- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
3113 Management courses in Camborne delivered Live Online
Security+ training course description A hands on course aimed at getting delegates successfully through the CompTia Security+ examination. What will you learn Explain general security concepts. Describe the security concepts in communications. Describe how to secure an infrastructure. Recognise the role of cryptography. Describe operational/organisational security. Security+ training course details Who will benefit: Those wishing to pass the Security+ exam. Prerequisites: TCP/IP foundation for engineers Duration 5 days Security+ training course contents General security concepts Non-essential services and protocols. Access control: MAC, DAC, RBAC. Security attacks: DOS, DDOS, back doors, spoofing, man in the middle, replay, hijacking, weak keys, social engineering, mathematical, password guessing, brute force, dictionary, software exploitation. Authentication: Kerberos, CHAP, certificates, usernames/ passwords, tokens, biometrics. Malicious code: Viruses, trojan horses, logic bombs, worms. Auditing, logging, scanning. Communication security Remote access: 802.1x, VPNs, L2TP, PPTP, IPsec, RADIUS, TACACS, SSH. Email: S/MIME, PGP, spam, hoaxes. Internet: SSL, TLS, HTTPS, IM, packet sniffing, privacy, Javascript, ActiveX, buffer overflows, cookies, signed applets, CGI, SMTP relay. LDAP. sftp, anon ftp, file sharing, sniffing, 8.3 names. Wireless: WTLS, 802.11, 802.11x, WEP/WAP. Infrastructure security Firewalls, routers, switches, wireless, modems, RAS, PBX, VPN, IDS, networking monitoring, workstations, servers, mobile devices. Media security: Coax, UTP, STP, fibre. Removable media. Topologies: Security zones, DMZ, Intranet, Extranet, VLANs, NAT, Tunnelling. IDS: Active/ passive, network/host based, honey pots, incident response. Security baselines: Hardening OS/NOS, networks and applications. Cryptography basics Integrity, confidentiality, access control, authentication, non-repudiation. Standards and protocols. Hashing, symmetric, asymmetric. PKI: Certificates, policies, practice statements, revocation, trust models. Key management and certificate lifecycles. Storage: h/w, s/w, private key protection. Escrow, expiration, revocation, suspension, recovery, destruction, key usage. Operational/Organisation security Physical security: Access control, social engineering, environment. Disaster recovery: Backups, secure disaster recovery plans. Business continuity: Utilities, high availability, backups. Security policies: AU, due care, privacy, separation of duties, need to know, password management, SLAs, disposal, destruction, HR policies. Incident response policy. Privilege management: Users, groups, roles, single sign on, centralised/decentralised. Auditing. Forensics: Chain of custody, preserving and collecting evidence. Identifying risks: Assets, risks, threats, vulnerabilities. Role of education/training. Security documentation.

SAFe Advanced Scrum Master: In-House Training
By IIL Europe Ltd
SAFe® Advanced Scrum Master: In-House Training Prepare to step into a SAFe® leadership role and learn how to facilitate Agile team, program, and enterprise success by becoming a SAFe® 5 Advanced Scrum Master (SASM). This course prepares current Scrum Masters for their leadership role in facilitating Agile team, program, and enterprise success in a SAFe® implementation. Explore facilitation of cross-team interactions in support of program execution and relentless improvement. Expand the Scrum paradigm with an introduction to scalable engineering and DevOps practices, the application of Kanban to facilitate the flow of value, and supporting interactions with architects, product management, and other critical stakeholders. Learn actionable tools for building high-performing teams and explore practical ways of addressing Agile and Scrum anti-patterns in the enterprise. What you will Learn To perform the role of a SAFe® Advanced Scrum Master, you should be able to: Apply SAFe® principles to facilitation, enablement, and coaching in a multi-team environment Build a high-performing team and foster relentless improvement at scale Address Agile and Scrum anti-patterns Support the adoption of engineering practices, DevOps, and Agile architecture Learn to apply Kanban and Extreme Programming (XP) frameworks to optimize flow and improve the team's work Facilitate program planning, execution, and delivery of end-to-end systems value Support learning through participation in communities of practice and innovation cycles Exploring the Scrum Master role in the SAFe® enterprise Applying SAFe® Principles: A Scrum Master's perspective Exploring Agile and Scrum anti-patterns Facilitating program execution Improving flow with Kanban and XP Building high-performing teams Improving program performance with Inspect and Adapt

Project Stakeholder Relationship Skills (Virtual)
By IIL Europe Ltd
Project Stakeholder Relationship Skills (Virtual) This course is designed to provide project managers with the ability to: Analyze the complexities of major stakeholder relationship categories Apply the most appropriate interpersonal relationship skills to the different categories of relationships Align the dynamic needs of the stakeholders with a project's objective throughout the project life cycle What You Will Learn At the end of this program, you will be able to: Gain a deep understanding of the Scrum Framework - the theory, practices, roles, rules, and values - as defined in The Scrum Guide Understand, in detail, the role of Scrum Master, and how the role interacts with different members of the Scrum Team and other stakeholders Master the Scrum principles to better understand their application when returning to the workplace Understand how to construct an effective development team with an appropriate mix of skills and experience Know how to act as a servant-leader for the Scrum Team, promoting and enabling self-organization to create high-value products. Learn how to facilitate Scrum Events and remove impediments to the Scrum Team's progress Help Scrum Product Owners shape and refine product backlogs to guide early and incremental delivery of valuable products Drive adoption of the Scrum framework for more effective product and solution development, working with stakeholders and other Scrum Masters to improve its effectiveness Foundation Concepts Stakeholders and project success Stakeholder management research Managing stakeholder relationships Identifying Stakeholders Stakeholder categories Stakeholder relationships across the project life cycle Tools and techniques for identifying stakeholders Assessing Stakeholders Assessing stakeholder relationships Recognizing stakeholder attitudes toward the project Analyzing stakeholders Using other types of stakeholder assessments Building Stakeholder Relationships The importance of psychological safety Building trust and getting results The anatomy of trust Navigating Challenging Situations Dynamics of conflict Responding to conflict Managing difficult conversations

Microsoft security training course description A hands on training course focusing on security in the Microsoft environment. The course progresses from patch management onto the use of Microsoft security tools. Then server, desktop and network security are studied in the Microsoft environment. What will you learn Use Microsoft security tools. Secure Microsoft servers. Secure Microsoft desktops. Secure Microsoft networks. Microsoft security training course details Who will benefit: Technical server support staff. Technical desktop support staff. Technical network staff. Technical security staff. Prerequisites: Supporting Windows server 2016 Networking Microsoft systems. Duration 3 days Microsoft security training course contents Introduction Security threats, Microsoft defaults, admin accounts, security patches, patch management, patch tools. Hands on: Studying Microsoft defaults, applying security patches. Microsoft security tools Microsoft updates, WSUS, Inventory tool, baseline security analyser, URLscan, EventCombMT, Cipher security tool, Port reporter, PortQry. Tools hackers use. Hands on: Using Microsoft security tools. Server security Checklists, core server security, AD, Member server security, Domain controller security, Specific roles. Hands on Hardening Microsoft servers, security templates. Active Directory Admin authority in AD, group policy, trust and authentication. Desktop security Checklists, core client security, anti virus software, anti spyware software, firewalls, securing clients with AD, securing clients with group policy, software restriction policies. Hands on Securing Microsoft desktops. Network security Checklist, IP security, VPNs, PKI, certificate authorities, RAS, RRAS, IAS. Hands on: VPN configuration, IAS configuration. Monitoring Auditing, authorisation and logons, tracking, system monitoring, detecting attacks. Hands on: Monitoring Microsoft systems. Summary Microsoft security response centre, security advisories.

Scrum Master and Product Owner Workshop: In-House Training
By IIL Europe Ltd
Scrum Master and Product Owner Workshop This workshop builds on the specific roles and responsibilities of the Product Owner and Scrum Master in a Scrum environment, and how they need to work together as part of the Scrum methodology. During these sessions, you will explore who does what before, during, and after the Scrum Sprint cycles, as well as how to make the process work best in your specific Agile environment. You will come away from this workshop with a much deeper understanding of the roles and responsibilities so that individual performance improves on the job. Improved target results include providing focused leadership, making effective decisions, guiding Agile teams, and delivering business value. Foundation Concepts Agile History, Values, and Mindset Introduction to Scrum Scrum Events Scrum Artifacts Scrum Roles and Responsibilities Scrum Roles Product Owner Responsibilities Scrum Master Responsibilities The Scrum Team Responsibilities Cross-functional Teams Product Ownership Product Ownership Vision Understand Your Customers and Market Stakeholder Management and Engagement Product Backlog What is a User Story? Epics and User Stories Acceptance Criteria Preparing User Stories for a Sprint Definition of Ready (DoR) and Definition of Done (DoD) User Story Estimation Using Planning Poker Backlog Grooming Roadmaps, Story Maps, Impact Mapping Product Backlog Prioritization, MoSCoW, Kano Analysis Technical Debt The Sprint Team Capacity and Velocity Planning Sprint Planning Meeting and Sprint Plan The Sprint: Learning to Become Self-managing, Self-organizing, Self-improving Sprint Review Meeting Retrospectives Project Progress and Completion The Daily Scrum The Task Board and The Burndown Chart Information Radiators Closing a Scrum Project Summary and Next Steps Review of course goals, objectives, and content

Overview Intro. Translating Strategy into Goals and Metrics Components of Strategy Understanding the failure of strategies Analysing you and your organisation mission, vision and strengths Introduction into Strategy Implementation Understanding Performance Management System Objectives and Measures The importance of strategy planning

Petroleum Geology for Non-Geologists
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course To the non-geologist, working with Petroleum Geologists can be confusing. Petroleum geology has specific terminology and many concepts and data sources unfamiliar to the uninitiated. This course has been designed to introduce these terms and provide an insight into how oil and gas are formed, how they are found and how they are extracted. Using a holistic combination of lectures, experiments, case study and practical exercises, the course involves an introduction to fundamental geological concepts, to exploration techniques, prospecting, drilling, well logs and recovery methods. The course will also demystify the terminology surrounding petroleum geology, demonstrate the use of geological information to show the value and weakness of different datasets, and lead to better communication and decision-making between the geologists and non-geologists. It will feature world-class virtual reality field trips that incorporate activities and features unavailable in the physical field, and provide for a more integrated and flexible learning resource (also see the trainer's article on page 4 which was first published in GEO ExPro Magazine, the upstream oil and gas industry's favourite magazine). Course Highlights: Course facilitator has delivered petroleum geology training to many companies over the years Facilitator is also a professionally trained teacher and former university lecturer who is experienced in communicating with people at all levels of technical knowledge Practical exercises, experiments, examination of real rocks, a virtual reality field trip and case study are used to clarify and reinforce important concepts Training Objectives By attending this training, you will be able to acquire the following: Understand the geological methods and principles used in hydrocarbon exploration, development and production. Understand the key elements of a petroleum system, from hydrocarbon source to reservoir and seal Appreciate basin analysis, regional geology and play based exploration techniques Be aware of the different sorts of hydrocarbon trap from structural to stratigraphic Understand the technical terminology, tools and methods used in exploration geology Learn about unconventional Understand and evaluate the sources and reliability of various types of geological information Understand acquisition, processing and interpretation of seismic data Learn the technical processes and terminology involved in exploration Understand how a prospect is defined and risked Understand how seismic, existing well information and outcrop geology can be used for exploration Gain an understanding of the methods used for petroleum geology to allow a discovery to be appraised and then developed Target Audience The course is suitable to all personnel, but those that benefit most include: This course will benefit Petroleum Engineers (reservoir, drilling, production) who work with geological data, Geophysicists with little or no geological background, Project managers whose teams include petroleum geologists, Finance, Procurement, Marketing and Communications staff, and government Data Managers who handle petroleum geological data and need to understand the sources of different types of data. Trainer Your expert course leader is the Geosciences Technical Director for PetroEdge. She was previously, the manager of Robertson Petroleum Training Centre and a Senior Project Scientist at Robertson CGG. She has over 20 years of experience in teaching geology and leading field trips. Prior to her 8 years at Robertson, she was in academia as a lecturer for 6 years and a Research Fellow for 3 years. She has conducted fieldwork and led field trips in the US and many areas in the UK. In addition, she has led university regional geology day schools and has comprehensive experience in course and study programme writing. She has extensive experience in delivering courses and in Clastic and Carbonate Reservoir Geology, Deepwater Turbidites, Sandstone Reservoirs, Wireline Log Interpretation, Integrated Sequence Stratigraphy, Basin Analysis and Exploration & Appraisal workshops globally. In delivering the Exploration Team Management Workshop, she has project managed and taught key principles and modules on project planning, data collection/collation, geophysical assessment, stratigraphy and facies mapping, source rock facies and hydrocarbon generation, play fairway mapping, risking and prospect evaluation. Her knowledge and enthusiasm for instructing is reflected in consistently being rated as excellent by trainees, and clients specifically requesting her participation in courses. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

SAFe Advanced Scrum Master: Virtual In-House Training
By IIL Europe Ltd
SAFe® Advanced Scrum Master: Virtual In-House Training Prepare to step into a SAFe® leadership role and learn how to facilitate Agile team, program, and enterprise success by becoming a SAFe® 5 Advanced Scrum Master (SASM). This course prepares current Scrum Masters for their leadership role in facilitating Agile team, program, and enterprise success in a SAFe® implementation. Explore facilitation of cross-team interactions in support of program execution and relentless improvement. Expand the Scrum paradigm with an introduction to scalable engineering and DevOps practices, the application of Kanban to facilitate the flow of value, and supporting interactions with architects, product management, and other critical stakeholders. Learn actionable tools for building high-performing teams and explore practical ways of addressing Agile and Scrum anti-patterns in the enterprise. What you will Learn To perform the role of a SAFe® Advanced Scrum Master, you should be able to: Apply SAFe® principles to facilitation, enablement, and coaching in a multi-team environment Build a high-performing team and foster relentless improvement at scale Address Agile and Scrum anti-patterns Support the adoption of engineering practices, DevOps, and Agile architecture Learn to apply Kanban and Extreme Programming (XP) frameworks to optimize flow and improve the team's work Facilitate program planning, execution, and delivery of end-to-end systems value Support learning through participation in communities of practice and innovation cycles Exploring the Scrum Master role in the SAFe® enterprise Applying SAFe® Principles: A Scrum Master's perspective Exploring Agile and Scrum anti-patterns Facilitating program execution Improving flow with Kanban and XP Building high-performing teams Improving program performance with Inspect and Adapt

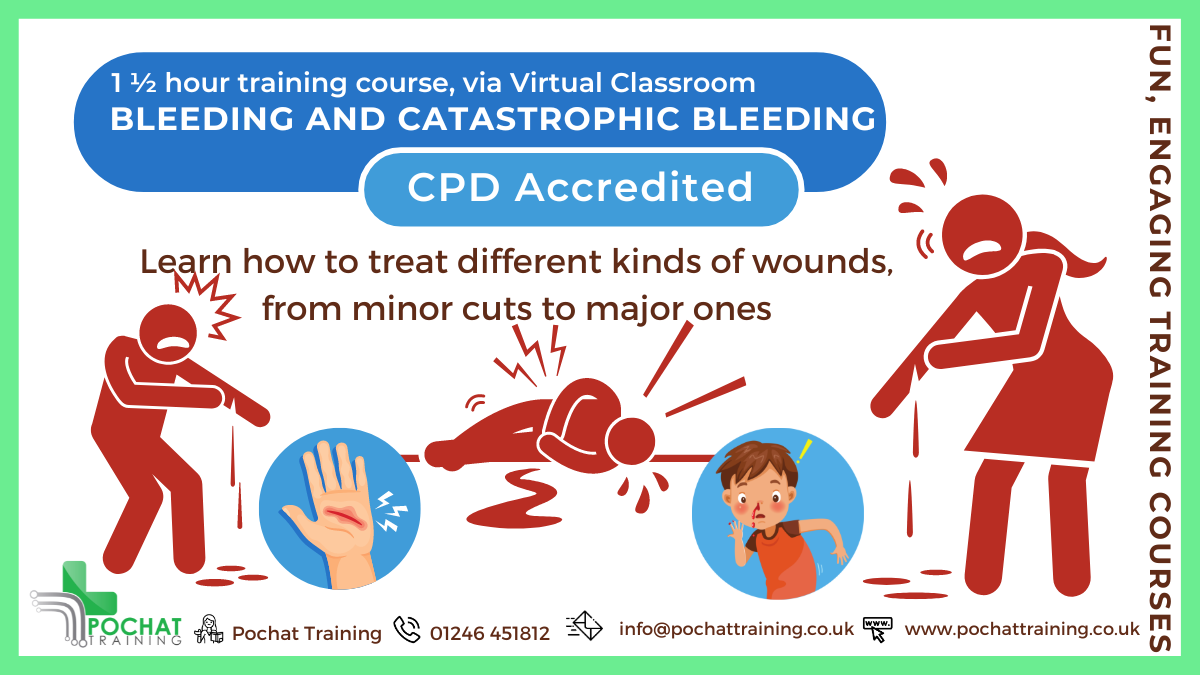
CPD Accredited, Interactive Short Course 1½ hr session Learn to deal with bleeding, from minor bleeds to catastrophic bleeds Become a life-saving hero if ever someone is seriously injured Course Contents: How to treat minor bleeding How to treat major bleeding Types of bleeding How to treat catastrophic bleeding Tourniquets Why to use a tourniquet How to use a tourniquet How to make an improvised tourniquet How to use a Tourni-Key Wound packing How to use Celox Z-Gauze How to improvise packing a wound How to treat gunshot wounds Practical elements: There is an option of learning how to deal with catastrophic bleeding in person, so you get to practice these skills (and play about with fake blood 😀). For that, see our Catastrophic Bleeding course module. Benefits of this Short Course: We all have regular injuries which cause us to bleed If not properly cared for, even a small cut can turn septic and kill or maim Serious car accidents, machinery accidents at work, weapon wounds, terrorist attacks and more can also lead to catastrophic bleeding Did you know that a person could bleed out in just five minutes..? You're got to act quick, decisive and correctly Please don't do what you see in the movies - you will kill the person even quicker...
Lexcel Standard Training Requirements Course
By DG Legal
This training is for lawyers and covers key topics to ensure compliance with the Lexcel standard and other regulations.
