- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
3041 Software Development courses delivered Online
WD515G Create, Secure, and Publish APIs with IBM API Connect 10
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for API developers. Overview Configure services in Cloud Manager for an on-premises installation of API Connect Create a catalog and Developer Portal Create consumer and provider organizations Create, test, and publish SOAP, REST, and GraphQL APIs Create message processing policies that transform API requests and responses Authorize client API requests with security definitions Enforce an OAuth flow with an OAuth 2.0 API security provider Perform advanced testing of APIs by using the Test tab and the Local Test Environment Define products and plans in API Manager Stage, publish, version, migrate, deprecate, and retire products and APIs Manage member roles and permissions in the Developer Portal Create an application and subscribe to a plan Review API analytics in the Developer Portal Review analytics dashboards and visualizations in API Manager Customize the Developer Portal This course teaches you how to configure a newly built API Connect 10 environment. You are taught how to configure a catalog with the gateway, portal, and analytics services and set up the environment for API development. You then define API interfaces according to the OpenAPI specification. You build SOAP and REST based APIs along with a GraphQL API. You assemble message processing policies and define client authorization schemes, such as OAuth 2.0, in the API definition. You verify the proper sequencing of policies in the assembly tester and further test your APIs in the new Test tab and Local Test Environment. After building and testing your APIs, you publish them and make them available on the Developer Portal. You manage all aspects of the provider organization in the API Manager user interface to create, publish, version, and retire API artifacts such as products, plans and APIs themselves. You also learn how to manage consumer organizations who use the APIs that are made available on the Developer Portal. You learn how to add members to the consumer organization that provides access to the APIs on the Developer Portal. You learn how the layout of the Developer Portal can be customized. Finally, you call the APIs on the secure gateway and you view the graphs and metrics of API usage. Course Outline Introduction to IBM API Connect V10 Exercise: Reviewing the API Connect development and runtime environments Managing catalogs and organizations Exercise: Managing catalogs and consumer organizations Defining APIs in API Manager Exercise: Defining an API that calls an existing SOAP service Defining a REST API in API Manager Exercise: Defining a REST API from a target service Assembling message processing policies Exercise: Assembling message processing policies Declaring client authorization requirements Creating an OAuth 2.0 provider Exercise: Implementing OAuth 2.0 security Testing and debugging APIs Exercise: Introduction to the Test tab Creating and testing a GraphQL API Exercise: Creating and testing a GraphQL API Testing an API in the Local Test Environment Exercise: Testing an API in the Local Test Environment Publishing and managing products and APIs Exercise: Define and publish an API product The product lifecycle Exercise: Subscribing and testing APIs in the Developer Portal Exercise: Managing and approving API Products Subscribing and testing APIs in the Developer Portal API Analytics Exercise: Calling an API on the gateway and monitoring API usage Customizing the Developer Portal Exercise: Customizing the Developer Portal Additional course details: Nexus Humans WD515G Create, Secure, and Publish APIs with IBM API Connect 10 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the WD515G Create, Secure, and Publish APIs with IBM API Connect 10 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Professional Certificate Course in Requirements Control and Change Management in London 2024
4.9(261)By Metropolitan School of Business & Management UK
This Professional Certificate Course in Requirements Control and Change Management provides a comprehensive overview, emphasizing the significance of mastering skills in effective change management. Participants will identify processes, tools, and differentiate between minor and major changes, while also learning to navigate challenges and pitfalls through practical solutions. After the successful completion of the course, you will be able to learn about the following:• Understand the importance of requirements control and change management.• Identify the different processes and tools used for requirements control and change management.• Understand the difference between minor and major changes.• Identify the challenges and pitfalls of requirements control and change management, and how to address them. This Professional Certificate Course in Requirements Control and Change Management offers a comprehensive understanding of the vital principles, processes, and tools involved, covering distinctions between minor and major changes, and providing strategies to address challenges and pitfalls in effective requirements control and change management. This Professional Certificate Course in Requirements Control and Change Management equips participants to comprehend the significance, processes, and tools involved, distinguishing between minor and major changes, while addressing challenges and pitfalls through effective strategies. Course Structure and Assessment Guidelines Watch this video to gain further insight. Navigating the MSBM Study Portal Watch this video to gain further insight. Interacting with Lectures/Learning Components Watch this video to gain further insight. Project Requirements Control and Change Management Self-paced pre-recorded learning content on this topic. Requirements Control and Change Management Put your knowledge to the test with this quiz. Read each question carefully and choose the response that you feel is correct. All MSBM courses are accredited by the relevant partners and awarding bodies. Please refer to MSBM accreditation in about us for more details. There are no strict entry requirements for this course. Work experience will be added advantage to understanding the content of the course.The certificate is designed to enhance the learner's knowledge in the field. This certificate is for everyone eager to know more and get updated on current ideas in their respective field. We recommend this certificate for the following audience, Project Managers Business Analysts Software Developers Quality Assurance Professionals System Architects Product Managers Requirements Engineers IT Professionals Stakeholders in Project Management Professionals involved in Change Management Average Completion Time 2 Weeks Accreditation 3 CPD Hours Level Advanced Start Time Anytime 100% Online Study online with ease. Unlimited Access 24/7 unlimited access with pre-recorded lectures. Low Fees Our fees are low and easy to pay online.

Machine Learning Masterclass
By Study Plex
Recognised Accreditation This course is accredited by continuing professional development (CPD). CPD UK is globally recognised by employers, professional organisations, and academic institutions, thus a certificate from CPD Certification Service creates value towards your professional goal and achievement. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. What is CPD? Employers, professional organisations, and academic institutions all recognise CPD, therefore a credential from CPD Certification Service adds value to your professional goals and achievements. Benefits of CPD Improve your employment prospects Boost your job satisfaction Promotes career advancement Enhances your CV Provides you with a competitive edge in the job market Demonstrate your dedication Showcases your professional capabilities What is IPHM? The IPHM is an Accreditation Board that provides Training Providers with international and global accreditation. The Practitioners of Holistic Medicine (IPHM) accreditation is a guarantee of quality and skill. Benefits of IPHM It will help you establish a positive reputation in your chosen field You can join a network and community of successful therapists that are dedicated to providing excellent care to their client You can flaunt this accreditation in your CV It is a worldwide recognised accreditation What is Quality Licence Scheme? This course is endorsed by the Quality Licence Scheme for its high-quality, non-regulated provision and training programmes. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. Benefits of Quality License Scheme Certificate is valuable Provides a competitive edge in your career It will make your CV stand out Course Curriculum Welcome to the course Introduction 00:02:00 Setting up R Studio and R crash course Installing R and R studio 00:05:00 Basics of R and R studio 00:10:00 Packages in R 00:10:00 Inputting data part 1: Inbuilt datasets of R 00:04:00 Inputting data part 2: Manual data entry 00:03:00 Inputting data part 3: Importing from CSV or Text files 00:06:00 Creating Barplots in R 00:13:00 Creating Histograms in R 00:06:00 Basics of Statistics Types of Data 00:04:00 Types of Statistics 00:02:00 Describing the data graphically 00:11:00 Measures of Centers 00:07:00 Measures of Dispersion 00:04:00 Introduction to Machine Learning Introduction to Machine Learning 00:16:00 Building a Machine Learning Model 00:08:00 Data Preprocessing for Regression Analysis Gathering Business Knowledge 00:03:00 Data Exploration 00:03:00 The Data and the Data Dictionary 00:07:00 Importing the dataset into R 00:03:00 Univariate Analysis and EDD 00:03:00 EDD in R 00:12:00 Outlier Treatment 00:04:00 Outlier Treatment in R 00:04:00 Missing Value imputation 00:03:00 Missing Value imputation in R 00:03:00 Seasonality in Data 00:03:00 Bi-variate Analysis and Variable Transformation 00:16:00 Variable transformation in R 00:09:00 Non Usable Variables 00:04:00 Dummy variable creation: Handling qualitative data 00:04:00 Dummy variable creation in R 00:05:00 Correlation Matrix and cause-effect relationship 00:10:00 Correlation Matrix in R 00:08:00 Linear Regression Model The problem statement 00:01:00 Basic equations and Ordinary Least Squared (OLS) method 00:08:00 Assessing Accuracy of predicted coefficients 00:14:00 Assessing Model Accuracy - RSE and R squared 00:07:00 Simple Linear Regression in R 00:07:00 Multiple Linear Regression 00:05:00 The F - statistic 00:08:00 Interpreting result for categorical Variable 00:05:00 Multiple Linear Regression in R 00:07:00 Test-Train split 00:09:00 Bias Variance trade-off 00:06:00 Test-Train Split in R 00:08:00 Regression models other than OLS Linear models other than OLS 00:04:00 Subset Selection techniques 00:11:00 Subset selection in R 00:07:00 Shrinkage methods - Ridge Regression and The Lasso 00:07:00 Ridge regression and Lasso in R 00:12:00 Classification Models: Data Preparation The Data and the Data Dictionary 00:08:00 Importing the dataset into R 00:03:00 EDD in R 00:11:00 Outlier Treatment in R 00:04:00 Missing Value imputation in R 00:03:00 Variable transformation in R 00:06:00 Dummy variable creation in R 00:05:00 The Three classification models Three Classifiers and the problem statement 00:03:00 Why can't we use Linear Regression? 00:04:00 Logistic Regression Logistic Regression 00:08:00 Training a Simple Logistic model in R 00:03:00 Results of Simple Logistic Regression 00:05:00 Logistic with multiple predictors 00:02:00 Training multiple predictor Logistic model in R 00:01:00 Confusion Matrix 00:03:00 Evaluating Model performance 00:07:00 Predicting probabilities, assigning classes and making Confusion Matrix in R 00:06:00 Linear Discriminant Analysis Linear Discriminant Analysis 00:09:00 Linear Discriminant Analysis in R 00:09:00 K-Nearest Neighbors Test-Train Split 00:09:00 Test-Train Split in R 00:08:00 K-Nearest Neighbors classifier 00:08:00 K-Nearest Neighbors in R 00:08:00 Comparing results from 3 models Understanding the results of classification models 00:06:00 Summary of the three models 00:04:00 Simple Decision Trees Basics of Decision Trees 00:10:00 Understanding a Regression Tree 00:10:00 The stopping criteria for controlling tree growth 00:03:00 The Data set for this part 00:03:00 Importing the Data set into R 00:06:00 Splitting Data into Test and Train Set in R 00:05:00 Building a Regression Tree in R 00:14:00 Pruning a tree 00:04:00 Pruning a Tree in R 00:09:00 Simple Classification Tree Classification Trees 00:06:00 The Data set for Classification problem 00:01:00 Building a classification Tree in R 00:09:00 Advantages and Disadvantages of Decision Trees 00:01:00 Ensemble technique 1 - Bagging Bagging 00:06:00 Bagging in R 00:06:00 Ensemble technique 2 - Random Forest Random Forest technique 00:04:00 Random Forest in R 00:04:00 Ensemble technique 3 - GBM, AdaBoost and XGBoost Boosting techniques 00:07:00 Gradient Boosting in R 00:07:00 AdaBoosting in R 00:09:00 XGBoosting in R 00:16:00 Maximum Margin Classifier Content flow 00:01:00 The Concept of a Hyperplane 00:05:00 Maximum Margin Classifier 00:03:00 Limitations of Maximum Margin Classifier 00:02:00 Support Vector Classifier Support Vector classifiers 00:10:00 Limitations of Support Vector Classifiers 00:01:00 Support Vector Machines Kernel Based Support Vector Machines 00:06:00 Creating Support Vector Machine Model in R The Data set for the Classification problem 00:01:00 Importing Data into R 00:08:00 Test-Train Split 00:09:00 Classification SVM model using Linear Kernel 00:16:00 Hyperparameter Tuning for Linear Kernel 00:06:00 Polynomial Kernel with Hyperparameter Tuning 00:10:00 Radial Kernel with Hyperparameter Tuning 00:06:00 The Data set for the Regression problem 00:03:00 SVM based Regression Model in R 00:11:00 Assessment Assessment - Machine Learning Masterclass 00:10:00 Certificate of Achievement Certificate of Achievement 00:00:00 Get Your Insurance Now Get Your Insurance Now 00:00:00 Feedback Feedback 00:00:00
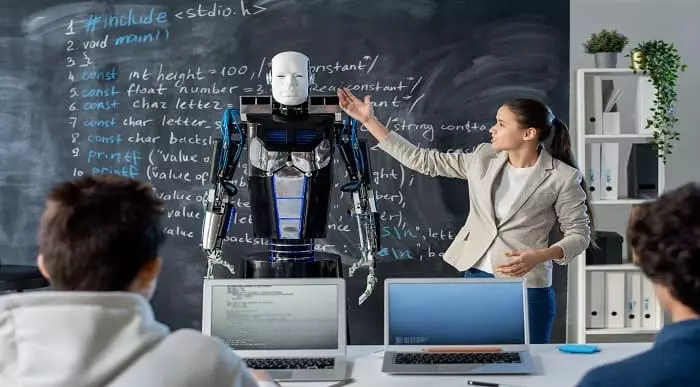
Project on Deep Learning - Artificial Neural Network Course
By One Education
Step into the intricate world of artificial neural networks with a course that sheds light on one of the most dynamic branches of deep learning. Designed for those keen to explore the structure, function and logic behind intelligent systems, this course blends academic insight with a clear, structured approach to the evolving digital frontier. From perceptrons to multilayer networks, it offers a layered understanding of how machines mimic the human brain’s decision-making process — minus the caffeine and existential crises. Whether you're sharpening your knowledge or stepping into the field with curiosity, this course provides a sharp focus on the core principles that power technologies like image recognition, voice synthesis and predictive modelling. Delivered in an accessible format, it caters to learners who want depth without the fluff, logic without the waffle, and progress without the guesswork. Neural networks may be artificial — but your understanding of them won’t be. Learning Outcomes: Gain a solid understanding of artificial neural networks and their applications in deep learning. Learn how to install the necessary packages and preprocess data for neural network training. Discover how to encode data and build your own artificial neural network using Python. Understand the steps involved in making predictions using your neural network model. Learn how to deal with imbalanced data in your neural network training. The Project on Deep Learning - Artificial Neural Network course is designed to provide you with the skills and knowledge you need to build your own neural network and perform complex tasks using deep learning. You'll learn how to install the necessary packages, preprocess data, and encode data for neural network training. You'll also gain a deeper understanding of artificial neural networks and learn how to build your own model using Python. By the end of the course, you'll be able to make predictions using your neural network model and understand how to deal with imbalanced data in your training. Project on Deep Learning - Artificial Neural Network Course Curriculum Section 01: Introduction Section 02: ANN Installation Section 03: Data Preprocessing Section 04: Data Encoding Section 05: Steps to Build ANN Section 06: Predictions and Imbalance-Learn How is the course assessed? Upon completing an online module, you will immediately be given access to a specifically crafted MCQ test. For each test, the pass mark will be set to 60%. Exam & Retakes: It is to inform our learners that the initial exam for this online course is provided at no additional cost. In the event of needing a retake, a nominal fee of £9.99 will be applicable. Certification Upon successful completion of the assessment procedure, learners can obtain their certification by placing an order and remitting a fee of __ GBP. £9 for PDF Certificate and £15 for the Hardcopy Certificate within the UK ( An additional £10 postal charge will be applicable for international delivery). CPD 10 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Data analysts who want to expand their skills in deep learning and artificial neural networks. Programmers who want to learn how to build their own neural network models for advanced tasks. Entrepreneurs who want to develop their own deep learning-based applications. Students who want to enhance their skills in deep learning and prepare for a career in the field. Anyone who wants to explore the world of artificial neural networks and deep learning projects. Career path Data Analyst: £24,000 - £45,000 Machine Learning Engineer: £28,000 - £65,000 Deep Learning Engineer: £30,000 - £75,000 Technical Lead: £40,000 - £90,000 Chief Technology Officer: £90,000 - £250,000 Certificates Certificate of completion Digital certificate - £9 You can apply for a CPD Accredited PDF Certificate at the cost of £9. Certificate of completion Hard copy certificate - £15 Hard copy can be sent to you via post at the expense of £15.

Web Development (CSS , HTML & Bootstrap 4) - 8 Courses Bundle
By NextGen Learning
Are you ready to embark on an enlightening journey of wisdom with the Web Development bundle, and pave your way to an enriched personal and professional future? If so, then Step into a world of knowledge with our course bundle - Web Development (CSS, HTML & Bootstrap 4). Delve into eight immersive CPD Accredited courses, each a standalone course: Course 01: Learn Web Development from Scratch Course 02: HTML Web Development Crash Course Course 03: CSS Web Development Crash Course Course 04: Bootstrap 4 Responsive Web Development Course 05: Front End Web Development Training for Everyone Course 06: Web Design in Affinity Designer Course 07: Advanced Diploma in User Experience UI/UX Design Course 08: UX (User Experience) Fundamentals Traverse the vast landscapes of theory, unlocking new dimensions of understanding at every turn. Let the Web Development (CSS, HTML & Bootstrap 4) bundle illuminate your path to wisdom. The Web Development (CSS, HTML & Bootstrap 4) bundle offers a comprehensive exploration into a rich tapestry of vast knowledge across eight carefully curated courses. The journey is designed to enhance your understanding and critical thinking skills. Each course within the bundle provides a deep-dive into complex theories, principles, and frameworks, allowing you to delve into the nuances of the subject matter at your own pace. In the framework of the Web Development (CSS, HTML & Bootstrap 4) package, you are bestowed with complimentary PDF certificates for all the courses included in this bundle, all without any additional charge. Adorn yourself with the Web Development bundle, empowering you to traverse your career trajectory or personal growth journey with self-assurance. Register today and ignite the spark of your professional advancement! So, don't wait further and join the Web Development (CSS, HTML & Bootstrap 4) community today and let your voyage of discovery begin! Learning Outcomes: Upon completing this Web Development bundle, the learner will be able to: Attain a holistic understanding in the designated areas of study with the Web Development bundle. Establish robust bases across each course nestled within the Web Development bundle. Decipher intricate concepts through the articulate content of the Web Development bundle. Amplify your prowess in interpreting, scrutinising, and implementing theories. Procure the capacity to engage with the course material on an intellectual and profound level. Become proficient in the art of problem-solving across various disciplines. Stepping into the Web Development bundle is akin to entering a world overflowing with deep theoretical wisdom. Each course within this distinctive bundle is an individual journey meticulously crafted to untangle the complex web of theories, principles, and frameworks. Learners are inspired to explore, question, and absorb, thus enhancing their understanding and honing their critical thinking skills. Each course invites a personal and profoundly enlightening interaction with knowledge. The Web Development bundle shines in its capacity to cater to a wide range of learning needs and lifestyles. It gives learners the freedom to learn at their own pace, forging a unique path of discovery. More than just an educational journey, the Web Development bundle fosters personal growth, enabling learners to skillfully navigate the complexities of the world. The Web Development bundle also illuminates the route to a rewarding career. The theoretical insight acquired through this bundle forms a strong foundation for various career opportunities, from academia and research to consultancy and programme management. The profound understanding fostered by the Web Development bundle allows learners to make meaningful contributions to their chosen fields. Embark on the Web Development journey and let knowledge guide you towards a brighter future. CPD 85 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This Web Development bundle is suitable for: Aspiring Web Developers: Beginners seeking foundational web development skills. Front-End Developers: Professionals enhancing skills in responsive design and user experience. Graphic Designers: Designers expanding into web design using tools like Affinity Designer. UX/UI Designers: Specialists improving their knowledge in user experience and UI design. Entrepreneurs: Business owners wanting to build or manage their websites. Anyone with a thirst for knowledge and a passion for continuous learning. Requirements Without any formal requirements, you can delightfully enrol in this Web Development bundle. Career path This Web Development bundle will help to pursue various career paths: Junior Web Developer HTML Developer CSS Developer Bootstrap Web Developer Front-End Web Developer UI/UX Designer Certificates CPD Certificate Of Completion Digital certificate - Included 8 Digital Certificates Are Included With This Bundle CPD Quality Standard Hardcopy Certificate (FREE UK Delivery) Hard copy certificate - £9.99 Hardcopy Transcript - £9.99

WordPress - Complete Website Masterclass - 8 Courses Bundle
By NextGen Learning
Are you ready to embark on an enlightening journey of wisdom with the WordPress bundle, and pave your way to an enriched personal and professional future? If so, then Step into a world of knowledge with our bundle - WordPress - Complete Website Masterclass. Delve into eight immersive CPD Accredited courses, each a simple course: Course 1: WordPress Training for Everyone Course 2: WordPress Security Mastery Course 3: How To Build Easy Drag & Drop Landing Pages With WordPress Course 4: Using WordPress for Affiliate Marketing Course 5: Learn to Code HTML, CSS, Javascript: Guide for Beginners Course 6: PHP Webforms for Everyone Course 7: MySql Masterclass Course 8: User Experience Design from A-Z: Adobe XD UI/UX Design Traverse the vast landscapes of theory, unlocking new dimensions of understanding at every turn. Let the WordPress - Complete Website Masterclass bundle illuminate your path to wisdom. The WordPress - Complete Website Masterclass bundle offers a comprehensive exploration into a rich tapestry of vast knowledge across eight carefully curated courses. The journey is designed to enhance your understanding and critical thinking skills. Each course within the bundle provides a deep-dive into complex theories, principles, and frameworks, allowing you to delve into the nuances of the subject matter at your own pace. In the framework of the WordPress - Complete Website Masterclass package, you are bestowed with complimentary PDF certificates for all the courses included in this bundle, all without any additional charge. Adorn yourself with the WordPress bundle, empowering you to traverse your career trajectory or personal growth journey with self-assurance. Register today and ignite the spark of your professional advancement! So, don't wait further and join the WordPress - Complete Website Masterclass community today and let your voyage of discovery begin! Learning Outcomes: Upon completion of the WordPress - Complete Website Masterclass Bundle, you will be able to: Attain a holistic understanding in the designated areas of study with the WordPress bundle. Establish robust bases across each course nestled within the WordPress bundle. Decipher intricate concepts through the articulate content of the WordPress bundle. Amplify your prowess in interpreting, scrutinising, and implementing theories. Procure the capacity to engage with the course material on an intellectual and profound level. Become proficient in the art of problem-solving across various disciplines. Stepping into the WordPress - Complete Website Masterclass bundle is akin to entering a world overflowing with deep theoretical wisdom. Each course within this distinctive bundle is an individual journey, meticulously crafted to untangle the complex web of theories, principles, and frameworks. Learners are inspired to explore, question, and absorb, thus enhancing their understanding and honing their critical thinking skills. Each course invites a personal and profoundly enlightening interaction with knowledge. The WordPress bundle shines in its capacity to cater to a wide range of learning needs and lifestyles. It gives learners the freedom to learn at their own pace, forging a unique path of discovery. More than just an educational journey, the WordPress - Complete Website Masterclass bundle fosters personal growth, enabling learners to skillfully navigate the complexities of the world. The WordPress bundle also illuminates the route to a rewarding career. The theoretical insight acquired through this bundle forms a strong foundation for various career opportunities, from academia and research to consultancy and programme management. The profound understanding fostered by the WordPress bundle allows learners to make meaningful contributions to their chosen fields. Embark on the WordPress journey and let knowledge guide you towards a brighter future. CPD 100 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Individuals keen on deepening their firm understanding in the respective fields. Students pursuing higher education looking for comprehensive theory modules. Professionals seeking to refresh or enhance their knowledge. Anyone with a thirst for knowledge and a passion for continuous learning. Requirements Without any formal requirements, you can delightfully enrol in this WordPress - Complete Website Masterclass Bundle. Career path Armed with the WordPress - Complete Website Masterclass bundle, your professional journey can reach new heights. The comprehensive theoretical knowledge from this bundle can unlock diverse career opportunities across several fields. Whether it's academic research, consultancy, or programme management, the WordPress bundle lays a solid groundwork. Certificates CPD Certificate Of Completion Digital certificate - Included 8 Digital Certificates Are Included With This Bundle CPD Quality Standard Hardcopy Certificate (FREE UK Delivery) Hard copy certificate - £9.99 Hardcopy Transcript: £9.99
Microsoft Excel Mastery with SQL, Data Analysis, Financial Modelling - 8 Courses Bundle
By NextGen Learning
Have you ever wondered how businesses transform raw data into actionable insights or how financial analysts accurately pinpoint market trends? Microsoft Excel stands tall as the fulcrum that balances numerous sectors of the business world. This 8-course Microsoft Excel Mastery: AutoCAD, SQL, Data Analysis, Financial Modelling & Marketing bundle dives deep into the myriad applications of Microsoft Excel, from interfacing with AutoCAD to crafting marketing strategies and comprehensive financial models. In an era defined by data-driven decisions, this 8-course Microsoft Excel Mastery: AutoCAD, SQL, Data Analysis, Financial Modelling & Marketing bundle is tailored to equip learners with the multifaceted applications of Microsoft Excel. Ranging from foundational Excel operations to advanced integrations with tools like AutoCAD and MySQL, the course bundle aims to foster expertise in data management, analysis, and visualisation. Whether you're venturing into financial modelling, HR analytics, or design integration, this bundle serves as a comprehensive guide to mastering Excel in diverse professional realms, ensuring you are well-prepared to leverage its capabilities in the modern workplace. Ready to excel in your career? Embrace the transformative power of data and design by mastering Microsoft Excel with our comprehensive course bundle. Dive in now and shape your future with unparalleled proficiency! The Eight CPD Accredited courses that the bundle includes are: Course 1: Microsoft Excel Course for Everyone - Complete Excel Course Course 2: Excel VBA/Macros Foundations Course 3: Dynamic Excel Gantt Chart and Timelines Course 4: Hands on Programming on AutoCAD to Excel Using VB.NET Course 5: Learn MySQL from Scratch for Data Science and Analytics Course 6: Data Analytics Course 7: Build HR Dashboard using Excel Course 8: Financial Modelling Using Excel Learning Outcomes: Gain comprehensive knowledge and understanding of Microsoft Excel and its vast capabilities. Understand the seamless integration between Excel and tools like AutoCAD and MySQL. Develop proficiency in creating intricate financial models and marketing strategies. Acquire skills to analyse data, forecast trends, and build informative dashboards. Learn the principles of personal finance management using Excel. Master the art of crafting Gantt charts and timelines for effective project management. Microsoft Excel Course for Everyone - Complete Excel Course: Acquaint yourself with the foundational and advanced facets of Microsoft Excel, fostering data management expertise. Excel VBA/Macros Foundations: Dive into the transformative world of VBA, unlocking Excel's programming potentials. Dynamic Excel Gantt Chart and Timelines: Grasp the essentials of project management by designing insightful Gantt charts and timelines in Excel. Hands on Programming on AutoCAD to Excel Using VB.NET: Bridge the realms of design and data by merging AutoCAD functionalities with Microsoft Excel's prowess. Learn MySQL from Scratch for Data Science and Analytics: Understand the confluence of Excel and MySQL, anchoring data science and analytics. Data Analytics: Master the techniques of transforming raw numbers into actionable insights using Microsoft Excel. Build HR Dashboard using Excel: Curate informative HR dashboards, offering a snapshot of organisational metrics, all within Excel. Financial Modelling Using Excel: Unravel the intricacies of financial markets, crafting accurate models in Microsoft Excel. CPD 90 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Individuals keen on enhancing their Microsoft Excel skills for professional or personal reasons. Marketing professionals aiming to refine their strategic planning with Excel. Financial analysts and enthusiasts looking to build and understand models in Excel. Data scientists and analysts desire to integrate Excel with tools like MySQL. Design engineers and architects keen on integrating AutoCAD designs with Excel data. Career path Data Analyst Financial Modeller Marketing Strategist HR Dashboard Specialist Database Administrator (with Excel integration knowledge) Project Manager (familiar with Gantt and timelines in Excel) Design Engineer using Excel with AutoCAD Certificates CPD Certificate Of Completion Digital certificate - Included 8 Digital Certificates Are Included With This Bundle CPD Quality Standard Hardcopy Certificate (FREE UK Delivery) Hard copy certificate - £9.99 Hardcopy Transcript: £9.99