- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
186 Trust courses in Manchester
RELATIONSHIP COUNSELLING IN KENSINGTON
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
Relationship Counselling in Kensington: Reconnect and Grow with Our 3-Session PackageEnhance your relationship with our personalized Relationship Counselling in Kensington. Our specialized package offers three intensive 1-hour sessions designed to improve communication, resolve conflicts, and build a deeper emotional connection.In these sessions, couples will learn and practice: Communication Skills: Develop the ability to express your thoughts and emotions clearly while improving your active listening skills. Conflict Resolution Strategies: Learn effective methods to address and resolve disagreements constructively, ensuring mutual respect and understanding. Emotional Intimacy: Strengthen your emotional bond by understanding each other’s needs and fostering empathy. Trust Building: Discover techniques to rebuild and maintain trust, an essential element of a healthy relationship. Stress Management: Gain tools to manage external stressors together, fostering a supportive and resilient partnership. Goal Alignment: Align your personal and relationship goals to create a harmonious and unified vision for your future. Our experienced therapists in Kensington provide a safe and supportive environment where couples can explore these critical aspects of their relationship. Each session is tailored to address your unique challenges and aspirations, ensuring personalized and effective guidance.Book your Relationship Counselling in Kensington today and take the first step towards a stronger, more fulfilling relationship. Relationship Counselling in Kensington and Chelsea | M.D.D Dating Coach, Couples Therapy, Breakup Counselling, Personal development Consultancy (relationshipsmdd.com)

Building Better Careers with Soft Skills: 1-Day Workshop in Bolton
By Mangates
10 Soft Skills You Need 1 Day Training in Bolton

Relationship Counselling in Victoria: Strengthen Your Bond with Our Expert 3-Session Program Revitalize your relationship with our bespoke Relationship Counselling in Victoria. Our expertly designed package includes three comprehensive 1-hour sessions aimed at improving communication, resolving conflicts, and fostering a deeper emotional connection. Throughout these sessions, couples will explore and develop: Effective Communication: Master the art of expressing your thoughts and feelings clearly while actively listening to your partner. Conflict Resolution Techniques: Learn to navigate disagreements constructively, ensuring mutual respect and understanding. Emotional Intimacy: Build a stronger emotional bond by understanding each other’s needs and cultivating empathy. Trust Enhancement: Implement strategies to rebuild and maintain trust, a cornerstone of any healthy relationship. Stress Management: Develop coping mechanisms to manage external stressors together, promoting a supportive partnership. Shared Goal Setting: Harmonize your personal and relationship goals to create a unified vision for your future. Our skilled therapists in Victoria provide a nurturing and confidential environment, allowing couples to address their unique challenges and grow together. Each session is tailored to your specific needs, ensuring personalized and impactful support. Schedule your Relationship Counselling in Victoria today and embark on a journey towards a more resilient and fulfilling relationship. Marriage Counselling Victoria | M.D.D Dating Coach, Couples Therapy, Breakup Counselling, Personal development Consultancy (relationshipsmdd.com)

M.D.D RELATIONSHIP COUNSELLING LONDON PACKAGE (COUPLES)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
Introducing Relationship Counselling London Package: Strengthening Bonds and Nurturing Lasting Connections Are you and your partner experiencing challenges in your relationship and seeking professional support to improve communication and enhance intimacy? Miss Date Doctor’s Relationship Counselling London Package offers you expert guidance to navigate difficulties, strengthen your bond, and foster a healthier, more fulfilling partnership. Relationship counselling is a valuable opportunity for couples to address underlying issues, improve communication, and gain insights into each other’s needs and perspectives. Our experienced relationship counsellors in London are committed to helping you and your partner build a stronger foundation for a lasting and loving relationship. Here’s how the Relationship Counselling London Package can support you: Effective Communication: Our counsellors will help you and your partner improve communication skills, fostering a deeper understanding of each other’s feelings and needs. Conflict Resolution: Relationship counselling addresses conflict resolution strategies, helping you navigate disagreements constructively and prevent recurring patterns of conflict. Rebuilding Trust: If trust has been compromised, our counsellors will guide you in rebuilding trust and creating a more secure emotional bond. Intimacy and Emotional Connection: We’ll explore ways to enhance emotional intimacy and create a more fulfilling emotional connection between you and your partner. Identifying Patterns: Relationship counselling helps identify negative patterns of behaviour or communication that may be contributing to relationship challenges. Exploring Relationship Goals: Our counsellors will help you and your partner explore your shared goals and aspirations, ensuring that you are aligned in your vision for the future. Navigating Transitions: Relationship counselling can assist you in navigating major life transitions together, providing support during times of change. Tools for Sustaining a Healthy Relationship: We’ll equip you with tools and techniques to sustain a healthy and loving relationship beyond counselling. The Relationship Counselling London Package at Miss Date Doctor is tailored to meet the unique needs of your relationship. Our skilled counsellors provide a safe and supportive space for open and honest dialogue, allowing you and your partner to work towards a more fulfilling and harmonious partnership. Invest in the well-being of your relationship and take the first step towards a healthier and more loving connection with the Relationship Counselling London Package. Embrace the opportunity to strengthen your bond, improve communication, and create a lasting and satisfying relationship. Let our experienced counsellors guide you and your partner towards a brighter future filled with love, understanding, and mutual support. 3 x1 hour https://relationshipsmdd.com/product/relationship-counselling-london-package/

Relationship Counselling in Mayfair: Transform Your Partnership with Our Comprehensive 3-Session Package Unlock the full potential of your relationship with our specialized Relationship Counselling in Mayfair. Our tailored package includes three intensive 1-hour sessions designed to strengthen your bond, enhance communication, and resolve conflicts effectively. During these sessions, couples will delve into essential areas such as: Communication Skills: Learn how to articulate your thoughts and feelings clearly and listen actively to your partner. Conflict Resolution: Discover strategies to manage disagreements constructively, ensuring both partners feel heard and respected. Emotional Intimacy: Enhance your emotional connection by understanding each other’s needs and fostering deeper empathy. Trust Building: Develop techniques to rebuild and maintain trust, a critical component of a healthy relationship. Stress Management: Learn how to handle external stressors together, creating a supportive and resilient partnership. Goal Setting: Align your personal and relationship goals to ensure a harmonious future together. Our experienced therapists in Mayfair are dedicated to providing a safe and supportive environment where couples can explore these vital aspects of their relationship. Each session is crafted to address your unique challenges and aspirations, ensuring personalized and effective guidance. Book your Relationship Counselling in Mayfair today and take the first step towards a stronger, more fulfilling relationship. Relationship Coaching London (relationshipsmdd.co.uk) Relationship counselling Mayfair⭐⭐⭐⭐⭐ | M.D.D Dating Coach, Couples Therapy, Breakup Counselling, Personal development Consultancy (relationshipsmdd.com)

M.D.D PRE-MARITAL COUNSELLING LONDON PACKAGE (COUPLES)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
Introducing Pre-Marital Counselling London Package: Building a Strong Foundation for a Lifelong Partnership Are you planning to tie the knot and seeking guidance to ensure a strong and healthy foundation for your marriage? Miss Date Doctor’s Pre-Marital Counselling London Package offers you expert support and valuable insights to prepare for a fulfilling and lasting partnership. Pre-marital counselling is a proactive approach that helps couples explore their expectations, communication styles, and potential areas of growth before entering into marriage. Our experienced counsellors in London are dedicated to helping you lay the groundwork for a successful and harmonious marriage. Here’s how the Pre-Marital Counselling London Package can support you: Effective Communication: Our counsellors will guide you in developing open and effective communication skills to express your feelings and needs clearly, fostering understanding and connection. Conflict Resolution: Pre-marital counselling addresses conflict resolution strategies, ensuring that you are equipped with healthy ways to navigate disagreements and challenges in your marriage. Exploring Expectations: We’ll help you and your partner explore and align your expectations about various aspects of marriage, such as roles, finances, family, and lifestyle. Strengthening Intimacy: Pre-marital counselling provides a safe space to discuss emotional and physical intimacy, fostering a deeper connection and understanding between you and your partner. Financial Planning: Our counsellors will assist you in creating a financial plan, emphasizing financial transparency and teamwork to manage shared resources. Building Trust: Trust is a fundamental aspect of a successful marriage. Pre-marital counselling helps you and your partner build and strengthen trust through open and honest discussions. Shared Values and Goals: We’ll explore your shared values and long-term goals, ensuring that you are aligned in your vision for the future. Handling Life Transitions: Pre-marital counselling can prepare you for various life transitions, such as starting a family, changing careers, or dealing with unexpected challenges. The Pre-Marital Counselling London Package at Miss Date Doctor offers you an opportunity to invest in the foundation of your marriage. Our skilled counsellors provide a safe and supportive space to discuss important topics, discover each other’s strengths, and build a solid framework for a successful partnership. Take the first step towards a joyful and harmonious marriage with the Pre-Marital Counselling London Package. Embrace the opportunity to grow together, nurture your relationship, and create a lasting bond that will withstand the tests of time. Let our experienced counsellors guide you towards a fulfilling and loving marriage that stands the test of time. 3 x 1 hour https://relationshipsmdd.com/product/pre-marital-counselling-london-package/

Microsoft security training course description A hands on training course focusing on security in the Microsoft environment. The course progresses from patch management onto the use of Microsoft security tools. Then server, desktop and network security are studied in the Microsoft environment. What will you learn Use Microsoft security tools. Secure Microsoft servers. Secure Microsoft desktops. Secure Microsoft networks. Microsoft security training course details Who will benefit: Technical server support staff. Technical desktop support staff. Technical network staff. Technical security staff. Prerequisites: Supporting Windows server 2016 Networking Microsoft systems. Duration 3 days Microsoft security training course contents Introduction Security threats, Microsoft defaults, admin accounts, security patches, patch management, patch tools. Hands on: Studying Microsoft defaults, applying security patches. Microsoft security tools Microsoft updates, WSUS, Inventory tool, baseline security analyser, URLscan, EventCombMT, Cipher security tool, Port reporter, PortQry. Tools hackers use. Hands on: Using Microsoft security tools. Server security Checklists, core server security, AD, Member server security, Domain controller security, Specific roles. Hands on Hardening Microsoft servers, security templates. Active Directory Admin authority in AD, group policy, trust and authentication. Desktop security Checklists, core client security, anti virus software, anti spyware software, firewalls, securing clients with AD, securing clients with group policy, software restriction policies. Hands on Securing Microsoft desktops. Network security Checklist, IP security, VPNs, PKI, certificate authorities, RAS, RRAS, IAS. Hands on: VPN configuration, IAS configuration. Monitoring Auditing, authorisation and logons, tracking, system monitoring, detecting attacks. Hands on: Monitoring Microsoft systems. Summary Microsoft security response centre, security advisories.

Marriage Counselling London Miss Date Doctor
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
Strengthen your marriage with professional marriage counselling in London. Our experienced counsellors help couples navigate marital issues such as communication problems, intimacy concerns, and trust issues. Through tailored therapy sessions, we aim to foster a healthy, loving relationship that can withstand life's pressures and challenges. Key areas: couples therapy, relationship counselling, marital therapy, marriage support, relationship advice, marriage guidance, partnership counselling. 3 x 1 hour sessions

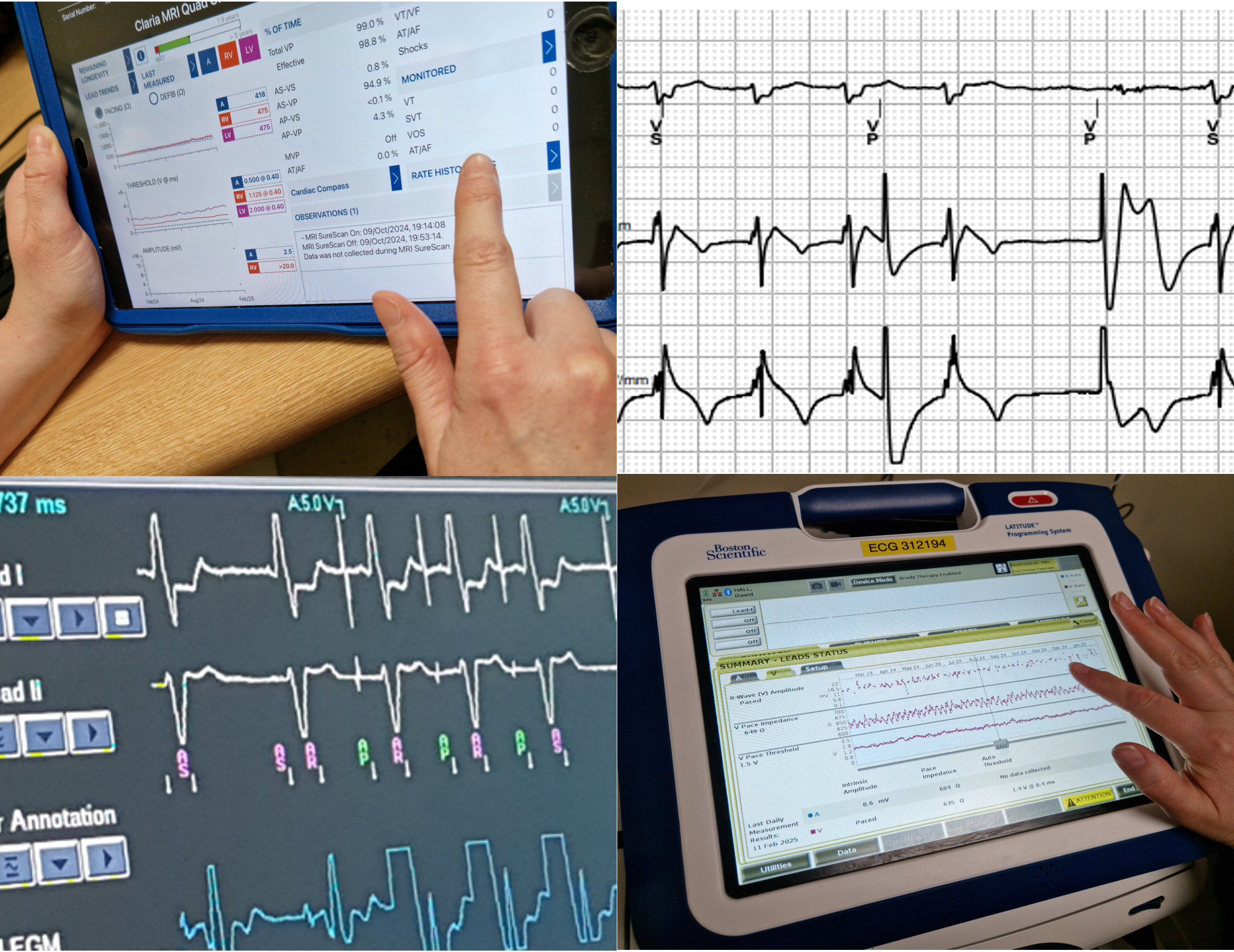
Demystifying cardiac devices — a practical introduction for healthcare professionals new to device therapy and monitoring A one day introductory course for all healthcare professionals with limited or no experience of cardiac devices. Ever wanted to know why there are so many different devices and what they do? What do device checks even involve? When are they needed? What should I be looking for on my telemetry? The course will be hosted by senior Cardiac Physiologists/ Scientists from the Cardiac Rhythm Management team at Manchester University NHS Foundation Trust. Full draft agenda below. **If submitting payment via CPD funding OR Purchase Order (i.e. not a card payment) - please DO complete your registration - you can detail payment method in the ‘Billing name' box. Many thanks. **
WSET Level 3 Award in Wines Course inc Exam
By Manchester Wine School
A payment plan is available, please contact us for more details. WSET Level 3 in Wines Award is an advanced level qualification for professionals working in the wine industry and for wine enthusiasts. If you are looking to delve deeper into the world of wines, this qualification provides a detailed understanding of grape growing and wine making. Upon completion you will be able to assess wines accurately, and use your understanding to confidently explain wine style and quality. What the course covers Wine Tasting: Taste, describe and analyse wines using the WSET Systematic Approach to Tasting Food and Wine Matching: A guide to the key considerations when matching food and wine successfully Labelling: Learn how to decode and understand labels Wine Production: Learn about the production factors influencing the style, quality and price of wine from vineyard to bottling Light Wines: Learn about the styles of wines produced in the key wine regions and districts of the world: France, Italy, Spain, Portugal, Austria, Germany, Greece, South Africa, Australia, New Zealand, North and South America, England and Wales Sparkling Wines: Learn about the methods of production and the main styles of sparkling wines from the key wine producing countries: France, Spain, Italy, Germany, New World - Australia, California, New Zealand, South Africa Fortified Wines: Learn about the methods of production/main styles of fortified wines from the key wine countries: Spain, Portugal, France, Australia Examination: The examination is in two parts and takes place in the afternoon session of the final day of the course. The WSET Exam fee is included in the course cost. Theory paper: a combined theory paper consisting of a 50 question multiple-choice section and a four question short answer written section. 2 hours. Tasting: a blind tasting of two wines. A mark of 55% required in all sections to pass. 1 hour. The qualification has full accreditation from the UK Government’s Qualifications & Curriculum Authority as a Level 3 Vocational Qualification. To view the full course specification, including examples of exam questions, please click HERE. Recommended Private Study: 56 hours additional private study is recommended for this course. It is strongly recommended the majority of the private study is done in preparation for each session. Private study is essential to ensure that you are ready and prepared for the exam. Entry requirements: Although not essential, we do recommend you have completed the WSET Level 2 Award in Wines before enrolling on the course. The syllabus assumes that candidates already possess a good basic understanding of simple wine making techniques, key grape varieties and viticultural patterns. The fee of £825 includes All WSET course materials including; 'Accounting For Style And Quality' course manual (comprehensive 250 page textbook), Study Guide and Full SAT Tasting Card All wine tasting samples (60 to 70 wines) The use of professional ISO tasting glasses 6 days of professional WSET tuition by a WSET Certified tutor Teaching of the WSET Level 3 Systematic Approach to Tasting Wine (SAT) ® which will enable you to analyse wines objectively and consistently in preparation for the tasting exam Two fully marked mock tasting exams and weekly written exam technique sessions to ensure you are fully prepared for the exam Comprehensive student support by WSET certified educator outside of class time should you have any questions before, during and after the course Registration with WSET and all examination fees Internationally-recognised certificate and pin badge upon successful completion VAT at 20% (VAT receipt can be provided on request) Special Educational Needs Please make us aware if you have a condition that may mean you qualify for additional help during the exam such as dyslexia. Funding Funding for this course is available: DEVELOP is the educational programme of The Drinks Trust, the drinks and hospitality industry charity. DEVELOP offers fully funded training and skills courses, delivered by industry-leading providers for people already working, or with an ambition to work, in the drinks and hospitality industry. Manchester Wine SChool has partnered with The Drinks Trust to bring courses free of charge to eligible students. All of the WSET courses are available for funding with DEVELOP. To learn more please visit the Drinks Trust website HERE Criteria of eligibility for DEVELOP funding: must be 18 or over, eligible to work in the UK, have a National Insurance Number, and be earning less than £26k/pa

Search By Location
- Trust Courses in London
- Trust Courses in Birmingham
- Trust Courses in Glasgow
- Trust Courses in Liverpool
- Trust Courses in Bristol
- Trust Courses in Manchester
- Trust Courses in Sheffield
- Trust Courses in Leeds
- Trust Courses in Edinburgh
- Trust Courses in Leicester
- Trust Courses in Coventry
- Trust Courses in Bradford
- Trust Courses in Cardiff
- Trust Courses in Belfast
- Trust Courses in Nottingham