- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
697 Associate courses in Sheerness delivered Live Online
Database fundamentals training course description This three-day training course helps you prepare for Microsoft Technology Associate Exam 98-364, and build an understanding of these topics: Core Database Concepts, Creating Database Objects, Manipulating Data, Data Storage, and Administering a Database. What will you learn Describe core database concepts. Create database objects. Manipulate data. Describe data storage. Administer a database. Create a relational database consisting of 3 related tables. Database fundamentals training course details Who will benefit: Those working with databases. Prerequisites: None. Duration 3 days Database fundamentals training course contents Understanding core database concepts Flat-type databases, hierarchical databases, relational databases, database fundamentals, relational database concepts, using the SQL Server Management Studio Interface. Data Manipulation Language (DML), Data Definition Language (DDL), using DDL statements. Creating database objects Defining data types, using built-in data types, using exact numeric data types, using approximate numeric data types. Creating and using tables. Creating views. Creating stored procedures, SQL injections. Manipulating data Using Queries to select data, combining conditions, using the BETWEEN clause, using the NOT clause, using the UNION clause, using the EXCEPT and INTERSECT clauses, using the JOIN clause. Using Queries to insert data, Inserting data. Updating data and databases, Using the UPDATE statement. Deleting data, Using the DELETE statement, truncating a table with TRUNCATE TABLE, deleting a table with DROP TABLE, using referential integrity. Understanding data storage Normalising a database, normalization, first normal form, second normal form, third normal form, fourth normal form, fifth normal form. Primary, foreign and composite keys, clustered and non-clustered indexes, creating a non-clustered table. Administering a Database Securing Databases, server-level security, database-level security, Windows security, SQL authentication, database server roles, granting access to a database, fixed database roles, object permissions, managing roles, ownership chains, reviewing a sample security model. Backing up and restoring databases, recovery models, backup devices.

CWSP training course description A hands-on training course concentrating solely on WiFi security with an emphasis on the delegates learning the necessary knowledge and skills to pass the CWSP exam. The course progresses from simple authentication, encryption and key management onto in depth coverage of 802.X and EAP along with many other security solutions such as access control, intrusion prevention and secure roaming. What will you learn Demonstrate the threats to WiFi networks. Secure WiFi networks. Configure: WPA2 RADIUS 802.1x EAP Pass the CWSP exam. CWSP training course details Who will benefit: Technical network staff. Technical security staff. Prerequisites: Certified Wireless Network Associate. Duration 5 days CWSP training course contents WLAN Security overview Standards, security basics, AAA, 802.11 security history. Hands on WLAN connectivity. Legacy 802.11 security Authentication: Open system, shared key. WEP. VPNs. MAC filters. SSID segmentation, SSID cloaking. Hands on Analysing 802.11 frame exchanges, viewing hidden SSIDs. Encryption Basics, AES, TKIP, CCMP, WPA, WPA2. Hands on Decrypting 802.11 data frames. 802.11 layer 2 authentication 802.1X: Supplicant, Authenticator, Authentication server. Credentials. Legacy authentication. EAP, Weak EAP protocols, Strong EAP protocols: EAP -PEAP, EAP-TTLS, EAP-TLS, EAP-FAST. Hands on Analysing 802.1X/EAP frames. 802.11 layer 2 dynamic key generation Robust Security Network. Hands on Authentication and key management. SOHO 802.11 security WPA/WPA2 personal, Preshared Keys, WiFi Protected Setup (WPS). Hands on PSK mapping. WLAN security infrastructure DS, Autonomous APs, WLAN controllers, split MAC, mesh, bridging, location based access control. Resilience. Wireless network management system. RADIUS/LDAP servers, PKI, RBAC. Hands on 802.1X/EAP configuration. RADIUS configuration. 802.11 Fast secure roaming History, RSNA, OKC, Fast BSS transition, 802.11k. Hands on Roaming. Wireless security risks Rogue devices, rogue prevention. Eavesdropping, DOS attacks. Public access and hotspots. Hands on Backtrack. WiFi security auditing Layer 1 audit, layer 2 audit, pen testing. WLAN security auditing tools. WiFi security monitoring Wireless Intrusion Detection and Prevention Systems. Device classification, WIDS/WIPS analysis. Monitoring. 802.11w. Hands on Laptop spectrum analysers. VPNs, remote access, guest access Role of VPNs in 802.11, remote access, hotspots, captive portal. Wireless security policies General policy, functional policy, recommendations.

SC-100T00 Microsoft Cybersecurity Architect
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for experienced cloud security engineers who have taken a previous certification in the security, compliance and identity portfolio. Specifically, students should have advanced experience and knowledge in a wide range of security engineering areas, including identity and access, platform protection, security operations, securing data, and securing applications. They should also have experience with hybrid and cloud implementations. Beginning students should instead take the course SC-900: Microsoft Security, Compliance, and Identity Fundamentals. This is an advanced, expert-level course. Although not required to attend, students are strongly encouraged to have taken and passed another associate level certification in the security, compliance and identity portfolio (such as AZ-500, SC-200 or SC-300) before attending this class. This course prepares students with the expertise to design and evaluate cybersecurity strategies in the following areas: Zero Trust, Governance Risk Compliance (GRC), security operations (SecOps), and data and applications. Students will also learn how to design and architect solutions using zero trust principles and specify security requirements for cloud infrastructure in different service models (SaaS, PaaS, IaaS). Prerequisites Highly recommended to have attended and passed one of the associate level certifications in the security, compliance and identity portfolio (such as AZ-500T00 Microsoft Azure Security Technologies, SC-200T00: Microsoft Security Operations Analyst, or SC-300T00: Microsoft Identity and Access Administrator.) Advanced experience and knowledge in identity and access, platform protection, security operations, securing data and securing applications. Experience with hybrid and cloud implementations. 1 - Introduction to Zero Trust and best practice frameworks Zero Trust initiatives Zero Trust technology pillars part 1 Zero Trust technology pillars part 2 2 - Design solutions that align with the Cloud Adoption Framework (CAF) and Well-Architected Framework (WAF) Define a security strategy Cloud Adoption Framework secure methodology Design security with Azure Landing Zones The Well-Architected Framework security pillar 3 - Design solutions that align with the Microsoft Cybersecurity Reference Architecture (MCRA) and Microsoft cloud security benchmark (MCSB) Design solutions with best practices for capabilities and controls Design solutions with best practices for attack protection 4 - Design a resiliency strategy for common cyberthreats like ransomware Common cyberthreats and attack patterns Support business resiliency Ransomware protection Configurations for secure backup and restore Security updates 5 - Case study: Design solutions that align with security best practices and priorities Case study description Case study answers Conceptual walkthrough Technical walkthrough 6 - Design solutions for regulatory compliance Translate compliance requirements into a security solution Address compliance requirements with Microsoft Purview Address privacy requirements with Microsoft Priva Address security and compliance requirements with Azure policy Evaluate infrastructure compliance with Defender for Cloud 7 - Design solutions for identity and access management Design cloud, hybrid and multicloud access strategies (including Azure AD) Design a solution for external identities Design modern authentication and authorization strategies Align conditional access and Zero Trust Specify requirements to secure Active Directory Domain Services (AD DS) Design a solution to manage secrets, keys, and certificates 8 - Design solutions for securing privileged access The enterprise access model Design identity governance solutions Design a solution to secure tenant administration Design a solution for cloud infrastructure entitlement management (CIEM) Design a solution for privileged access workstations and bastion services 9 - Design solutions for security operations Design security operations capabilities in hybrid and multicloud environments Design centralized logging and auditing Design security information and event management (SIEM) solutions Design solutions for detection and response Design a solution for security orchestration, automation, and response (SOAR) Design security workflows Design threat detection coverage 10 - Case study: Design security operations, identity and compliance capabilities Case study description Case study answers Conceptual walkthrough Technical walkthrough 11 - Design solutions for securing Microsoft 365 Evaluate security posture for collaboration and productivity workloads Design a Microsoft 365 Defender solution Design configurations and operational practices for Microsoft 365 12 - Design solutions for securing applications Design and implement standards to secure application development Evaluate security posture of existing application portfolios Evaluate application threats with threat modeling Design security lifecycle strategy for applications Secure access for workload identities Design a solution for API management and security Design a solution for secure access to applications 13 - Design solutions for securing an organization's data Design a solution for data discovery and classification using Microsoft Purview Design a solution for data protection Design data security for Azure workloads Design security for Azure Storage Design a security solution with Microsoft Defender for SQL and Microsoft Defender for Storage 14 - Case study: Design security solutions for applications and data Case study description Case study answers Conceptual walkthrough Technical walkthrough 15 - Specify requirements for securing SaaS, PaaS, and IaaS services Specify security baselines for SaaS, PaaS, and IaaS services Specify security requirements for web workloads Specify security requirements for containers and container orchestration 16 - Design solutions for security posture management in hybrid and multicloud environments Evaluate security posture by using Microsoft Cloud Security Benchmark Design integrated posture management and workload protection Evaluate security posture by using Microsoft Defender for Cloud Posture evaluation with Microsoft Defender for Cloud secure score Design cloud workload protection with Microsoft Defender for Cloud Integrate hybrid and multicloud environments with Azure Arc Design a solution for external attack surface management 17 - Design solutions for securing server and client endpoints Specify server security requirements Specify requirements for mobile devices and clients Specify internet of things (IoT) and embedded device security requirements Secure operational technology (OT) and industrial control systems (ICS) with Microsoft Defender for IoT Specify security baselines for server and client endpoints Design a solution for secure remote access 18 - Design solutions for network security Design solutions for network segmentation Design solutions for traffic filtering with network security groups Design solutions for network posture management Design solutions for network monitoring 19 - Case study: Design security solutions for infrastructure Case study description Case study answers Conceptual walkthrough Technical walkthrough Additional course details: Nexus Humans SC-100T00 Microsoft Cybersecurity Architect training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the SC-100T00 Microsoft Cybersecurity Architect course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Cisco Administering Cisco Contact Center Enterprise (CCEA)
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for Account and project managers Contact Center Enterprise (CCE) administrators Deployment engineers Technical sales Overview After taking this course, you should be able to: Navigate CCE configuration and scripting tools Configure a dialed number, call type, and media routing domain Build a basic Cisco Intelligent Contact Management (ICM) script Configure agents and skill groups Configure basic Interactive Voice Response (IVR) functionality Implement attributes and precision queues Configure Ring-No-Answer (RONA) using CCE configuration tools Configure and populate an agent team and primary supervisor Improve agent efficiency through finesse enhancements Build and test a basic Voice XML (VXML) application Implement roles, departments, and business hours Run Cisco Unified Intelligence Center (CUIC) reports using the Reporting tool The Administering Cisco Contact Center Enterprise (CCEA) v1.0 course teaches you the contextual information around call flow between components in the Cisco© Unified Contact Center Enterprise (UCCE) solution including intelligent contact routing, call treatment, network-to-desktop Computer Telephony Integration (CTI), and multichannel contact management over an IP infrastructure. You receive hands-on practice using administrative tools to perform routine adds, moves, and changes in an inbound contact center environment. Cisco Unified Contact Center Review Contact Center Basics Components and Architecture Deploying Basic Call Settings Associate Basic Call Settings Explore Media Routing Domains Building a Basic Cisco Unified Contact Center Enterprise Script Introduce Script Editor Use Script Editor Nodes Configuring Basic Agent Functionality Introduce Agent Functionality Configure Agent Desk Settings Configuring Basic Call Treatment and Queuing Explore Media Server and Files Introduce Microapps Implementing Precision Routing Introduce Precision Routing Basics Examine the Migration Path Configuring RONA Support Introduce RONA Functionality Identify RONA Timeout Considerations Configuring Agent Teams and Supervisors Configuring Teams and Supervisors Explore Agent Roles Administering the Cisco Finesse Desktop Administering Cisco Finesse Desktop Introduce Cisco Finesse Administration Implementing Voice XML Applications Introduce VXML Build a Basic Call Studio Project Configuring Roles, Departments, and Business Hours Examine Post-Call Survey Functionality Configure Post-Call Survey Running Unified CC Enterprise Reports with Unified Intelligence Center (IC) Configure Unified CC Enterprise Administrators Configure Departments

Developing women academic leaders: coaching workshop programme for women/identify as women academics higher education aspiring to leadership roles - series 1 2023/24
By Coach Academic
This coaching programme is for aspiring women leaders in higher education, delivered in real time, fully online. Five workshops have been designed to support you in a group environment to work actively towards realising your professional goals, whatever they may look like, focused on leadership at all levels in higher education. HE needs leaders like you - workshops with Coach Academic will help to propel you to becoming one. For all academics who are female/identify as female. During this coaching experience you will explore and learn from: - your values and beliefs, and how they impact on your professional identity and actions - your beliefs about higher education, leadership, and yourself - your strengths and how to harness them for impact - your areas for development, and embracing the actions you choose to address these - your internal and external blockers, and how to manage these - your motivation - why do you want to lead in HE? From these you will be able to build your confidence and your leadership identity, and take concrete steps towards becoming the leader you aspire to be.

Developing women academic leaders: coaching workshop programme for women/identify as women academics higher education aspiring to leadership roles - series 2 2023/24
By Coach Academic
This coaching programme is for aspiring women leaders in higher education, delivered in real time, fully online. Five workshops have been designed to support you in a group environment to work actively towards realising your professional goals, whatever they may look like, focused on leadership at all levels in higher education. HE needs leaders like you - workshops with Coach Academic will help to propel you to becoming one. For all academics who are female/identify as female. During this coaching experience you will explore and learn from: - your values and beliefs, and how they impact on your professional identity and actions - your beliefs about higher education, leadership, and yourself - your strengths and how to harness them for impact - your areas for development, and embracing the actions you choose to address these - your internal and external blockers, and how to manage these - your motivation - why do you want to lead in HE? From these you will be able to build your confidence and your leadership identity, and take concrete steps towards becoming the leader you aspire to be.

Software development training course description This three-day MTA Training course helps you prepare for Microsoft Technology Associate Exam 98-361, and build an understanding of these topics: Core programming, Object-Oriented programming, general software development, web applications, desktop applications, and databases. This course leverages the same content as found in the Microsoft Official Academic Course (MOAC) for this exam. What will you learn Describe core programming. Explain Object Oriented programming. Describe general software development. Describe Web applications. Describe desktop applications. Explain how databases work. Software development training course details Who will benefit: Anyone looking to learn the fundamentals of software. Prerequisites: None. Duration 3 days Software development training course contents Core programming Computer storage and data types How a computer stores programs and the instructions in computer memory, memory stacks and heaps, memory size requirements for the various data storage types, numeric data and textual data. Computer decision structures Various decision structures used in all computer programming languages; If decision structures; multiple decision structures, such as Ifâ¦Else and switch/Select Case; reading flowcharts; decision tables; evaluating expressions. Handling repetition For loops, While loops, Do...While loops and recursion. Understand error handling Structured exception handling. Object-oriented programming Classes Properties, methods, events and constructors; how to create a class; how to use classes in code. Inheritance Inheriting the functionality of a base class into a derived class. Polymorphism Extending the functionality in a class after inheriting from a base class, overriding methods in the derived class. Encapsulation Creating classes that hide their implementation details while still allowing access to the required functionality through the interface, access modifiers. General software development Application life cycle management Phases of application life cycle management, software testing. Interpret application specifications Application specifications, translating them into prototypes, code, select appropriate application type and components. Algorithms and data structures Arrays, stacks, queues, linked lists and sorting algorithms; performance implications of various data structures; choosing the right data structure. Web applications Web page development HTML, CSS, JavaScript. ASP.NET web application development Page life cycle, event model, state management, client-side versus server-side programming. Web hosting Creating virtual directories and websites, deploying web applications, understanding the role of Internet Information Services. Web services Web services that will be consumed by client applications, accessing web services from a client application, SOAP, WSDL. Desktop applications Windows apps UI design guideline categories, characteristics and capabilities of Store Apps, identify gestures. Console-based applications Characteristics and capabilities of console- based applications. Windows Services Characteristics and capabilities of Windows Services. Databases Relational database management systems Characteristics and capabilities of database products, database design, ERDs, normalisation concepts. Database query methods SQL, creating and accessing stored procedures, updating and selecting data. Database connection methods Connecting to various types of data stores, such as flat file; XML file; in-memory object; resource optimisation.

CompTIA A+ Certification (Exams 220-1101 and 220-1102)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is targeted to those seeking A+ Certification and anyone in these roles: IT Support Specialist Helpdesk Technician Field Technician Tier I Support Specialist Desktop Support Specialist Associate Network Engineer Systems Support Technician Junior Systems Administrator Overview At completion of this course, you will be able to: Install and configure end-user devices and software Address connectivity problems Perform basic cybersecurity mitigations Troubleshoot common problems to diagnose and resolve issues Demonstrate basic knowledge of scripting, the cloud, and virtualization CompTIA A+ certified professionals are proven problem solvers. They support today?s core technologies from security to networking to virtualization and more. CompTIA A+ is the industry standard for launching IT careers into today?s digital world. This course, prepares you for the CompTIA A+ Certification exams 220-1101 and 220-1102. Lesson 1: Installing Motherboards and Connectors Topic 1A: Explain Cable Types and Connectors Topic 1B: Install and Configure Motherboards Topic 1C: Explain Legacy Cable Types Lesson 2: Installing System Devices Topic 2A: Install and Configure Power Supplies and Cooling Topic 2B: Select and Install Storage Devices Topic 2C: Install and Configure System Memory Topic 2D: Install and Configure CPUs Lesson 3: Troubleshooting PC Hardware Topic 3A: Apply Troubleshooting Methodology Topic 3B: Configure BIOS/UEFI Topic 3C: Troubleshoot Power and Disk Issues Topic 3D: Troubleshoot System and Display Issues Lesson 4: Comparing Local Networking Hardware Topic 4A: Compare Network Types Topic 4B: Compare Networking Hardware Topic 4C: Explain Network Cable Types Topic 4D: Compare Wireless Networking Types Lesson 5: Configuring Network Addressing and Internet Connections Topic 5A: Compare Internet Connection Types Topic 5B: Use Basic TCP/IP Concepts Topic 5C: Compare Protocols and Ports Topic 5D: Compare Network Configuration Concepts Lesson 6: Supporting Network Services Topic 6A: Summarize Services Provided by Networked Hosts Topic 6B: Compare Internet and Embedded Appliances Topic 6C: Troubleshoot Networks Lesson 7: Summarizing Virtualization and Cloud Concepts Topic 7A: Summarize Client-Side Virtualization Topic 7B: Summarize Cloud Concepts Lesson 8: Supporting Mobile Devices Topic 8A: Set Up Mobile Devices and Peripherals Topic 8B: Configure Mobile Device Apps Topic 8C: Install and Configure Laptop Hardware Topic 8D: Troubleshoot Mobile Device Issues Lesson 9: Supporting Print Devices Topic 9A: Deploy Printer and Multifunction Devices Topic 9B: Replace Print Device Consumables Topic 9C: Troubleshoot Print Device Issues Lesson 10: Configuring Windows Topic 10A: Configure Windows User Settings Topic 10B: Configure Windows System Settings Lesson 11: Managing Windows Topic 11A: Use Management Consoles Topic 11B: Use Performance and Troubleshooting Tools Topic 11C: Use Command-line Tools Lesson 12: Identifying OS Types and Features Topic 12A: Explain OS Types Topic 12B: Compare Windows Editions Lesson 13: Supporting Windows Topic 13A: Perform OS Installations and Upgrades Topic 13B: Install and Configure Applications Topic 13C: Troubleshoot Windows OS Problems Lesson 14: Managing Windows Networking Topic 14A: Manage Windows Networking Topic 14B: Troubleshoot Windows Networking Topic 14C: Configure Windows Security Settings Topic 14D: Manage Windows Shares Lesson 15: Managing Linux and macOS Topic 15A: Identify Features of Linux Topic 15B: Identify Features of macOS Lesson 16: Configuring SOHO Network Security Topic 16A: Explain Attacks, Threats, and Vulnerabilities Topic 16B: Compare Wireless Security Protocols Topic 16C: Configure SOHO Router Security Topic 16D: Summarize Security Measures Lesson 17: Managing Security Settings Topic 17A: Configure Workstation Security Topic 17B: Configure Browser Security Topic 17C: Troubleshoot Workstation Security Issues Lesson 18: Supporting Mobile Software Topic 18A: Configure Mobile OS Security Topic 18B: Troubleshoot Mobile OS and App Software Topic 18C: Troubleshoot Mobile OS and App Security Lesson 19: Using Support and Scripting Tools Topic 19A: Use Remote Access Technologies Topic 19B: Implement Backup and Recovery Topic 19C: Explain Data Handling Best Practices Topic 19D: Identify Basics of Scripting Lesson 20: Implementing Operational Procedures Topic 20A: Implement Best Practice Documentation Topic 20B: Use Proper Communication Techniques Topic 20C: Use Common Safety and Environmental Procedures

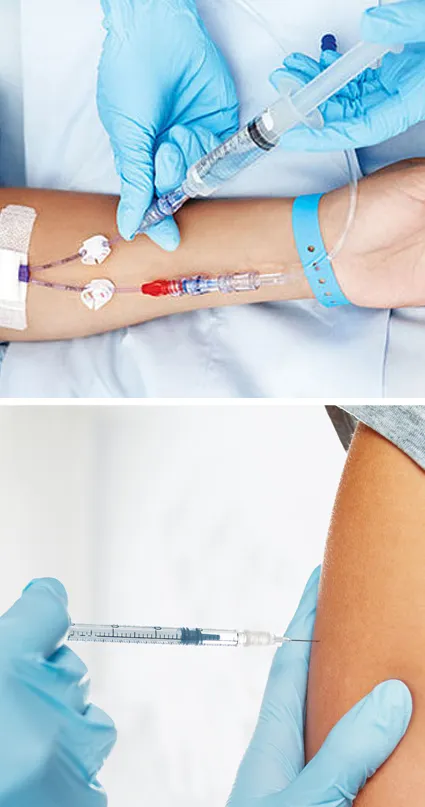
THIS COURSE PACKAGE INCLUDES: 1: PERIPHERAL I.V. CANNULATION - IV THERAPIES COURSE (GPT008) 2: VACCINATION / INJECTION COURSE (GPT601) Learn how to administer injectables and intravenous therapies ... FAST-TRACK YOUR AESTHETICS TRAINING WITH OUR COMPLETE TRAINING PACKAGE 20% Multi-Course Discount Cover all stages from Level 1 through to Level 4 (FDSc) Cover your theory training online Complete your advanced practical training in 1 day Practical training in Classroom or Virtual Classroom Comprehensive Practise@Home training kits for VC Awards 2 accredited qualifications Dual Accreditations for all courses Covers all steps required to safely perform injectables Covers all steps required to safely perform IV therapies Practise IV on artificial arm with fake blood Practise injection techniques on realistic injection pads Learn beginner to advanced skills and techniques Basic understanding of English language required OPEN TO ALL APPLICANTS
HTML5 development training course description This three-day MTA Training course helps you prepare for Microsoft Technology Associate Exam 98-375, and build an understanding of these topics: Manage the Application Life Cycle, Build the User Interface by Using HTML5, Format the User Interface by Using CSS, Code by Using JavaScript. This course leverages the same content as found in the Microsoft Official Academic Course (MOAC) for this exam. What will you learn Manage the Application Life Cycle. Build the User Interface by Using HTML5. Format the User Interface by Using CSS. Code by Using JavaScript. HTML5 development training course details Who will benefit: Anyone working with HTML5. Prerequisites: None. Duration 3 days HTML5 development training course contents Managing the Application Life Cycle Platform fundamentals Packaging and the runtime environment: app package, app container, credentials/permission sets, host process, leverage existing HTML5 skills and content for slate/tablet applications. Manage the state of an application Manage session state, app state and persist state information; understand states of an application; understand the differences between local and session storage. Debug and test a HTML5 touch-enabled application Touch gestures; gestures you test on a device. HTML5 UI: Text, Graphics, and Media HTML5 tags for text content and graphics. When, why and how to use Canvas; when, why and how to use scalable vector graphics (SVG). HTML5 tags to play media. Video and audio tags. HTML5 UI: Organization, Input, and Validation HTML5 tags to organise content and forms Tables, lists, sections; semantic HTML. HTML5 tags for input and validation CSS Essentials: Content Flow, Positioning, styling Core CSS concepts Separate presentation from content (create content with HTML and style content with CSS); manage content flow (inline versus block flow); manage positioning of individual elements( float versus absolute positioning); manage content overflow (scrolling, visible and hidden); basic CSS styling. CSS Essentials: Layouts Arrange UI content by using CSS Use flexible box and grid layouts to establish content alignment, direction and orientation; proportional scaling and use of "free scale" for elements within a flexible box or grid; order and arrange content; concepts for using flex box for simple layouts and grid for complex layouts; grid content properties for rows and columns; use application templates. Managing Text Flow by Using CSS Regions and using regions to flow text content between multiple sections (content source, content container, dynamic flow, flow-into, flow-from, msRegionUpdate, msRegionOverflow, msGetRegionContent); columns and hyphenation and using these CSS settings to optimise the readability of text; use "positioned floats" to create text flow around a floating object Managing the Graphical Interface by Using CSS Graphics effects (rounded edges, shadows, transparency, background gradients, typography and Web Open Font Format); 2-D 3-D transformations (translate, scale, rotate, skew and 3-D perspective transitions and animations); SVG filter effects; Canvas. JavaScript and coding essentials Manage and maintain JavaScript, Create and use functions; jQuery and other third-party libraries. Update the UI by using JavaScript Locate/access elements; listen and respond to events; show and hide elements; update the content of elements. Animations, Graphics, and Accessing Data Code animations with JavaScript animation; manipulate the canvas; work with images, shapes and other graphics. Access data access by using JavaScript Send and receive data; transmit complex objects and parsing; load and save files; App Cache; datatypes; forms; cookies; localStorage JavaScript coding for Touch Interface, Device and Operating System Resources, and More Respond to the touch interface, Gestures, how to capture and respond to gestures, Code additional HTML5 APIs, GeoLocation, Web Workers, WebSocket; File API, Access device and operating system resources, In- memory resources, such as contact lists and calendar; hardware capabilities, such as GPS, accelerometer and camera.
