- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1911 Object courses in Liverpool delivered Live Online
Computer Networking Course Online
By Hi-Tech Training
Computer Networking Online Virtual Classroom course is designed to enable participants to install, configure and test a fundamental computer network. The opportunities for employment within the area of network support are enormous as businesses continue to grow and utilise the new technology available to them. This is a vital role to ensure the smooth running of businesses reliant on their network and IT systems. This course provides learners with both the practical and theoretical knowledge of networks. During the course, participants will learn about the different components used to create a network including hardware, software and topologie

Fire Alarm Foundation Course
By Hi-Tech Training
The Fire Alarm Foundation course is designed to give participants a practical knowledge of the operation and installation of Fire Alarm Systems at a foundation level. During this practical and theory-based course students will gain the skills and knowledge to install and wire up a Fire Alarm Control Panel to typical auxiliary equipment such as Break Glass Units, Smoke Detectors, Heat Detectors, Bells, and Sirens.

JSEC - Junos Security
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The primary audiences for this course are the following: • Operators of Juniper Networks security solutions, including network engineers, administrators, support personnel, and resellers. Overview After successfully completing this course, you should be able to: Identify security challenges in today's networks. Identify products that are incorporated into the Juniper Connected Security solution. Explain the value of implementing security solutions. Explain how Juniper Connected Security solves the cyber security challenges of the future. Explain SRX Series session management. Explain Junos ALG functions and when to use them. Describe policy logging on the SRX series device. Explain security policy scheduling. Describe application security theory. Explain application signature usage in AppID. Describe the AppTrack service. Describe the AppFW service. Describe the AppQoS service. Configure security policies using the AppSecure suite of services. Explain unified security policies. Describe IPS signatures. Configure an IPS policy using pre-defined templates. Describe how to update the IPS attack object database. Describe IPS rules and rule bases. Configure custom attack objects. Describe Junos Space and Security Director. Configure policy management using Security Director. Describe Security Director objects. Explain the different licensing options for Sky ATP List Sky ATP's features and benefits. Configure Sky ATP profiles and enroll an SRX Series device. Configure file scanning on Sky ATP. Configure Sky ATP to scan email Configure GeoIP on Sky ATP. Describe the JATP features and benefits List the JATP device options. Explain the JATP architecture. List 3rd party support options for JATP. Explain JATP SmartCore analytics processes. Describe Policy Enforcer configuration options. Describe Policy Enforcer integration with Sky ATP. Configure Policy Enforcer to block lateral malware movement. Explain Juniper Secure Analytics features and benefits. Describe JSA log collection. Describe JSA network flow collection. Describe the JSA Offense Management workspace. Explain the JSA Risk Manager features. Configure JSA to collect network and log collection. Explain the features of JIMS. Describe JIMS integration into the current AD network. Describe the Sky Enterprise service and how it can save resources. Explain the Sky Enterprise monitoring service. Explain the vSRX Series device benefits. Describe use cases for the vSRX. Explain the cSRX Series device benefits. Describe use cases for the cSRX. Describe SSL Proxy Concepts. Explain Forward and Reverse Proxy and the limitations of each. Configure both Forward and Reverse Proxy. This five-day course uses the Junos J-Web, CLI, Junos Space, and other user interfaces to introduce students to the concept of Juniper Connected Security. Chapter 1: Course Introduction Course Introduction Chapter 2: CLI Overview User Interface Options Command-Line Interface Initial Configuration Interface Configuration Lab 1: CLI Overview Chapter 3: Advanced Security Policy Session Management Junos ALGs Policy Scheduling Policy Logging Lab 2: Advanced Security Policy Chapter 4: Application Security Theory Application ID Application Signatures App Track App Firewall App QoS App QoE Chapter 5: Application Security Implementation AppTrack Implementation AppFW Implementation AppQos Implementation APBR Implementation Lab 3: Application Security Chapter 6: Intrusion Detection and Prevention IPS Overview IPS Policy Attack Objects IPS Configuration IPS Monitoring Lab 4: Implementing IPS Chapter 7: Security Director Overview Security Director Objects Security Director Policy Management Lab 5: Security Director Chapter 8: Sky ATP Implementation Architecture and Key Components Features and Benefits Configuration Compromised Hosts Command and Control File Scanning E-mail Scanning Geo IP Security Policy Integration Troubleshooting Lab 6: Sky ATP Implementation Chapter 9: Policy Enforcer Policy Enforcer Concepts Configuration Options Policy Enforcer Installation Lab 7: Policy Enforcer Chapter 10: JATP Overview Traffic Inspection Threat Detection Threat Analysis JATP Architecture Chapter 11: JATP Implementation Data Collectors Configure SmartCore Analytics Engine Log Ingestion Incident Management SRX Threat Prevention 3rd Party support for Threat Prevention Reporting Lab 8: JATP Chapter 12: Juniper Secure Analytics (JSA) JSA Overview Data Collection Log Analytics Threat Analytics Vulnerability Management Risk Management Lab 9: JSA Chapter 13: JIMS JIMS Overview JIMS Integration Lab 10: JIMS Chapter 14: vSRX and cSRX vSRX Overview vSRX Supported Features vSRX Use Cases cSRX Overview Lab 11: vSRX Installation Chapter 15: SSL Proxy SSL Proxy Overview SSL Concepts SSL Proxy Configurations Troubleshooting Lab 12: SSL Proxy Chapter 16: Cluster Concepts Chassis Cluster Concepts Chassis Cluster Operation Chapter 17: Chassis Cluster Implementation Chassis Cluster Configuration Chassis Cluster Advanced Options Lab 13: Chassis Cluster Implementation Chapter 18: Chassis Cluster Troubleshooting Chassis Cluster Case Studies Troubleshooting Examples Lab 14: Chassis Cluster Troubleshooting Additional course details: Nexus Humans JSEC - Junos Security training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the JSEC - Junos Security course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Digital, Text & Voice Communicators Course
By Hi-Tech Training
The Hi-Tech Training Digital Text & Voice Communicator Course is designed to provide participants with the skills required to connect Digital, Text & Voice Communicators to an Alarm Control Panel for transmission of Digital status signals via the telephone line, GSM Network or IP network to a central monitoring station. The Digital Communicator Course’s practical application and our highly experienced trainers ensure that this course is second to none. The course is technical and practical in nature and is suitable for participants who have successfully completed the Hi-Tech Training Intruder Alarm Installation Course or equivalent.
F5 Networks Configuring BIG-IP Advanced WAF - Web Application Firewall (formerly ASM)
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is intended for security and network administrators who will be responsible for the installation, deployment, tuning, and day-to-day maintenance of the F5 Advanced Web Application Firewall. In this 4 day course, students are provided with a functional understanding of how to deploy, tune, and operate F5 Advanced Web Application Firewall to protect their web applications from HTTP-based attacks. The course includes lecture, hands-on labs, and discussion about different F5 Advanced Web Application Firewall tools for detecting and mitigating threats from multiple attack vectors such web scraping, Layer 7 Denial of Service, brute force, bots, code injection, and zero day exploits. Module 1: Setting Up the BIG-IP System Introducing the BIG-IP System Initially Setting Up the BIG-IP System Archiving the BIG-IP System Configuration Leveraging F5 Support Resources and Tools Module 2: Traffic Processing with BIG-IP Identifying BIG-IP Traffic Processing Objects Overview of Network Packet Flow Understanding Profiles Overview of Local Traffic Policies Visualizing the HTTP Request Flow Module 3: Web Application Concepts Overview of Web Application Request Processing Web Application Firewall: Layer 7 Protection F5 Advanced WAF Layer 7 Security Checks Overview of Web Communication Elements Overview of the HTTP Request Structure Examining HTTP Responses How F5 Advanced WAF Parses File Types, URLs, and Parameters Using the Fiddler HTTP Proxy Module 4: Common Web Application Vulnerabilities A Taxonomy of Attacks: The Threat Landscape What Elements of Application Delivery are Targeted? Common Exploits Against Web Applications Module 5: Security Policy Deployment Defining Learning Comparing Positive and Negative Security Models The Deployment Workflow Policy Type: How Will the Policy Be Applied Policy Template: Determines the Level of Protection Policy Templates: Automatic or Manual Policy Building Assigning Policy to Virtual Server Deployment Workflow: Using Advanced Settings Selecting the Enforcement Mode The Importance of Application Language Configure Server Technologies Verify Attack Signature Staging Viewing Requests Security Checks Offered by Rapid Deployment Defining Attack Signatures Using Data Guard to Check Responses Module 6: Policy Tuning and Violations Post-Deployment Traffic Processing Defining Violations Defining False Positives How Violations are Categorized Violation Rating: A Threat Scale Defining Staging and Enforcement Defining Enforcement Mode Defining the Enforcement Readiness Period Reviewing the Definition of Learning Defining Learning Suggestions Choosing Automatic or Manual Learning Defining the Learn, Alarm and Block Settings Interpreting the Enforcement Readiness Summary Configuring the Blocking Response Page Module 7: Attack Signatures & Threat Campaigns Defining Attack Signatures Attack Signature Basics Creating User-Defined Attack Signatures Defining Simple and Advanced Edit Modes Defining Attack Signature Sets Defining Attack Signature Pools Understanding Attack Signatures and Staging Updating Attack Signatures Defining Threat Campaigns Deploying Threat Campaigns Module 8: Positive Security Policy Building Defining and Learning Security Policy Components Defining the Wildcard Defining the Entity Lifecycle Choosing the Learning Scheme How to Learn: Never (Wildcard Only) How to Learn: Always How to Learn: Selective Reviewing the Enforcement Readiness Period: Entities Viewing Learning Suggestions and Staging Status Violations Without Learning Suggestions Defining the Learning Score Defining Trusted and Untrusted IP Addresses How to Learn: Compact Module 9: Cookies and Other Headers F5 Advanced WAF Cookies: What to Enforce Defining Allowed and Enforced Cookies Configuring Security Processing on HTTP headers Module 10: Reporting and Logging Overview: Big Picture Data Reporting: Build Your Own View Reporting: Chart based on filters Brute Force and Web Scraping Statistics Viewing F5 Advanced WAF Resource Reports PCI Compliance: PCI-DSS 3.0 The Attack Expert System Viewing Traffic Learning Graphs Local Logging Facilities and Destinations How to Enable Local Logging of Security Events Viewing Logs in the Configuration Utility Exporting Requests Logging Profiles: Build What You Need Configuring Response Logging Module 11: Lab Project 1 Lab Project 1 Module 12: Advanced Parameter Handling Defining Parameter Types Defining Static Parameters Defining Dynamic Parameters Defining Dynamic Parameter Extraction Properties Defining Parameter Levels Other Parameter Considerations Module 13: Automatic Policy Building Overview of Automatic Policy Building Defining Templates Which Automate Learning Defining Policy Loosening Defining Policy Tightening Defining Learning Speed: Traffic Sampling Defining Track Site Changes Lesson 14: Web Application Vulnerability Scanner Integration Integrating Scanner Output Importing Vulnerabilities Resolving Vulnerabilities Using the Generic XML Scanner XSD file Lesson 15: Deploying Layered Policies Defining a Parent Policy Defining Inheritance Parent Policy Deployment Use Cases Lesson 16: Login Enforcement and Brute Force Mitigation Defining Login Pages for Flow Control Configuring Automatic Detection of Login Pages Defining Session Tracking Brute Force Protection Configuration Source-Based Brute Force Mitigations Defining Credentials Stuffing Mitigating Credentials Stuffing Lesson 17: Reconnaissance with Session Tracking Defining Session Tracking Configuring Actions Upon Violation Detection Lesson 18: Layer 7 DoS Mitigation Defining Denial of Service Attacks Defining the DoS Protection Profile Overview of TPS-based DoS Protection Creating a DoS Logging Profile Applying TPS Mitigations Defining Behavioral and Stress-Based Detection Lesson 19: Advanced Bot Protection Classifying Clients with the Bot Defense Profile Defining Bot Signatures Defining Proactive Bot Defense Defining Behavioral and Stress-Based Detection Defining Behavioral DoS Mitigation Lesson 20: Form Encryption using DataSafe Targeting Elements of Application Delivery Exploiting the Document Object Model Protecting Applications Using DataSafe The Order of Operations for URL Classification Lesson 21: Review and Final Labs Review and Final Labs

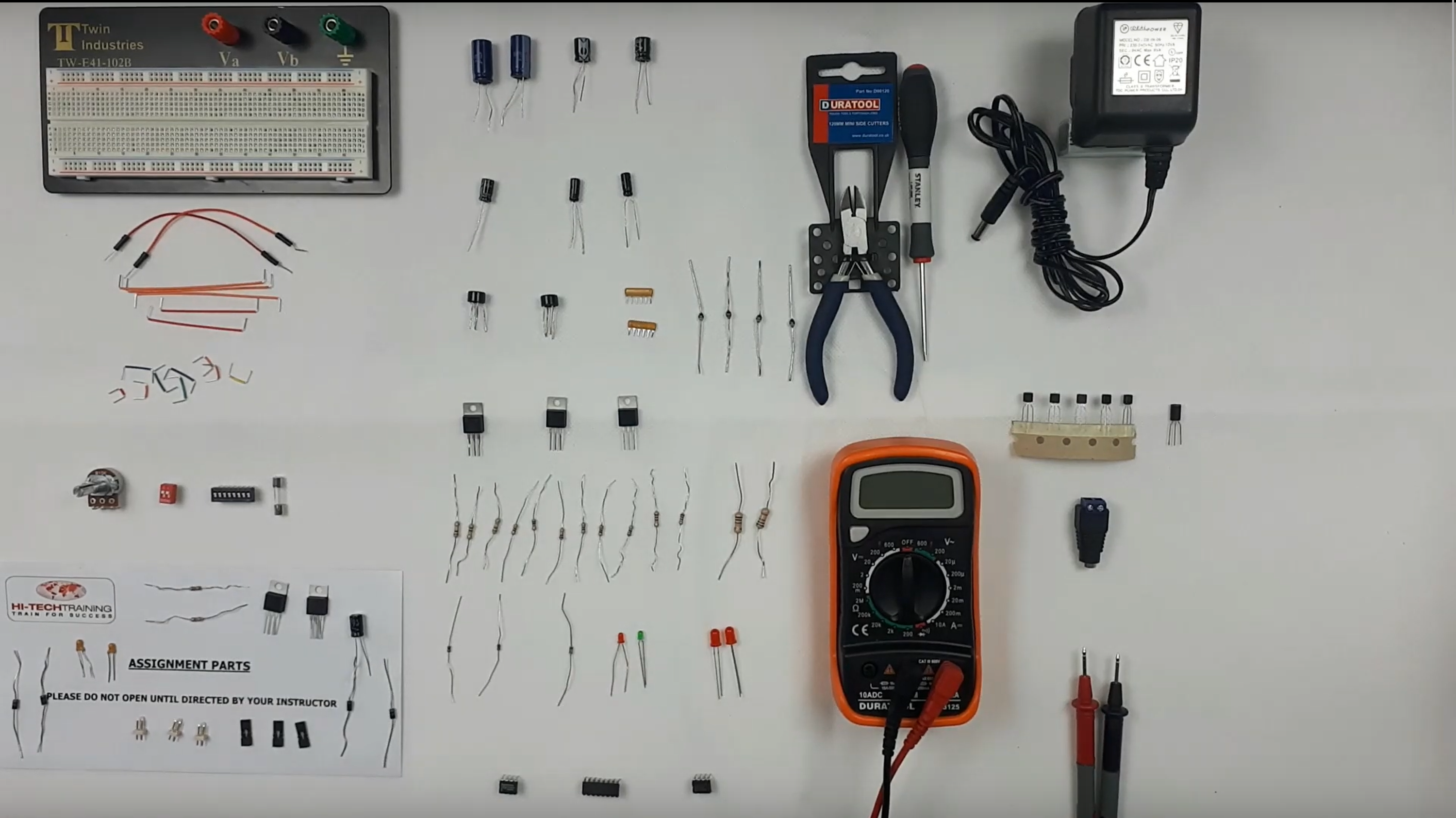
Electronics Repair 2 Course
By Hi-Tech Training
Electronics Equipment Repair 2 (Online Virtual Classroom) is a follow on course to Electronics Equipment Repair 1. This course builds on the skills gained and enables participants to build, test and fault-find more complex Analogue Electronic circuits
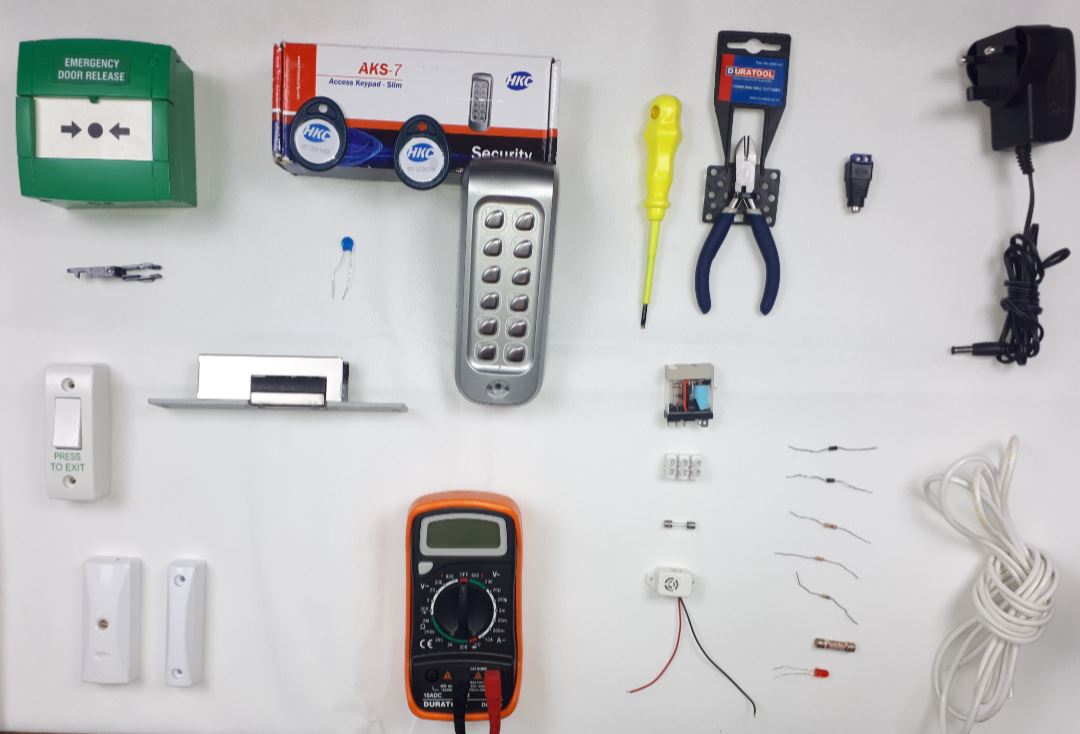
Access Control Course
By Hi-Tech Training
An effective Access Control System can form an integral part of an effective security system. At Hi-Tech Training our course is designed to give participants a practical knowledge of the operation and installation of Access Control Systems. Our experience has taught us that in order to gain the required skills an installer needs to learn through as much practical training as possible. This course involves 50% “Hands-On” training which involves building, setting up, testing and troubleshooting faults using core elements of modern Access Control Systems. At the end of the course, an interested and hardworking participant will have a good solid foundation of knowledge of what access control is all about.
Cognitive Stimulation Therapy (CST) Training online via Zoom
By Dementia Pathfinders Community Interest Company
This one day training will give learners an overview of how to deliver Cognitive Stimulation Therapy (CST). CST is a brief evidence-based group treatment for people with dementia. This interactive course will include a background about CST and how it can be used, research overview and detailed presentation of the treatment, including video footage and role-play.

Mastering React | React Foundation (TT4195)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This introductory-level, fast-paced course is for skilled web developers new to React who have prior experienced working HTML5, CSS3 and JavaScript. Overview Our engaging instructors and mentors are highly experienced practitioners who bring years of current 'on-the-job' experience into every classroom. Working in a hands-on learning environment, guided by our expert team, attendees will learn about and explore: A basic and advanced understanding of React components An advanced, in-depth knowledge of how React works A complete understanding of using Redux How to build, validate, and populate interactive forms How to use inline styles for perfect looking components How to test React components How to build and use components How to get control of your build process A deep understanding of data-driven modeling with props and state How to use client-side routing for pages in your apps How to debug a React application Mastering React is a comprehensive hands-on course that aims to be the single most useful resource on getting up to speed quickly with React. Geared for more experienced web developers new to React, this course provides students with the core knowledge and hands-on skills they require to build reliable, powerful React apps. After the first few modules, you?ll have a solid understanding of React?s fundamentals and will be able to build a wide array of rich, interactive web apps with the framework. The first module is an introduction to the new functionality in ECMAScript 6 (JavaScript). Client-side routing between pages, managing complex state, and heavy API interaction at scale are also covered. This course consists of two parts. In the first part of the course students will explore all the fundamentals with a progressive, example-driven approach. You?ll create your first apps, learn how to write components, start handling user interaction, and manage rich forms. We end the first part by exploring the inner workings of Create React App (Facebook?s tool for running React apps), writing automated unit tests, and building a multi-page app that uses client-side routing. The latter part of the course moves into more advanced concepts that you?ll see used in large, production applications. These concepts explore strategies for data architecture, transport, and management: Redux is a state management paradigm based on the Flux architecture. Redux provides a structure for large state trees and allows you to decouple user interaction in your app from state changes. GraphQL is a powerful, typed, REST API alternative where the client describes the data it needs. Hooks is the powerful, new way to maintain state and properties with functional components and the future of React according to Facebook. ES6 Primer (Optional) Prefer const and let over var Arrow functions Modules Object.assign() Template literals The spread operator and Rest parameters Enhanced object literals Default arguments Destructuring assignments Your first React Web Application Setting up your development environment JavaScript ES6 /ES7 Getting started What?s a component? Our first component Building the App Making the App data-driven Your app?s first interaction Updating state and immutability Refactoring with the Babel plugin transform-class-properties JSX and the Virtual DOM React Uses a Virtual DOM Why Not Modify the Actual DOM? What is a Virtual DOM? Virtual DOM Pieces ReactElement JSX JSX Creates Elements JSX Attribute Expressions JSX Conditional Child Expressions JSX Boolean Attributes JSX Comments JSX Spread Syntax JSX Gotchas JSX Summary Components A time-logging app Getting started Breaking the app into components The steps for building React apps from scratch Updating timers Deleting timers Adding timing functionality Add start and stop functionality Methodology review Advanced Component Configuration with props, state, and children ReactComponent props are the parameters PropTypes Default props with getDefaultProps() context state Stateless Components Talking to Children Components with props.children Forms Forms 101 Text Input Remote Data Async Persistence Redux Form Modules Unit Testing & Jest Writing tests without a framework What is Jest? Using Jest Testing strategies for React applications Testing a basic React component with Enzyme Writing tests for the food lookup app Writing FoodSearch.test.js Routing What?s in a URL? React Router?s core components Building the components of react-router Dynamic routing with React Router Supporting authenticated routes Intro to Flux and Redux Why Flux? Flux is a Design Pattern Flux implementations Redux & Redux?s key ideas Building a counter The core of Redux The beginnings of a chat app Building the reducer() Subscribing to the store Connecting Redux to React Intermediate Redux Using createStore() from the redux library Representing messages as objects in state Introducing threads Adding the ThreadTabs component Supporting threads in the reducer Adding the action OPEN_THREAD Breaking up the reducer function Adding messagesReducer() Defining the initial state in the reducers Using combineReducers() from redux React Hooks Motivation behind Hooks How Hooks Map to Component Classes Using Hooks Requires react 'next' useState() Hook Example useEffect() Hook Example useContext() Hook Example Using Custom Hooks Using Webpack with Create React App JavaScript modules Create React App Exploring Create React App Webpack basics Making modifications Hot reloading; Auto-reloading Creating a production build Ejecting Using Create React App with an API server When to use Webpack/Create React App Using GraphQL Your First GraphQL Query GraphQL Benefits GraphQL vs. REST GraphQL vs. SQL Relay and GraphQL Frameworks Chapter Preview Consuming GraphQL Exploring With GraphiQL GraphQL Syntax 101 . Complex Types Exploring a Graph Graph Nodes ; Viewer Graph Connections and Edges Mutations Subscriptions GraphQL With JavaScript GraphQL With React

Mental Health in Education Update
By Brightcore Consultancy
During this live-online masterclass we will focus on understanding recent developments in the mental health and wellbeing of children in the UK, including looking at the impact of cultural and technological changes over recent years and the impact this is having in schools.