- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
843 Courses
Navigating the maze of healthcare data privacy in a GDPR-regulated world is no simple task. The 'Mastering Healthcare GDPR Certificate' is tailored to demystify this intricate realm, encompassing everything from data governance, to rights of data subjects, and even delving into cross-border health data intricacies. Step into the future of healthcare data compliance with a course curriculum that not only acquaints you with the basics but also explores the nuances of modern-day data protection in the medical world. Learning Outcomes Understand the foundational principles of Healthcare GDPR. Grasp the complexities of data governance within the healthcare sector. Familiarise with healthcare data subject rights, obligations, and associated GDPR guidelines. Develop knowledge on safeguarding sensitive healthcare data in various scenarios. Learn the intricacies of cross-border health data transfer and its implications. Why buy this Mastering Healthcare GDPR Certificate? Unlimited access to the course for a lifetime. Opportunity to earn a certificate accredited by the CPD Quality Standards and CIQ after completing this course. Structured lesson planning in line with industry standards. Immerse yourself in innovative and captivating course materials and activities. Assessments designed to evaluate advanced cognitive abilities and skill proficiency. Flexibility to complete the Course at your own pace, on your own schedule. Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience. Unlock career resources for CV improvement, interview readiness, and job success Who is this Mastering Healthcare GDPR Certificate for? Medical professionals keen on understanding GDPR compliance. Healthcare administrators aiming to streamline data governance. Legal professionals focusing on healthcare data regulations. IT specialists in the healthcare sector looking to bolster data protection strategies. Researchers venturing into medical studies requiring data compliance. Career path Healthcare Data Compliance Officer: £35,000 - £50,000 Healthcare IT Specialist: £40,000 - £60,000 Medical Data Governance Advisor: £45,000 - £65,000 GDPR Healthcare Consultant: £50,000 - £70,000 Healthcare Legal Advisor (GDPR Specialisation): £60,000 - £85,000 Medical Research Data Analyst: £40,000 - £58,000 Prerequisites This Mastering Healthcare GDPR Certificate does not require you to have any prior qualifications or experience. You can just enrol and start learning. This course was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Certification After studying the course materials, there will be a written assignment test which you can take at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £4.99 Original Hard Copy certificates need to be ordered at an additional cost of £8. Course Curriculum Module 1: Introduction to Healthcare GDPR Introduction to Healthcare GDPR 00:17:00 Module 2: Data Governance in Healthcare Data Governance in Healthcare 00:18:00 Module 3: Healthcare Data Subject Rights and Obligations Healthcare Data Subject Rights and Obligations 00:19:00 Module 4: Protecting Health Data Protecting Health Data 00:17:00 Module 5: GDPR Obligations and Sensitive Data GDPR Obligations and Sensitive Data 00:19:00 Module 6: Transferring Health Data Transferring Health Data 00:19:00 Module 7: Consent and Lawful Bases for Healthcare Data Processing Consent and Lawful Bases for Healthcare Data Processing 00:18:00 Module 8: Rights of Data Subjects Rights of Data Subjects 00:19:00 Module 9: Safeguarding Healthcare Data Safeguarding Healthcare Data 00:19:00 Module 10: Protecting Health Data in the Modern Age Protecting Health Data in the Modern Age 00:18:00 Module 11: Cross-Border Health Data Cross-Border Health Data 00:18:00 Module 12: Medical Research Medical Research 00:18:00

Adobe Acrobat Pro DC Beginner
By iStudy UK
Learning Objectives Introduction , Accessing PDFs , Creating PDFs , Navigating PDFs , Reviewing PDFs , Modifying PDFs , Optimizing PDFs , Exporting PDFs , Protecting PDFs , Conclusion Pre-Requisites Basic computer skills. Knowledge of PDF concepts is helpful but not required. Description Workplace demand for digital media skills including creating, managing, and integrating PDF documents is on the rise. Adobe Acrobat training is an excellent way to learn and validate your digital communication skills. This brings value to prospective clients and employers. Unit 1: Introduction to Adobe Acrobat Lesson 1-Introducing Acrobat and PDFs 00:03:00 Lesson 2-Opening a PDF and Navigating Acrobat 00:09:00 Lesson 3-Customizing Toolbars 00:03:00 Lesson 4-Changing Preferences 00:04:00 Unit 2: Introduction to Creating PDFs Lesson 1-Creating PDFs from Office 00:09:00 Lesson 2-Creating PDFs from Creative Cloud Apps 00:10:00 Lesson 3-Creating PDFs from the Document Cloud 00:04:00 Lesson 4-Storing PDFs 00:05:00 Lesson 5-Combining PDFs 00:05:00 Unit 3: Using Search, Bookmarks and Links Lesson 1-Using Search 00:06:00 Lesson 2-Creating Bookmarks 00:06:00 Lesson 3-Creating Links 00:10:00 Unit 4: Commenting Lesson 1-Commenting on a PDF 00:10:00 Lesson 2-Sending for Comments 00:07:00 Unit 5: Editing PDFs Lesson 1-Editing Text and Images 00:06:00 Lesson 2-Cropping Images 00:03:00 Lesson 3-Adding, Updating and Removing Headers and Footers 00:09:00 Lesson 4-Using Watermarks 00:07:00 Lesson 5-Organizing Pages 00:03:00 Lesson 6-Extracting Pages 00:03:00 Lesson 7-Inserting Pages 00:03:00 Lesson 8-Replacing Pages 00:03:00 Unit 6: Advanced Features Lesson 1-Reducing File Size 00:05:00 Lesson 2-Advanced Optimization 00:16:00 Lesson 3-Using Actions 00:04:00 Lesson 4-Creating Actions 00:08:00 Unit 7: Exporting Lesson 1-Exporting to Word 00:05:00 Lesson 2-Exporting to Excel 00:04:00 Lesson 3-Exporting to Rich Text Format 00:04:00 Unit 8: Protecting File Lesson 1-Redacting Content 00:08:00 Lesson 2-Protecting a PDF 00:15:00 Resource Resource - Adobe Acrobat Pro DC Beginner 00:00:00 Final Exam Final Exam - Adobe Acrobat Pro DC Beginner 00:20:00

AZ-500T00 Microsoft Azure Security Technologies
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for Azure Security Engineers who are planning to take the associated certification exam, or who are performing security tasks in their day-to-day job. This course would also be helpful to an engineer that wants to specialize in providing security for Azure-based digital platforms and play an integral role in protecting an organization's data. This course provides IT Security Professionals with the knowledge and skills needed to implement security controls, maintain an organization?s security posture, and identify and remediate security vulnerabilities. This course includes security for identity and access, platform protection, data and applications, and security operations. Prerequisites AZ-104T00 - Microsoft Azure Administrator Security best practices and industry security requirements such as defense in depth, least privileged access, role-based access control, multi-factor authentication, shared responsibility, and zero trust model. Be familiar with security protocols such as Virtual Private Networks (VPN), Internet Security Protocol (IPSec), Secure Socket Layer (SSL), disk and data encryption methods. Have some experience deploying Azure workloads. This course does not cover the basics of Azure administration, instead the course content builds on that knowledge by adding security specific information. Have experience with Windows and Linux operating systems and scripting languages. Course labs may use PowerShell and the CLI. 1 - Manage identities in Microsoft Entra ID Secure users in Microsoft Entra ID Secure groups in Microsoft Entra ID Recommend when to use external identities Secure external identities Implement Microsoft Entra Identity protection 2 - Manage authentication by using Microsoft Entra ID Configure Microsoft Entra Verified ID Implement multifactor authentication (MFA) Implement passwordless authentication Implement password protection Implement single sign-on (SSO) Integrate single sign-on (SSO) and identity providers Recommend and enforce modern authentication protocols 3 - Manage authorization by using Microsoft Entra ID Configure Azure role permissions for management groups, subscriptions, resource groups, and resources Assign built-in roles in Microsoft Entra ID Assign built-in roles in Azure Create and assign a custom role in Microsoft Entra ID Implement and manage Microsoft Entra Permissions Management Configure Microsoft Entra Privileged Identity Management Configure role management and access reviews by using Microsoft Entra Identity Governance Implement Conditional Access policies 4 - Manage application access in Microsoft Entra ID Manage access to enterprise applications in Microsoft Entra ID, including OAuth permission grants Manage app registrations in Microsoft Entra ID Configure app registration permission scopes Manage app registration permission consent Manage and use service principals Manage managed identities for Azure resources Recommend when to use and configure a Microsoft Entra Application Proxy, including authentication 5 - Plan and implement security for virtual networks Plan and implement Network Security Groups (NSGs) and Application Security Groups (ASGs) Plan and implement User-Defined Routes (UDRs) Plan and implement Virtual Network peering or gateway Plan and implement Virtual Wide Area Network, including secured virtual hub Secure VPN connectivity, including point-to-site and site-to-site Implement encryption over ExpressRoute Configure firewall settings on PaaS resources Monitor network security by using Network Watcher, including NSG flow logging 6 - Plan and implement security for private access to Azure resources Plan and implement virtual network Service Endpoints Plan and implement Private Endpoints Plan and implement Private Link services Plan and implement network integration for Azure App Service and Azure Functions Plan and implement network security configurations for an App Service Environment (ASE) Plan and implement network security configurations for an Azure SQL Managed Instance 7 - Plan and implement security for public access to Azure resources Plan and implement Transport Layer Security (TLS) to applications, including Azure App Service and API Management Plan, implement, and manage an Azure Firewall, Azure Firewall Manager and firewall policies Plan and implement an Azure Application Gateway Plan and implement an Azure Front Door, including Content Delivery Network (CDN) Plan and implement a Web Application Firewall (WAF) Recommend when to use Azure DDoS Protection Standard 8 - Plan and implement advanced security for compute Plan and implement remote access to public endpoints, Azure Bastion and just-in-time (JIT) virtual machine (VM) access Configure network isolation for Azure Kubernetes Service (AKS) Secure and monitor AKS Configure authentication for AKS Configure security for Azure Container Instances (ACIs) Configure security for Azure Container Apps (ACAs) Manage access to Azure Container Registry (ACR) Configure disk encryption, Azure Disk Encryption (ADE), encryption as host, and confidential disk encryption Recommend security configurations for Azure API Management 9 - Plan and implement security for storage Configure access control for storage accounts Manage life cycle for storage account access keys Select and configure an appropriate method for access to Azure Files Select and configure an appropriate method for access to Azure Blob Storage Select and configure an appropriate method for access to Azure Tables Select and configure an appropriate method for access to Azure Queues Select and configure appropriate methods for protecting against data security threats, including soft delete, backups, versioning, and immutable storage Configure Bring your own key (BYOK) Enable double encryption at the Azure Storage infrastructure level 10 - Plan and implement security for Azure SQL Database and Azure SQL Managed Instance Enable database authentication by using Microsoft Entra ID Enable and monitor database audit Identify use cases for the Microsoft Purview governance portal Implement data classification of sensitive information by using the Microsoft Purview governance portal Plan and implement dynamic mask Implement transparent data encryption? Recommend when to use Azure SQL Database Always Encrypted 11 - Plan, implement, and manage governance for security Create, assign, and interpret security policies and initiatives in Azure Policy Configure security settings by using Azure Blueprint Deploy secure infrastructures by using a landing zone Create and configure an Azure Key Vault Recommend when to use a dedicated Hardware Security Module (HSM) Configure access to Key Vault, including vault access policies and Azure Role Based Access Control Manage certificates, secrets, and keys Configure key rotation Configure backup and recovery of certificates, secrets, and keys 12 - Manage security posture by using Microsoft Defender for Cloud Implement Microsoft Defender for Cloud Identify and remediate security risks by using the Microsoft Defender for Cloud Secure Score and Inventory Assess compliance against security frameworks and Microsoft Defender for Cloud Add industry and regulatory standards to Microsoft Defender for Cloud Add custom initiatives to Microsoft Defender for Cloud Connect hybrid cloud and multicloud environments to Microsoft Defender for Cloud Identify and monitor external assets by using Microsoft Defender External Attack Surface Management 13 - Configure and manage threat protection by using Microsoft Defender for Cloud Enable workload protection services in Microsoft Defender for Cloud, including Microsoft Defender for Storage, Databases, Containers, App Service, Key Vault, Resource Manager, and DNS Configure Microsoft Defender for Servers Configure Microsoft Defender for Azure SQL Database Manage and respond to security alerts in Microsoft Defender for Cloud Configure workflow automation by using Microsoft Defender for Cloud Evaluate vulnerability scans from Microsoft Defender for Server 14 - Configure and manage security monitoring and automation solutions Monitor security events by using Azure Monitor Configure data connectors in Microsoft Sentinel Create and customize analytics rules in Microsoft Sentinel Configure automation in Microsoft Sentinel Additional course details: Nexus Humans AZ-500T00 Microsoft Azure Security Technologies training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the AZ-500T00 Microsoft Azure Security Technologies course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

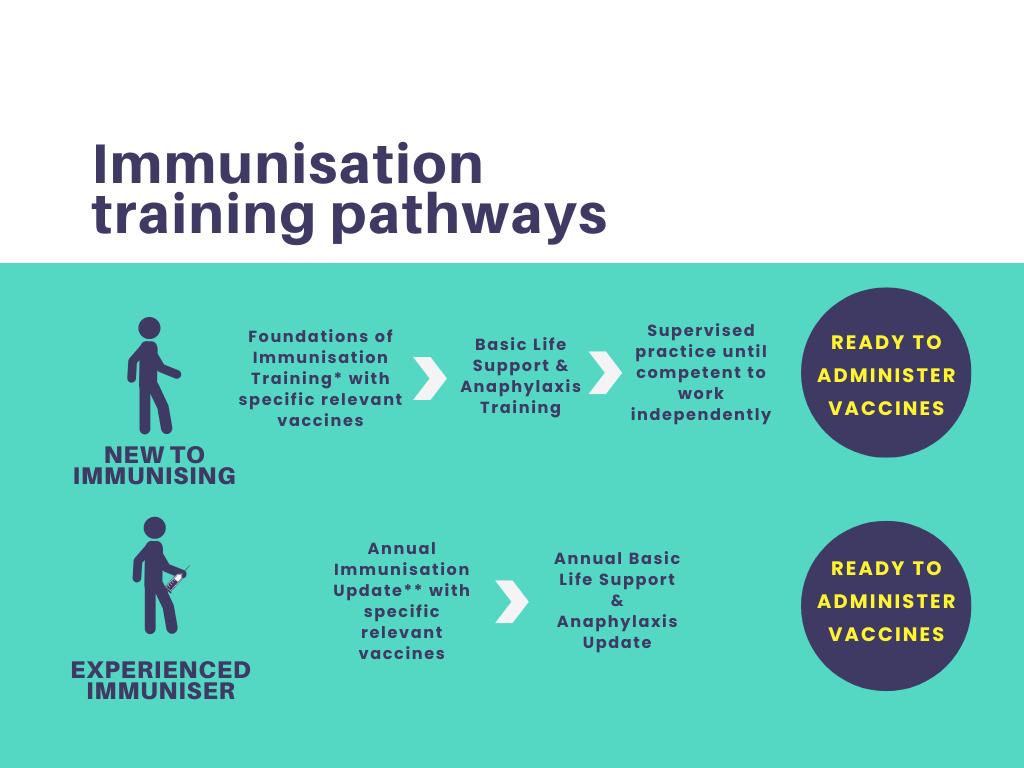
Foundations of Immunisation and Vaccines
By Guardian Angels Training
Gain a comprehensive understanding of immunisation and vaccines with our "Foundations of Immunisation and Vaccines" course. Designed for healthcare professionals, public health workers, and individuals interested in immunisation, this course covers vaccine development, administration, safety, and the role of vaccines in preventing infectious diseases.
Cyber Security Analyst - IT Job Ready Program + Career Support & Money Back Guarantee
4.5(3)By Studyhub UK
The year is 2023. The world is a very different place than it was just a few years ago. Technology has advanced at an unprecedented pace, and with it, the threat of cyber attacks has grown exponentially. In this new world, cyber security is more important than ever. That's where cyber security analysts come in. These professionals are responsible for protecting computer systems and networks from attack. Our Cyber Security Analyst Training program provides comprehensive training in all aspects of cyber security, from basic security concepts to advanced penetration testing techniques. In addition to training, our program also provides career mentoring and support. We'll help you build your resume, practice your interview skills, and network with potential employers. We'll also be there to support you throughout your job search. We will help you to get a job, so you won't have to worry about a thing. Just gain knowledge and learn skills, getting you a job is our duty. Enrol today and take your career to the next level! If you're ready to start a career in cyber security, our program can help you get there. Our affordable tuition makes our program accessible to everyone. Our mission is simple: to be your trusted partner and assist you every step of the way until you land the job of your dreams. Why Choose Us Here's what makes our Cyber Security Analyst Training Program stand out from the crowd: Personalised Job Search Assistance: We're in this together! Our dedicated team will work tirelessly to support your entire job searching process. From crafting a standout resume to submitting it to top companies, we'll ensure you have a compelling application that gets noticed. Expertly Crafted CV: Your resume is your ticket to the interview room. Our professional resume writers will create a customised CV highlighting your unique skills and experiences. This will maximise your chances of standing out among the competition. Strategic Placement: We understand the power of casting a wide net. We'll strategically submit your CV to various platforms and networks, expanding your reach and connecting you with valuable opportunities that align with your career goals. One-On-One Consultation Sessions with Industry Experts: Gain invaluable insights and guidance from seasoned professionals who have thrived in the Cyber Security field. Our consultation sessions provide you with insider tips, tricks, and advice, empowering you to navigate the industry with confidence and expertise. Comprehensive Skill Development: Our program is designed to equip you with the most sought-after skills in the Cyber Security sector. From mastering cutting-edge tools to honing your Cyber Security prowess, we'll ensure you have the knowledge and expertise to excel in any Cyber Security-driven environment. Ongoing Support: We understand that the journey to landing your dream job doesn't end with placement. That's why our commitment to your success extends well beyond your initial training. Our support team will be available to answer your questions, provide guidance, and assist you as you progress in your career. Here are the 6 courses we will provide once you enrol in the program: CompTIA CySA+ Cybersecurity Analyst (CS0-002) CompTIA Security+ (SY0-601) Linux Security and Hardening Web Application Penetration Testing Course Computer Networks Security from Scratch to Advanced Cyber Security Incident Handling and Incident Response These courses will help you to develop your knowledge and skills to become a successful Cyber Security Analyst. The Program is completed in 5 easy steps: Step 1 - Enrol in the program and start learning from the courses we provide After you enrol in this Cyber Security Analyst Training Program, you will get lifetime access to 6 premium courses related to Cyber Security. These courses will teach you the knowledge and skills required to become a successful Cyber Security Analyst. Our customer service team will help you and keep in contact with you every step of the way. Step 2 - Complete your courses and get certifications After learning from the courses, you must obtain certificates for each course. There will be exams for every course, and you have to pass them to get your certificate. To pass successfully, you must get 90% marks for the first course and 80% for the rest relevant courses. Once you pass the exams, you will receive hardcopy certificates. These certificates will prove that you're an expert in the subject. Step 3 - Get a consultation session from a professional Cyber Security Analyst Take your Cyber Security skills to new heights with a one-on-one consultation session led by a seasoned professional. Gain invaluable insights, expert tips, and tailored advice that will propel your career forward. Step 4 - Complete the CV and attend the interview Once you've successfully obtained the certifications, our team of professionals will build you a compelling CV and LinkedIn profile. With these powerful tools in hand, you'll be fully prepared to tackle job interviews confidently. Kickstart your Cyber Security Analyst career with a starting salary ranging from •30,000 to •50,000 annually. Step into the Cyber Security industry with the assurance of a promising future. Step 5 - We will not leave you until you get a job Our commitment to your success goes above and beyond. We won't stop until you land that dream job. With personalised support, expert guidance, and unwavering dedication, we'll be by your side until you secure the perfect opportunity. Your job search becomes our mission, ensuring you have the best chance at a successful career in Cyber Security. Don't miss out on this incredible opportunity to kickstart your cybersecurity career with our Cyber Security Analyst Training Program. With our unwavering support and guidance, you can confidently navigate the job market, land your dream job, and excel in your chosen field. Enrol today and join the ranks of successful cybersecurity professionals who have found their footing with Studyhub. Together, let's secure the future! CPD 100 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This Cyber Security Analyst Training program is ideal for: Aspiring cybersecurity professionals seeking a comprehensive training program. Career changers looking to transition into the lucrative field of cybersecurity. Recent graduates aiming to kickstart their cybersecurity career with industry-relevant skills. IT professionals seeking to specialise in cybersecurity and enhance their job prospects. Individuals passionate about protecting digital assets and combating cyber threats. Requirements No experience required. Just enrol & start learning. Career path The cybersecurity industry in the UK offers a promising career path. With an increasing demand for skilled professionals, graduates of our program can pursue roles as Cyber Security Analysts, Penetration Testers, Incident Responders, and more. Companies across various sectors, including finance, healthcare, and government, are actively hiring in this field. Certificates CPD Accredited e-Certificate Digital certificate - Included CPD Accredited Framed (Hardcopy) Certificate Hard copy certificate - Included Enrolment Letter Digital certificate - Included Student ID Card Digital certificate - Included

Aggression Managemnet Training Course Online
By Study Plex
Recognised Accreditation This course is accredited by continuing professional development (CPD). CPD UK is globally recognised by employers, professional organisations, and academic institutions, thus a certificate from CPD Certification Service creates value towards your professional goal and achievement. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. What is CPD? Employers, professional organisations, and academic institutions all recognise CPD, therefore a credential from CPD Certification Service adds value to your professional goals and achievements. Benefits of CPD Improve your employment prospects Boost your job satisfaction Promotes career advancement Enhances your CV Provides you with a competitive edge in the job market Demonstrate your dedication Showcases your professional capabilities What is IPHM? The IPHM is an Accreditation Board that provides Training Providers with international and global accreditation. The Practitioners of Holistic Medicine (IPHM) accreditation is a guarantee of quality and skill. Benefits of IPHM It will help you establish a positive reputation in your chosen field You can join a network and community of successful therapists that are dedicated to providing excellent care to their client You can flaunt this accreditation in your CV It is a worldwide recognised accreditation What is Quality Licence Scheme? This course is endorsed by the Quality Licence Scheme for its high-quality, non-regulated provision and training programmes. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. Benefits of Quality License Scheme Certificate is valuable Provides a competitive edge in your career It will make your CV stand out Course Curriculum Making Yourself Safe Introduction 00:02:00 Lesson 1.1: What situations produce aggression? 00:03:00 Lesson 1.2: Effective Use of Conflict Management Skills 00:06:00 Lesson 1.3: Preventing Aggression 00:10:00 Lesson 2.1: Situational Signs 00:07:00 Lesson 2.2: Recognizing the Warning Signs 00:10:00 Lesson 2.3: Recognizing the Warning Signs (cont.) 00:08:00 Lesson 3.1: Defusing the Situation I 00:07:00 Lesson 3.2: Defusing the Situation II 00:12:00 Lesson 3.3: Defusing the Situation III 00:16:00 Lesson 4.1: Protecting Yourself I 00:04:00 Lesson 4.2: Protecting Yourself II 00:10:00 Lesson 4.3: Protecting Yourself III 00:07:00 Lesson 5.1: The Role of Adrenaline 00:07:00 Lesson 5.2: Dealing with the Aftermath 00:12:00 Lesson 5.3: Grief, Crisis and Trauma 00:15:00 Lesson 6.1: DOs 00:09:00 Lesson 6.2: DON'Ts 00:09:00 Lesson 6.3: Challenges and Rewards 00:02:00 Concluding video 00:01:00 Assessment Assessment -Aggression Handling Training 00:10:00 Certificate of Achievement Certificate of Achievement 00:00:00 Get Your Insurance Now Get Your Insurance Now 00:00:00 Feedback Feedback 00:00:00

Search By Location
- protecting Courses in London
- protecting Courses in Birmingham
- protecting Courses in Glasgow
- protecting Courses in Liverpool
- protecting Courses in Bristol
- protecting Courses in Manchester
- protecting Courses in Sheffield
- protecting Courses in Leeds
- protecting Courses in Edinburgh
- protecting Courses in Leicester
- protecting Courses in Coventry
- protecting Courses in Bradford
- protecting Courses in Cardiff
- protecting Courses in Belfast
- protecting Courses in Nottingham