- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Adaptive Leadership in Uncertain Times: Leading with Clarity, Courage and Flexibility
By Elite Forums Events
Course Duration: Full-day program (or two half-day modules), with options for virtual delivery or leadership retreats Target Audience: Mid to senior-level leaders, team managers, project leads, or high-potential employees who are responsible for leading through disruption, complexity, or organisational transformation. Course Objectives By the end of this course, participants will be able to: Understand the principles of adaptive leadership and why it's essential in unpredictable environments. Recognise the difference between technical and adaptive challenges. Build the mindset and behaviours needed to lead with resilience and flexibility. Engage and empower teams in the face of uncertainty and resistance. Apply practical tools to lead through change, conflict, and complexity. Course Outline Module 1: Understanding Adaptive Leadership What is adaptive leadership? Origins (Harvard Kennedy School, Ronald Heifetz model) How adaptive leadership differs from traditional leadership The link between complexity, uncertainty, and the need for adaptability Module 2: The Nature of Change and Challenge Technical vs adaptive challenges Why some problems can’t be solved with expertise alone Common leadership traps during crisis or disruption Adaptive work: reframing problems and shifting mindsets Module 3: The Core Principles of Adaptive Leadership Get on the balcony – seeing the bigger picture Regulate distress – maintaining productive tension Maintain disciplined attention – keeping teams focused Give the work back – empowering others to lead Protect voices of leadership from below – enabling diverse input Module 4: Leading Yourself Through Uncertainty Developing personal resilience and emotional agility Navigating ambiguity, setbacks, and pressure Identifying your leadership default style under stress Reflection: What kind of leader does your team need now? Module 5: Engaging Others in Times of Uncertainty Building trust and psychological safety during turbulence Managing resistance to change with curiosity and empathy Tools for courageous conversations and adaptive dialogue Creating shared purpose and distributed leadership in teams Module 6: Adaptive Tools and Techniques Scenario planning and sensemaking Stakeholder mapping in dynamic environments Using inquiry over advocacy Holding space for experimentation and learning Leading with both confidence and humility Module 7: Action Planning and Application Identify one adaptive challenge in your role/team Map your adaptive leadership response Peer coaching conversations Build a 30-day Adaptive Leadership Plan Delivery Style Workshop-style, highly interactive Case studies, breakout discussions, and guided self-reflection Scenario-based practice and small group exercises Option to include pre-work, post-session coaching or check-ins Course Materials Provided Adaptive Leadership workbook Reflection tools and leader self-assessment Conversation guide for adaptive challenges Change resistance diagnostic Personal Leadership Development Plan template Optional Add-ons Executive coaching package 360 feedback or team diagnostic on adaptive capacity Integration with change management or innovation programs Customisation for specific industries (e.g., public sector, healthcare, education, finance)

Using an excavator as a crane is a common practice in certain construction and lifting operations. Using the digger as a crane requires appropriate training and skills However, it’s important to note that excavators are primarily designed for digging and earthmoving, not lifting. Using an Excavator as a Crane involves some inherent risks, and it’s crucial to follow safety guidelines and manufacturer recommendations. To book the NPORS Excavator as a Crane training or test please contact us to schedule your Training Here are some general considerations and steps you might take when using an excavator as a crane: 1. Check Manufacturer Guidelines: Always consult the manufacturer’s guidelines and specifications for the specific excavator model you are using. Manufacturers provide load charts and other essential information to ensure safe operation. 2. Understand Load Capacities: Know the lifting capacities of your excavator at various boom lengths and angles. Exceeding these capacities can lead to instability and accidents. 3. Use Proper Attachments: If your excavator is equipped with a lifting attachment, make sure it is designed and rated for lifting operations. Using inappropriate attachments can compromise safety. 4. Stabilise the Excavator: Ensure that the excavator is on stable ground. Extend the outriggers or stabilisers to provide additional support and prevent tipping. 5. Inspect the Excavator: Regularly inspect the excavator for any signs of wear, damage, or malfunction. Pay particular attention to the boom, hydraulics, and other critical components. 6. Position the Excavator: Position the excavator in a way that allows for a stable lifting operation. Avoid working on slopes or uneven surfaces. 7. Rigging and Lifting Techniques: Use proper rigging techniques, and ensure that the load is properly secured. Lift the load smoothly and avoid sudden movements. 8. Maintain Clear Communication: Establish clear communication between the operator and any ground personnel involved in the lifting operation. Use hand signals or radios to coordinate movements. 9. Avoid Exceeding Reach Limits: Do not exceed the excavator’s reach limits. Lifting loads beyond the recommended reach can lead to instability. 10. Training and Certification: Ensure that operators are properly trained and certified for lifting operations. Holding the NPORS Excavator As A Crane bolt on is essential for lifting operations Operating an excavator as a crane requires specific skills and knowledge. 11. Weather Conditions: Consider weather conditions, especially wind speeds, as they can affect the stability of the excavator during lifting operations. Always prioritise safety when using equipment for tasks it wasn’t originally designed for. If the lifting requirements are frequent or extensive, it may be more appropriate to use a dedicated crane with the necessary capacity and features. Remember, safety is paramount in any construction or lifting operation. Frequently Asked Questions 1. What is Excavator As A Crane Training, and why is it necessary? Excavator As A Crane Training provides individuals with the skills and knowledge required to safely and effectively use excavators for lifting operations. Although excavators are primarily designed for digging and earthmoving, this training ensures operators can perform lifting tasks safely, minimizing risks and accidents on job sites. 2. Who should undergo Excavator As A Crane Training? This training is essential for anyone involved in using excavators for lifting operations, including machine operators, construction workers, and site supervisors. Proper training ensures that individuals understand equipment operation procedures, load capacities, and safety protocols. 3. What topics are covered in Excavator As A Crane Training programs? Training programs cover a range of topics, including: Manufacturer guidelines and load charts Understanding load capacities at various boom lengths and angles Proper use of lifting attachments Excavator stabilization techniques Rigging and lifting techniques Positioning and communication strategies Safety procedures and weather considerations Regular inspection and maintenance of equipment 4. Is Excavator As A Crane Training mandatory in certain industries? While not legally mandated in all areas, many employers in the construction and lifting industries require operators to undergo training as part of their occupational health and safety policies. Compliance with excavator as a crane training requirements helps prevent accidents and ensures regulatory compliance. 5. Where can I find reputable Excavator As A Crane Training courses? Reputable Excavator As A Crane Training Courses are offered by various institutions, including industry associations, equipment manufacturers, and specialized training providers like Vally Plant Training. It is important to choose a program that offers accredited certification and covers relevant industry standards and best practices.

This course aims to give the learner the understanding of what autism is and how it affects a child or adults daily life, we will discuss the typical behaviours and how to offer support. We will identify a range of interventions and approaches improve the quality and daily lives of individuals with these conditions

Maximizing Academic Success: How to Use a Free Assignment Sample in UK
By david hude
This article explores the advantages of using a Free Assignment Sample in UK to improve academic performance. It highlights how New Assignment Help provides valuable resources tailored to UK academic standards, assisting students in creating well-structured, high-quality assignments.
Online Options
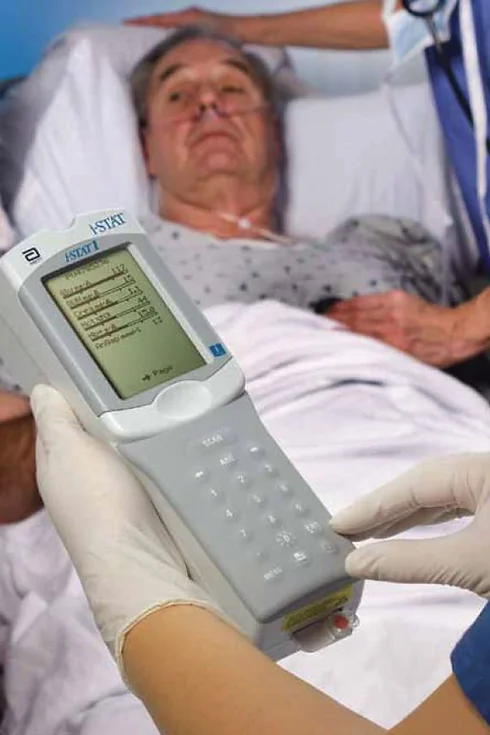
Show all 1444Take your phlebotomy qualifications to the next level ... Nationally Recognised Qualification OCN Accredited - Level 3 (advanced) CPD Accredited Covers specialised and advanced phlebotomy techniques and practices Comprehensively covers Peripheral IV Cannulation Advanced qualification - additional credits Download a digital certificate on completion Basic understanding of English language required LOOKING TO ADD PRACTICAL TRAINING? ALSO AVAILABLE AS SEPARATE CLASSROOM OR VIRTUAL CLASSROOM COURSES: 1: Advanced Phlebotomy Course - Level 4 2: Peripheral IV Cannulation Course - Level 3 COMPLETION OF INTRODUCTION TO PHLEBOTOMY COURSE RECOMMENDED BUT NOT ESSENTIAL
THIS COURSE PACKAGE INCLUDES: 1: INTRODUCTION TO ECG COURSE - RECORDING & BASIC INTERPRETATION (GPT009) 2: ADVANCED ECG COURSE - INTERPRETATION & ANALYSIS (GPT010) Learn how to set up and record a basic ECG trace, followed by advanced analysis and interpretation FAST-TRACK YOUR ECG TRAINING WITH OUR BEGINNER TO ADVANCED TRAINING PACKAGE 20% off - Multi-Course Discount Cover all stages from Level 1 through to Level 4 (FDSc) Cover your theory training online Practical training in Classroom or Virtual Classroom Comprehensive Practise@Home training kits for VC Awards 2 accredited qualifications Dual Accreditations are awarded for all courses (Open College Network and CPD) Covers all steps required to competently set up and perform an ECG trace. Practical sessions include electrode placement on mannequin, running traces and identifying anomalies. Learn beginner to advanced skills and interpretation. Basic understanding of English language required. OPEN TO ALL APPLICANTS About these courses 1: INTRODUCTION TO ECG COURSE - RECORDING AND BASIC INTERPRETATION (GPT009) PART 1 - Theory Allow approx. 5-6 hours PART 2 - Practical Training Attend a classroom location or join us in our virtual classroom * - 3-4 hours ACCREDITED LEVEL 3 QUALIFICATION * Virtual Classroom option includes a free comprehensive Practise@Home ECG training kit. 2: ADVANCED ECG COURSE - INTERPRETATION AND ANALYSIS (GPT010) E-LEARNING - Theory Allow approx. 6-8 hours ACCREDITED LEVEL 4 QUALIFICATION OPTIONAL: GETTING STARTED IN ECG (GPT002) A free starter ECG Course (unassessed) developed to help you understand the basics of ECG recording: 3 modules in total with no Questions! If you are already familiar with ECGs then you may prefer to save time and opt out of this mini-course at booking stage. This "mini-course" is available at no charge. Learning Outcomes GPT009: Understanding different ECG equipment types ECG equipment - set-up and calibration Includes professionalism, consent, IPC and legal requirement Patient preparation How to correctly apply electrodes to limbs and chest Identify artifacts (equipment and patients Identify and recognise routine traces Identify and recognise non-routine traces Identify traces requiring urgent attention Labelling and reporting GPT010: Understand the acceptable variations within the normal ECG of healthy adults. Recognise the expected patterns of an ECG from a healthy child from birth onwards and identify abnormalities. Interpret abnormal ECG patterns in adults. Diagnose arrhythmias as an underlying cause of palpitations and syncope. Exploring sinus rhythm, extrasystoles, paroxysmal tachycardia and the importance of a physical examination. Identifying syncopal episodes attributable to cardiovascular disease as opposed to arrhythmias. Recognise ECG markers for tachycardias, bradycardias, pre-excitation syndromes, bi-fascicular block, and first-degree block with bundle branch block. Differentiate between supraventricular and ventricular extrasystoles and be able to diagnose broad complex tachycardias, ventricular flutter and fibrillation, sick sinus syndrome, and Stokes-Adams attacks. Recognise and identify symptoms associated with the causes of acute or chronic chest pain in patients who present with myocardial infarction (heart attack), pulmonary embolism, significant central pulmonary embolism, pericarditis, aortic dissection, oesophageal rupture, spinal disorders, vertebral collapse, posterior infarction, and angina. Recognise symptoms indicative of conditions such as pulmonary oedema, chest diseases, and pulmonary congestion. After the course GPT009: Safely and competently set up an ECG machine Introduce patients to the ECG test, adhering to compliancy requirements before and after testing Perform an ECG test to national guidelines Understand basic traces and their correlation to cardiac issues Recognise normal and erroneous recordings Recognise recordings that require urgent medical follow-up Complete the recording and label (or record digital copies) as per guidelines GPT010: Appreciate normal and abnormal ECG variations in the context of varying pathologies. Be able to determine whether an arrhythmia has an underlying cause that requires medical intervention. Interpret ECGs as a function of the patient's ongoing cardiac management. Understand and apply the Burce Protocol exercise test in relevant clinical situations. Know how to clinically respond to a patient with chest pain including further investigations required, pain relief, history and examination and echocardiogram. Understand and apply the fundamental principles of arrhythmia management. Understand the primary causes of heart disease and the diagnostic process. Appreciate the importance of the ECG as a diagnostic tool alongside the patient’s history and clinical presentation and recognising its limitations. Course Package Components: PACKAGE - Beginner to Advanced ECG - Virtual Classroom - INTRO - Part 1 online Part 2 Virtual Classroom (AM) + ADVANCED - E-learning

🌿 Guided Minds: A 12-Month Meditation Journey Create calm, clarity & connection—one month at a time. Guided Minds is a year-long meditation programme designed to help you build a sustainable, enriching practice through monthly themes, supportive sessions, and practical tools for real life. Whether you're new to meditation or looking to deepen your experience, this programme will guide you with compassion and clarity. 🔁 Programme Format Weekly Live Sessions (Online & In-Person) Monthly Themes & Challenges Guided Meditations & Practices Supportive Community Access to Session Recordings Join monthly or commit to the full journey—the choice is yours. 🌟 Monthly Themes Overview July: Making Meditation a Healthy Habit Learn how to create a sustainable daily practice using breath, posture and science-backed techniques. ✔️ Relaxation response ✔️ Meditation for clarity & calm ✔️ Core practices: breath, posture, stillness ✔️ In-person Session 5: “Pulling It All Together” August: Meditation & Mindfulness Focus on the profound benefits of meditation: ✔️ Stress relief, heart health, immunity ✔️ Slowing ageing, boosting self-compassion ✔️ 3 Principles: Habituation, Wisdom, Openheartedness ✔️ Diamond Dedication Meditation September: Calming a Wandering Mind Tame your busy mind through simple, powerful practices. ✔️ Focused attention vs. mind-wandering ✔️ Thought loops & rumination ✔️ Colour, mantra & visualisation meditations ✔️ Mindfulness of thought October: Creating a Mindful Life Bring mindfulness into everyday moments. ✔️ Living in the now ✔️ Radical acceptance & surrender ✔️ Senses as anchors: sound, touch, breath ✔️ Showing up fully for life November: Meditation for Stress Relief Practical methods to manage stress & emotional overload. ✔️ Good vs. bad stress ✔️ The ego, fight/flight, and impermanence ✔️ Gratitude & visualisation ✔️ Overcoming obstacles to meditation December: Rest & Reflection Warm the heart and calm the mind before the holidays. ✔️ Body-based awareness ✔️ Reviewing your progress ✔️ Meditations for resilience ✔️ Peaceful practices for winter January: Meditation for Positive Emotions Start the year with joy, love, and purpose. ✔️ Heart-opening meditations ✔️ Gratitude & happiness ✔️ Intention-setting with optional cacao ceremony ✔️ Emotional healing & connection February: Meditation for Well-Being A holistic approach to health from the inside out. ✔️ Four foundations of mindfulness ✔️ Forgiveness (including Huna meditations) ✔️ Body-mind connection ✔️ Compassion and curiosity March: Deeper into Meditation Explore advanced techniques with renewed clarity. ✔️ Insight, wisdom, open-heartedness ✔️ Posture & Nine-Cycle Breathing ✔️ Concentration & mental clarity ✔️ Appreciation for life April: Meditation for Relaxation Recharge your nervous system with rest-focused meditations. ✔️ Body scan & breath awareness ✔️ Guided deep relaxation ✔️ Calming anxiety & overactivity ✔️ Rest as a radical act May: The Art of Living Live with intention and reverence. ✔️ Meditation on impermanence & emptiness ✔️ Self-love & emotional nourishment ✔️ Present moment awareness ✔️ Breath as a life companion June: Meditation on Inner Peace End the year rooted, spacious, and unshakable. ✔️ Letting go of resistance ✔️ Unflappability & mental resilience ✔️ Responsibility & self-awareness ✔️ Lasting inner calm and clarity 💷 Pricing Options Online sessions: £10 each In-person sessions: £15 each Join the Guided Minds Meditation Community for £28/month ✓ Includes all sessions (online & in-person) ✓ Unlimited access to recordings ✓ Bonus practices & group support 🌱 Ready to begin? Each month offers a new opportunity to reset, reflect and grow. Join any time, or commit to the full year and transform your relationship with your mind, body and life.
The UK's first and only Level 4 qualification in Phlebotomy (equivalent to Ireland Level 6) FDSc (Foundation Degree Level) qualification Nationally Recognised certificate Dually accredited: Open College Network and CPD Covers both aspirated and evacuated systems Covers specialised blood collection systems & methods Classroom or Virtual Classroom learning options Comprehensive Training Kit is provided when booking our Virtual Classroom option (yours to keep) Complete your training from beginner to advanced level This course either follows on from our Introduction to Phlebotomy Course or can be combined with our introductory course as part of a course package (see below) Available to candidates who have completed (or are currently enrolled to complete) our Introduction to Phlebotomy Course or have previous phlebotomy practical experience.

Overview This comprehensive course on Attention Management will deepen your understanding on this topic. After successful completion of this course you can acquire the required skills in this sector. This Attention Management comes with accredited certification from CPD, which will enhance your CV and make you worthy in the job market. So enrol in this course today to fast track your career ladder. How will I get my certificate? You may have to take a quiz or a written test online during or after the course. After successfully completing the course, you will be eligible for the certificate. Who is This course for? There is no experience or previous qualifications required for enrolment on this Attention Management. It is available to all students, of all academic backgrounds. Requirements Our Attention Management is fully compatible with PC's, Mac's, Laptop, Tablet and Smartphone devices. This course has been designed to be fully compatible with tablets and smartphones so you can access your course on Wi-Fi, 3G or 4G. There is no time limit for completing this course, it can be studied in your own time at your own pace. Career Path Learning this new skill will help you to advance in your career. It will diversify your job options and help you develop new techniques to keep up with the fast-changing world. This skillset will help you to- Open doors of opportunities Increase your adaptability Keep you relevant Boost confidence And much more! Course Curriculum 2 sections • 13 lectures • 03:21:00 total length •Module One - Getting Started: 00:30:00 •Module Two - Introduction to Attention Management: 00:08:00 •Module Three - Types of Attention: 00:13:00 •Module Four - Strategies for Goal Setting: 00:10:00 •Module Five - Meditation: 00:15:00 •Module Six - Training Your Attention: 00:45:00 •Module Seven - Attention Zones Model: 00:15:00 •Module Eight - SMART Goals: 00:09:00 •Module Nine - Keeping Yourself Focused: 00:13:00 •Module Ten - Procrastination: 00:15:00 •Module Eleven - Prioritizing Your Time: 00:18:00 •Module Twelve - Wrapping Up: 00:10:00 •Attention Management- Activities: 00:00:00

Description: Employees who do not pay attention to their work can waste valuable time and make careless mistakes. Through this course, you will learn the necessary skill that allows managers to connect with their employees on an emotional level and motivate them to focus on their work and how to reach their personal and company goals. This will be a key tool to guide your progress in the days, weeks, months, and years to come. In this course, you will learn the necessary skills, knowledge, and information of attention management. Who is the course for? Professionals or employees who want to learn about attention management People who have an interest in knowing more about attention management Entry Requirement: This course is available to all learners, of all academic backgrounds. Learners should be aged 16 or over to undertake the qualification. Good understanding of English language, numeracy and ICT are required to attend this course. Assessment: At the end of the course, you will be required to sit an online multiple-choice test. Your test will be assessed automatically and immediately so that you will instantly know whether you have been successful. Before sitting for your final exam, you will have the opportunity to test your proficiency with a mock exam. Certification: After you have successfully passed the test, you will be able to obtain an Accredited Certificate of Achievement. You can however also obtain a Course Completion Certificate following the course completion without sitting for the test. Certificates can be obtained either in hard copy at the cost of £39 or in PDF format at the cost of £24. PDF certificate's turnaround time is 24 hours, and for the hardcopy certificate, it is 3-9 working days. Why choose us? Affordable, engaging & high-quality e-learning study materials; Tutorial videos/materials from the industry leading experts; Study in a user-friendly, advanced online learning platform; Efficient exam systems for the assessment and instant result; The UK & internationally recognized accredited qualification; Access to course content on mobile, tablet or desktop from anywhere anytime; The benefit of career advancement opportunities; 24/7 student support via email. Career Path: The Attention Management Diploma Course is a useful qualification to possess, and would be beneficial for the following careers: Businessmen Entrepreneur Director Manager Team Leader Top Executive. Attention Management Diploma Module One - Getting Started 00:30:00 Module Two - Introduction to Attention Management 00:30:00 Module Three - Types of Attention 01:00:00 Module Four - Strategies for Goal Setting 01:00:00 Module Five - Meditation 01:00:00 Module Six - Training Your Attention 01:00:00 Module Seven - Attention Zones Model 01:00:00 Module Eight - SMART Goals 01:00:00 Module Nine - Keeping Yourself Focused 01:00:00 Module Ten - Procrastination 01:00:00 Module Eleven - Prioritizing Your Time 01:00:00 Module Twelve - Wrapping Up 00:30:00 Activities Attention Management- Activities 00:00:00 Mock Exam Mock Exam- Attention Management Diploma 00:20:00 Final Exam Final Exam- Attention Management Diploma 00:20:00 Certificate and Transcript Order Your Certificates and Transcripts 00:00:00

Description Attention Deficit Hyperactivity Disorder Awareness Diploma Attention deficit hyperactivity disorder (ADHD) is a chronic condition that influences an individual's behaviour. People having ADHD seem to be restless, sometimes have trouble focusing, and might be impulsive in action. A person with ADHD shows signs from childhood; it might become more visible when a child's environment changes as they begin schooling. Usually, cases get diagnosed when kids are six to twelve of age. The signs and symptoms related to ADHD typically turn better as one gets older, but in some cases, adults who have been diagnosed with ADHD at an early age gradually suffer further problems, including anxiety and sleep disorders. Many children struggle with certain stages where they become inattentive and restless. ADHD is usually found among children and doesn't necessarily mean they are affected by ADHD. It is advised to raise one's concern to their child's teacher, SENCO, or the GP if one thinks their child's behaviour differs from other children of their age. This particular Attention deficit hyperactivity disorder Awareness Diploma course will provide the knowledge one needs to work or live with an individual suffering from ADHD. The principal aim of this course is to educate students about ADHD by defining and managing the conditions into victorious stories and making them better. ADHD does not discriminate; a person who likely works with it knows it coexists or even is a person who has ADHD. In addition, this Attention deficit hyperactivity disorder Awareness Diploma course aims to highlight the struggles and symptoms faced by those with ADHD. They are unknown to many others in society. Students will also study the techniques to engage with those affected by ADHD. This online Attention deficit hyperactivity disorder Awareness Diploma course would enable people to study at their speed and convenience. Numerous people who have opted for this course used regular work and learned whenever they wanted. One can attend this online course using any device, such as a mobile that has an internet connection, and the person would also have access to web-based support when you need it. The Attention deficit hyperactivity disorder Awareness Diploma course includes a specific syllabus that has been fragmented into simple modules. After completing several tests to test our knowledge, if a person has passed the exams, they will be awarded a diploma certificate to make their resume or portfolio more impressive. What you will learn⯠1: Introduction to ADHD 2: Causes of ADHD 3: Symptoms 4: Evaluation 5: Treatment and Medication 6: Managing Behaviour 7: Diet 8: Therapies 9: Dealing with the challenges of ADHD 10: Organising life around ADHD Course Outcomes After completing the course, you will receive a diploma certificate and an academic transcript from Elearn college. Assessment Each unit concludes with a multiple-choice examination. This exercise will help you recall the major aspects covered in the unit and help you ensure that you have not missed anything important in the unit. The results are readily available, which will help you see your mistakes and look at the topic once again. If the result is satisfactory, it is a green light for you to proceed to the next chapter. Accreditation Elearn College is a registered Ed-tech company under the UK Register of Learning( Ref No:10062668). After completing a course, you will be able to download the certificate and the transcript of the course from the website. For the learners who require a hard copy of the certificate and transcript, we will post it for them for an additional charge.

Personal Development: Attention Management and Memory Increase
By iStudy UK
Concentrate better and Increase the Capacity of your Memory Are you someone who is making careless mistakes during work struggling with memory retention? Or do you just want to improve your focus and your memory capacity? Then this course will be perfect for your needs! If you are one of those people who is struggling with temporary memory loss or you are losing attention during work, this course will be helpful to retain your memory. You will also learn the necessary skills that allow managers to connect with their employees on an emotional level and motivate them to focus on their work and how to reach their personal and company goals. You will be able to increase your productivity and get the best result from your hard work. Most importantly, expanding your memory capacity and improve your day to day activity will be lot easier. This course is ideal for you since you will be able to learn about how memory is gained and how it should be restored for you to enjoy or learn from the past. Course Highlights Personal Development: Attention Management and Memory Increase is an award winning and the best selling course that has been given the CPD Certification & IAO accreditation. It is the most suitable course anyone looking to work in this or relevant sector. It is considered one of the perfect courses in the UK that can help students/learners to get familiar with the topic and gain necessary skills to perform well in this field. We have packed Personal Development: Attention Management and Memory Increase into several modules for teaching you everything you need to become successful in this profession. To provide you ease of access, this course is designed for both part-time and full-time students. You can become accredited in just 20/30 hours and it is also possible to study at your own pace. We have experienced tutors who will help you throughout the comprehensive syllabus of this course and answer all your queries through email. For further clarification, you will be able to recognize your qualification by checking the validity from our dedicated website. Why You Should Choose Personal Development: Attention Management and Memory Increase Lifetime access to the course No hidden fees or exam charges CPD Accredited certification on successful completion Full Tutor support on weekdays (Monday - Friday) Efficient exam system, assessment and instant results Download Printable PDF certificate immediately after completion Obtain the original print copy of your certificate, dispatch the next working day for as little as £9. Improve your chance of gaining professional skills and better earning potential. Who is this Course for? Personal Development: Attention Management and Memory Increase is CPD certified and IAO accredited. This makes it perfect for anyone trying to learn potential professional skills. As there is no experience and qualification required for this course, it is available for all students from any academic backgrounds. Requirements Our Personal Development: Attention Management and Memory Increase is fully compatible with any kind of device. Whether you are using Windows computer, Mac, smartphones or tablets, you will get the same experience while learning. Besides that, you will be able to access the course with any kind of internet connection from anywhere at any time without any kind of limitation. Career Path You will be ready to enter the relevant job market after completing this course. You will be able to gain necessary knowledge and skills required to succeed in this sector. All our Diplomas' are CPD and IAO accredited so you will be able to stand out in the crowd by adding our qualifications to your CV and Resume. Attention Management Module One - Getting Started FREE 00:30:00 Module Two - Introduction to Attention Management FREE 00:30:00 Module Three - Types of Attention 01:00:00 Module Four - Strategies for Goal Setting 01:00:00 Module Five - Meditation 01:00:00 Module Six - Training Your Attention 01:00:00 Module Seven - Attention Zones Model 01:00:00 Module Eight - SMART Goals 01:00:00 Module Nine - Keeping Yourself Focused 01:00:00 Module Ten - Procrastination 01:00:00 Module Eleven - Prioritizing Your Time 01:00:00 Module Twelve - Wrapping Up 00:30:00 Attention Management- Activities 00:00:00 Memory Increasing Techniques How Memory is Gained 01:00:00 How can You Improve Your Memory 01:00:00 A Great Technique for Improving Your Memory 01:00:00 A Healthy Lifestyle for an Improved Memory 01:00:00 Remembering Things by Association 01:00:00 Ways to Improve Your Memory 01:00:00 Conclusion 00:15:00 Mock Exam Final Exam

Educators matching "Attention"
Show all 4Search By Location
- Attention Courses in London
- Attention Courses in Birmingham
- Attention Courses in Glasgow
- Attention Courses in Liverpool
- Attention Courses in Bristol
- Attention Courses in Manchester
- Attention Courses in Sheffield
- Attention Courses in Leeds
- Attention Courses in Edinburgh
- Attention Courses in Leicester
- Attention Courses in Coventry
- Attention Courses in Bradford
- Attention Courses in Cardiff
- Attention Courses in Belfast
- Attention Courses in Nottingham