- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1266 Management courses in Glasgow
Network DevOps course description This course is not a soft skills course covering the concepts of DevOps but instead concentrates on the technical side of tools and languages for network DevOps. Particular technologies focussed on are ansible, git and Python enabling delegates to leave the course ready to starting automating their network. Hands on sessions follow all major sections. More detailed courses on individual aspects of this course are available. What will you learn Evaluate network automation tools. Automate tasks with ansible. Use git for version control. Use Python to manage network devices. Use Python libraries for network devices. Network DevOps course details Who will benefit: Administrators automating tasks. Prerequisites: TCP/IP Foundation Duration 5 days Network DevOps course contents What is DevOps Programming and automating networks, networks and clouds, AWS, OpenStack, SDN, DevOps for network operations. Initial configuration Configuring SSH, ZTP, POAP. Hands on Initial lab configuration. Getting started with ansible The language, the engine, the framework. Uses of ansible, orchestration. The architecture, Controlling machines, nodes, Agentless, SSH, modules. Configuration management, inventories, playbooks, modules, roles. Hands on Installing ansible, running ad hoc commands. Ansible playbooks ansible-playbook, YAML, plays, tasks, handlers, modules. Playbook variables. Register module, debug module. Hands on Running playbooks. Ansible Inventories /etc/ansible/hosts, hosts, groups, static inventories, dynamic inventories. Inventory variables, external variables. Limiting hosts. Hands on Static inventories, variables in inventory files. Ansible modules for networking Built in modules, custom modules, return values. Core modules for network operations. Cisco and/or Juniper modules. ansible_connection. Ansible 2.6 CLI. Hands on Using modules. Ansible templating and roles aConfiguration management, full configurations, partial configurations. The template module, the assemble module, connection: local, Jinja2 templates, variables, if, for, roles. Hands on Generating multiple configurations from a template. Network programming and modules Why use Python? Why use ansible? alternatives, ansible tower, Linux network devices. Programming with Python Python programming Functions. Classes, objects and instances, modules, libraries, packages. Python strings, Python file handling, pip list, pip instal. Hands on Python programming with pyping. More Python programming Functions. Classes, objects and instances, modules, libraries, packages. Python strings, Python file handling, pip list, pip install. Hands on Python programming with pyping. Git Distributed version control, repositories, Git and GitHub, Alternatives to GitHub, Installing git, git workflows, creating repositories, adding and editing files, branching and merging, merge conflicts. Hands on working with Git. Python and networking APIs, Sockets, Telnetlib, pysnmp, ncclient, ciscoconfparse. Paramiko SSH and Netmiko Integrating Python and network devices using SSH. Netmiko, Netmiko methods. Hands on Netmiko. NAPALM What is NAPALM, NAPALM operations, getters, Replace, merge, compare, commit, discard. Hands on Configuration with NAPALM. Integrating ansible and NAPALM. Python and REST REST APIs, enabling the REST API. Accessing the REST API with a browser, cURL, Python and REST, the request library. Hands on Using a REST API with network devices.

Overview With the major responsibility of managing finances, managers have also responsibilities to write and control budgets. They face a number of decisions that need planning and forecasting, especially preparing budgets. Using examples and exercises from the gas and oil industry, this course is designed to break down all sorts of financial restrictions in an informative yet engaging style. It will provide the necessary skills to develop efficient strategic planning, forecasting and budgeting processes. The main aim of the training is to enable the participants to understand the framework that builds strategies for annual budgets targeting efficient management and organisational performance. Our course will explain financial terms and budgeting tools in such a way that a financial professional or even a non-financial profession will be able to understand and relate to in their working environment. It will include a lot of examples, a budgeting format and case studies.

Red Hat training course description This three day hands on course provides a comprehensive coverage of core Linux administration tasks on Red Hat Linux. What will you learn Administer & configure Linux systems. Maintain Linux by handling disk space and taking regular backups. Manage software packages. Perform basic troubleshooting. Maintain a secure Linux system. Describe the organisation and implementation of the filesystem. Red Hat training course details Who will benefit: System administrators. Network administrators. Prerequisites: Linux fundamentals Duration 3 days Red Hat training course contents Managing software Package Concepts, RPM, rpm Commands, Yum, Dependencies and Conflicts, Startup Script Problems, Shared Libraries, Library Management, Managing Processes, the Kernel: The First Process, Process Lists, Foreground & Background Processes, Process Priorities, Killing Processes. Configuring hardware Configuring Firmware and Hardware, IRQs, I/O Addresses, DMA Addresses, Boot Disks, Coldplug and Hotplug Devices, Configuring Expansion Cards and PCI Cards, Kernel Modules, USB Devices, Linux USB Drivers, Configuring Hard Disks, Partitioning Systems, LVM, Common Layouts, Creating Partitions and Filesystems, Maintaining Filesystem Health, Tuning, Journals, Checking Filesystems, Monitoring Disk Use, Mounting and Unmounting Filesystems. Managing files File Management Commands, File Naming and Wildcards, File Archiving, Links, Directory Commands, File Ownership and Group, File access control, Permissions, chmod, Defaults, File Attributes, Disk Quotas, Enabling and setting Quotas, Locating Files, The FHS. Booting Linux and editing files Installing Boot Loaders, GRUB Legacy, GRUB 2, Alternative Boot Loaders, the Boot Process, Boot Messages, Runlevels and the Initialization Process, Runlevel Functions, Runlevel Services, Alternative Boot Systems , Upstart, system. Administering the system Managing Users and Groups, Tuning User and System Environments, Using System Log Files, Understanding syslogd , Setting Logging Options, Manually Logging Data, Rotating Log Files, Reviewing Log File Contents, Maintaining the System Time, Linux Time Concepts, Manually Setting the Time, Using NTP, Running Jobs in the Future, Understanding the Role of cron, Creating System cron Jobs, Creating User cron Jobs, Using anacron, Using at. Configuring basic networking TCP/IP, Network Hardware, Network Addresses, Hostnames, Network Ports, Configuring Linux for a Local Network, Configuring with DHCP, Static IP Address, Configuring Routing, Using GUI Configuration Tools, ifup and ifdown, Diagnosing Network Connections, Testing Connectivity, Tracing a Route, Checking Network Status , Examining Network Traffic, Additional Tools. Securing your systems Administering Network Security, Super Server Restrictions, Disabling Unused Servers, Administering Local Security, Securing Passwords, Limiting root Access, Setting Login, Process, SUID/SGID Files, Configuring SSH, Using GPG, Generating, Importing and Revoking Keys, Encrypting and Decrypting Data, Signing Messages and Verifying Signatures. Clustered File Systems Principles of cluster file systems. Create, maintain and troubleshoot GFS2 file systems in a cluster, create, maintain and troubleshoot OCFS2 file systems in a cluster, Integration of GFS2 and OCFS2 with Pacemaker, the O2CB cluster stack, other commonly used clustered file systems.

DevOps training course description This course is an introduction to DevOps. The course emphasizes communication, collaboration , integration, and automation to improve the workflow between developers and IT operations professionals. Improved workflows lead to more opportunities to design software and services in a more agile fashion. This course is a basis for discovering the most important DevOps concepts and to understand the principles and methods behind this. The course will leave you with the inspiration to be the advocate of change. What will you learn Explain DevOps principles. Describe the relationship between Agile , Lean and IT Service Management ( ITSM). Describe methods for automation and technology factors. Describe considerations when changing. Describe challenges, risks and critical success factors. DevOps training course details Who will benefit: IT development, IT operations and IT service management. Prerequisites: Introduction to data communications & networking. Duration 2 days DevOps training course contents Why DevOps? Introduction DevOps Goals DevOps Added value of DevOps Proven Results DevOps for businesses DevOps principles (The Three Ways) DevOps and other frameworks DevOps and Agile DevOps and Lean DevOps and IT Service Management DevOps culture Characteristics of a DevOps culture Organizational Considerations DevOps DevOps stakeholders DevOps roles DevOps teams DevOps organizational structures DevOps methods Continuous Integration Continuous delivery Continuous deployment Value stream mapping Kanban Theory of Constraints Improvement Kata Deming's quality circle ITSM processes DevOps and Automation Methods for DevOps automation Longevity and tools categories DevOps applications Transitioning to a DevOps culture. Implementation Challenges, risks and critical success factors Measuring DevOps successes

CWNA training course description A hands-on course focusing on the technical support of WiFi. Wireless LANs are often seen as simple communications that are simply installed and then left alone to work. This course ensures that delegates will be able to install WiFi networks which work but also enable the delegates to troubleshoot WiFi when it does go wrong. What will you learn Compare 802.11 standards. Configure WiFi networks. Troubleshoot WiFi networks using spectrum analysers, Wireshark and other tools. Implement 802.11 security. Perform RF surveys. CWNA training course details Who will benefit: Technical staff working with WiFi networks. Anyone wishing to pass the CWNA exam. Prerequisites: Intro to data communications & networking Duration 5 days CWNA training course contents Introduction History, standards. RF fundamentals What is RF? Wavelength, Frequency, Amplitude, Phase. Wave behaviour. RF components. Watts, mW, dB, SNR, Link budgets. Hands on Spectrum analysis. Listing WiFi networks. WiFi connection. inSSIDer. Antennas Radiation envelopes, polar charts, gain, Antenna types. Line of Sight, MIMO. Hands on Connecting, installing, changing antennae. RSSI values. 802.11 802.11-2007, 802.11 post 2007, 802.11 drafts. 802.11 b/g/n. Hands on WiFi performance measurement. Spread Spectrum RF frequency bands, FHSS, DSSS, OFDM. Channels. Hands on Configuring channels. Topologies Mesh, Access points, distribution systems, SSID. Hands on AP configuration. Client connection profiles. 802.11 MAC CSMA/CA, Management frames, control frames, data frames. Passive scanning, active scanning. Open system authentication. Shared Key authentication. Association. RTS/CTS. Power management. Hands on Capturing frames, analysing frames. WiFi architecture WiFi client, WLAN architecture: Autonomous, Centralised, distributed. WiFi bridges. WiFi routers. PoE. Hands on WLAN controllers. Troubleshooting RF interference, multipath, adjacent channels, low SNR, mismatched power. Coverage, capacity. 802.11 Security Basics, Legacy security: WEP, MAC filters, SSID cloaking. PSK, 8021.X/EAP, WPA/WPA2. TKIP/ CCMP encryption. Guest WLANs. Wireless attacks, intrusion monitoring. Hands on WEP cracking, WPA2 configuration. RADIUS. RF Site surveys Protocol and spectrum analysis, coverage analysis. Site survey tools. Hands on Performing a site survey.

4G training course description This course is designed to give the delegate an understanding of the technologies used within a 3G UMTS mobile network. During the course we will investigate the UMTS air interface and the use of Wideband-Code Division Multiple Access (WCDMA) to facilitate high speed data access, together with HSPA to offer mobile broadband services. We will describe the use of soft handover rather than hard handover procedures and soft capacity sharing. The course includes a brief exploration of the UMTS protocol stack and the use of PDP Context and QoS support features. What will you learn Explain the 3G UMTS architecture. Describe the role of a Drifting & Serving RNC. Explain the use of ARQ & HARQ for mobile broadband. Describe how IMS integrates into the architecture. Describe the use of Media Gateway Controllers. Identify the temporary identities used within 3G UMTS. 4G training course details Who will benefit: Anyone working within the telecommunications area, especially within the mobile environment. Prerequisites: Mobile communications demystified Telecommunications Introduction Duration 2 days 4G training course contents LTE Introduction The path to LTE, 3GPP. LTE to LTE advanced. LTE Architecture The core, Access, roaming. Protocols: User plane, Control plane. Example information flows. Bearer management. Spectrum allocation. LTE technologies Transmission, reception, OFDMA, multiple antenna, MIMO. LTE Air interface Air interface protocol stack. Channels, Resource Grid, cell acquisition. Up and downlink controls. Layer 2 protocols. Cell acquisition Power on, selecting networks and cells. RRC connection. Attach procedure. Mobility management Roaming, RRC_IDLE, RRC_CONNECTED, cell reselection, handover, interoperation with UMTS and GSM networks. Voice and text IMS, QoS, policy and charging.

Total QoS training course description An advanced technical hands on course focusing on Quality of Service issues in IP networks. What will you learn Explain the difference between Integrated services and differentiated services. Explain how DiffServ works. Explain how RSVP works. Design networks supporting QoS. Total QoS training course details Who will benefit: Network administrators. Network operators. Prerequisites: TCP/IP Foundation for engineers Duration 3 days Total QoS training course contents What is QoS QoS and CoS, throwing bandwidth at the problem, Best effort services, Differentiated services, Integrated services, guarantees, the need for QoS, IETF working groups. Application issues Video, Voice, other applications, Jitter, delay, packet loss. Flows, per flow and per aggregate QoS, Stateful vs. stateless QoS, applications vs. network QoS. 'Traditional' IP QoS The TOS field and precedence, the obsolete OSPF use of the TOS field, TCP congestion avoidance. Queuing Where to use queuing, FIFO, Priority queuing, Custom queuing, Weighted Fair Queuing, CBWFQ, PQWFQ, LLQ, RED and WRED. DiffServ Architecture, DSCP, CU, packet classification and marking, meters and conditioners, Bandwidth brokers and COPS, Per Hop Behaviours, best effort PHB, Assured Forwarding PHB, Expedited forwarding PHB, Network Based Application Recognition (NBAR). Layer 2 issues Fragmentation and interleaving, compression (codecs, MPEG formats, header compressionâ¦), 802.1p, Subnet bandwidth management, Bandwidth allocators and requestor modules, the use of MPLS, traffic engineering, traffic shaping. RSVP What is RSVP? architectures, paths, path messages, reservations, traffic specifications, tear downs, guaranteed and controlled load, token buckets, Call Admission Control in voice networks, gatekeepers. Other issues Policy based routing, the Resource Allocation Protocol, QoS management tools, baselining networks, design issues, QoS in IPv6, QoS and multicasts.

DWDM training course description A concise overview of Wave Division Multiplexing (WDM) with both Coarse Wave Division Multiplexing (CWDM) and Dense Wave Division Multiplexing (DWDM) being covered. The course starts with a review of the relevant elements of fibre transmission and multiplexing before then studying WDM components and architectures. Reliability, resilience and management are then followed by WDM services and futures. What will you learn Explain the benefits of WDM. Describe Dispersion and four way mixing. Describe the different WDM equipment components. Describe different WDM architectures. Explain How DWDM works. DWDM training course details Who will benefit: Anyone working with CWDM/DWDM. Prerequisites: Telecommunications Introduction Duration 2 days DWDM training course contents Fibre communications review Optical transmission, Fibre characteristics, Fibre component parts. Multi Mode Fibre (MMF). Single Mode Fibre (SMF). Fibre connections. Lasers. Attenuations, dispersion, optical signal noise ratios (OSNR) and their effects. Channel Spacing and Signal Direction. Limiting factors to single wavelength. WDM overview Multiplexing, TDM, WDM benefits. WDM standards. CWDM vs. DWDM. Four Wave Mixing (FWM). Impact and countermeasures to FWM on WDM. CWDM ITU G.694.2, channels, channel spacing. DWDM ITU G.694.1, channels, channel spacing. WDM Equipment Components Equipment components and building blocks. Optical Terminal Multiplexers (OTM). Optical Add/Drop Multiplexers (OADM). Adding versus dropping. Optical Amplifiers. Erbium Doped Fibre Amplifiers (EDFA). Transponders and Combiners. WDM/DWDM Hubs. Optical and Electrical Cross Connects (OXCs/DXCs). Types of Cross Connects (Transparent/Opaque). Advantages and disadvantages of various Optical cross connects. WDM Architectures WDM network sections. Point-to-Point, Optical switches, mesh, ring and star topology. Example of combined WDM and other technology network. Wavelength converting transponders, 1R, 2R, 3R. Protection for WDM Sub 50ms failover. Equipment protection. Card protection. Y cable, Splitter protection. Far end laser control. Line protection. OMSP 1+1, OMSP 1:1, OMSP 1: N. Self healing optical ring. Sub Network Connection Protection (SNCP). Automatically Switched Optical Networks (ASON). WDM Management Options In band management. Out of band management. The Optical Supervisory Channel (OSC). OSC capabilities. WDM services WDM Access. Bit rates, Transparent Networks. Modulation, DQPSK. SDH over WDM. Migrating from SDH to DWDM. Ethernet over WDM, IP over WDM. Optical Transport Networks G.709, 'digital wrapper', Optical Channel Payload Unit (OPU), Optical Channel Transport Unit ( OTU), Optical Channel Data Unit (ODU). OTU1, OTU2, OTU3, OTU4. WDM Futures All optical amplification, Raman amplification, distributed, lumped. Bit rates. Solitons. Coherent technologies.

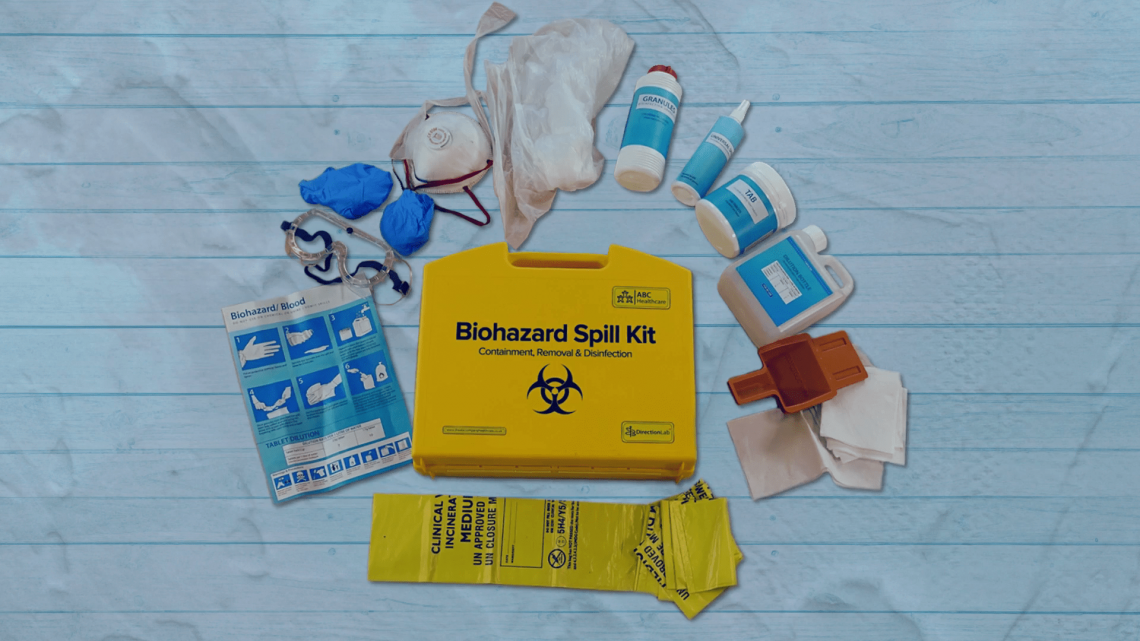
Biohazard Safety: Managing Blood and Body Fluid Spillages Instructor
By Guardian Angels Training
Gain expertise in biohazard safety with our "Biohazard Safety: Managing Blood and Body Fluid Spillages Instructor Training" course. Ideal for healthcare professionals, lab staff, and emergency responders.
Search By Location
- Management Courses in London
- Management Courses in Birmingham
- Management Courses in Glasgow
- Management Courses in Liverpool
- Management Courses in Bristol
- Management Courses in Manchester
- Management Courses in Sheffield
- Management Courses in Leeds
- Management Courses in Edinburgh
- Management Courses in Leicester
- Management Courses in Coventry
- Management Courses in Bradford
- Management Courses in Cardiff
- Management Courses in Belfast
- Management Courses in Nottingham