- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
2903 Intelligence courses delivered Online
Basics of Chatbots with Machine Learning & Python
By Packt
Let's learn the basic concepts for developing chatbots with machine learning models. This compact course will help you learn to use the power of Python to evaluate your chatbot datasets based on conversational notes, online resources, and websites. Garner hands-on practice in text generation with Python for chatbot development.
The Business Analyst Program: A Career Launchpad for the Future Business Analysis is the process of identifying business needs, defining solutions, and implementing changes to achieve strategic goals. It involves identifying opportunities for improvement, evaluating alternatives, and recommending solutions. Business analysts play a critical role in ensuring that organisations operate effectively and efficiently. They work closely with stakeholders to identify business needs, and then work to find solutions that meet those needs while also staying within budget and timelines. The Business Analysis course is designed to equip students with the skills and knowledge necessary to become successful business analysts. The course covers a range of topics, including business processes, strategic analysis, solution evaluation, stakeholder management, and process improvement. By the end of the course, students will have a solid understanding of what it takes to be a successful business analyst. If you're looking for a career in IT, the Business Analyst Program is the perfect place to start. This program will provide you with the skills and knowledge you need to become a successful Business Analyst. In addition to the training, you'll also receive career mentoring and support. Our experienced career counsellors will help you develop your resume, write cover letters, and practice your interviewing skills. They'll also connect you with potential employers and help you land your dream job. The Business Analyst Program is the perfect way to launch your career in IT. We will help you until you find a job, so you won't have to worry about anything. Just gain knowledge and learn skills, getting you a job is our duty. With our comprehensive training and career support, you'll be well on your way to a successful and rewarding career in this exciting field. Don't miss your chance to join the Business Analyst Program! Apply today! Our mission is simple: To be your trusted partner and assist you every step of the way until you land the job of your dreams. Why Choose Us Here's what makes our Business Analyst Training stand out from the crowd: Personalised Job Search Assistance: We're in this together! Our dedicated team will work tirelessly to support your entire job searching process. From crafting a standout resume to submitting it to top companies, we'll ensure you have a compelling application that gets noticed. Expertly Crafted CV: Your resume is your ticket to the interview room. Our professional resume writers will create a customised CV highlighting your unique skills and experiences. This will maximise your chances of standing out among the competition. Strategic Placement: We understand the power of casting a wide net. We'll strategically submit your CV to various platforms and networks, expanding your reach and connecting you with valuable opportunities that align with your career goals. One-On-One Consultation Sessions with Industry Experts: Gain invaluable insights and guidance from seasoned professionals who have thrived in the Business Analysis field. Our consultation sessions provide you with insider tips, tricks, and advice, empowering you to navigate the industry with confidence and expertise. Comprehensive Skill Development: Our program is designed to equip you with the most sought-after skills in the Business Analysis sector. From mastering cutting-edge tools to honing your skills, we'll ensure you have the knowledge and expertise to excel in any IT-driven environment. Ongoing Support: We understand that the journey to landing your dream job doesn't end with placement. That's why our commitment to your success extends well beyond your initial training. Our support team will be available to answer your questions, provide guidance, and assist you as you progress in your career. Here are the 6 courses we will provide once you enrol in the program: Course 01: Business Analysis Strategy and Evaluation Course 02: The Business Intelligence Analyst Course Course 03: Business English and Communication Skills Course 04: Economics Course 05: Business Law Course 06: Financial Analysis Methods These courses will help you to develop your knowledge and skills to become a successful Business Analyst. The Program is completed in 5 easy steps: Step 1 - Enrol in the program and start learning from the courses we provide After you enrol in this Business Analyst Program, you will get lifetime access to 6 premium courses related to Business Analysis. These courses will teach you the knowledge and skills required to become a successful Business Analyst. Our customer service team will help you and keep in contact with you every step of the way. Step 2 - Complete your courses and get certifications After learning from the courses, you must obtain certificates for each course. There will be exams for every course, and you have to pass them to get your certificate. To pass successfully, you must get 90% marks for the first course and 80% for the rest of the relevant courses. Once you pass the exams, you will receive hardcopy certificates. These certificates will prove that you're an expert in the subject. Step 3 - Get a consultation session from a professional Business Analyst Take your Business Analysis skills to new heights with a one-on-one consultation session led by a seasoned professional. Gain invaluable insights, expert tips, and tailored advice that will propel your career forward. Step 4 - Complete the CV and attend the interview Once you've successfully obtained the certifications, our team of professionals will build you a compelling CV and LinkedIn profile. With these powerful tools in hand, you'll be fully prepared to tackle job interviews confidently. Kickstart your Business Analysis career with a starting salary ranging from •30,000 to •50,000 annually. Step into the IT industry with the assurance of a promising future. Step 5 - We will not leave you until you get a job Our commitment to your success goes above and beyond. We won't stop until you land that dream job. With personalised support, expert guidance, and unwavering dedication, we'll be by your side until you secure the perfect opportunity. Your job search becomes our mission, ensuring you have the best chance at a successful career in Business Analysis. Don't let your dream career as a Business Analyst remain out of reach. You just have to learn and gain knowledge and skills. Finding a job is our task! We will remove most of your worries and help you focus on only developing your skills. So join our Business Analyst Training Program today, and let us be your trusted partner on your journey to success. CPD 100 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This Business Analyst Training program is ideal for: Aspiring IT professionals looking to launch a career in Business Analysis. Individuals with a passion for technology and problem-solving who lack experience in the IT industry. Recent graduates or career changers seeking comprehensive mentoring and support in theBusiness Analysis field. Those who desire personalised guidance and one-on-one counselling to navigate the complexities of the IT job market. Individuals who want to build a strong foundation in Business Analysis and secure job opportunities with the help of industry experts. Requirements No experience required. Just enrol & start learning. Career path Embark on a rewarding career as an Business Analyst in the UK. Gain valuable experience and certifications while providing essential technical support to organisations. Progress into roles such as Administrative Manager,Program Manager, Business Manager,Business Management Analyst, with opportunities for growth and advancement. Certificates CPD Accredited e-Certificate Digital certificate - Included CPD Accredited Framed (Hardcopy) Certificate Hard copy certificate - Included Enrolment Letter Digital certificate - Included Student ID Card Digital certificate - Included

M.D.D LONELINESS SUPPORT PACKAGE (DEPRESSION/LONELINESS)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
Per month Someone to go out with every weekend Anonymity M.D.D Worker will pose as a friend 4 weeks of company on the weekends and receiving coaching simultaneously Life coaching Social skills training Emotional intelligence training 30 min call per day on weekdays https://relationshipsmdd.com/product/loneliness-support-package/

Boost Your Career with Apex Learning and Get Noticed By Recruiters in this Hiring Season! Get Hard Copy + PDF Certificates + Transcript + Student ID Card worth £160 as a Gift - Enrol Now Gain the skills and knowledge to work in criminal intelligence. Whether you are already working in the sector, someone who is interested in a career in criminal intelligence, or simply a layperson interested in learning more about the fascinating discipline of security and criminology, this Forensic Science course is for you. In this Forensic Science course, you will learn about crime science, pattern detection and analytical techniques. You will explore research methods and criminal statistics. You will learn about white-collar crime, hate crime, counter-terrorism and forensic psychology, and learn to understand the way the criminal justice system responds to criminal activity. Take this course anywhere and at any time. Don't let your lifestyle limit your learning or your potential. Forensic Science will provide you with the CPD certificate that you'll need to succeed. This Forensic Science Bundle Consists of the following Premium courses: Course 01: Online Training on Forensic Science Course 02: Forensic Anthropology: Skeletal Analysis Course 03: Computer Hacking Forensic Investigator Course 04: Digital Forensics for Cyber Professionals Course 05: Criminal Intelligence and Crime Analysis Complete Diploma Course 06: Criminal Psychology Course Level 2 Course 07: Emotional Intelligence and Human Behaviour Course 08: Criminal Law Course 09: Fraud Management & Anti Money Laundering Awareness Complete Diploma Course 10: Data Protection and Data Security Level 2 Course 11: Creativity and Problem Solving Skills Gain experience online and interact with experts. This can prove to be the perfect way to get noticed by a prospective employer and stand out from the crowd. Forensic Science has been rated and reviewed highly by our learners and professionals alike. We have a passion for teaching, and it shows. All of our courses have interactive online modules that allow studying to take place where and when you want it to. The only thing you need to take Forensic Science is Wi-Fi and a screen. You'll never be late for class again. Experienced tutors and mentors will be there for you whenever you need them, and solve all your queries through email and chat boxes. Benefits you'll get choosing Apex Learning for this Forensic Science: Pay once and get lifetime access to 11 CPD courses Certificates, student ID for the title course included in a one-time fee Free up your time - don't waste time and money travelling for classes Accessible, informative modules designed by expert instructors Learn at your ease - anytime, from anywhere Study the course from your computer, tablet or mobile device CPD accredited course - improve the chance of gaining professional skills Gain valuable knowledge without leaving your home How will I get my Certificate? After successfully completing the course you will be able to order your CPD Accredited Certificates (PDF + Hard Copy) as proof of your achievement. PDF Certificate: Free (Previously it was £6*11 = £66) Hard Copy Certificate: Free (For The Title Course: Previously it was £10) This course curriculum has been designed by experts with years of experience behind them. The course is extremely dynamic and well-paced to help you understand Forensic Science with ease. You'll discover how to master the Forensic Science skill while exploring relevant and essential topics. Curriculum of the Bundle Course 01: Online Training on Forensic Science The History and Organisation Crime Scene Investigation Collecting and Packaging Physical Evidence Fingerprints: Your Personal Signature Bloodstain Analysis DNA Analysis Drug Analysis Firearms Examination Questioned Documents: Handwriting And Forgery Examination Digital Evidence Forensic Psychology: Delving into the Criminal Mind Course 02: Forensic Anthropology: Skeletal Analysis Course outline The field of Anthropology Forensic Anthropology Human Osteology Comparative Osteology Estimation of sex from skeletal remains Estimating age at death from skeletal remains Estimating stature, BMI, and MNI Estimating ancestral affiliation Analyzing bones for trauma Writing it up! Ethical Considerations Exercise Answers Textbooks Course 03: Computer Hacking Forensic Investigator Overview Overview Reconnaissance Protocols Windows Hacking Attacking Web Technologies Pen Testing Wireless Networks Forensic Investigation Examination and Analysis Protocols Digital Evidence Artifacts Other Forensics Incident Handling Course 04: Digital Forensics for Cyber Professionals Course Overview Building Your Forensics Lab Environment Using VirtualBox Using Kali Forensic Mode and Autopsy Digital Forensics Case Management Open-source intelligence (OSINT) Computer Forensics Using Shodan to Search for Vulnerable devices Stenography Network forensics Using Wireshark Practice What You Have learned Course 05: Criminal Intelligence and Crime Analysis Complete Diploma Introduction to Intelligence Analysis Criminal Intelligence Analysis Criminal Intelligence Analyst - Skills and Competencies Understanding Criminal Psychology Research Methods in Crime Analysis Decision Making in Criminal Intelligence Analysis Intelligence-Led Policing Counterterrorism and Criminal Intelligence Analysis Technology in Criminal Intelligence Analysis The Criminal Justice System in England and Wales Course 06: Criminal Psychology Course Level 2 Understanding Criminal Psychology Influence of Mental Disorders Classification of Crime Victimology The Criminal Justice System in England and Wales Course 07: Emotional Intelligence and Human Behaviour Human Behaviour and Basic Psychological Process Evolutionary Perspective of Human Behaviour Human Intelligence Intelligence Test and Variations in Intelligence Learning and Conditioning Language and Communication Introduction to Emotion Emotion Influences Cognition Stress, Anger and Conflict Emotional Intelligence Self-Leadership Neuro-Linguistic Programming (NLP) Course 08: Criminal Law Introduction to Criminal Law Elements of a Crime Incitement, Conspiracy and Attempt Accomplice Crime Prevention The Police Prosecution, Caution and Diversion Youth Justice The Trial Sentencing Process Homicide Offences against Person Sexual Offences Theft Blackmail, Robbery & Burglary White-Collar Crime Terrorism & Law Property Offences Cybercrime & Piracy Prisons Probation Service War Crimes Course 09: Fraud Management & Anti Money Laundering Awareness Complete Diploma Introduction to Money Laundering Proceeds of Crime Act 2002 Development of Anti-Money Laundering Regulation Responsibility of the Money Laundering Reporting Office Risk-based Approach Customer Due Diligence Record Keeping Suspicious Conduct and Transactions Awareness and Training Course 10: Data Protection and Data Security Level 2 GDPR Basics GDPR Explained Lawful Basis for Preparation Rights and Breaches Responsibilities and Obligations Course 11: Creativity and Problem Solving Skills Getting Started The Problem Solving Method Information Gathering Problem Definition Preparing for Brainstorming Generating Solutions (I) Generating Solutions (II) Analyzing Solutions Selecting a Solution Planning Your Next Steps Recording Lessons Learned CPD 125 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Anyone from any background can enrol in this Forensic Science bundle. Requirements This Forensic Science course has been designed to be fully compatible with tablets and smartphones. Career path Having this various expertise will increase the value of your CV and open you up to multiple job sectors. Certificates Certificate of completion Digital certificate - Included Certificate of completion Hard copy certificate - Included You will get the Hard Copy certificate for the title course (Online Training on Forensic Science) absolutely Free! Other Hard Copy certificates are available for £10 each. Please Note: The delivery charge inside the UK is £3.99, and the international students must pay a £9.99 shipping cost.

Thinking about learning more about the data you are using in your job and how to present this? The BCS Foundation Award in Data Visualisation teaches how data is used to make decisions in an organisation and the importance of presenting accurate data in a way that enables decision making to happen.

Do you want to prepare for your dream job but strive hard to find the right courses? Then, stop worrying, for our strategically modified Data Analyst Training: Boost Your Career bundle will keep you up to date with the relevant knowledge and most recent matters of this emerging field. So, invest your money and effort in our 33 course mega bundle that will exceed your expectations within your budget. The Data Analyst Training: Boost Your Career related fields are thriving across the UK, and recruiters are hiring the most knowledgeable and proficient candidates. It's a demanding field with magnitudes of lucrative choices. If you need more guidance to specialise in this area and need help knowing where to start, then StudyHub proposes a preparatory bundle. This comprehensive Data Analyst Training: Boost Your Career bundle will help you build a solid foundation to become a proficient worker in the sector. This Data Analyst Training: Boost Your Career Bundle consists of the following 30 CPD Accredited Premium courses - Course 01 :Diploma in Data Analysis Fundamentals Course 02 :Google Data Studio: Data Analytics Course 03 :Statistics Course 04 :Statistical Analysis Course 05 :Research Methods in Business Course 06 :Business Intelligence and Data Mining Course 07 :Quick Data Science Approach from Scratch Course 08 :Microsoft Power BI - Master Power BI in 90 Minutes! Course 09 :PowerBI Formulas Course 10 :R Programming for Data Science Course 11 :Python Data Science Course 12 :Data Science & Machine Learning with Python Course 13 :Data Science & Machine Learning with R Course 14 :Excel Data Tools and Data Management Course 15 :Master JavaScript with Data Visualization Course 16 :Mastering SQL Programming Course 17 :Fundamentals of Business Analysis Course 18 :Financial Analysis Course 19 :Financial Statement Analysis Masterclass Course 20 :Financial Modeling Using Excel Course 21 :Investment Analyst Course 22 :Technical Analysis Masterclass for Trading & Investing Course 23 :Understanding Financial Statements and Analysis Course 24 :Strategic Planning and Analysis for Marketing Course 25: Stock Trading Analysis with Volume Trading Course 26: Time Management Training - Online Course Course 27: Complete Communication Skills Master Class for Life Course 28: Public Speaking Course 29: Minute Taking Executive Training Course 30: Receptionist Skills 3 Extraordinary Career Oriented courses that will assist you in reimagining your thriving techniques- Course 01 :Career Development Plan Fundamentals Course 02 :CV Writing and Job Searching Course 03 :Interview Skills: Ace the Interview Learning Outcome This tailor-made Data Analyst Training: Boost Your Career bundle will allow you to- Uncover your skills and aptitudes to break new ground in the related fields Deep dive into the fundamental knowledge Acquire some hard and soft skills in this area Gain some transferable skills to elevate your performance Maintain good report with your clients and staff Gain necessary office skills and be tech savvy utilising relevant software Keep records of your work and make a report Know the regulations around this area Reinforce your career with specific knowledge of this field Know your legal and ethical responsibility as a professional in the related field This Data Analyst Training: Boost Your Career Bundle resources were created with the help of industry experts, and all subject-related information is kept updated on a regular basis to avoid learners from falling behind on the latest developments. Certification After studying the complete training you will be able to take the assessment. After successfully passing the assessment you will be able to claim all courses pdf certificates and 1 hardcopy certificate for the Title Course completely free. Other Hard Copy certificates need to be ordered at an additional cost of •8. CPD 330 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Ambitious learners who want to strengthen their CV for their desired job should take advantage of the Data Analyst Training: Boost Your Career bundle! This bundle is also ideal for professionals looking for career advancement. Requirements To participate in this course, all you need is - A smart device A secure internet connection And a keen interest in Data Analyst Training: Boost Your Career Career path Upon completing this essential Bundle, you will discover a new world of endless possibilities. These courses will help you to get a cut above the rest and allow you to be more efficient in the relevant fields.

Microsoft Project Blue Belt 2013: In-House Training
By IIL Europe Ltd
Microsoft Project Blue Belt® 2013: In-House Training This course introduces Project Server 2013 features that expedite scheduling projects and simplify managing tasks within an enterprise environment. Learn different aspects of Project Server and their benefits to varying roles in the enterprise, and gain hands-on experience and insights on best practices from SMEs around the world. This course introduces Project Server 2013 features that expedite scheduling projects and simplify managing tasks within an enterprise environment. Learn different aspects of Project Server and their benefits to varying roles in the enterprise, and gain hands-on experience and insights on best practices from SMEs around the world. What you Will Learn You'll learn how to: Identify the project's life cycle Understand the Enterprise Project Management (EPM) environment Apply the basic project management principles to selecting, initiating, planning, executing, monitoring and controlling, and closing your Project 2013 schedules Take advantage of new features Explain Project Server 2013 views and project sites Meet deadlines and budget restrictions Keep the workloads of your resources within their available limits Efficiently update your schedule Take advantage of the standard reports, custom views, and visual reports for your projects Take a brief look at the Business Intelligence potential Efficiently and effectively manage your project(s) and programs Work comfortably within Project Server 2013 or Project Online Getting Started with Microsoft® Project Server 2013 Describing the EPM context Discovering Project Server 2013 and Project Online Differentiating the users of Project Server 2013 Working with Project Professional 2013 and Project Server 2013 Recognizing the Life Cycle within EPM Projects and Portfolio Management Portfolio management and governance Originating new initiatives within EPTs and workflows Prioritizing initiatives, analyzing scenarios, optimizing, and selecting the portfolio Initiating Projects Initiating processes with Project Professional, SharePoint lists, Enterprise Projects, and Resource Plans Importing projects and managing project owner and permissions Planning Projects - Scope and Schedule Management Planning context and framework Scheduling in PWA Using the Deliverables feature Planning Projects - Staffing Management Plan Building a project team Managing resource availability Reviewing the assignment cycle Resolving resource overallocation Planning Projects - Cost Components, Baseline, and Consolidated Schedules Developing components of the Cost Management Planning processes Working with the baseline in projects and programs or master schedules Improving the Collaboration in the Project Sites Creating the Project Sites Developing components of the Risk Management Plan and Issues Tracking Linking planning documents Additional apps and customization Executing Projects Understanding executing processes Managing resources using Build Team and other features Working with timesheets Reporting administrative time Configuring personal settings Monitoring and Controlling Projects - Tracking Task and Project Progress Understanding the Monitoring and Controlling processes Task progress and updates in PWA including considerations for different tracking methods Task progress and updates in Project Professional 2013 Monitor and Control Projects - Measuring Performance and Reporting Progress Understanding status reports Reviewing performance metrics and progress reports Taking advantage of preloaded reports at the Business Intelligence Center Considerations for defining custom reports Closing Projects Reviewing the closing processes and closing tasks to updates Supporting the closing process

48-Hour Knowledge Knockdown! Prices Reduced Like Never Before! Looking to become a Close Protection Bodyguard? Look no further than our comprehensive Close Protection Bodyguard Training bundle, featuring 11 courses designed to give you the knowledge you need to succeed in this exciting and challenging field. With our QLS-endorsed Close Protection course, you'll receive a free QLS hardcopy certificate upon completion, giving you the credentials you need to stand out from the crowd. But that's just the beginning - our bundle also includes 10 CPD-QS accredited courses covering everything from basic security guard training to emotional intelligence and human behaviour. Whether you're looking to start a new career as a bodyguard or simply want to enhance your existing skills, our Close Protection Bodyguard Training bundle has everything you need. From security management to criminal intelligence and crisis management, our courses cover the full spectrum of knowledge required for success in this field. So why wait? Sign up for our Close Protection Bodyguard Training bundle today and take the first step towards a rewarding and fulfilling career as a Close Protection Bodyguard. This Close Protection Bodyguard Training Bundle Package includes: Course 01: Certificate in Close Protection at QLS Level 3 10 Premium Additional CPD QS Accredited Courses - Course 01: Basic Security Guard Training Course 02: Bodyguard Training Course 03: Security Management Course 04: Detective: Private Investigator Course 05: Criminal Intelligence and Crime Analysis Course 06: Interrogations And Confessions Psychology Course 07: Emotional Intelligence and Human Behaviour Course 08: Diet & Fitness Training Course 09: Decision Making and Critical Thinking Training Course 10: Crisis Management Why Prefer This Close Protection Bodyguard Training Bundle? You will receive a completely free certificate from the Quality Licence Scheme Option to purchase 10 additional certificates accredited by CPD Get a free Student ID Card - (£10 postal charges will be applicable for international delivery) Free assessments and immediate success results 24/7 Tutor Support After taking this Close Protection Bodyguard Training bundle courses, you will be able to learn: Gain an in-depth understanding of close protection, security guard training and bodyguard training Learn how to manage security and protect individuals and assets Develop the skills necessary for private investigation, criminal intelligence and crisis management Understand the psychology of interrogations and confessions Enhance your emotional intelligence and human behaviour knowledge Gain knowledge in diet and fitness training, decision-making and critical thinking Earn a QLS-endorsed certificate and 10 CPD-QS accredited certificates upon completion of the courses ***Curriculum breakdown of Close Protection*** Module 01: Introduction to Close Protection Module 02: The Close Protection Team Module 03: The Planning Module 04: Threat Assessment Module 05: Vehicle Drills: Embus and Debus Module 06: Route Selection and Reconnaissance Module 07: Legislation Regarding Close Protection How is the Close Protection Bodyguard Training Bundle Assessment Process? You have to complete the assignment questions given at the end of the course and score a minimum of 60% to pass each exam. Our expert trainers will assess your assignment and give you feedback after you submit the assignment. You will be entitled to claim a certificate endorsed by the Quality Licence Scheme after you successfully pass the exams. CPD 220 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This bundle is perfect for: Individuals looking to pursue a career in close protection or security management Security professionals seeking to enhance their knowledge and skills Individuals seeking to start a new career in private investigation or criminal intelligence Anyone interested in learning about emotional intelligence and human behaviour in relation to security and protection Career path Our courses will prepare you for a range of careers, including: Security Guard: £18,000 - £25,000 per year Close Protection Officer: £30,000 - £45,000 per year Bodyguard: £40,000 - £70,000 per year Private Investigator: £20,000 - £50,000 per year Security Manager: £30,000 - £60,000 per year Crisis Management Consultant: £40,000 - £80,000 per year Certificates Certificate in Close Protection at QLS Level 3 Hard copy certificate - Included After successfully completing the course, you can order an original hardcopy Certificate of Achievement endorsed by the Quality Licence Scheme. This certificate will be delivered to your home, free of charge. To obtain the additional Quality License Scheme Endorsed Certificate, you will need to pay the corresponding fee based on the level of the courses: Level 1: £59 Level 2: £79 Level 3: £89 Level 4: £99 Level 5: £119 Level 6: £129 Level 7: £139 CPD QS Accredited Certificate Digital certificate - £10 Upon successfully completing the Bundle, you will need to place an order to receive a PDF Certificate for each course within the bundle. These certificates serve as proof of your newly acquired skills, accredited by CPD QS and will cost you £10 for each course. Also, the certificates are recognised throughout the UK and internationally. CPD QS Accredited Certificate Hard copy certificate - £29 International students are subject to a £10 delivery fee for their orders, based on their location.

Cyber Incident Response for Business Professionals
By Mpi Learning - Professional Learning And Development Provider
This course covers incident response methods and procedures are taught in alignment with industry frameworks such as US-CERT's NCISP (National Cyber Incident Response Plan), and Presidential Policy Directive (PPD) 41 on Cyber Incident Coordination Policy.

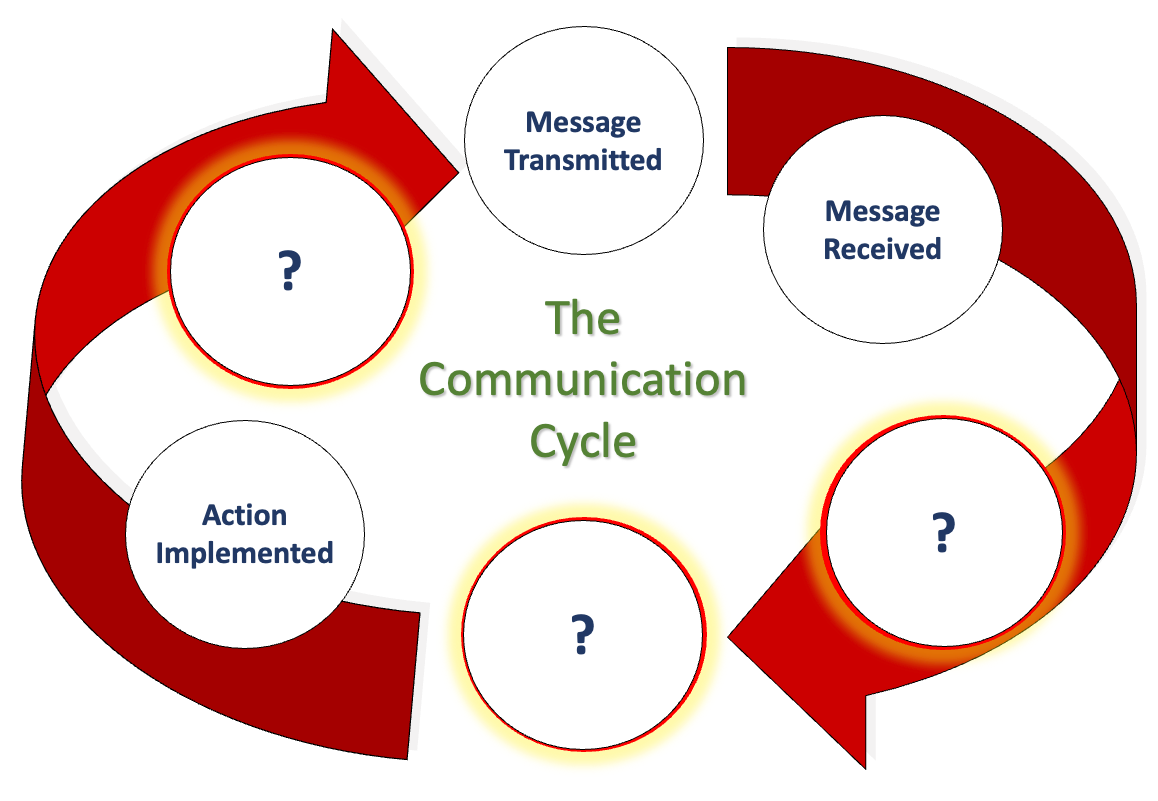
We communicate daily in many ways, including email, phone, text, Zoom, Teams, Google Meets, Slack, and even that old-fashioned thing, what was it now... oh yes, talking face-to-face. But, when we look at communication closely and really drill down into what we are doing in conjunction with how our brain works (neuroscience), how internal, organisational, and social politics control what we believe we can say, how hierarchical positioning impacts our honesty and how the lack of psychological safety means we say what we know others want to hear rather than what they need to hear…. It is oh so complicated! This workshop not only explores the concept of excellent communication, but we also want to hear what you believe it is too. We also delve into how organisational culture influences our perception of speaking up. Factors that hinder open and honest communication, and we work collaboratively towards removing these barriers to achieve a communication style that fosters trust and transparency, creating psychological safety. This workshop is particularly relevant to our Emotional Intelligence workshop (EI and Me). We firmly believe that developing emotional intelligence is the key to unlocking Clean Communication, a skill that is crucial for all of us, regardless of our roles and responsibilities, so that we thrive in our professional environment. If you want to see if we are correct, why not have us facilitate a workshop for you and see what you get by the end of it? LENGTH - Normally, one day. But please contact us to discuss your specific needs, or we can offer advice. NEXT WORKSHOP START - Please ask for more information as we deliver bespoke closed events for your people at your location or a mutually suitable location. WORKSHOP DELIVERY - The best environment for this workshop is face-to-face, but we can facilitate this workshop online. Suitability - Who should attend? Who Should Attend and Why? Who? - Perhaps think of this another way… who shouldn’t attend to ensure we can attain Clean Communication? There’s your answer. Why? - Every person needs to understand what we are saying above about how we get trapped in this organisational formatting which changes how we communicate and how it prevents us from communicating cleanly. EVERY organisation has this, despite what our values profess. And 'Values', that’s a whole other story. Workshop Content Using the 'Moccasin Approach'® to clean our personal and organisational communication LaPD’s Communication Cycle and what we must consider. (Can you work out what the ? represent above? Accountability and Responsibility raises its head in Communication. It has to. Bias, unconscious bias and its impacts on our communication. The conundrum of communicating with others and their styles (The TRAP). How would my perfect Manager/Leader communicate with me? Nonverbal communication (body language), rapport, Clean Communication. Negative communication can go viral (Self-Fulfilling Prophecy). Reflections, findings and goals (individual and team). Meeting our workshop objectives by listing five areas for development. Workshop delivery and venue This workshop is usually one day in duration, and it focuses solely on how we communicate with each other. It can also be a two-day event incorporating aspects of Emotional Intelligence (EI) with group, and individual activities to allow discussions about the various communication we need in your organisation. When you consider the content we deliver, we are sure you will understand why we always prefer to deliver our workshops, courses and programmes face-to-face. Face-to-face workshops and courses can be held at a location of your choice or, if you wish, a central UK location, such as the Macdonald Burlington Hotel in Birmingham, located directly across from the Birmingham New Street train station. We can deliver our workshops, courses and programmes online, although this will mean splitting elements into manageable learning events to suit the online environment.