- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Advanced TP-CT - Implementing and Configuring Cisco TelePresence Video Suite
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The primary audience for this course is as follows: Network Video Engineer Voice/UC/Collaboration/Communications Engineer Collaboration Tools Engineer Collaboration Sales/Systems Engineer Overview Implement and Configure Cisco Endpoints Implement and Configure Cisco Unified Communications Manager for Video Endpoints Implement and Configure Cisco IMP for Jabber Implement and Configure Cisco Expressway Implement and Configure Cisco Video Communications Server (VCS) Control Implement and Configure Cisco Video Communications Server (VCS) Expressway Implement and Configure connectivity between a Cisco VCS and Cisco UCM Implement and Configure a Cisco Conductor Implement, Configure, and Operate Cisco TelePresence Management Suite (TMS) and provision devices using Cisco TMS Provisioning Extension (TMSPE) Implement and Configure Cisco Meeting Server This one of kind Cisco Collaboration in-depth course takes student from initial endpoint configuration to a full solution deployment using all of the Cisco Collaboration Components. Students will have extensive labs in which they will configure and troubleshoot a full Cisco Telepresence Deployment. Participants will gain in-depth practical knowledge with exercises on installing, configuring, maintaining and troubleshooting of all Cisco Telepresence Components.The software applications that are covered in this course include:Cisco Unified Communications Manager (CUCM)Cisco Unified Communications Manager IM and PresenceCisco ExpresswayCisco Video Communication Server (VCS)Cisco ConductorCisco Telepresence Server (TS)Cisco Meeting Server (CMS)Cisco Telepresence Management Suite (TMS)Cisco TMS Extensions Understanding Cisco TelePresence Endpoints Cisco TelePresence Endpoint Solutions Overview Cisco DX Series Endpoint Characteristics Cisco TelePresence TC Software-Based Endpoint Characteristics Cisco TelePresence EX60 and EX90 Cisco TelePresence MX Series Cisco TelePresence SX Series Endpoints Cisco TelePresence Room Kits Cisco Intelligent Proximity Cisco TelePresence TC Software-Based Endpoint Peripherals Cisco TelePresence TC Software-Based Endpoint Deployments Cisco TelePresence Integrator C Series-Based Endpoints Cisco Jabber Video for TelePresence Characteristics Cisco Jabber Understanding the Cisco Video Network Network Overview H323 Overview SIP Overview VCS vs Unified Communications Manager Internetworking QOS Overview Implementing and Configuring Unified Communication Manager Unified Communications Manager Initial Settings Service Activation Enterprise and Service Parameters SIP Domains Configure IMP for Jabber Configure Jabber Settings Registering Endpoints Verifying Network Registration Cisco VCS / Expressway Overview and Configuration Configuring Initial VCS Setting Configuring Authentication Registration Conflict Policy Registration Restriction Policy Local Zone Components Membership Rules Transforms Purpose of Zones Search Priority Neighbor Zones Creating Neighbor Zones Need for Traversal Zones H.460 and Assent Protocols Traversal Zone Configuration Domain Name System Dialing E.164 Number Mapping Bandwidth Management Pipes Subzones and Zones Subzone Call Failure Call Processing Order Certificates Certificate Installation Clustering and the Cisco VCS Clustering Configuration Collecting Information Log Files Search History Connecting VCS-C to CUCM Connect VCS-C to VCS-E Connecting CUCM to VCS-C Understanding the Cisco TelePresence Conductor What is Conductor? Conductor ? How it works Installing Cisco Conductor Configuring Conductor Network Settings Configuring Conductor for a CUCM Configuration MCU Configuration Telepresence Server Telepresence Conductor Server Configuration Configuring TelePresence Conductor for ad hoc conferences Configuring TelePresence Conductor for rendezvous conferences Configuring Unified CM Configuring general settings on Unified CM Locations in Unified CM Unified CM trusts TelePresence Conductor's server certificate SIP trunk security profile Configuring Unified CM for rendezvous conferences Sip Trunk Configuration Conference Bridge Configuration MRG and MRGL Configuration Unified CM normalization scripts Configuring Unified CM for ad hoc conferences Sip Trunk Configuration Route pattern to match the SIP Trunk Configuration Unified CM normalization scripts Configuring the Cisco VCS with TelePresence Conductor Designing a Dial Plan MCU Configuration Telepresence Server Configuring the Cisco VCS Telepresence Conductor Server Configuration Backing Up Conductor Troubleshooting Conductor Overview of Cisco Telepresence Management Server (TMS) Windows Server Installation SQL Server Installation Server Pre-requisites and configuration Installing TMS Installing TMS Provisioning Extensions Initial Configuration Endpoint Configuration Adding Systems to TMS Configuration Templates Setting Configuration VCS Configuration for TMS Direct Endpoint Management VCS/TMS CUCM Configuration for TMS Direct Endpoint Management?CUCM Phonebooks & Phonebook Sources Conference Creation Advanced Conference Settings Booking & Scheduling Participant Types Methods Conference Monitoring Dial Plans, Configuration Templates Scheduler/Smart Scheduler Managing and Troubleshooting Cisco TMS Using the Logs Cisco TMS Ticketing System Troubleshooting VCS Registrations Troubleshooting CUCM Registrations System Maintenance Configuring Cisco Meeting Server (formerly Acano) Setting up CMS Installing Certificates Configuring CUCM with CMS Provision the RTC Client Configuring Meeting Spaces Additional course details: Nexus Humans Advanced TP-CT - Implementing and Configuring Cisco TelePresence Video Suite training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Advanced TP-CT - Implementing and Configuring Cisco TelePresence Video Suite course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

KM423 IBM InfoSphere DataStage v11.5 - Advanced Data Processing
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Experienced DataStage developers seeking training in more advanced DataStage job techniques and who seek techniques for working with complex types of data resources. Overview Use Connector stages to read from and write to database tables Handle SQL errors in Connector stages Use Connector stages with multiple input links Use the File Connector stage to access Hadoop HDFS data Optimize jobs that write to database tables Use the Unstructured Data stage to extract data from Excel spreadsheets Use the Data Masking stage to mask sensitive data processed within a DataStage job Use the Hierarchical stage to parse, compose, and transform XML data Use the Schema Library Manager to import and manage XML schemas Use the Data Rules stage to validate fields of data within a DataStage job Create custom data rules for validating data Design a job that processes a star schema data warehouse with Type 1 and Type 2 slowly changing dimensions This course is designed to introduce you to advanced parallel job data processing techniques in DataStage v11.5. In this course you will develop data techniques for processing different types of complex data resources including relational data, unstructured data (Excel spreadsheets), and XML data. In addition, you will learn advanced techniques for processing data, including techniques for masking data and techniques for validating data using data rules. Finally, you will learn techniques for updating data in a star schema data warehouse using the DataStage SCD (Slowly Changing Dimensions) stage. Even if you are not working with all of these specific types of data, you will benefit from this course by learning advanced DataStage job design techniques, techniques that go beyond those utilized in the DataStage Essentials course. Accessing databases Connector stage overview - Use Connector stages to read from and write to relational tables - Working with the Connector stage properties Connector stage functionality - Before / After SQL - Sparse lookups - Optimize insert/update performance Error handling in Connector stages - Reject links - Reject conditions Multiple input links - Designing jobs using Connector stages with multiple input links - Ordering records across multiple input links File Connector stage - Read and write data to Hadoop file systems Demonstration 1: Handling database errors Demonstration 2: Parallel jobs with multiple Connector input links Demonstration 3: Using the File Connector stage to read and write HDFS files Processing unstructured data Using the Unstructured Data stage in DataStage jobs - Extract data from an Excel spreadsheet - Specify a data range for data extraction in an Unstructured Data stage - Specify document properties for data extraction. Demonstration 1: Processing unstructured data Data masking Using the Data Masking stage in DataStage jobs - Data masking techniques - Data masking policies - Applying policies for masquerading context-aware data types - Applying policies for masquerading generic data types - Repeatable replacement - Using reference tables - Creating custom reference tables Demonstration 1: Data masking Using data rules Introduction to data rules - Using the Data Rules Editor - Selecting data rules - Binding data rule variables - Output link constraints - Adding statistics and attributes to the output information Use the Data Rules stage to valid foreign key references in source data Create custom data rules Demonstration 1: Using data rules Processing XML data Introduction to the Hierarchical stage - Hierarchical stage Assembly editor - Use the Schema Library Manager to import and manage XML schemas Composing XML data - Using the HJoin step to create parent-child relationships between input lists - Using the Composer step Writing Hierarchical data to a relational table Using the Regroup step Consuming XML data - Using the XML Parser step - Propagating columns Topic 6: Transforming XML data - Using the Aggregate step - Using the Sort step - Using the Switch step - Using the H-Pivot step Demonstration 1: Importing XML schemas Demonstration 2: Compose hierarchical data Demonstration 3: Consume hierarchical data Demonstration 4: Transform hierarchical data Updating a star schema database Surrogate keys - Design a job that creates and updates a surrogate key source key file from a dimension table Slowly Changing Dimensions (SCD) stage - Star schema databases - SCD stage Fast Path pages - Specifying purpose codes - Dimension update specification - Design a job that processes a star schema database with Type 1 and Type 2 slowly changing dimensions Demonstration 1: Build a parallel job that updates a star schema database with two dimensions Additional course details: Nexus Humans KM423 IBM InfoSphere DataStage v11.5 - Advanced Data Processing training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the KM423 IBM InfoSphere DataStage v11.5 - Advanced Data Processing course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Mastering Python Programming (TTPS4820)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This introductory-level Python course is geared for experienced users who want to use Python in web development projects, or system administrators and web site administrators who want to use Python to support their server installations, as well as anyone else who wants to automate or simplify common tasks with the use of Python scripts. Basic familiarity with any programming or scripting language would be helpful, along with a working, user-level knowledge of Unix/Linux, Mac, or Windows. Overview This course is approximately 50% hands-on, combining expert lecture, real-world demonstrations and group discussions with machine-based practical labs and exercises. Our engaging instructors and mentors are highly experienced practitioners who bring years of current 'on-the-job' experience into every classroom. Throughout the hands-on course students, will learn to write essential Python scripts using the most current and efficient skills and techniques. Working in a hands-on learning environment, guided by our expert team, attendees will learn to: Create working Python scripts following best practices Use python data types appropriately Read and write files with both text and binary data Search and replace text with regular expressions Get familiar with the standard library and its work-saving modules Use lesser known but powerful Python data types Create 'real-world', professional Python applications Work with dates, times, and calendars Know when to use collections such as lists, dictionaries, and sets Understand Pythonic features such as comprehensions and iterators Write robust code using exception handling Mastering Python Programming is an introductory and beyond-level practical, hands-on Python training course that leads the student from the basics of writing and running Python scripts to more advanced features such as file operations, regular expressions, working with binary data, and using the extensive functionality of Python modules. Extra emphasis is placed on features unique to Python, such as tuples, array slices, and output formatting. This comprehensive, practical course provides an in-depth exploration of working with the programming language, not an academic overview of syntax and grammar. Students will immediately be able to use Python to complete tasks in the real world. An overview of Python What is python? Python Timeline Advantages/Disadvantages of Python Getting help with pydoc The Python Environment Starting Python Using the interpreter Running a Python script Python scripts on Unix/Windows Editors and IDEs Getting Started Using variables Builtin functions Strings Numbers Converting among types Writing to the screen Command line parameters Flow Control About flow control White space Conditional expressions Relational and Boolean operators While loops Alternate loop exits Array types About array types (AKA sequences) Lists and list methods Tuples Indexing and slicing Iterating through a sequence Nested sequences Sequence functions, keywords, and operators List comprehensions Generator Expressions Working with files File overview Opening a text file Reading a text file Writing to a text file Reading and writing raw (binary) data Converting binary data with struct Dictionaries and Sets About dictionaries Creating dictionaries Iterating through a dictionary About sets Creating sets Working with sets Functions Defining functions Parameters Global and local scope Nested functions Returning values Sorting The sorted() function Alternate keys Lambda functions Sorting collections Using operator.itemgetter() Reverse sorting Errors and Exception Handling Syntax errors Exceptions Using try/catch/else/finally Handling multiple exceptions Ignoring exceptions Modules and Packages The import statement Module search path Creating Modules Using packages Function and Module aliases An Introduction to Python Classes About o-o programming Defining classes Constructors Methods Instance data Properties Class methods and data Regular Expressions RE syntax overview RE Objects Searching and matching Compilation flags Groups and special groups Replacing text Splitting strings Using the Standard Library The sys module Launching external programs Math functions Random numbers Reading CSV data Dates and Times Working with dates and times Translating timestamps Parsing dates from text Formatting dates Calendar data Working with the File System Paths, directories, and filenames Checking for existence Permissions and other file attributes Walking directory trees Creating filters with fileinput Using shutil for file operations Advanced Data Handling Defaultdict and Counter Prettyprinting data structures Compressed archives (zip, gzip, tar, etc.) Persistent data Network Programming Using requests Grabbing web content Sending email Using SSH for remote access Using FTP Writing real-life applications Reading input files a la Unix Parsing command-line options Detecting the current platform Implementing logging Additional course details: Nexus Humans Mastering Python Programming (TTPS4820) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Mastering Python Programming (TTPS4820) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Introduction to R Programming
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Business Analysts, Technical Managers, and Programmers Overview This intensive training course helps students learn the practical aspects of the R programming language. The course is supplemented by many hands-on labs which allow attendees to immediately apply their theoretical knowledge in practice. Over the past few years, R has been steadily gaining popularity with business analysts, statisticians and data scientists as a tool of choice for conducting statistical analysis of data as well as supervised and unsupervised machine learning. What is R ? What is R? ? Positioning of R in the Data Science Space ? The Legal Aspects ? Microsoft R Open ? R Integrated Development Environments ? Running R ? Running RStudio ? Getting Help ? General Notes on R Commands and Statements ? Assignment Operators ? R Core Data Structures ? Assignment Example ? R Objects and Workspace ? Printing Objects ? Arithmetic Operators ? Logical Operators ? System Date and Time ? Operations ? User-defined Functions ? Control Statements ? Conditional Execution ? Repetitive Execution ? Repetitive execution ? Built-in Functions ? Summary Introduction to Functional Programming with R ? What is Functional Programming (FP)? ? Terminology: Higher-Order Functions ? A Short List of Languages that Support FP ? Functional Programming in R ? Vector and Matrix Arithmetic ? Vector Arithmetic Example ? More Examples of FP in R ? Summary Managing Your Environment ? Getting and Setting the Working Directory ? Getting the List of Files in a Directory ? The R Home Directory ? Executing External R commands ? Loading External Scripts in RStudio ? Listing Objects in Workspace ? Removing Objects in Workspace ? Saving Your Workspace in R ? Saving Your Workspace in RStudio ? Saving Your Workspace in R GUI ? Loading Your Workspace ? Diverting Output to a File ? Batch (Unattended) Processing ? Controlling Global Options ? Summary R Type System and Structures ? The R Data Types ? System Date and Time ? Formatting Date and Time ? Using the mode() Function ? R Data Structures ? What is the Type of My Data Structure? ? Creating Vectors ? Logical Vectors ? Character Vectors ? Factorization ? Multi-Mode Vectors ? The Length of the Vector ? Getting Vector Elements ? Lists ? A List with Element Names ? Extracting List Elements ? Adding to a List ? Matrix Data Structure ? Creating Matrices ? Creating Matrices with cbind() and rbind() ? Working with Data Frames ? Matrices vs Data Frames ? A Data Frame Sample ? Creating a Data Frame ? Accessing Data Cells ? Getting Info About a Data Frame ? Selecting Columns in Data Frames ? Selecting Rows in Data Frames ? Getting a Subset of a Data Frame ? Sorting (ordering) Data in Data Frames by Attribute(s) ? Editing Data Frames ? The str() Function ? Type Conversion (Coercion) ? The summary() Function ? Checking an Object's Type ? Summary Extending R ? The Base R Packages ? Loading Packages ? What is the Difference between Package and Library? ? Extending R ? The CRAN Web Site ? Extending R in R GUI ? Extending R in RStudio ? Installing and Removing Packages from Command-Line ? Summary Read-Write and Import-Export Operations in R ? Reading Data from a File into a Vector ? Example of Reading Data from a File into A Vector ? Writing Data to a File ? Example of Writing Data to a File ? Reading Data into A Data Frame ? Writing CSV Files ? Importing Data into R ? Exporting Data from R ? Summary Statistical Computing Features in R ? Statistical Computing Features ? Descriptive Statistics ? Basic Statistical Functions ? Examples of Using Basic Statistical Functions ? Non-uniformity of a Probability Distribution ? Writing Your Own skew and kurtosis Functions ? Generating Normally Distributed Random Numbers ? Generating Uniformly Distributed Random Numbers ? Using the summary() Function ? Math Functions Used in Data Analysis ? Examples of Using Math Functions ? Correlations ? Correlation Example ? Testing Correlation Coefficient for Significance ? The cor.test() Function ? The cor.test() Example ? Regression Analysis ? Types of Regression ? Simple Linear Regression Model ? Least-Squares Method (LSM) ? LSM Assumptions ? Fitting Linear Regression Models in R ? Example of Using lm() ? Confidence Intervals for Model Parameters ? Example of Using lm() with a Data Frame ? Regression Models in Excel ? Multiple Regression Analysis ? Summary Data Manipulation and Transformation in R ? Applying Functions to Matrices and Data Frames ? The apply() Function ? Using apply() ? Using apply() with a User-Defined Function ? apply() Variants ? Using tapply() ? Adding a Column to a Data Frame ? Dropping A Column in a Data Frame ? The attach() and detach() Functions ? Sampling ? Using sample() for Generating Labels ? Set Operations ? Example of Using Set Operations ? The dplyr Package ? Object Masking (Shadowing) Considerations ? Getting More Information on dplyr in RStudio ? The search() or searchpaths() Functions ? Handling Large Data Sets in R with the data.table Package ? The fread() and fwrite() functions from the data.table Package ? Using the Data Table Structure ? Summary Data Visualization in R ? Data Visualization ? Data Visualization in R ? The ggplot2 Data Visualization Package ? Creating Bar Plots in R ? Creating Horizontal Bar Plots ? Using barplot() with Matrices ? Using barplot() with Matrices Example ? Customizing Plots ? Histograms in R ? Building Histograms with hist() ? Example of using hist() ? Pie Charts in R ? Examples of using pie() ? Generic X-Y Plotting ? Examples of the plot() function ? Dot Plots in R ? Saving Your Work ? Supported Export Options ? Plots in RStudio ? Saving a Plot as an Image ? Summary Using R Efficiently ? Object Memory Allocation Considerations ? Garbage Collection ? Finding Out About Loaded Packages ? Using the conflicts() Function ? Getting Information About the Object Source Package with the pryr Package ? Using the where() Function from the pryr Package ? Timing Your Code ? Timing Your Code with system.time() ? Timing Your Code with System.time() ? Sleeping a Program ? Handling Large Data Sets in R with the data.table Package ? Passing System-Level Parameters to R ? Summary Lab Exercises Lab 1 - Getting Started with R Lab 2 - Learning the R Type System and Structures Lab 3 - Read and Write Operations in R Lab 4 - Data Import and Export in R Lab 5 - k-Nearest Neighbors Algorithm Lab 6 - Creating Your Own Statistical Functions Lab 7 - Simple Linear Regression Lab 8 - Monte-Carlo Simulation (Method) Lab 9 - Data Processing with R Lab 10 - Using R Graphics Package Lab 11 - Using R Efficiently

AJER - Advanced Junos Enterprise Routing
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course benefits individuals responsible for configuring and monitoring devices running the Junos OS. Overview After successfully completing this course, you should be able to: Describe the various OSPF link-state advertisement (LSA) types. Explain the flooding of LSAs in an OSPF network. Describe the shortest-path-first (SPF) algorithm. Describe OSPF link metrics. Describe the various OSPF authentication methods. Explain the differences between OSPFv2 and OSPFv3. Describe OSPF area types and operations. Configure various OSPF area types. Summarize and restrict routes. Configure OSPF multi-area adjacencies. Configure OSPF virtual links. Explain OSPF external reachability. List useful commands that are used to troubleshoot and verify OSPF. Isolate different OSPF issues. Describe BGP operations. Configure various BGP options. Explain the route selection process for BGP. Describe how to alter the route selection process. Explain the use of routing policies in BGP. Explain how BGP routes are processed. Describe the various BGP attributes and their use. Manipulate common BGP attributes. Review common BGP troubleshooting procedures. List common BGP troubleshooting commands. Identify issues with BGP peering. Explain reasons to use BGP in the Enterprise. Explain how ISP policies can influence external connectivity. Describe three common routing policies for external connectivity in the enterprise. Identify common commands for troubleshooting routing policy. Describe basic multicast terminology. Describe the multicast address space. Describe how RPF is used in a multicast network. Describe the basic functionality of IGMP. Describe the multicast service models and modes. Describe PIM-SM operation and configuration when using the ASM model. Describe PIM-SM operation and configuration when using the SSM model. Verify and troubleshoot multicast. Identify environments that may require a modified CoS implementation. Describe the various CoS components and their respective functions. Explain the CoS processing along with CoS defaults on SRX Series devices. Describe situations in which some CoS features are used in the enterprise. Describe the use of the Real-Time Performance Monitoring tool. Verify and troubleshoot CoS. Describe a traditional Campus network design. Understand the need for a new architectural design. Describe the five key concepts of the Evolved Core. Describe the benefits of a Layer 3-based Campus Networks. Describe Layer 2 tunneling. Explain VXLAN functionality. Describe VXLAN gateways. Describe EVPN features. Describe EVPN operations. This five-day course is designed to provide students with the tools required for implementing, monitoring, and troubleshooting Layer 3 components in an enterprise network. Chapter 1: Course Introduction Course Introduction Chapter 2: OSPF OSPFv2 Review Link-State Advertisements Protocol Operations OSPF Authentication OSPFv3 Lab 1: Configuring and Monitoring OSPF Chapter 3: OSPF Areas Review of OSPF Areas Stub Area Operation Stub Area Configuration NSSA Operation NSSA Configuration Route Summarization Lab 2: Configuring and Monitoring OSPF Areas and Route Summarization Chapter 4: Advanced OSPF Options OSPF Multi-Area Adjacencies Virtual Links External Reachability Lab 3: Configuring and Monitoring Routing Policy and Advanced OSPF Options Chapter 5: Troubleshooting Troubleshooting LSDB Consistency Issues Case Study: Adjacency Issues Lab: Troubleshooting OSPF Chapter 6: BGP Review of BGP BGP Configuration Options BGP Operations BGP Path Selection and Options Lab: Implementing BGP Chapter 7: BGP Attributes and Policy Policy and BGP BGP Attributes Details and Manipulation of Common BGP Path Attributes Lab: BGP Attributes Chapter 8: Troubleshooting BGP BGP Troubleshooting BGP Case Study Lab: Troubleshooting BGP Chapter 9: Enterprise Routing Policies Enterprise BGP Core Network Design Enterprise External Network Deployment Lab: Implementing Enterprise Routing Policies Chapter 10: Troubleshooting Policies Routing Policy Structure Using RegEx Routing Policy Troubleshooting Case Study Lab: Troubleshooting Routing Policies Chapter 11: Introduction to Multicast Overview of Multicast Multicast Addressing RPF IGMP Lab: PIM-SM Chapter 12: Multicast Routing Protocols and SSM Overview of Multicast Routing Protocols PIM-SM Using the ASM Model PIM-SM Using the SSM Model Lab: Implementing PIM-SM Lab: Implementing SSM Chapter 13: Troubleshooting Multicast Multicast Troubleshooting Multicast Case Study Lab: Troubleshooting Multicast Chapter 14: Class of Service CoS Components Review and Case Study CoS Processing and CoS Defaults on the SRX Series Device Policing Virtual Channels Monitoring with Resource Performance Monitoring Lab 9: Implementing CoS Features in the Enterprise Chapter 15: Troubleshooting Class of Service CoS Troubleshooting CoS Case Study Lab: Troubleshooting Class of Service Chapter 16: Enterprise Architectures Traditional Enterprise Networks A New Architecture Key Concepts of the Evolved Core IP Fabric Campus Design Chapter 17: VXLAN Layer 2 Connectivity over a Layer 3 Network VXLAN Overview VXLAN Gateways Chapter 18: EVPN-VXLAN Overview of EVPN EVPN Operations EVPN and VXLAN Chapter 19: Configuring EVPN-VXLAN Configuring EVPN-VXLAN Spine Only network Add IP Fabric leaf nodes to a Spine Only design Configuring a new IP Fabric EVPN-VXLAN network Chapter 20: Migrating to an IP Fabric EVPN Routes Useful EVPN Commands Appendix A: BGP Route Reflection Route Reflection Operation Configuration and Routing Knowledge Lab: BGP Route Reflection (Optional) Appendix B: Troubleshooting IS-IS IS-IS Troubleshooting Lab: Troubleshooting IS-IS and Mixed Environments Additional course details: Nexus Humans AJER - Advanced Junos Enterprise Routing training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the AJER - Advanced Junos Enterprise Routing course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Cisco Administering Collaboration Environments (CLACE)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The primary audience for this course is as follows: Administrator IT support personnel Helpdesk support staff The secondary audience for this course is as follows: Network Engineering Staff Overview Upon completing this course, the learner can meet these overall objectives: Demonstrate an overall understanding of the Cisco Unified Communications Manager (CUCM) system and its environment Configure CUCM to support IP Phones Configure Cisco Unified Communications Manager and IM&Presence to support Cisco Jabber soft client. Configure CUCM to route calls to internal and PSTN destinations Configure User accounts and multi-level administration Demonstrate the use of Self Care Portal functionality Configure user features, including Hunt Groups, Call Pickup, and Call Park. Define the capabilities of and demonstrate the Bulk Administration Tool Define the SMART Licensing model for Cisco Unified Communications Demonstrate the use of the Unified Reporting tool Demonstrate the use of the Dialed Number Analyzer Explain the function of Cisco Unity Connection and the various interfaces that are used to access the system Describe the components that are required for user call processing by Cisco Unity Connection Implement the various features and options that are available to users in Cisco Unity Connection Explore Cisco Unity Connection version features and functions Use the various applications, tools, and reports that are available in Cisco Unity Connection Administering Collaboration Environments (CLACE) is an instructor-led course presented by Skyline-ATS to system administrators and customers involved with the Cisco Unified Communications Manager and Cisco Unity Connection product's day-to-day operation. The CLACE course is the replacement for the CMA / UCA courses. CLACE is a lab-intensive course. The primary focus is learning by performing the configuration tasks. The amount of theory is limited to allow more time for discovery exercises. This course introduces you to the CUCM system, the necessary procedures for administering IP Phones and Users, understanding the Dial Plan, and implementing Features. The course also covers Jabber administration and Cisco Unity Connection administration features, options, and configuration settings. In addition to instructor-led lectures and discussions, you will configure CUCM and Cisco IP Phones in the lab, either in a live classroom or WebEx remote classroom environment. While the CUCM and CUC software used in the class is version 12.5.1, the course material applies to versions 8.x, 9.x, 10.x, 11.x, or 12.x of the applications. The concepts and the lab tasks are the same for most of the software versions. Define Collaboration Technology and Benefits Define Collaboration Benefits Describe On-Premise, Cloud, and Hybrid Deployments Describe On-Premise Collaboration Deployments Describe Cisco's Collaboration Endpoints Describe Cisco Collaboration On-Premise Edge Solutions Describe Cisco's Collaboration On-Premise Conferencing Solutions Describe Cisco Cloud Services Administering Initial Parameters for Cisco Unified Communications Manager Understand the On-Premise Collaboration Deployment Models Describe The Cisco Unified CM Cluster Services Define Network requirements for Collaboration Define Network Services for Collaboration Navigate Cisco Unified CM Discovery 1: Configure Cisco Unified Communications Manager Initial Parameters Explore Cisco Unified CM Groups Discovery 2: Configure the Cisco UCM Core Systems Settings Exploring Endpoints and the Registration Process Identify Cisco Endpoint Solutions Explore the Boot up Process of an Endpoint Describe Power Over Ethernet Discovery 3: Configure an Access Switch for an Endpoint Describe IP Network Settings Discovery 4: Deploy an IP Phone Through Auto and Manual Registration Discovery 5: Administer Endpoints in Cisco Unified Communications Manager Managing Users in Cisco Unified Communications Manager Analyze Cisco UCM Users Types and Settings Describe Methods for Authenticating Cisco UCM Users Discovery 6: Create Local User Accounts Discovery 7: Adding Users in Cisco Unified Communications Manager Describing a Basic Dial Plan Describe the Concepts of a Dial Plan and Call Routing Describe Elements of Call Routing Explore Digit Manipulation and Translation Patterns Discovery 8: Create a Basic Dial Plan Describing Class of Service Explore the Concepts of Class of Control Discovery 9: Explore Partitions and Calling Search Spaces Discovery 10: Explore Private Line Automatic Ringdown (PLAR) Enabling Endpoints and Features Configure a Cisco Jabber Endpoint in Cisco UCM Discovery 11: Implementing Common Endpoint Features (Configuring Hunt Groups and Call Coverage) Explore Mobility Discovery 12: Implement Mobility Implementing Media Resources in Cisco Unified Communications Manager Media Resource Overview Media Resource Selection and Access Control Audio and Video Conference Bridge Devices Audio and Video Conference Bridge Integration Options Discovery 13: Configuring Media Resources Reporting and Maintenance Explore the Troubleshooting Process Describe Reporting and Maintenance Tools Describe the Cisco Real-Time Monitoring Tool Discovery 14: Use Reporting and maintenance Tools Describing Cisco Instant Messaging and Presence Describe Cisco IM and Presence Features and Architecture Clustering Describe Cisco IM and Presence Components and Communication Flows Enabling Jabber Cisco Jabber Deployment Modes Discovery 15: Deploy an On-Premise Cisco Jabber Client for Windows Configure Unity Connection Integration Overview of Cisco Unity Connection Integration SIP Integration Typical Integration Mistakes Integration Considerations Discovery 16: Configure the integration between Cisco Unity Connection and Cisco UCM Discovery 17: Configure Voicemail Users Configuring Cisco Unity Connection Call Handlers Call handler Overview System Call Handler Caller Input Operator Call Handler Goodbye Call Handler Directory Handler Interview Handler Troubleshooting Cisco Unity Connection Overview of Cisco Unity Connection Troubleshooting Options Integration Troubleshooting Tools Cisco Real-Time Monitoring Tool Discovery 18: Troubleshoot Cisco Unity Connection Additional course details: Nexus Humans Cisco Administering Collaboration Environments (CLACE) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Cisco Administering Collaboration Environments (CLACE) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Cisco Implementing and Operating Cisco Security Core Technologies v1.0 (SCOR)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Security engineer Network engineer Network designer Network administrator Systems engineer Consulting systems engineer Technical solutions architect Network manager Cisco integrators and partners Overview After taking this course, you should be able to: Describe information security concepts and strategies within the network Describe common TCP/IP, network application, and endpoint attacks Describe how various network security technologies work together to guard against attacks Implement access control on Cisco ASA appliance and Cisco Firepower Next-Generation Firewall Describe and implement basic email content security features and functions provided by Cisco Email Security Appliance Describe and implement web content security features and functions provided by Cisco Web Security Appliance Describe Cisco Umbrella security capabilities, deployment models, policy management, and Investigate console Introduce VPNs and describe cryptography solutions and algorithms Describe Cisco secure site-to-site connectivity solutions and explain how to deploy Cisco Internetwork Operating System (Cisco IOS) Virtual Tunnel Interface (VTI)-based point-to-point IPsec VPNs, and point-to-point IPsec VPN on the Cisco ASA and Cisco Firepower Next-Generation Firewall (NGFW) Describe and deploy Cisco secure remote access connectivity solutions and describe how to configure 802.1X and Extensible Authentication Protocol (EAP) authentication Provide basic understanding of endpoint security and describe Advanced Malware Protection (AMP) for Endpoints architecture and basic features Examine various defenses on Cisco devices that protect the control and management plane Configure and verify Cisco IOS software Layer 2 and Layer 3 data plane controls Describe Cisco Stealthwatch Enterprise and Stealthwatch Cloud solutions Describe basics of cloud computing and common cloud attacks and how to secure cloud environment The Implementing and Operating Cisco Security Core Technologies (SCOR) v1.0 course helps you prepare for the Cisco© CCNP© Security and CCIE© Security certifications and for senior-level security roles. In this course, you will master the skills and technologies you need to implement core Cisco security solutions to provide advanced threat protection against cybersecurity attacks. You will learn security for networks, cloud and content, endpoint protection, secure network access, visibility, and enforcements. You will get extensive hands-on experience deploying Cisco Firepower© Next-Generation Firewall and Cisco Adaptive Security Appliance (ASA) Firewall; configuring access control policies, mail policies, and 802.1X Authentication; and more. You will get introductory practice on Cisco Stealthwatch© Enterprise and Cisco Stealthwatch Cloud threat detection features. This course, including the self-paced material, helps prepare you to take the exam, Implementing and Operating Cisco Security Core Technologies (350-701 SCOR), which leads to the new CCNP Security, CCIE Security, and the Cisco Certified Specialist - Security Core certifications. Describing Information Security Concepts* Information Security Overview Assets, Vulnerabilities, and Countermeasures Managing Risk Vulnerability Assessment Understanding Common Vulnerability Scoring System (CVSS) Describing Common TCP/IP Attacks* Legacy TCP/IP Vulnerabilities IP Vulnerabilities Internet Control Message Protocol (ICMP) Vulnerabilities TCP Vulnerabilities User Datagram Protocol (UDP) Vulnerabilities Attack Surface and Attack Vectors Reconnaissance Attacks Access Attacks Man-in-the-Middle Attacks Denial of Service and Distributed Denial of Service Attacks Reflection and Amplification Attacks Spoofing Attacks Dynamic Host Configuration Protocol (DHCP) Attacks Describing Common Network Application Attacks* Password Attacks Domain Name System (DNS)-Based Attacks DNS Tunneling Web-Based Attacks HTTP 302 Cushioning Command Injections SQL Injections Cross-Site Scripting and Request Forgery Email-Based Attacks Describing Common Endpoint Attacks* Buffer Overflow Malware Reconnaissance Attack Gaining Access and Control Gaining Access via Social Engineering Gaining Access via Web-Based Attacks Exploit Kits and Rootkits Privilege Escalation Post-Exploitation Phase Angler Exploit Kit Describing Network Security Technologies Defense-in-Depth Strategy Defending Across the Attack Continuum Network Segmentation and Virtualization Overview Stateful Firewall Overview Security Intelligence Overview Threat Information Standardization Network-Based Malware Protection Overview Intrusion Prevention System (IPS) Overview Next Generation Firewall Overview Email Content Security Overview Web Content Security Overview Threat Analytic Systems Overview DNS Security Overview Authentication, Authorization, and Accounting Overview Identity and Access Management Overview Virtual Private Network Technology Overview Network Security Device Form Factors Overview Deploying Cisco ASA Firewall Cisco ASA Deployment Types Cisco ASA Interface Security Levels Cisco ASA Objects and Object Groups Network Address Translation Cisco ASA Interface Access Control Lists (ACLs) Cisco ASA Global ACLs Cisco ASA Advanced Access Policies Cisco ASA High Availability Overview Deploying Cisco Firepower Next-Generation Firewall Cisco Firepower NGFW Deployments Cisco Firepower NGFW Packet Processing and Policies Cisco Firepower NGFW Objects Cisco Firepower NGFW Network Address Translation (NAT) Cisco Firepower NGFW Prefilter Policies Cisco Firepower NGFW Access Control Policies Cisco Firepower NGFW Security Intelligence Cisco Firepower NGFW Discovery Policies Cisco Firepower NGFW IPS Policies Cisco Firepower NGFW Malware and File Policies Deploying Email Content Security Cisco Email Content Security Overview Simple Mail Transfer Protocol (SMTP) Overview Email Pipeline Overview Public and Private Listeners Host Access Table Overview Recipient Access Table Overview Mail Policies Overview Protection Against Spam and Graymail Anti-virus and Anti-malware Protection Outbreak Filters Content Filters Data Loss Prevention Email Encryption Deploying Web Content Security Cisco Web Security Appliance (WSA) Overview Deployment Options Network Users Authentication Secure HTTP (HTTPS) Traffic Decryption Access Policies and Identification Profiles Acceptable Use Controls Settings Anti-Malware Protection Deploying Cisco Umbrella* Cisco Umbrella Architecture Deploying Cisco Umbrella Cisco Umbrella Roaming Client Managing Cisco Umbrella Cisco Umbrella Investigate Overview and Concepts Explaining VPN Technologies and Cryptography VPN Definition VPN Types Secure Communication and Cryptographic Services Keys in Cryptography Public Key Infrastructure Introducing Cisco Secure Site-to-Site VPN Solutions Site-to-Site VPN Topologies IPsec VPN Overview IPsec Static Crypto Maps IPsec Static Virtual Tunnel Interface Dynamic Multipoint VPN Cisco IOS FlexVPN Deploying Cisco IOS VTI-Based Point-to-Point IPsec VPNs Cisco IOS VTIs Static VTI Point-to-Point IPsec Internet Key Exchange (IKE) v2 VPN Configuration Deploying Point-to-Point IPsec VPNs on the Cisco ASA and Cisco Firepower NGFW Point-to-Point VPNs on the Cisco ASA and Cisco Firepower NGFW Cisco ASA Point-to-Point VPN Configuration Cisco Firepower NGFW Point-to-Point VPN Configuration Introducing Cisco Secure Remote Access VPN Solutions Remote Access VPN Components Remote Access VPN Technologies Secure Sockets Layer (SSL) Overview Deploying Remote Access SSL VPNs on the Cisco ASA and Cisco Firepower NGFW Remote Access Configuration Concepts Connection Profiles Group Policies Cisco ASA Remote Access VPN Configuration Cisco Firepower NGFW Remote Access VPN Configuration Explaining Cisco Secure Network Access Solutions Cisco Secure Network Access Cisco Secure Network Access Components AAA Role in Cisco Secure Network Access Solution Cisco Identity Services Engine Cisco TrustSec Describing 802.1X Authentication 802.1X and Extensible Authentication Protocol (EAP) EAP Methods Role of Remote Authentication Dial-in User Service (RADIUS) in 802.1X Communications RADIUS Change of Authorization Configuring 802.1X Authentication Cisco Catalyst© Switch 802.1X Configuration Cisco Wireless LAN Controller (WLC) 802.1X Configuration Cisco Identity Services Engine (ISE) 802.1X Configuration Supplicant 802.1x Configuration Cisco Central Web Authentication Describing Endpoint Security Technologies* Host-Based Personal Firewall Host-Based Anti-Virus Host-Based Intrusion Prevention System Application Whitelists and Blacklists Host-Based Malware Protection Sandboxing Overview File Integrity Checking Deploying Cisco Advanced Malware Protection (AMP) for Endpoints* Cisco AMP for Endpoints Architecture Cisco AMP for Endpoints Engines Retrospective Security with Cisco AMP Cisco AMP Device and File Trajectory Managing Cisco AMP for Endpoints Introducing Network Infrastructure Protection* Identifying Network Device Planes Control Plane Security Controls Management Plane Security Controls Network Telemetry Layer 2 Data Plane Security Controls Layer 3 Data Plane Security Controls Deploying Control Plane Security Controls* Infrastructure ACLs Control Plane Policing Control Plane Protection Routing Protocol Security Deploying Layer 2 Data Plane Security Controls* Overview of Layer 2 Data Plane Security Controls Virtual LAN (VLAN)-Based Attacks Mitigation Sp

MB-335T00: Microsoft Dynamics 365 Supply Chain Management, Expert
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for the Dynamics 365 Supply Chain Management Functional Consultant Expert or those whose role includes implementing and configuring advanced features of Dynamics 365 Supply Chain Management. Overview Objectives: Create products as type Item and Service. Set up product unit conversions. Set up transfer orders Set up default order settings. Create product masters with predefined variants. Create and set up category hierarchies. Create product attributes. Create bill of materials using BOM designer Discrete manufacturing concepts Production order statuses Production stages Bill of materials (BOM) Resources Routes and operations Configure commodity pricing in Supply Chain Management. Configure product compliance in Supply Chain Management. Configure commodity pricing in Supply Chain Management. Configure product compliance in Supply Chain Management. Configure process manufacturing. Create and configure catch weight items. Configure approved vendors. Understand the features in engineering change management. Learn how the end-to-end engineering change management process works. Set up engineering organizations. Work with product versioning. Create dimension groups by using the version dimensions. Create product life cycle states. Use engineering categories. Set up engineering change severities and severity rules. Set up product owners. Use a workflow with engineering change management. Create an engineering change request. Learn about business impacts. Create an engineering change order. Important terminology to help you understand the concepts and processes that are associated with product configuration. Product configuration end-to-end scenario. Different areas that span the product configuration process. The product configuration model. How to build a product configuration model. Configure the costing sheet. Perform BOM calculation and analyze costs by using the costing sheet. IoT intelligence and insights in Supply Chain Management This course is designed to build your in Dynamics 365 Supply Chain Management application knowledge. This course will cover the most important features and functionalities needed by Dynamics 365 Supply Chain Management functional consultant including: The product information and how to configure, create, and manage your product and inventory. Supply chain management configuration and processing. The transportation management features, and the warehouse management features. Asset Management functionalities. Master planning configuration and processing. Sales and procurement processes. Create products and product masters in Dynamics 365 Supply Chain Management Product information workspace Concept of a product Create products Set up unit conversions Batch disposition codes Default order settings Define products as not stocked Create product masters with variants Gain productivity by using the Variant suggestions page Create and set up category hierarchies and attributes Set up item pricing Create bill of materials in Dynamics 365 Supply Chain Management Work with the BOM designer BOM and formula versions BOM line types BOM levels Get started with discrete manufacturing in Dynamics 365 Supply Chain Management Discrete manufacturing life cycle Master planning and planned production orders Bills of materials Working with BOM and item configurations Create a bill of materials Production orders Work with commodity pricing and compliance in Dynamics 365 Supply Chain Management Configure commodity pricing Configure product compliance Configure process manufacturing in Dynamics 365 Supply Chain Management Process manufacturing item types Production type setup Set up packaging and batch attributes Shelf life related setup Item model group, product compliance, and approved vendors Catch weight Transaction adjustments Catch weight item handling policy Catch weight tags Configure approved vendors Get started with Engineering Change Management for Dynamics 365 Supply Chain Management Overview of features End-to-end walkthrough of features Set up versioned products in Dynamics 365 Supply Chain Management Create an engineering organization Create nomenclature for product versions Create product version number rules Create product dimension groups by using the version dimension Create product life cycle states Engineering attributes Product readiness policies Product release policies Create engineering categories Configure engineering change management for Dynamics 365 Supply Chain Management Set up engineering change severities Set up severity rule sets Set up product owners Engineering workflows Request and follow up with product changes in Dynamics 365 Supply Chain Management Engineering change requests Engineering change orders up with product changes in Dynamics 365 Supply Chain Management Get started with product configuration in Dynamics 365 Supply Chain Management Elements of a product configuration model Expression constraints and table constraints in product configuration models Validate and test a product configuration model Finalize a model for configuration Set up a product configuration model Calculations for product configuration models Solver strategy for product configuration Reuse product configurations Release a product configuration model Customize a product configuration model Work with the costing sheet in Dynamics 365 Supply Chain Management Costing versions Cost groups Calculation groups Costing sheets BOM calculations BOM Measurements BOM Reports Configure formulas for process manufacturing in Dynamics 365 Supply Chain Management Formulas, formula lines, and formula versions Formula features Approve and activate formulas and formula versions Use step consumption Coproducts By-products Burden allocation Planning items Get started with production control in Dynamics 365 Supply Chain Management Core concepts in production control Understand unified manufacturing Manufacturing principles Overview of the production process and production life cycle Batch orders Discrete manufacturing Process manufacturing Lean manufacturing Configure production control for unified manufacturing Capacity planning Integration between the General ledger and the Production control modules IoT intelligence and insights Describe the value proposition for mixed-reality Guides for production floor workers Use warehouse management for manufacturing in Dynamics 365 Supply Chain Management Production input location Production output location Staging and order picking Release BOM and formula lines to the warehouse Cross-docking Planned cross docking Visibility into material exceptions Work with manufacturing execution in Dynamics 365 Supply Chain Management Understand the manufacturing executions Identify roles in manufacturing execution Planning consideration for manufacturing execution Configure manufacturing execution Setup time and attendance for manufacturing execution processes Control production with manufacturing execution Create and process report as finished journals with co-products and by-products Calculate and approve raw time registrations Report as finished from the job card device Get started with Asset Management for Dynamics 365 Supply Chain Management Asset Management terminology and concepts Functional locations and assets Assets and work orders Install the Asset Management mobile workspace Use the Asset Management mobile workspace Asset Management integration capabilities Integrate Asset Management with Dynamics 365 Guides Schedule work orders in Asset Management for Dynamics 365 Supply Chain Management Configure workers for work order scheduling Schedule and dispatch work orders Calculate capacity load on scheduled work orders Configure and perform the procure-to-purchase process in Dynamics 365 Supply Chain Management Procurement scenario Overview of the procure-to-purchase process Set up procurement categories Use procurement catalogs Create a purchase requisition Create and process a request for quotation Create purchase orders Vendor categories and catalogs Evaluate a vendor and put a vendor on hold Use purchasing policies Configure activity-based subcontracting and production flow costing in Dynamics 365 Supply Chain Management Subcontracting capabilities Subcontracting a vendor Subcontracting service Transfer activities as subcontracting activities Subcontracting as an alternate resource Cost accounting of subcontracted services Subcontracting cost flow Backflush costing Products and material in Work in Progress Standard cost Costing lean manufacturing Calculation of standard cost Calculate unused quantities Calculation of production variances to standard cost Ledger entries created from processing a production flow Configure and use agreements in Dynamics 365 Supply Chain Management Work with trade agreements Create sales agreements Create purchase agreements Configure trade allowance management Configure brokerage contract management Configure royalty contract management Configure vendor rebates Rebate management module Work with capa Additional course details: Nexus Humans MB-335T00: Microsoft Dynamics 365 Supply Chain Management, Expert training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the MB-335T00: Microsoft Dynamics 365 Supply Chain Management, Expert course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

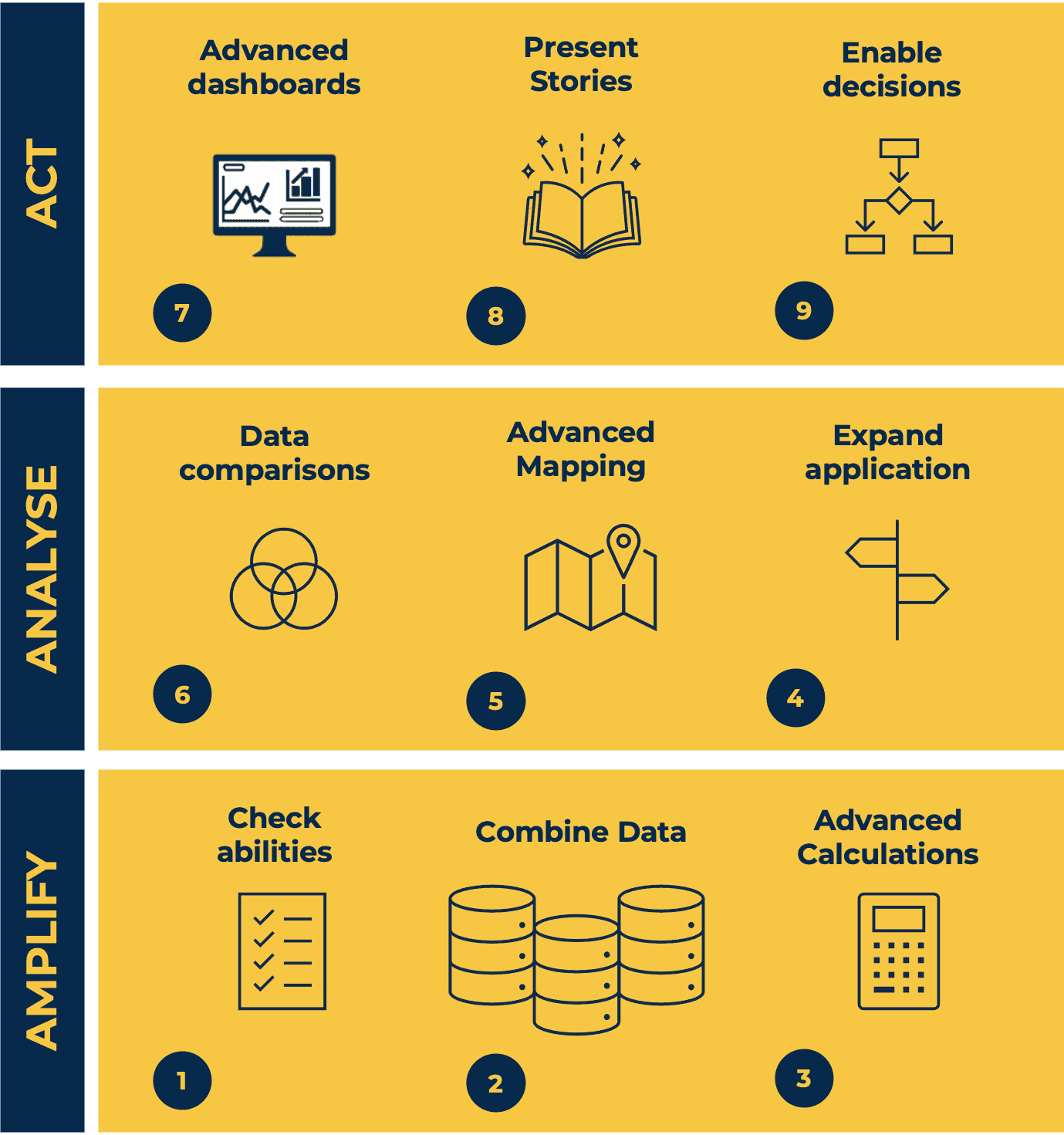
Tableau Desktop Training - Analyst
By Tableau Training Uk
This Tableau Desktop Training intermediate course is designed for the professional who has a solid foundation with Tableau and is looking to take it to the next level. For Private options, online or in-person, please send us details of your requirements: This Tableau Desktop training intermediate course is designed for the professional who has a solid foundation with Tableau and is looking to take it to the next level. Attendees should have a good understanding of the fundamental concepts of building Tableau worksheets and dashboards typically achieved from having attended our Tableau Desktop Foundation Course. At the end of this course you will be able to communicate insights more effectively, enabling your organisation to make better decisions, quickly. The Tableau Desktop Analyst training course is aimed at people who are used to working with MS Excel or other Business Intelligence tools and who have preferably been using Tableau already for basic reporting. The course is split into 3 phases and 9 modules: Phase 1: AMPLIFY MODULE 1: CHECK ABILITIES Revision – What I Should Know What is possibleHow does Tableau deal with dataKnow your way aroundHow do we format chartsHow Tableau deals with datesCharts that compare multiple measuresCreating Tables MODULE 2: COMBINE DATA Relationships Joining Tables – Join Types, Joining tables within the same database, cross database joins, join calculations Blending – How to create a blend with common fields, Custom defined Field relationships and mismatched element names, Calculated fields in blended data sources Unions – Manual Unions and mismatched columns, Wildcard unions Data Extracts – Creating & Editing Data extracts MODULE 3: ADVANCED CALCULATIONS Row Level v Aggregations Aggregating dimensions in calculations Changing the Level of Detail (LOD) of calculations – What, Why, How Adding Table Calculations Phase 2: ANALYSE MODULE 4: EXPAND APPLICATION Making things dynamic with parameters Sets Trend Lines How do we format charts Forecasting MODULE 5: ADVANCED MAPPING Using your own images for spatial analysis Mapping with Spatial files MODULE 6: DATA COMPARISONS Advanced Charts Bar in Bar charts Bullet graphs Creating Bins and Histograms Creating a Box & Whisker plot Phase 3: ACT MODULE 7: ADVANCED DASHBOARDS Using the dashboard interface and Device layout Dashboard Actions and Viz In tooltips Horizontal & Vertical containers Navigate between dashboards MODULE 8: PRESENT STORIES Telling data driven stories MODULE 9: ENABLE DECISIONS What is Tableau Server Publishing & Permissions How can your users engage with content This training course includes over 25 hands-on exercises and quizzes to help participants “learn by doing” and to assist group discussions around real-life use cases. Each attendee receives a login to our extensive training portal which covers the theory, practical applications and use cases, exercises, solutions and quizzes in both written and video format. Students must bring their own laptop with an active version of Tableau Desktop 2018.2 (or later) pre-installed. What People Are Saying About This Course “Course was fantastic, and completely relevant to the work I am doing with Tableau. I particularly liked Steve’s method of teaching and how he applied the course material to ‘real-life’ use-cases.”Richard W., Dashboard Consulting Ltd “This course was extremely useful and excellent value. It helped me formalise my learning and I have taken a lot of useful tips away which will help me in everyday work.” Lauren M., Baillie Gifford “I would definitely recommend taking this course if you have a working knowledge of Tableau. Even the little tips Steve explains will make using Tableau a lot easier. Looking forward to putting what I’ve learned into practice.”Aron F., Grove & Dean “Steve is an excellent teacher and has a vast knowledge of Tableau. I learned a huge amount over the two days that I can immediately apply at work.”John B., Mporium “Steve not only provided a comprehensive explanation of the content of the course, but also allowed time for discussing particular business issues that participants may be facing. That was really useful as part of my learning process.”Juan C., Financial Conduct Authority “Course was fantastic, and completely relevant to the work I am doing with Tableau. I particularly liked Steve’s method of teaching and how he applied the course material to ‘real-life’ use-cases.”Richard W., Dashboard Consulting Ltd “This course was extremely useful and excellent value. It helped me formalise my learning and I have taken a lot of useful tips away which will help me in everyday work.” Lauren M., Baillie Gifford “I would definitely recommend taking this course if you have a working knowledge of Tableau. Even the little tips Steve explains will make using Tableau a lot easier. Looking forward to putting what I’ve learned into practice.”Aron F., Grove & Dean “Steve is an excellent teacher and has a vast knowledge of Tableau. I learned a huge amount over the two days that I can immediately apply at work.”John B., Mporium
Building services and maintenance - introduction (In-House)
By The In House Training Company
To provide a fundamental understanding of building services in the context of: The working environment The success of the core business The health and safety of the occupants Operating cost and environmental impact The optimisation of cost and value Strategies for continuous improvement DAY ONE 1 Building services fundamentals The function of services in commercial buildings and their importance to the core businessElectrical servicesLightingHeatingVentilation and air conditioningLiftsWater Understanding IT and communication systems Practical exercises 2 The provision of comfort and safety Statutory requirementsHealth and safety legislationControl of contractorsRisk assessmentFire precautionsLegionella, sick building and other risks Business requirementsUnderstanding user requirementsMatching systems to business needs Practical exercises 3 Getting the design right What the FM needs to know about design and its procurementSuccessful space planningRelationship between services, space planning and designGetting the brief rightSupplier selection and management Practical exercises DAY TWO 4 Operation and maintenance Why maintain?Maintenance contractsInput and output specificationsResource optionsContracts - principal elementsTendering - key stepsSelection criteriaOperational criteriaMaintenance trends Performance-based service provisionInput and output specificationsKPIs and thresholdsRisk containmentValue-add opportunitiesPerformance contract strategy Practical exercises 5 Contingency planning Being ready for the unexpected Identifying and reducing riskInternal risksExternal risksIdentifying threats at your site Managing riskProtective systemsOccupier obligationsFire managementTesting Practical exercises 6 Commissioning services systems Physical commissioning Common problems Typical costs Commissioning stages Continuous commissioning Energy efficiency and the scope for environmental improvement Practical exercises 7 Satisfying the occupants Obtaining and responding to feedbackWhen to get feedbackWhyHowWhat to do with it Practical exercises 8 'Air time' Sharing experience and addressing specific issues of interest to participants Course review Close
