dampening. Hands on More troubleshooting, packet analysis. MBGP and IPv6 Multiprotocol routing, AFI, SAFI, MBGP and multicasts, IPv6, MPLS VPNs. Hands on IPv6 BGPv4 aggregation CIDR, benefits, techniques, shortcuts, configuring BGP aggregation, leaking routes. Hands on Reducing routing table size. BGP path selection BGP attributes, attribute types, route selection order, Local preference, AS prepend, MEDs. Hands on Influencing traffic with BGP. BGP routing policies What is policy? Examples, route filtering, AS filtering, REs, applying preference selectively, peer groups. Hands on Sophisticated policies. RIPE and routing registries RIRs, Allocations, assignments, PI vs. PA. Objects, RPSL, routing registry, Hands on The RIPE database. Automating BGP configuration Automation tools, whois, IRRToolSet, Bogon lists, tracking bogon lists, HTTP, Peering, routing registries, DNS. Communities What is a community? Community names, communities for: peer types and geography. RFC 1998, default communities. Hands on Setting local preference on other routers. Route servers What are route servers? LINX route servers, route server policy control, What are route collectors, Looking glasses. Hands on Setting up and working with a route server. Peer relationships IBGP, EBGP, next hop self, advertising routes into/out of BGP, synchronisation. Hands on IBGP, troubleshooting a large BGP network. Route reflectors and confederations Full mesh IBGP, Route reflectors, RR configuration and design, confederations, migration issues. Hands on RR configuration. BGP architectures Stub vs. transit AS, when to use BGP, multihoming strategies and issues, default routes. Multihop EBGP, load balancing. Hands on Multihoming. BGP security RFC 7454, security steps, BGP TTL security, filters, RPKI, ROAs, rsync, rrdp, validators. A secure BGP template. Hands on RPKI prefix validation.

Project Contract Management Skills
By IIL Europe Ltd
Project Contract Management Skills Contracts are a critical part of most large or strategic projects/programs. As such, it is imperative that Project and Program Managers be well versed on basic implications of a contract as well as best practices in contract management. While not as critical a need, anyone involved in projects that involve external relationships should have a healthy appreciation for the power of good contract management. The overall goal of the course is to provide knowledge to manage complex contracts in a global environment. What You Will Learn After this program, you will be able to: Explain overall project procurement process from a buyer and seller perspective Recognize the importance of key contractual terms and how they affect projects Evaluate and contribute to the pre-contract documents and processes Identify and mitigate common pitfalls throughout the procurement process Utilize techniques to administer contracts Getting Started Introductions Course structure Course goals and objectives Foundation Concepts The Importance of Contract Management Terms and Definitions Contract Management Process Legal Systems Codes of Conduct Planning Business Analysis Procurement Management Plan Procurement Statement of Work (SOW) Common Pitfalls Solicit Contract Market Analysis Bid documents Sellers' Proposals Pitfalls Execute Contract Evaluate and Award Contract Negotiate Contract Execute Contract Common Pitfalls Deliver the Contract Preparing to Deliver Project Plan Risk Management Common Pitfalls Administer Contract Enabling Contract Management Contract Performance Monitoring and Control Change Management Financial Management / Payment Dispute Management & Resolution Contract Completion and Closure

Lawful Intercept training course description Packet based networks require a different approach to Lawful Intercept (LI) than that used in circuit switched networks. This course focuses on what Lawful Interception and Data Retention (DR) means to communications service providers in the IP and NGN areas. The course assumes a basic knowledge of IP networking (i.e. DNS, TCP/UDP, IP, RTP) and the building of services on an IP platform (e.g. SIP, SDP, FTP, HTTP). The course first looks at the regulatory context for LI and DR and how this is translated to a practical architecture. What will you learn Recognise the legal and regulatory obligations to provide LI and DR. Identify the components of the handover architecture for each of LI and DR. Identify the preferred location of points of interception and points of retention in the IP network. Map intercepted material to handover protocols. Understand the data mapping defined in the available standards for both LI and DR. Lawful Intercept training course details Who will benefit: Technical and managerial staff needing to implement public networks. Prerequisites: TCP/IP Foundation Duration 1 day Lawful Intercept training course contents What is meant by LI and DR? Review of regulation: Data protection Directive; Data Retention Directive; RIPA. LI architectures Handover and Interception: ETSI standards ES 201 671 and TS 102 232. LI handover protocol IRI and CC handover; correlation; manual interfaces. DR architectures Handover of query results; points of retention. DR query command set Retrieval of retained records. Security concerns Operation privacy; target privacy; storage and transmission integrity. Implementation Identifying PoI and PoR for provided services. LI and DR wrap up Interaction with other services, storage obligations (volume, time, availability).

Geomechanics
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course This five-day course provides an intermediate level of understanding of the geomechanical factors that affect wellbore instability, sand production and hydraulic fracture design. The course is structured such that upon completion, participants will have understood the value that geomechanics can bring to drilling, completion and production operations and will be able to leverage this value wherever it applies. The course emphasis will be on integrating the topics presented through a combination of lectures, case-studies and hands-on exercises. A special focus will be on how geomechanics knowledge is extracted from routinely acquired well data and how it is applied in the prediction and prevention of formation instability. Course Highlights The course is essentially non-mathematical and makes wide use of diagrams, pictures and exercises to illustrate the essential concepts of geomechanics Essential Rock Mechanics Principles Wellbore Stability Analysis Anisotropic Rock Properties for unconventional projects Lost Circulation and Wellbore Strengthening applications Sand Production Management Input to Hydraulic Fracture design Salt instability Training Objectives By attending this training, you will be able to acquire the following: Apply the basic concepts of geomechanics to identify, predict and mitigate against formation instability during drilling, completion and production Target Audience This course is intended for Drilling Engineers, Well Engineers, Production Technologists, Completion Engineers, Well Superintendents, Directional Drillers, Wellsite Supervisors and others, who wish to further their understanding of rock mechanics and its application to drilling and completion. There is no specific formal pre-requisite for this course. However, attendees are requested to have been exposed to drilling, completions and production operations in their positions and to have a recommended minimum of 3 years of field experience. Trainer Your Expert Course Instructor is an operational geomechanics advisor with over 46 years of experience in exploration, development and production in the upstream oil and gas industry. After obtaining a BSc (Hons) Physics degree from Aberdeen University, he worked for a variety of oil service companies in wireline operations, management and formation evaluation, before joining Schlumberger in 1995. Since 2000 he has worked principally in real-time geomechanics operations and developing acousto-geomechical applications, taking on the role of geomechanics advisor and technical manager within the Europe-Africa area of operations. Before forming his own company in 2014, Your Expert Course Instructor was one of Schlumberger's principal instructors, delivering cross-discipline internal and external geomechanics training to petrophysicists, geologists, reservoir, petroleum, well construction and drilling engineers at operating company locations, training centers and operational centers worldwide. Through extensive operational and wellsite experience gained in the North Sea, Europe, Africa, South America and the Far East, he has gained a broad based knowledge of drilling, production, log data acquisition, analysis and interpretation that has allowed him to develop and deliver pragmatic solutions to the geomechanical challenges of drilling, sand production, fracturing and unconventional reservoirs, faced by operators. His principal interests include the development and application of acousto-geomechanical techniques for the evaluation of anisotropic formations and fracture systems and the identification and prevention of wellbore instability POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

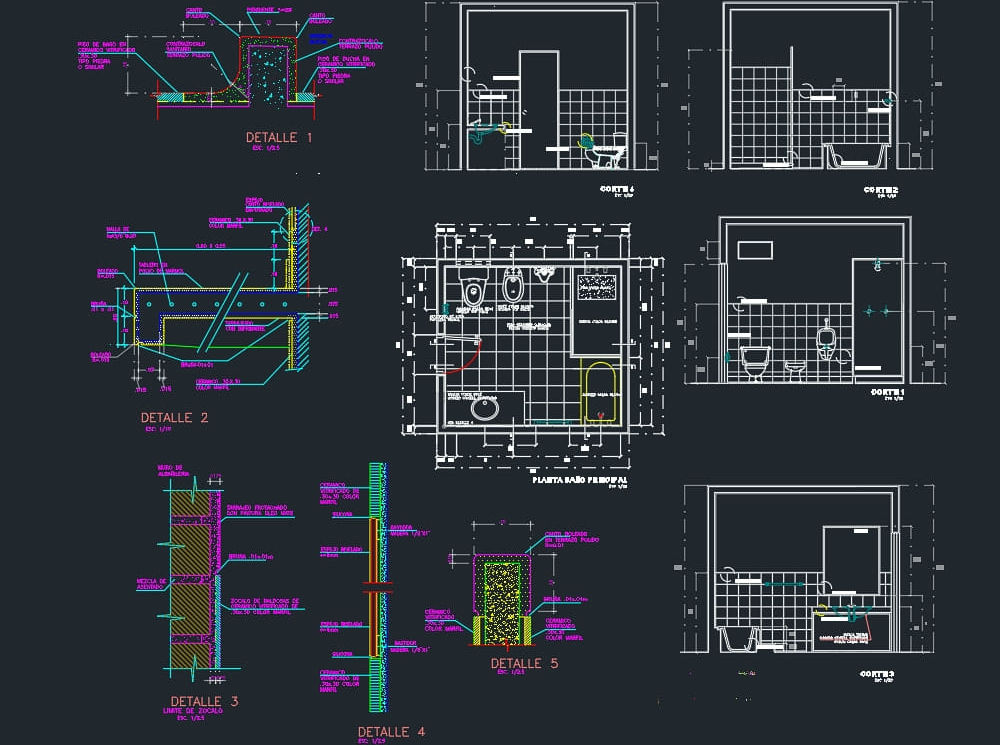
AutoCAD 3D modeling course
By Real Animation Works
Autocad face to face training customised and bespoke.
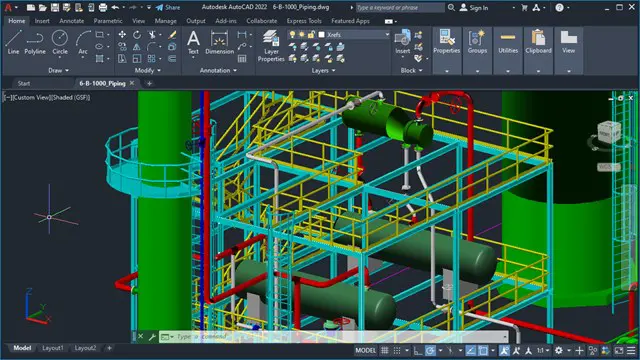
AutoCAD 2D Basics to Advanced Course
By ATL Autocad Training London
Who is this course for? AutoCAD 2D Basics to Advanced Course. Click here for more info: Website This course enables you to learn the skills in the CAD. Upon completion, you'll proficiently edit and create 2D drawings, utilizing advanced features like Paperspace and Block Attributes for increased efficiency. 1-on-1 sessions. Our booking are available Mon to Sat, 9 am to 7 pm Duration: 16 hours, which you can flexibly distribute across as many days you want. Approach: In-person or live online training. AutoCAD Basics to Advanced Level Training Course Outline. Fundamental Concepts: Introduction to AutoCAD interface, commands, and tools. Managing drawings and creating basic shapes. Basic modification techniques like erase, move, rotate, and scale. Intermediate Techniques: Working with layers and adjusting properties. Creating and modifying text and dimensions. Introduction to blocks and attributes. Advanced Topics: Advanced object modification techniques such as fillet, chamfer, trim, and extend. Utilizing grips for object manipulation. Creating and editing polylines and splines. Course Highlights: Engaging exercises and projects for skill reinforcement. Access to Q&A and troubleshooting support. Proficiency in AutoCAD 2D for basic to intermediate drawings. Topics Covered: Drawing techniques encompassing various shapes. Inquiry tools for measurement and selection. Modification commands for object manipulation. Layer management and attributes. Annotation and dimensioning. Hatching objects and working with reusable content. Layouts and viewports for better organization. Annotating drawings effectively. Polylines, splines, ellipses, and tables. Plotting drawings and creating templates. Multi-lines, revision clouds, and wipeout objects. Working with point objects and calculations. Creating and managing templates. Annotation scaling and text manipulation. Dimensioning and geometric annotations. Dynamic blocks and attributes. Layer management best practices. Introduction to sheet sets and their properties. Utilizing fields and attributes in sheet sets. Working with tables, table styles, and advanced tables. Exporting and importing tables. Creating tables linked to external data. Download AutoCAD Software https://www.autodesk.co.uk What Will I Gain from this Course? Throughout this course, you will develop expertise in the following areas: CAD layering techniques Text and dimension style manipulation Proficiency in creating and editing 2D drawings Mastery of attributed block creation and editing Efficient utilization of Paperspace Dynamic input and grips utilization This comprehensive training program not only provides you with an advanced comprehension of 2D drawing in AutoCAD but also offers a fundamental introduction to 3D drawing concepts. Upon completion of this course, you will possess the skills to: Swiftly generate schematics, parts, and assemblies Enhance efficiency by reusing content and customizing tool palettes Save time through the use of dynamic blocks, which can be edited in place Gain full control over your viewports and layouts Is This Course Right for Me? This advanced AutoCAD 2D training assumes that you are already a proficient AutoCAD user. We recommend prior attendance of our Introduction and/or Intermediate AutoCAD 2D training courses or practical experience in the topics covered in those courses. If you have any doubts about the suitability of this course for your skill level, please feel free to contact us, and we will be happy to assist you. In this course, you will gain proficiency in utilizing essential features of AutoCAD (Computer Aided Design) to enhance the efficiency of producing and editing 2D CAD drawings. You will acquire expertise in layering, text and dimension styles, the creation and modification of attributed blocks, and effective use of Paperspace. Additionally, you will master dynamic inputs, grips, and the art of renaming and purging. This flexible course grants you 16 hours to complete, typically spanning 4 to 5 days. It serves as a valuable continuation of skills acquired from the CAD: AutoCAD 2D Essentials course or as an opportunity to expand your existing AutoCAD knowledge. Upon course completion, you will possess the ability to efficiently create and modify 2D drawings, leveraging advanced features like Paperspace and Block Attributes. Your instruction will be provided by an Autodesk-certified instructor with industry experience." 1. All-encompassing course designed to accommodate both novices and advanced users. 2. Addresses essential functions and advanced methodologies in AutoCAD. 3. Enhances proficiency in creating precise and professional 2D drawings. Interactive instruction guided by seasoned educators. Benefit from on-demand access to lesson recordings for convenient revision. Receive ongoing support through lifetime email and phone assistance. Post-course Assistance: Enjoy continuous support via lifetime email and phone assistance. Should you encounter any challenges or queries after the course, we are readily available to address your concerns via email or phone calls."
Two Week Cooking Class - April 2021
By Station House Cookery School
Why not treat yourself to a deluxe culinary experience? A two week cookery course immersing you in a wonderful world of tastes, techniques and cookery skills to leave you a more confident cook. This course is ideal for the home cook who is looking to get more from their cookery and learn new tricks and techniques as well as discovering a wider range of cuisines and ingredients. Or maybe you are thinking about a career in food and drink? This is the perfect taster as you begin your culinary journey. What’s included on the course? International dishes from India, Thailand, North Africa, China, France, Italy and the Middle East. How to make Fresh Pasta and delicious Ravioli and Tortellini with different sauces to accompany them. A range of pastries including Rough Puff, Shortcrust, Hot Water Crust and Choux. Seafood - Preparing gorgeous local scallops from scratch as well as filleting a Flat Fish, a Round Fish and learning different techniques to cook them. Baking a different loaf of Bread every day. Farmhouse, Ciabatta, Soda Bread, Flat Breads and Sourdough are all covered. Basic butchery. How to joint a chicken. Ice creams and sorbets. Dairy. How to make your own Butter, Yoghurt and Soft Cheese. Stocks and Sauces. Cover Vegetarian and Vegan Cookery. How to use Herbs to best effect. The importance of Seasoning. A visit to a local Scottish Assured Venison Park and Venison Cookery. And lots more…

Two Week Cooking Class - November 2021
By Station House Cookery School
Why not treat yourself to a deluxe culinary experience? A two week cookery course immersing you in a wonderful world of tastes, techniques and cookery skills to leave you a more confident cook. This course is ideal for the home cook who is looking to get more from their cookery and learn new tricks and techniques as well as discovering a wider range of cuisines and ingredients. Or maybe you are thinking about a career in food and drink? This is the perfect taster as you begin your culinary journey. What’s included on the course? International dishes from India, Thailand, North Africa, China, France, Italy and the Middle East. How to make Fresh Pasta and delicious Ravioli and Tortellini with different sauces to accompany them. A range of pastries including Rough Puff, Shortcrust, Hot Water Crust and Choux. Seafood - Preparing gorgeous local scallops from scratch as well as filleting a Flat Fish, a Round Fish and learning different techniques to cook them. A range of Breads. Farmhouse, Ciabatta, Soda Bread, Flat Breads and Sourdough are all covered. Basic butchery. How to joint a chicken. Ice creams and sorbets. Dairy. How to make your own Butter, Yoghurt and Soft Cheese. Stocks and Sauces. Cover Vegetarian and Vegan Cookery. How to use Herbs to best effect. The importance of Seasoning. A visit to a local Scottish Assured Venison Park and Venison Cookery. And lots more…

Two Week Cooking Class - August 2021
By Station House Cookery School
Why not treat yourself to a deluxe culinary experience? A two week cookery course immersing you in a wonderful world of tastes, techniques and cookery skills to leave you a more confident cook. This course is ideal for the home cook who is looking to get more from their cookery and learn new tricks and techniques as well as discovering a wider range of cuisines and ingredients. Or maybe you are thinking about a career in food and drink? This is the perfect taster as you begin your culinary journey. What’s included on the course? International dishes from India, Thailand, North Africa, China, France, Italy and the Middle East. How to make Fresh Pasta and delicious Ravioli and Tortellini with different sauces to accompany them. A range of pastries including Rough Puff, Shortcrust, Hot Water Crust and Choux. Seafood - Preparing gorgeous local scallops from scratch as well as filleting a Flat Fish, a Round Fish and learning different techniques to cook them. A range of Breads. Farmhouse, Ciabatta, Soda Bread, Flat Breads and Sourdough are all covered. Basic butchery. How to joint a chicken. Ice creams and sorbets. Dairy. How to make your own Butter, Yoghurt and Soft Cheese. Stocks and Sauces. Cover Vegetarian and Vegan Cookery. How to use Herbs to best effect. The importance of Seasoning. A visit to a local Scottish Assured Venison Park and Venison Cookery. And lots more…

Project Contract Management Skills: In-House Training
By IIL Europe Ltd
Project Contract Management Skills: In-House Training Contracts are a critical part of most large or strategic projects/programs. As such, it is imperative that Project and Program Managers be well versed on basic implications of a contract as well as best practices in contract management. While not as critical a need, anyone involved in projects that involve external relationships should have a healthy appreciation for the power of good contract management. The overall goal of the course is to provide knowledge to manage complex contracts in a global environment. What You Will Learn After this program, you will be able to: Explain overall project procurement process from a buyer and seller perspective Recognize the importance of key contractual terms and how they affect projects Evaluate and contribute to the pre-contract documents and processes Identify and mitigate common pitfalls throughout the procurement process Utilize techniques to administer contracts Getting Started Introductions Course structure Course goals and objectives Foundation Concepts The Importance of Contract Management Terms and Definitions Contract Management Process Legal Systems Codes of Conduct Planning Business Analysis Procurement Management Plan Procurement Statement of Work (SOW) Common Pitfalls Solicit Contract Market Analysis Bid documents Sellers' Proposals Pitfalls Execute Contract Evaluate and Award Contract Negotiate Contract Execute Contract Common Pitfalls Deliver the Contract Preparing to Deliver Project Plan Risk Management Common Pitfalls Administer Contract Enabling Contract Management Contract Performance Monitoring and Control Change Management Financial Management / Payment Dispute Management & Resolution Contract Completion and Closure

Search By Location
- Basic Courses in London
- Basic Courses in Birmingham
- Basic Courses in Glasgow
- Basic Courses in Liverpool
- Basic Courses in Bristol
- Basic Courses in Manchester
- Basic Courses in Sheffield
- Basic Courses in Leeds
- Basic Courses in Edinburgh
- Basic Courses in Leicester
- Basic Courses in Coventry
- Basic Courses in Bradford
- Basic Courses in Cardiff
- Basic Courses in Belfast
- Basic Courses in Nottingham