- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
2096 Other courses in Milton Keynes delivered Live Online
Read and discuss the Queen of Crime - Agatha Christie! Highlights Join this book club and gain extra motivation to read in English 7 hours of live classes to help you develop fluent speaking in English Study this classic detective story and work out the clues by understanding the text Be corrected by an expert English teacher to remove errors and mistakes Learn English online using this great story from Agatha Christie - the most widely published author of all time and in any language. This is an 7 week online Zoom course with an expert English teacher from the UK. The Book Club book In Death on the Nile Poirot finds himself in the middle of a confusing murder while on holiday in Egypt. What reason would anyone have to murder the beautiful victim? And will they kill again? With an intricate plot, this is one of Agatha Christie's finest murder mysteries. Geoff says: "Agatha Christie is known as the Queen of Crime. She is the best-selling novelist of all time, writing 66 detective novels and 14 short story collections. This one stars her much loved detective, Hercule Poirot."
QA Level 2 Award In Fire Safety (RQF) Face to Face Classroom: Full day course Online / Virtual Classroom: 3 sessions of 2½ hours Suitable for Fire Wardens/Fire Marshals and all other members of staff Provides a foundation of fire safety knowledge on which employers and ‘responsible persons’ can build, keeping the business safe from fire Benefits of this course: How much do you know about keeping yourself and others safe in the workplace? Fire Safety Law breaches can result in unlimited fines and imprisonment More importantly, how would you feel if someone got injured or even killed by a fire you could have prevented? This course is for anyone who has a specific responsibility for fire safety in the workplace, such as designated fire wardens/fire marshals Successful candidates will gain an understanding of fire safety management at work and the specific roles and responsibilities related to fire safety in the workplace. Course Contents: Causes of Fire in the Workplace The Fire Triangle Hazards during and after a Fire Fire and Smoke Spread Identifying and Controlling Fire Hazards Fire Safety Laws Duties and Responsibilities of Employers and Employees Undertaking a Fire Safety Inspection Fire Safety Risk Assessments Contents of a Fire Safety Briefing Roles and Responsibilities of the Nominated Fire Warden Accredited, Ofqual regulated qualification: Our Fire Safety course is a nationally recognised, Ofqual regulated qualification accredited by Qualsafe Awards.You can rest assured that the training your employees receive is of a high quality and the candidates will get a strong grounding in Fire Safety, helping to keep your staff and your business safe from fire.The Ofqual Register number for this course is 603/2756/X

Wellbeing Ambassador Programme
By Clare Martin
The Wellbeing Ambassador Programme is our comprehensive wellbeing training for leaders. It is based on evidence-based positive psychology research to help those who lead others to confidently support wellbeing.

Level 2 Training: Domestic Abuse Understanding
By Restored
We're passionate about equipping churches to respond to domestic abuse. Our Domestic Abuse Awareness course will help you explore key questions around the issue of domestic abuse, like how to recognise the signs of domestic abuse, why domestic abuse happens, and how to start supporting survivors.

Mentoring Sessions
By LivePlayLearn
Unschooling questions have unschooling answers. Answers to your questions, with an unschooling perspective. A safe space in which to share anything from the everyday to your deepest concerns. Concentrated time set aside, to help you purposefully move forward, and take hold of a joyful family life. Select from the following options:1/2 Hour Discovery call (Free) : Come and meet me for half an hour and we can discuss together your needs and put together a personal plan for you. 1 hour Clinic (£75) : Bring your own questions and enjoy an unschooling perspective on your unique journey. With the option to upgrade to the full Mentoring Support Service .4 x 1 hour sessions (£266) or 6 x 1 hour sessions (£399) : 1:1 support over of a series of sessions. A bespoke program, tailored to you and your family. Compiled after an initial, in depth, diagnostic assessment. Identifying your challenges and putting together a practical plan that can be implemented with on-going support. LPL Monthly Members receive a 20% discount on mentoring services which is automatically applied at the checkout. Join the LPL Monthly Membership

Definitive Nagios training course description Nagios is an open source application designed to provide system and network monitoring. This hands on course gives a comprehensive coverage of using Nagios to provide monitoring of Linux, Windows and network devices. The course is based on Nagios core but contact us if you would like Nagios XI. What will you learn Install Nagios. Configure Nagios. Monitor Windows, Linux and Cisco (and other network equipment) using Nagios. Configure notifications Definitive Nagios training course details Who will benefit: Technical staff working with Nagios. Prerequisites: None. Duration 2 days Definitive Nagios for engineers Nagios architecture Downloading Nagios, Installing Nagios, Nagios core, plugins, frontends, addons. Nagios XI. Nagios Fusion. Hands on Installing Nagios. Getting started with Nagios Nagios files, nagios.cfg, minimal.cfg. Starting and stopping Nagios. Hands on Controlling Nagios. Using Nagios Nagios web interface. Maps, Hosts, host groups, services, service groups, problems. Reports. Configuration. Hands on Using the web interface. Monitoring Linux systems SSH, NRPE. Hands on Monitoring Linux system health. Monitoring Windows systems Installing NSClient++, Configuring NSClient++, check_nt plugin, monitoring uptime, CPU, memory, disks, services, processes. Hands on Monitoring Windows system health. Monitoring network devices SNMP architecture, MIBs. Polling. Hands on Configuring Nagios for SNMP. Agents Configuring Cisco devices for SNMP support, communities, traps, syslog. Hands on Monitoring network devices. Nagios alerts and notifications SNMP traps. Email notifications, SMS alerts other messaging

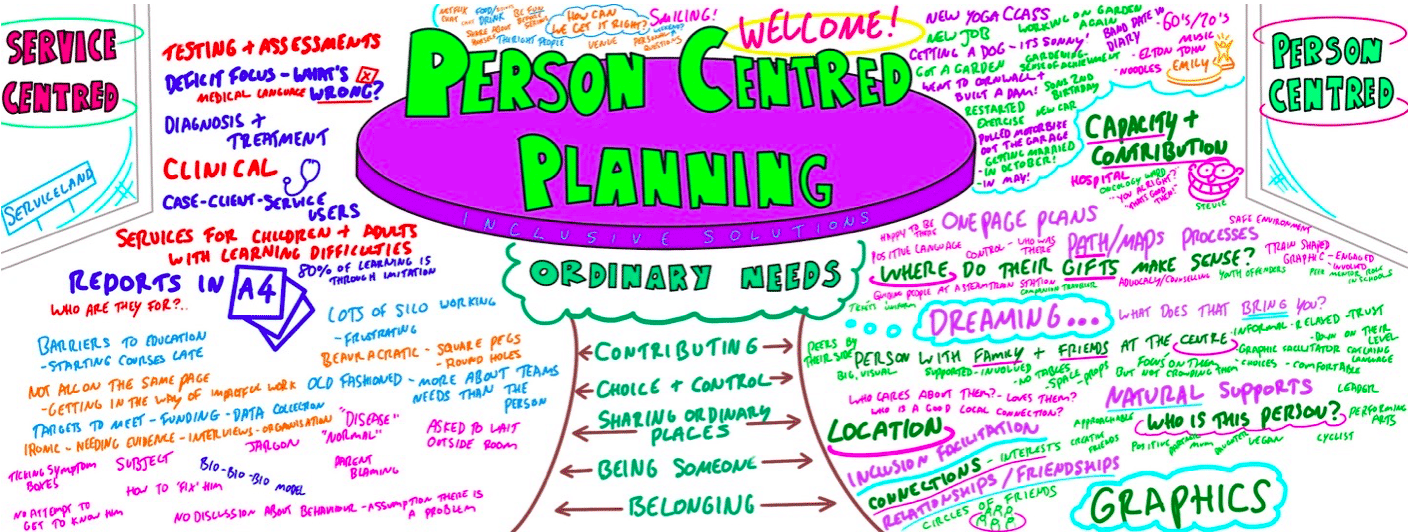
Person Centred Planning using PATH and MAPs
By Inclusive Solutions
What is Person Centred Planning? How is it different to any other kind of meeting or planning? On this day all will become clear… Give your team the opportunity to pause and reflect on what matters most to them about the work they do. The act of listening to each other creates relationship and strengthens trust and inclusion within the team – in creating a shared vision, groups of people build a sense of commitment together. They develop images of ‘the future we want to create together’, along with the values that will be important in getting there and the goals they want to see achieved along the way. Unfortunately, many people still think ’vision’ is the top leader’s job. In schools, the ‘vision task’ usually falls to the Headteacher and/or the governors or it comes in a glossy document from the local authority or the DfES. But visions based on authority are not sustainable. Making inclusive action plans using full participation and graphic facilitation Drawing on the planning tools MAPS and PATH (Pearpoint, Forest and O’Brien 1997) and other facilitation sources we use both process and graphic facilitation to enable the group to build their picture of what they would love to see happening within their organisation/community in the future and we encourage this to be a positive naming, not just a list of the things they want to avoid. Jack Pearpoint, Marsha Forest and John O’Brien developed these innovative approaches in North America and they are being used successfully in many parts of the UK. The planning can focus on an individual, group or organisation and provides a powerful problem solving opportunity, which is flexible and robust enough for many occasions. Tell the story, find the dream, touch the nightmare, and explore who you are, what are the gifts and strengths of the person or group, what are the needs of those present and what is the action plan for the future? Learning objectives Participants understand Person Centred Planning and its values and applications Participants have skills and confidence to facilitate PATH/MAP processes Participants learn graphic as well as process facilitation skills Strengthens practitioners inclusive practice Provides additional tools for those involved in inclusive work in schools and the community Further develop problem solving and planning skills Course Content The course answers the questions: Need to find new ways to bring Pathway Planning alive? Bored with annual reviews, transition plans and review meetings? Want to find a way of making meetings and planning feel more real and engaging? Need an approach, which engages a young person respectfully together with his or her family and friends? Want the ultimate visual record of the process of a meeting, which will help everyone, keep track? Want to problem solve and plan for the future of a small or large group, service or organisation up to the size of an LA? Inclusive Solutions offer an introductory day to person centred planning or a 3 – 10 session course which is practical as well as values based. Participants will receive direct individualised coaching and training. We will cover: The person being at the centre Family members and friends being full partners Planning reflecting the person’s capacities, what is important to the person and specifying the support they require to make a full contribution to their community Planning building a shared commitment to action that will uphold the person’s rights Planning leading to continual listening, learning and action and helping the person get what they want out of life. Essential Lifestyle Planning, PATH MAPS Personal Futures Planning.
May 2025 Fundamentals Organisation & Relationship Systems Coaching Training
By CRR UK
CRRUK equips professionals with the concepts, skills and tools to build conscious, intentional relationships, and to coach relationship systems of any size.

LOOKING FOR: ADULT FICTION, NON-FICTION Julie Gourinchas (she/they) is developing a selective list focused on upmarket and literary adult fiction across a wide variety of genres. Writers she represents have been nominated for the British Book Awards, the Hugo Awards, the BSFA Awards, and the Saltire National Book Awards, among others. In fiction, she's drawn to a uncommon voices, and striking, intelligent writing – whether vibrant and floral or tense, quick, and sparse – as well as texture in both tone and setting (particularly anything with a strong aesthetic). Above all, she is looking for hooky, high-concept work, but her taste can perhaps be best summarised as "the weird, dark, and gruesome." While literary-speculative is her sweet spot, she considers herself genre agnostic within upmarket/literary fiction, and remains open to compelling and well-executed genre overlap. These include: upmarket and literary horror: especially featuring feminist or cultural themes, body horror, mangled nature, or cosmic, Lovecraftian vibes and looking for a fresh, literary take on vampires. Think Mona Awad, Lucy Rose, Julia Armfield, Jade Song, Stephen Graham Jones. dark and spiky literary dramas with high emotional stakes - think Eliza Clark, Julia May Jonas. razor-sharp dark academia particularly with something to say about the complex and exploitative systems within academia, more The Secret History, less The Atlas Six. gothic fiction, specifically regional gothic anchored in an evocative sense of place in the vein of Alexis Henderson and Alix E. Harrow. grounded fantasy or otherwise speculative fiction with coherent, sharp worldbuilding that feels recognisable and familiar, or directly set in our world. Play with magic, faith, and technology in your story like Babel, or a more literary version like Emily Wilde's Encyclopaedia of Faeries, Blood Over Bright Haven, Metal From Heaven. Searing contemporary fiction centred on themes of identity and belonging: think Sally Rooney, Torrey Peters, or what Saltburn should have been. dark westerns, in particular any that play with the truth and false hopes of the American Dream. magical realism both whimsy with a touch of darkness, and darkness with a touch of whimsy. unhappy romances anything -punk: steampunk, solarpunk, silkpunk, clockpunk, dieselpunk, cyberpunk and more of these! Suffice to say: if you can successfully and smartly comp to Arcane, Julie wants to see it! character-focused historical fiction with a literary edge: think Lauren Groff, Anthony Doerr, Eleanor Catton, particularly in the 19th and 20th centuries; including and indeed encouraging alternate history. Stylistically, Julie loves uncommon, thought-provoking experimentation with both prose and form, and anything spiky, toothy, and dark. Happy endings, to her, should feel earned. In all things, compelling character development should come first. First person narration is not impossible, but hard to sell. A smart genre blend is always welcome, as is any fresh-eyed approach to a well-trodden trope. Julie is also very much looking for her first romantasy – especially one that approaches this exciting new genre from a fresh, bold perspective. She is keenly interested in hearing from authors traditionally underrepresented in the industry, including but not restricted to writers of colour; queer, trans, and nonbinary writers; working class writers; disabled writers; etc. Her enduring favourite books include All The Light We Cannot See by Anthony Doerr, Do Not Say We Have Nothing by Madeleine Thien, The Luminaries by Eleanor Catton, and Philip Pullman’s His Dark Materials series. More recent favourites include the masterful Tomorrow and Tomorrow and Tomorrow by Gabrielle Zevin, Babel by R.F. Kuang, Detransition Baby by Torrey Peters, Matrix by Lauren Groff, Tell Me I’m Worthless by Alison Rumfitt, Brother Alive by Zain Khalid, and Our Wives Under the Sea by Julia Armfield. In non-fiction, Julie is keen to read in the narrative and “big ideas” spaces, particularly in the realms of politics, history, and the social sciences. Please note: Julie is not looking for young adult, middle grade, and children’s books. Strictly no AI-generated content of any description. Please also bear in mind that, despite a deep and abiding love for all things Tolkien and Star Wars, she is not typically the right fit for epic or high fantasy, nor space-faring science fiction. She would also prefer to avoid pulpy crime and straightforward romance/romcoms. Julie would like you to submit a covering letter, 1 page synopsis and the first 5,000 words of your manuscript in a single word document. (In addition to the paid sessions, Julie is kindly offering one free session for low income/under-represented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Tuesday 29th April 2025

Network forensics training course description This course studies network forensics-monitoring and analysis of network traffic for information gathering, intrusion detection and legal evidence. We focus on the technical aspects of network forensics rather than other skills such as incident response procedures etc.. Hands on sessions follow all the major sections. What will you learn Recognise network forensic data sources. Perform network forensics using: Wireshark NetFlow Log analysis Describe issues such as encryption. Network forensics training course details Who will benefit: Technical network and/or security staff. Prerequisites: TCP/IP foundation for engineers. Duration 3 days Network forensics training course contents What is network forensics? What it is, host vs network forensics, purposes, legal implications, network devices, network data sources, investigation tools. Hands on whois, DNS queries. Host side network forensics Services, connections tools. Hands on Windows services, Linux daemons, netstat, ifoconfig/ipconfig, ps and Process explorer, ntop, arp, resource monitor. Packet capture and analysis Network forensics with Wireshark, Taps, NetworkMiner. Hands on Performing Network Traffic Analysis using NetworkMiner and Wireshark. Attacks DOS attacks, SYN floods, vulnerability exploits, ARP and DNS poisoning, application attacks, DNS ANY requests, buffer overflow attacks, SQL injection attack, attack evasion with fragmentation. Hands on Detecting scans, using nmap, identifying attack tools. Calculating location Timezones, whois, traceroute, geolocation. Wifi positioning. Hands on Wireshark with GeoIP lookup. Data collection NetFlow, sflow, logging, splunk, splunk patterns, GRR. HTTP proxies. Hands on NetFlow configuration, NetFlow analysis. The role of IDS, firewalls and logs Host based vs network based, IDS detection styles, IDS architectures, alerting. Snort. syslog-ng. Microsoft log parser. Hands on syslog, Windows Event viewer. Correlation Time synchronisation, capture times, log aggregation and management, timelines. Hands on Wireshark conversations. Other considerations Tunnelling, encryption, cloud computing, TOR. Hands on TLS handshake in Wireshark.
