- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
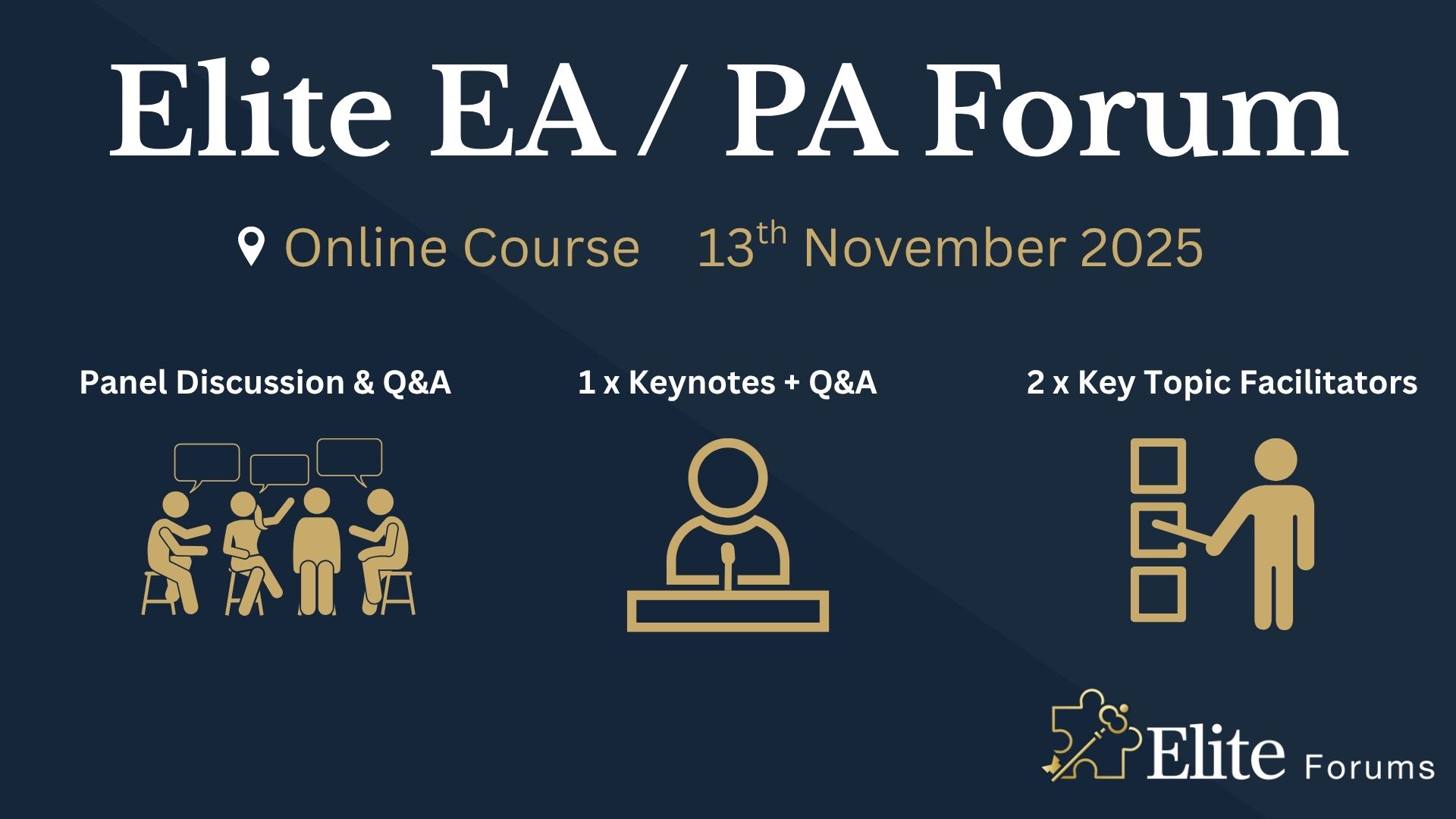
Elite EA PA Forum 🇬🇧
By Elite Forums UK
Elite EA/PA Forum We are delighted to announce the Elite EA/PA Forum for the UK & Ireland will be on the 13th November 2025. Our workshop aims to: Enhance your influence and impact by mastering assertive communication, negotiation, and self-advocacy skills. Stay composed and solution-focused in high-pressure situations with practical tools for crisis management and clear decision-making. Embrace evolving technology by understanding how AI and automation can streamline your role and boost efficiency. Future-proof your career by building strategic value, resilience, and adaptability in an ever-changing professional landscape. Keynote Address with Q&A from the audience: What to expect from Sam's Keynote: With over 30 years supporting leaders at the highest levels, Sam Cohen brings a wealth of insight, experience, and stories (the kind she can share) to the stage. From 18 years serving within The Royal Household - including as Deputy Private Secretary and Press Secretary to Her late Majesty Queen Elizabeth II - to working with The Duke and Duchess of Sussex, running the Prime Minister’s Office at Downing Street, and serving as Chief of Staff to the global CEO of Rio Tinto, Sam’s career is a masterclass in discretion, diplomacy, and delivering at the top. In this exclusive keynote, Beyond the Role, Sam will explore how Executive Assistants don’t just support leaders - they shape leadership, drive strategy, and build legacy from behind the scenes. Join us for this rare opportunity to hear from someone who’s been at the epicentre of power - and bring your questions! The keynote will include a live Q&A, where you can ask Sam about her remarkable career, leadership insights, and how to truly excel in high-performance environments. (Don’t ask her what the Queen kept in her handbag - she’s not telling.) Sam Cohen Career Bio: Sam Cohen has spent the last 30 years working to support leaders in the public and private sectors. Sam spent 18 years serving The Royal Household, as Deputy Private Secretary to Her late Majesty Queen Elizabeth II and Press Secretary to The Queen. Sam also served as Private Secretary to The Duke and Duchess of Sussex. Following this time, Sam worked as Director of the Prime Minister’s Office at Downing Street under Boris Johnson and, most recently, was Chief of Staff to the global CEO at Rio Tinto. Source: ABC News - YouTube Channel. Facilitator - AM: Monika Turner The Confident Assistant - Speak Up, Go After What You Want & Create The Future You Deserve: Develop practical strategies to negotiate workload, boundaries, and career growth with confidence. Learn assertive communication techniques to handle challenging conversations effectively. Build self-advocacy skills to articulate your value and influence outcomes in the workplace. Monika Turner Career Bio: Monika Anna Turner is an ICF-certified Leadership and Executive coach with over seven years of experience helping professionals unlock their confidence, elevate their voice, and lead with authenticity. Before stepping into coaching, she built a successful career as a Personal Assistant, Executive Assistant, and ultimately Chief Of Staff —giving her a deep understanding of the unique challenges and strengths of support roles. Originally from Poland, Monika knows firsthand what it’s like to question your voice and your value—especially in a second language. Her journey from self-doubt to self-assurance informs everything she does today. Through her coaching, she empowers assistants and leaders alike to move beyond fear, speak up and create fulfilling careers they’re proud of. Panel Fabiana Goncalves Executive Assistant to Global VP PerfectDraft & PerfectDraft Commercial Director An accomplished C-Suite Executive & Personal Assistant, I bring over a decade of experience supporting top-level leadership—including CEOs, Founders, and Executive Teams—across multinational and national organizations. I specialize in executive support that goes far beyond calendar management, contributing as a strategic partner in decision-making, operations, and leadership effectiveness. Known for my discretion, diplomacy, and operational precision, I help executives stay focused on what matters most—by anticipating needs, managing complexity, and driving efficiency in both corporate and personal domains. I bring a strategic lens to every task, balancing immediate priorities with long-term objectives. With a proactive mindset, sharp judgment, and strong communication skills, I serve as a trusted advisor and problem-solver in fast-paced, high-stakes environments. Rebecca Polson Executive Support Manager to the Chief Executive An award-winning Executive Assistant with over 10 years’ experience across the higher education, charity, private, and public sectors. Currently Executive Support Manager to the Chief Executive at Alzheimer’s Research UK, she provides high-level support in the fast-paced, mission-driven environment of the largest dementia research charity in the UK. Her previous roles include supporting senior leaders at the Natural History Museum, the Incorporated Society of Musicians, and the Royal College of Music. She brings expertise in executive support, governance, stakeholder engagement, and complex diary and project management. Named PA of the Year in 2023 and a finalist in the SecsintheCity PA of the Year Awards, she is known for her professionalism, discretion, and ability to stay ahead of the needs of the people and organisations she supports. Ola Boddington Senior Executive Assistant As a seasoned Executive Assistant, she has honed her skills in management and project planning over the years. She has worked with various organisations, including Zoa, Signal AI, and ConsenSys, where she provided high-level administrative support to senior executives. Her expertise lies in managing complex schedules, coordinating travel arrangements, and ensuring seamless communication among team members. She is also proficient in using various software tools to streamline workflows and enhance productivity. She is passionate about delivering exceptional service and contributing to the success of the teams she works with. Claudine Martin Senior Executive Assistant Claudine is a highly skilled Senior Executive Assistant, currently supporting the Head of BNY Pershing EMEA. With a distinguished career spanning nearly 17 years in the British Army, Claudine retired in 2023 at the rank of Staff Sergeant, bringing a wealth of experience in high-pressure environments and strategic operations to her current role. Throughout her military career, Claudine specialised in Human Resources, and served as the Personal Assistant to the Army Director of Engagement and Communication at the Ministry of Defence. In this capacity, she played a pivotal role in the planning and execution of significant events and initiatives, showcasing her exceptional organisational skills and attention to detail. Her dedication and professionalism were recognised when she was awarded PA of the Year in 2019 by PA Life. An advocate for the Executive Assistant profession, Claudine is also a sought-after public speaker. She regularly shares her insights at industry events, including the PA Show, and serves as an advisory board member, contributing to the ongoing development and recognition of the profession. Claudine is passionate about empowering others and has previously mentored young people through the Diana Award, a programme established in honour of Princess Diana to support disadvantaged youth. Additionally, she has participated in Fast Forward 15, a mentoring initiative aimed at women aspiring to build careers in events, hospitality, or related industries. With her extensive experience, dedication to excellence, and commitment to mentorship, Claudine continues to make a significant impact in her field and inspire the next generation of leaders. She proudly represented the UK at the Invictus Games 2023, showcasing her unwavering determination and unwavering spirit. In her spare time, Claudine enjoys park run and writing poems. The Importance of Becoming a Strategic Advisor Learn how to shift from reactive to proactive. Develop the mindset and behaviours of a strategic advisor. Understand how to add value beyond your job description. Facilitator - PM: Justin Kabbani AI Is Not Here to Replace You. It's Here to Upgrade You. We'll explore Justin's proven 3P framework: Priming – How to set up AI like a strategic advisor by feeding it context, tone and mindset Prompting – How to craft clear, structured instructions to get consistently great results Producing – How to turn AI outputs into high-leverage work that makes you stand out Your session outcomes: Real examples from admin professionals already using AI to elevate their work Prompts you can copy, adapt, and test live Interactive exercises to build confidence fast A practical challenge to implement right after the session If you’ve been overwhelmed by AI, or underwhelmed by its impact, this session will change that. You'll leave with tools you can use today, and a mindset you’ll carry forward for the rest of your career. Justin Kabbani Career Bio: Justin Kabbani is one of Australia’s most in-demand AI trainers and keynote speakers, known for making AI feel simple, powerful, and immediately useful. He’s worked with brands like Uber, Treasury Wine Estates, and Udemy, helping their teams embed AI into daily workflows, strategic planning, and executive communication. Over the past two years, Justin has trained more than 2,000 professionals across Australia and beyond, consistently earning feedback like “mind-blowing,” and “game-changing”. His signature Prime, Prompt, Produce framework has transformed how business leaders, executive assistants, marketers, and teams think, work, and communicate with AI, without needing to be “tech people.” Justin believes AI isn’t here to replace people. It’s here to take the robotic work off our plate, so we can focus on what humans do best. LinkedIn: https://www.linkedin.com/in/justinkabbani/ Website: https://justinkabbani.com/ Speed Connections Networking Session Join us for Speed Connections, a lively 30-minute networking session designed to foster meaningful connections in a fun, fast-paced environment. Every 10 minutes, attendees will be placed into new breakout rooms with small groups, giving everyone the chance to meet a diverse range of peers. Each breakout session will feature engaging prompts to spark conversations and make networking enjoyable and memorable! Who will attend this event? Executive Assistant (EA) Personal Assistant (PA) Virtual Assistant (VA) Legal Secretary Legal Executive Assistant Administrative Assistant Office Manager Health Care Office Manager Chief of Staff Additional roles may be relevant depending on role responsibilities along with development opportunities. This workshop is open to females, male including trans women/males and non-binary professionals. Group Rate Discounts To discuss our group rates in more detail, please email support@elite-forums.com and provide the following: Group Number (How many would like to attend) Event Date (If numerous dates, please advise if we are splitting attendees across multiple dates) Attendee Contact details (Or request our Group Rate Document. Complete and return - we'll sort the rest.) Group discounts are on request - see below group rate discount brackets: 🧩 You just need one piece to come together - to unlock your Elite Potential. 🔑 Media outlets/organisations will not be permitted to attend this event.
AML Training For Law Firms Not In Scope Course
By DG Legal
In an ever-evolving legal landscape, being a firm outside of the mandatory AML scope doesn't mean being out of the compliance conversation. This course is your guide to proactively managing risks, staying compliant and ensuring your firm's resilience. Don't miss this opportunity to navigate the unique challenges faced by out-of-scope AML law firms. The course will cover: AML regulations Why are some firms (or departments) in or out of scope? MLROs AML basics CDD (ID elements) Responsibility of doing CDD Source of Funds / Source of Wealth Ongoing monitoring Reporting to the MLRO Target Audience The online course is suitable for staff of all levels, from support staff to senior partners of firms outside of the regulated sector. Resources Comprehensive and up to date course notes will be provided to all delegates which may be useful for ongoing reference or cascade training. Please note a recording of the course will not be made available. Speaker Helen Torresi, Consultant, DG Legal Helen is a qualified solicitor with a diverse professional background spanning leadership roles in both the legal and tech/corporate sectors. Throughout her career, she has held key positions such as COLP, HOLP, MLCO, MLRO and DPO for law firms and various regulated businesses and services. Helen’s specialised areas encompass AML, complaint and firm negligence handling, DPA compliance, file review and auditing, law management, and operational effectiveness in law firms, particularly in conveyancing (CQS).

This Level 4 course aims to equip professionals with the knowledge about the skills and practical behaviours which are required for them to step into a leadership/management role. The demand for management roles is expected to grow in the coming years. This is due to a number of factors, including: The ageing population, which is leading to a shortage of skilled workers. The increasing complexity of businesses requires more managers to oversee operations. The growing importance of technology is creating new opportunities for managers to lead and innovate.

25th September Camille Burns #Agent121. Looking for: MG, YA inc YA/CROSSOVER ROMANCE, and ADULT FICTION; NON-FICTION FOR ALL AGES.
5.0(3)By I Am In Print
LOOKING FOR: MIDDLE GRADE, YOUNG ADULT & ADULT FICTION AS WELL AS NON-FICTION FOR ALL AGES Prior to joining DKW in 2023, Camille worked at David Higham Associates as Agent’s Assistant to Jane Gregory and in the Children’s Translation Rights team. She has also worked in editorial for an academic publisher, in rights and marketing for an audiobook publisher and as an intern at Felicity Bryan Literary Agency. Camille loves engaging with narratives on a structural level in order to draw out their best qualities. Camille has an MSc in Publishing from Edinburgh Napier University and an MA in English Literature from the University of Edinburgh. She was Secretary of the Association of Authors’ Agents, as well as Co-Chair for the AAA’s Bridge Committee for early career agents and assistants, from late 2021 to early 2024. She also previously volunteered at the Story Museum in Oxford. Camille is looking to grow her list with a particular focus on middle grade, young adult and adult/crossover fiction, as well as non-fiction for all ages. Books that she has loved and that speak to her taste include Lockwood and Co by Jonathan Stroud (MG), I’ll Give You The Sun by Jandy Nelson (YA), Fourth Wing by Rebecca Yarros (crossover) and Every Summer After by Carley Fortune (adult). For more information, please visit Camille's page on the Diamond Kahn Woods Literary Agency website. Camille would like you to submit a covering letter, 1 - 2 page synopsis and the first 5,000 words of your manuscript in a single Word document. (In addition to the paid sessions, Camille is kindly offering one free session for low income/underrepresented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Wednesday 17th September 2025

Cisco Implementing and Administering Cisco Solutions v2.0 (CCNA)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for anyone seeking CCNA certification. The course also provides foundational knowledge for all support technicians involved in the basic installation, operation, and verification of Cisco networks. The job roles best suited to the material in this course are: Entry-level network engineer Network administrator Network support technician Help desk technician Overview This course will help you: Learn the knowledge and skills to install, configure, and operate a small- to medium-sized network Gain a foundation in the essentials of networking, security, and automation Earn 30 CE credits toward recertification The Implementing and Administering Cisco Solutions (CCNA) v2.0 course gives you a broad range of fundamental knowledge for all IT careers. Through a combination of lecture, hands-on labs, and self-study, you will learn how to install, operate, configure, and verify basic IPv4 and IPv6 networks. The course covers configuring network components such as switches, routers, and wireless LAN controllers; managing network devices; and identifying basic security threats. The course also gives you a foundation in network programmability, automation, and software-defined networking. This course helps you prepare to take the 200-301 Cisco© Certified Network Associate (CCNA©) exam. By passing this one exam, you earn the CCNA certification. This course also earns you 30 Continuing Education (CE) credits towards recertification. Course Outline Exploring the Functions of Networking ? Lecture Introducing the Host-to-Host Communications Model ? Lecture Operating Cisco IOS Software ? Lecture Introducing LANs ? Lecture Exploring the TCP/IP Link Layer ? Lecture Starting a Switch ? Lecture Introducing the TCP/IP Internet Layer, IPv4 Addressing, and Subnets ? Lecture Explaining the TCP/IP Transport Layer and Application Layer ? Lecture Exploring the Functions of Routing ? Lecture Configuring a Cisco Router ? Lecture Exploring the Packet Delivery Process ? Lecture Troubleshooting a Simple Network ? Lecture Introducing Basic IPv6 ? Lecture Configuring Static Routing ? Lecture Implementing VLANs and Trunks ? Lecture Routing Between VLANs ? Lecture Introducing OSPF ? Lecture Building Redundant Switched Topologies ? Self-study Improving Redundant Switched Topologies with EtherChannel ? Lecture Exploring Layer 3 Redundancy ? Self-study Introducing WAN Technologies ? Self-study Explaining Basics of ACL ? Lecture Enabling Internet Connectivity ? Lecture Introducing QoS ? Self-study Explaining Wireless Fundamentals ? Self-study Introducing Architectures and Virtualization ? Self-study Explaining the Evolution of Intelligent Networks ? Lecture Introducing System Monitoring ? Lecture Managing Cisco Devices ? Lecture Examining the Security Threat Landscape ? Self-study Additional course details: Nexus Humans Cisco Implementing and Administering Cisco Solutions v2.0 (CCNA) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Cisco Implementing and Administering Cisco Solutions v2.0 (CCNA) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Food Safety, Education and Social Care Training Courses What You Need To Know About Food Allergies CPD Accredited, Interactive Short Course 2 hr session Do you serve food, or have people with known allergies in your school or on your team? In this webinar we will explain what food allergies are, and why it is vital for you to understand, for the health and safety, and indeed life, of the person involved Course Contents: What is a food allergy The 14 Allergens The Immune System Consequences of Food Allergies The importance of good food hygiene Benefits of this Short Course: More than 20% of the population in industrialized countries suffer from food intolerance or food allergy About two million people live with a diagnosed food allergy in the UK, and 32 million in the US 600,000 people in the UK have coeliac disease This course will teach you the importance of ensuring food is safe to eat for all, without causing significant pain or even death

Level 5 Learning & Skills Teacher
By Cavity Dental Training
Unlock Your Potential as a Learning & Skills Teacher with Our Level 5 Course This qualification is for those looking to teach in Further Education and Skills Sector (FES), usually in settings where students are aged 16 and above whether that is in FE colleges (whether general or specialist), independent training providers (ITPs), Adult Community Learning (ACL) providers or offender learning. In their daily work, A learning & Skills teacher interacts with other teachers and FES professionals and students of different ages, abilities, backgrounds, and ambitions. Also interacting with employers and stakeholders. Teachers who are specialists in a particular technical or vocational subject, sector or occupation will typically maintain close working relationships with others working in their industry/sector and keep their own knowledge and skills up to date. Learn about the Cavity Training Learning & Skills Teacher Course This qualification allows candidates to learn, develop and practice the skills required to prepare each of their students for progression to/or within employment or to further study. To deliver to a diverse group of students, including those with special educational needs. Fees This course can be completed as an government funded apprenticeship, through Cavity Training, or as a privately funded course for £4500. You can either pay as a lump sum or alternatively, you can split into 12 instalments. Entry requirements Apprentices without level 2 English and maths will need to achieve this level prior to taking the End-Point Assessment. Structure To achieve the qualification the learner must compile a portfolio of evidence during the on-program period of the apprenticeship, which will typically contain 15 discrete pieces of evidence. Two pieces of evidence should be records of observations of the apprentice teaching, with the accompanying lesson plan, and support materials for the observed lesson. The lesson observations must have been carried out by an experienced teaching practitioner in the capacity of a manager. With a final professional discussion. Knowledge Our course is delivered via live training webinars with specialist tutors. Skills and Behaviours You will be appointed a designated Learning & Skills Tutor, who will coach you through your qualification and complete regular assessments with you to support you to complete your qualification. You will have weekly contact from your Tutor. How we compare with our competitors? Don't just take our word for it, here is what our staff think Bridget I did my course years ago. It was classroom based one night per week. I think I would prefer to be more ‘hands on’ like it is now. Cavity really are a great company to work for. I truly believe that there expertise will ensure the next generation are amazing! Gina I did mine over an apprenticeship but the company my employer used wasn’t great and I didn’t get much support. Although I passed I can only imagine the length that Cavity have gone to to ensure that the students feel supported. As an employee, its super! Enquire Today

Complete C programming training course description A hands-on introduction to programming in the ANSI C programming language. The course initially moves at a fast pace in order to spend as much time as possible on the subject of pointers - the area which cause the most bugs in C programs. What will you learn Write ANSI C programs Use the C libraries Debug C programs Examine existing code and determine its function. Complete C programming training course details Who will benefit: Programmers wishing to learn C. Programmers wishing to learn C++ or Java. Prerequisites: None, although experience in another high level language would be useful. Duration 5 days Complete C programming training course contents Getting started The compilation process, comments, main(), statement blocks, printf(). C data types and operators char, int, float and double, qualifiers, arithmetic and assignment operators, precedence, Associativity. Basic I/O C libraries, stdin and stdout, getchar(), putchar(), printf() formatting. Flow control if else, dangling elses, else if, while and for loops. switch statements, the null statement, break, continue and gotos. Functions Function calls, arguments and return types, function declarations (prototypes), function definitions, scope of variables. The preprocessor Preprocessor actions, macros, #include. Libraries and their relationship with header files. Conditional compilation. More data types and operators Logical, bitwise and other operators, type conversion, casting, typedefs and access modifiers. Arrays Declaring and handling arrays, common gotchas, multidimensional arrays. Pointers What are pointers? Why they are so important, declaring and using pointers,The three uses of the *,pointer example - scanf, pointers as arguments. More pointers Golden rules of pointers and arrays, pointers to arrays, pointer arithmetic, arrays of pointers, multiple indirection. Character/string manipulation Arrays of characters, string definition, working with strings, String library. Program arguments argc and argv, example uses,char *argv[] versus char ** argv. Program structure and storage classes Globals (externals), multi source programs, the look of a C program. Structures Declaration, the . and - operators, unions and bitfields. Library functions File handling, fopen and fclose, reading from and writing to files, fseek().calloc() and malloc()

Network design training course description This course provides you with the knowledge needed to perform the design of a network infrastructure that supports desired network solutions to achieve effective performance, scalability, and availability. We recognise that the role of design does not normally require hands on skills but hands on sessions are used to reinforce the theory not to teach configuration or troubleshooting. What will you learn Create HA enterprise network designs. Develop optimum Layer 3 designs. Design effective modern WAN and data center networks. Develop effective migration approaches to IPv6. Create effective network security designs. Network design training course details Who will benefit: Anyone involved with network design. Prerequisites: TCP/IP Foundation for engineers Duration 5 days Network design training course contents Part I Reliable, resilient enterprise L2/3 network designOptimal Enterprise Campus Design:Enterprise campus design principles, hierarchy, modularity, flexibility, resiliency.EIGRP design:EIGRP Design, Should you use EIGRP?OSPF design: OSPF scalability designs, OSPF area design, OSPF Full-Mesh Design, OSPF Hub-and-Spoke Design, OSPF convergence design and optimization techniques. IS-IS Design:The protocol, IS-IS hierarchical architecture, IS-IS vs OSPF, IS-IS Deep Dive, IS-IS Design Considerations. BGP design:BGP overview, Designing Scalable iBGP Networks, BGP Route Reflector Design, Enhancing the Design of BGP Policies with BGP Communities, Case Study: Designing Enterprise wide BGP Policies Using BGP Communities, BGP Load-Sharing Design.Part II Enterprise IPv6 Design ConsiderationsIPv6 Design Considerations in the Enterprise: IPv6 Deployment and Design Considerations, Considerations for Migration to IPv6 Design, IPv6 Transition Mechanisms, Final Thoughts on IPv6 Transition Mechanisms. Challenges of the Transition to IPv6: IPv6 Services, Link Layer Security Considerations. Part III Modern Enterprise Wide-Area Networks DesignService Provider-Managed VPNs:Choosing Your WAN Connection, Layer 3 MPLS VPNs, Case Study: MPLS VPN Routing Propagation, Layer 2 MPLS VPN Services. Enterprise-Managed WANs: Enterprise-Managed VPNs, GRE, Multipoint GRE, Point-to-Point and Multipoint GRE, IPsec, IPsec and dynamic VTI, DMVPN, Case Study: EIGRP DMVPN, DMVPN and Redundancy, Case Study: MPLS/VPN over GRE/DMVPN, SSL VPN. Enterprise WAN Resiliency Design: WAN Remote-Site Overview, MPLS L3 WAN Design Models, Common L2 WAN Design Models, Common VPN WAN Design Models, 3G/4G VPN Design Models, Remote Site Using Local Internet, Remote-Site LAN, Case Study: Redundancy and Connectivity, NGWAN, SDWAN, and IWAN Solution Overview, IWAN Design Overview, Enterprise WAN and Access Management. Part IV Enterprise Data Center DesignsMultitier Data Center Designs: Case Study: Small Data Centers (Connecting Servers to an Enterprise LAN), Case Study: Two-Tier Data Center Network Architecture, Case Study: Three-Tier Data Center Network Architecture.Trends and Techniques to Design Modern Data Centers: The Need for a New Network Architecture, Limitations of Current Networking Technology, Modern Data Center Design Techniques and Architectures, Multitenant Data Center. SDN:SDN characteristics, How SDN addresses current Networking Limitations, SDN Architecture Components, SDN Network Virtualization overlays. Data Center Connections:Data Center Traffic Flows, The Need for DCI, IP Address Mobility, Case Study: Dark Fiber DCI, Pseudowire DCI. Part V Design QoS for Optimized User ExperienceQoS Overview:QoS Overview, IntServ versus DiffServ, Classification and Marking, Policers and Shapers, Policing Tools: Single-Rate Three-Color Marker, Policing Tools: TwoRate Three-Color Marker, Queuing Tools, Dropping Tools. QoS design principles and best practices: QoS overview, classification and marking design principles, policing and remarking design principles, queuing design principles, dropping design principles, Per-Hop behavior queue design principles, RFC 4594 QoS Recommendation, QoS Strategy Models. Campus QoS, WAN QoS, Data Center QoS.MPLS VPN QoS Design: The Need for QoS in MPLS VPN, Layer 2 Private WAN QoS Administration, Fully Meshed MPLS VPN QoS Administration, MPLS DiffServ Tunneling Modes, Sample MPLS VPN QoS Roles. IPsec VPN QoS Design: The Need for QoS in IPsec VPN, VPN Use Cases and Their QoS Models, IPsec Refresher, Encryption and Classification: Order of Operations, MTU Considerations, DMVPN QoS Considerations. Part VI IP Multicast DesignEnterprise IP Multicast Design: How Does IP Multicast Work? Multicast Protocols, Multicast Forwarding and RPF Check, Multicast Protocol Basics, PIM-SM Overview, Multicast Routing Table, Basic SSM Concepts, Bidirectional PIM. RP discovery, Anycast RP Features, MSDP. Part VII Designing Optimum Enterprise Network SecurityDesigning Security Services and Infrastructure Protection Network Security Zoning, Designing Infrastructure Protection.Designing firewall & IPS solutions: Firewall architectures, virtualized firewalls. Case Study: Application Tier separation, Case Study: Firewalls in a Data Center, Case Study: Firewall High Availability, IPS Architectures, Case Study: Secure Campus Edge Design (Internet and Extranet Connectivity). IP Multicast Security: Multicast Security Challenges, Multicast Network Security Considerations. Designing Network Access Control Solutions:IEEE 802.1X, EAP, 802.1X supplicants, 802.1X phased deployment, Case Study: Authorization Options. Part VIII Design scenariosDesign Case Studies: 1: Enterprise Connectivity, 2: Enterprise BGP with Internet Connectivity, 3: IPv6, 4: Data Center Connectivity, 5: Resilient Enterprise WAN, 6: Secure Enterprise Network, 7: QoS in the Enterprise Network.

Perl training course description A hands on introduction to programming in Perl. What will you learn Write Perl programs. Use Perl modules. Debug Perl programs. Examine existing code and determine its function. Perl training course details Who will benefit: Anyone wishing to learn Perl. Prerequisites: None although experience in another high level language would be useful. Duration 5 days Perl training course contents Introduction to Perl What is Perl? When to use Perl, downloading Perl, installing Perl, documentation, perldoc, running Perl, the Perl environment. Perl under UNIX, Perl under Windows. "Hello world". Variables Scalars, data types, $_, strings and numbers, assignment, constants, strict, scope, STDIN. Operators Number operators, string operators, precedence and associativity, converting numbers and strings, shortcut operators. Flow control Blocks, if, else, elseif, unless, foreach, while, for do, until. Regular expressions What are regular expressions? Pattern matching, Perl as a filter, file editing. Strings Comparing strings, concatenating, substrings, chomp, chop, formatting, string manipulation. Subroutines Comparing strings, concatenating, substrings, chomp, chop, formatting, string manipulation. Arrays and hashes Working with arrays, element access, push(), pop(), shift(), unshift(), <STDIN> as an array, associative arrays, hashes of arrays, hash references, arrays of hashes, hashes of hashes. Files Simple file handling, open, close, <FILEHANDLE>, <>, file tests, directory access, directory handles, database access, packing and packing binary data. I/O STDIN, STDOUT and STDERR, Command line arguments,@ARGV. Perl debugging The built in debugger, running the debugger, debugger commands, graphical debuggers. Script syntax errors, single stepping, breakpoints, watches. Packages and modules CPAN, Finding modules, installing modules, using modules, scope. Report formatting Formats, defining a format, invoking a format, field holders. Process management System interaction, system(), exec(), signals. Security issues.
