- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
96 Courses in Coventry
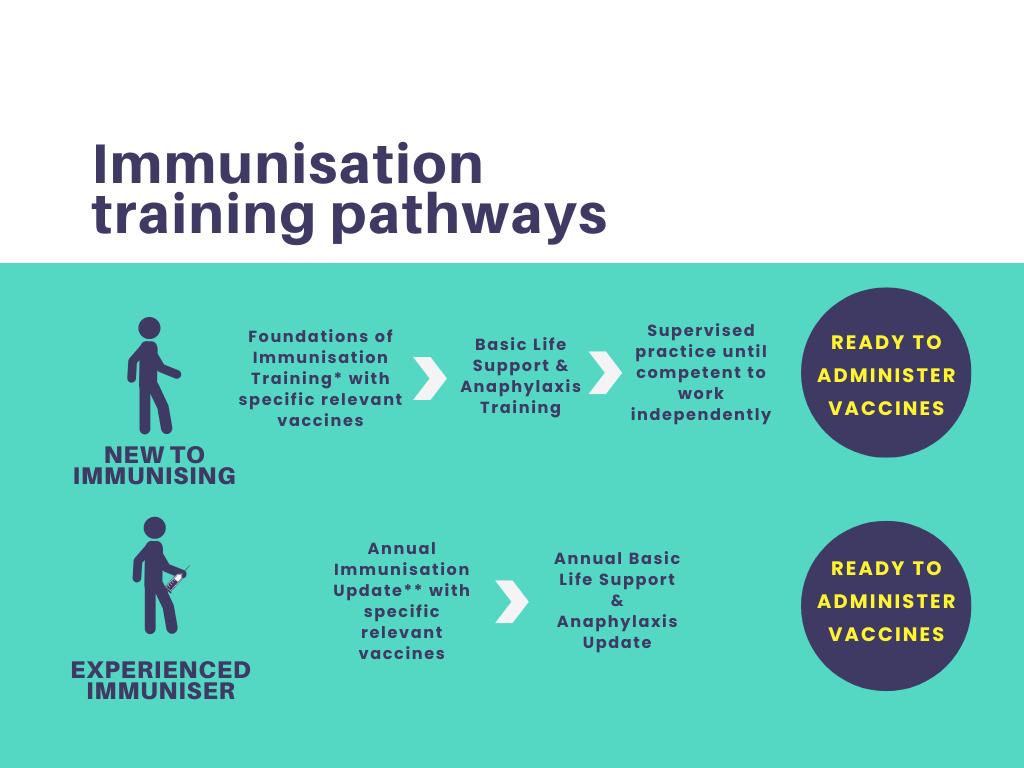
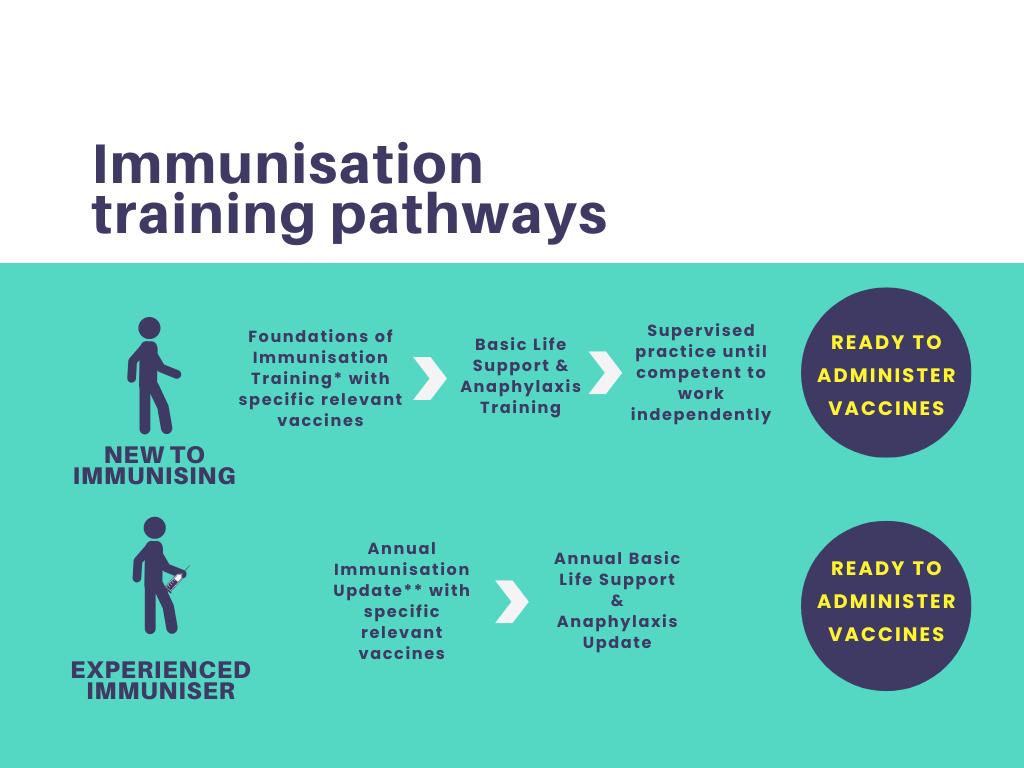
Foundations of Immunisation and Vaccines
By Guardian Angels Training
Gain a comprehensive understanding of immunisation and vaccines with our "Foundations of Immunisation and Vaccines" course. Designed for healthcare professionals, public health workers, and individuals interested in immunisation, this course covers vaccine development, administration, safety, and the role of vaccines in preventing infectious diseases.
Promoting Best Practice in Teaching and Assessing Medicines Management (Medication Train the Trainer)
By Guardian Angels Training
"Empower educators and healthcare professionals with evidence-based teaching strategies and practical assessment methods through our 'Promoting Best Practice in Teaching and Assessing Medicines Management' course. Ensure safe and competent medication administration practices among healthcare learners. Enroll now."

Foundations of Immunisation and Vaccines for Non-Registered Practitioners
By Guardian Angels Training
The "Foundations of Immunisation and Vaccines for Non-Registered Practitioners" course is fully compliant with the National Minimum Standards and Core Curriculum for Immunisation Training and is designed to equip non-registered healthcare professionals with a solid understanding of immunisation concepts, vaccine administration, and the importance of vaccination in public health.
Microsoft Lync training course description This course teaches IT staff how to plan, design, deploy, configure, and administer a Microsoft Lync Server solution. The course emphasizes Lync Server Enterprise Unified Communications features focussing particularly on coexisting with and migrating from legacy communication services. The labs in this course create a solution that includes IM and Presence, Conferencing, and Persistent Chat. This course helps prepare for Exam 70-336. What will you learn Describe the Lync Server architecture. Install and deploy Lync Server. Use Lync Server management interfaces. Deploy and manage clients. Manage and administer dial-in conferencing. Design audio and video for web conferencing. Plan for instant message and presence Federation. Deploy and configure persistent chat in Lync. Configure archiving and monitoring services. Troubleshoot Lync Server. Describe the required daily, weekly, and monthly maintenance tasks. Use SIP commands and analyze SIP logs. Configure high availability features in Lync. Design load balancing in Lync Server. Backup and restore Lync Server data. Microsoft Lync training course details Who will benefit: Technical staff working with Microsoft Lync. Prerequisites: Supporting Windows 2008 or 2012. Duration 5 days Microsoft Lync training course contents Microsoft Lync Server architecture Lync Server architecture, Lync core capabilities, Lync design process, assessing infrastructure requirements and updating the design, planning for all Microsoft solutions framework phases. Designing a Lync Server topology Infrastructure requirements for Lync Server, using the planning tool, using topology builder, server infrastructure, documentation. Hands on Environment preparation and Lync Server pools. Users and rights in Microsoft Lync Server Managing Lync Server, role based access control. Hands on Using the management shell, configuring role-based access control. Client/device deployment and management Deploy and manage clients, prepare for device deployment, IP phones. Hands on Clients. Conferencing in Lync Server Introduction to conferencing in Lync Server, designing for audio\video and web conferencing, dial-in conferencing in Lync Server, managing and administering conferencing. Hands on Conferencing in Microsoft Lync. Designing and deploying external access Conferencing and external capabilities of Lync Server, planning for IM and presence federation, designing edge services. Hands on Deploying Edge Server and Configuring Remote Access, Validating the Edge Server. Deploying Lync Server persistent chat Overview of persistent chat architecture in Lync Server, designing persistent chat, deploying and persistent chat. Hands on persistent chat server. Monitoring and archiving The archiving service, the monitoring service, configuring archiving and monitoring. Hands on Archiving and monitoring in Lync Server. Administration and maintenance of Lync Lync Server troubleshooting tools, Lync Server operational tasks, Lync Server troubleshooting techniques. Hands on Lync administration tools, centralized logging service, analysing Lync Server logs and traces. High Availability in Lync Server High availability in Lync Server, configuring high availability in Lync Server, planning for load balancing, designing load balancing. Hands on Configuring database mirroring, experiencing a scheduled SQL Server outage, experiencing an unscheduled SQL Server outage. Disaster recovery in Lync Server Disaster recovery in Lync Server, tools for backing up and restoring Lync Server, critical Lync Server data to back up and restore, critical data to export and import, designing branch site resiliency. Hands on Configure pool pairing, experiencing a pool failure or outage. Planning a migration to Lync Server Coexistence and migration, migration steps, planning for clients and devices. Designing a client migration and device migration strategy. Hands on Creating a migration plan, documenting the migration phases.

Securing UNIX systems training course description This course teaches you everything you need to know to build a safe Linux environment. The first section handles cryptography and authentication with certificates, openssl, mod_ssl, DNSSEC and filesystem encryption. Then Host security and hardening is covered with intrusion detection, and also user management and authentication. Filesystem Access control is then covered. Finally network security is covered with network hardening, packet filtering and VPNs. What will you learn Secure UNIX accounts. Secure UNIX file systems. Secure UNIX access through the network. Securing UNIX systems course details Who will benefit: Linux technical staff needing to secure their systems. Prerequisites: Linux system administration (LPIC-1) Duration 5 days Securing UNIX systems course contents Cryptography Certificates and Public Key Infrastructures X.509 certificates, lifecycle, fields and certificate extensions. Trust chains and PKI. openssl. Public and private keys. Certification authority. Manage server and client certificates. Revoke certificates and CAs. Encryption, signing and authentication SSL, TLS, protocol versions. Transport layer security threats, e.g. MITM. Apache HTTPD with mod_ssl for HTTPS service, including SNI and HSTS. HTTPD with mod_ssl to authenticate users using certificates. HTTPD with mod_ssl to provide OCSP stapling. Use OpenSSL for SSL/TLS client and server tests. Encrypted File Systems Block device and file system encryption. dm-crypt with LUKS to encrypt block devices. eCryptfs to encrypt file systems, including home directories and, PAM integration, plain dm-crypt and EncFS. DNS and cryptography DNSSEC and DANE. BIND as an authoritative name server serving DNSSEC secured zones. BIND as an recursive name server that performs DNSSEC validation, KSK, ZSK, Key Tag, Key generation, key storage, key management and key rollover, Maintenance and resigning of zones, Use DANE. TSIG. Host Security Host Hardening BIOS and boot loader (GRUB 2) security. Disable useless software and services, sysctl for security related kernel configuration, particularly ASLR, Exec-Shield and IP / ICMP configuration, Exec-Shield and IP / ICMP configuration, Limit resource usage. Work with chroot environments, Security advantages of virtualization. Host Intrusion Detection The Linux Audit system, chkrootkit, rkhunter, including updates, Linux Malware Detect, Automate host scans using cron, AIDE, including rule management, OpenSCAP. User Management and Authentication NSS and PAM, Enforce password policies. Lock accounts automatically after failed login attempts, SSSD, Configure NSS and PAM for use with SSSD, SSSD authentication against Active Directory, IPA, LDAP, Kerberos and local domains, Kerberos and local domains, Kerberos tickets. FreeIPA Installation and Samba Integration FreeIPA, architecture and components. Install and manage a FreeIPA server and domain, Active Directory replication and Kerberos cross-realm trusts, sudo, autofs, SSH and SELinux integration in FreeIPA. Access Control Discretionary Access Control File ownership and permissions, SUID, SGID. Access control lists, extended attributes and attribute classes. Mandatory Access Control TE, RBAC, MAC, DAC. SELinux, AppArmor and Smack. etwork File Systems NFSv4 security issues and improvements, NFSv4 server and clients, NFSv4 authentication mechanisms (LIPKEY, SPKM, Kerberos), NFSv4 pseudo file system, NFSv4 ACLs. CIFS clients, CIFS Unix Extensions, CIFS security modes (NTLM, Kerberos), mapping and handling of CIFS ACLs and SIDs in a Linux system. Network Security Network Hardening FreeRADIUS, nmap, scan methods. Wireshark, filters and statistics. Rogue router advertisements and DHCP messages. Network Intrusion Detection ntop, Cacti, bandwidth usage monitoring, Snort, rule management, OpenVAS, NASL. Packet Filtering Firewall architectures, DMZ, netfilter, iptables and ip6tables, standard modules, tests and targets. IPv4 and IPv6 packet filtering. Connection tracking, NAT. IP sets and netfilter rules, nftables and nft. ebtables. conntrackd Virtual Private Networks OpenVPN server and clients for both bridged and routed VPN networks. IPsec server and clients for routed VPN networks using IPsec-Tools / racoon. L2TP.

Windows PowerShell training course description This course is intended for IT Professionals who are already experienced in general Windows Server and Windows Client administration, and who want to learn more about using Windows PowerShell for administration. No prior experience with any version of Windows PowerShell, or any scripting language, is assumed. This course is also suitable for IT Professionals already experienced in server administration, including Exchange Server, SharePoint Server, SQL Server, System Center, and others. What will you learn Work with Windows PowerShell pipeline. Query system information by using WMI and CIM. Work with variables, arrays, and hash tables. Write advanced scripts in Windows PowerShell. Administer remote computers. Use advanced Windows PowerShell techniques. Windows PowerShell training course details Who will benefit: IT professionals. Prerequisites: Supporting Windows Server Duration 5 days Windows PowerShell training course contents Getting started with Windows PowerShell Overview and background of Windows PowerShell, Understanding command syntax, Finding commands. Hands on Configuring Windows PowerShell console & ISE application. Hands on Finding and running basic commands, Using the About files. Cmdlets for administration Active Directory administration cmdlets, Network configuration cmdlets, Other server administration cmdlets. Hands on Windows Administration. Creating and managing Active Directory objects, Configuring network settings on Windows Server, Creating a web site. Working with the Windows PowerShell pipeline Understanding the pipeline, Selecting, sorting, and measuring objects, Filtering objects out of the pipeline, enumerating objects in the pipeline, Sending pipeline data as output. Hands on Using the pipeline. Selecting, sorting, and displaying data. Hands on Filtering objects. Hands on Enumerating objects. Hands on Sending output to a file. Exporting user information to a file. Understanding how the pipeline works Passing the pipeline data, Advanced considerations for pipeline data. Hands on Working with pipeline parameter binding. Predicting pipeline behaviour. Using PSProviders and PSDrives Using PSProviders, Using PSDrives. Hands on Using PSProviders and PSDrives Creating files and folders on a remote computer, Creating a registry key for your future scripts, Create a new Active Directory group. Querying system information by using WMI and CIM Understanding WMI and CIM, Querying data by using WMI and CIM, Making changes with WMI/CIM. Hands on Working with WMI and CIM. Querying information by using WMI, Querying information by using CIM, Invoking methods. Working with variables, arrays, and hash tables Manipulating variables, arrays and hash tables. Hands on Working with variables, Using arrays, Using hash tables. Basic scripting Introduction to scripting, Scripting constructs, Importing data from files. Hands on Basic scripting. Setting a script, Processing an array with a ForEach loop, Processing items by using If statements, Creating a random password, Creating users based on a CSV file. Advanced scripting Accepting user input, Overview of script documentation, Troubleshooting and error handling, Functions and modules. Hands on Accepting data from users. Querying disk information from remote computers, Updating the script to use alternate credentials, Documenting a script. Hands on Implementing functions and modules. Creating a logging function, Adding error handling to a script, Converting a function to a module. Administering Remote Computers Using basic Windows PowerShell remoting, Using advanced Windows PowerShell remoting techniques, Using PSSessions. Hands on Using basic remoting. Enabling remoting on the local computer, Performing one-to-one remoting, Performing one-to-many remoting. Hands on Using PSSessions. Using implicit remoting, Managing multiple computers. Using background jobs and scheduled jobs Using background jobs, Using scheduled jobs. Hands on Using background jobs and scheduled jobs. Starting and managing jobs, Creating a scheduled job. Using advanced Windows PowerShell techniques Creating profile scripts, Using advanced techniques. Hands on Practicing advanced techniques. Creating a profile script, Verifying the validity of an IP address, Reporting disk information, Configuring NTFS permissions, Creating user accounts with passwords from a CSV file. Hands on Practicing script development (optional)

Overview This training will give you the platform to learn everything you need to carry out effective cost-benefit analyses, the risk and uncertainty involved, and how to handle the various different types of information available. The skills you will gain will allow the administration of more accurate and reflective cost-benefit analyses through improved methods and processes.

Supporting Microsoft IIS training course description This course provides students with the fundamental knowledge and skills to configure and manage Internet Information Services. This course is intended to help provide pre-requisite skills supporting a broad range of Internet web applications, security, and knowledge to help support other products that use IIS such as Exchange and SharePoint. What will you learn Install IIS. Configure IIS. Secure websites. Maintain IIS. Supporting Microsoft IIS training course details Who will benefit: Technical staff working with Microsoft IIS. Prerequisites: TCP/IP foundation for engineerss Supporting Windows ( XP or 2000 or 2003) Duration 5 days Supporting Microsoft IIS course contents Overview and Installing IIS Web Server infrastructure, installing IIS. Hands on Default install of IIS, verify and test.. Configuring the default website Default website, IIS Manager, default IIS file structure, configuring DNS records for a website, creating virtual directories and Applications. Hands on Configuring the Default website for public access. Creating Virtual Directories and Applications. Application Pools Application Pool Architecture, Application Pool recycling. Hands on Creating and managing Application Pools. Creating additional websites Multiple websites on a single server, website bindings. Hands on Creating new websites. Website and Web application support Configuring Common features, adding support for web applications. Hands on Adding support for web applications. Securing Websites and applications Access control, sites, applications, authentication and permissions. URL authorization rules. Hands on Configuring Authentication and permissions. Securing Data Transmissions with SSL Certificates and SSL, creating certificates for a web server, adding a certificate to a website. Hands on Certificates and HTTPS. Using the Central Certificate Store The Central Certificate Store. Hands on Install and configure the Central Certificate Store. Configuring Remote Administration Installing and Configuring the Management Service. Connecting to remote web servers and websites. Delegating Management Access. Hands on Remote administration. Implementing FTP Implementing FTP, configuring an FTP site. Hands on Install and configure a secured FTP site. Monitoring IIS IMonitoring IIS logs with Log Parser. Hands on Analyze a set of IIS log files for possible issues using Log Parser. Analyze performance data for performance related problems using PerfMon. Backing up and Restoring IIS The IIS environment. Hands on Performing a backup and restore of a website. Building Load-Balanced Web Farms Load-balancing mechanisms, building a Load-Balanced Web Farm using ARR, sharing content to a Web Farm using a network share, Sharing content to a Web Farm using DFS-R, Sharing IIS Configurations in a Web Farm. Hands on Installing and configuring ARR, sharing content to a Web Farm using network share and DFS-R, sharing IIS Configurations in a Web Farm.

Network design training course description This course provides you with the knowledge needed to perform the design of a network infrastructure that supports desired network solutions to achieve effective performance, scalability, and availability. We recognise that the role of design does not normally require hands on skills but hands on sessions are used to reinforce the theory not to teach configuration or troubleshooting. What will you learn Create HA enterprise network designs. Develop optimum Layer 3 designs. Design effective modern WAN and data center networks. Develop effective migration approaches to IPv6. Create effective network security designs. Network design training course details Who will benefit: Anyone involved with network design. Prerequisites: TCP/IP Foundation for engineers Duration 5 days Network design training course contents Part I Reliable, resilient enterprise L2/3 network designOptimal Enterprise Campus Design:Enterprise campus design principles, hierarchy, modularity, flexibility, resiliency.EIGRP design:EIGRP Design, Should you use EIGRP?OSPF design: OSPF scalability designs, OSPF area design, OSPF Full-Mesh Design, OSPF Hub-and-Spoke Design, OSPF convergence design and optimization techniques. IS-IS Design:The protocol, IS-IS hierarchical architecture, IS-IS vs OSPF, IS-IS Deep Dive, IS-IS Design Considerations. BGP design:BGP overview, Designing Scalable iBGP Networks, BGP Route Reflector Design, Enhancing the Design of BGP Policies with BGP Communities, Case Study: Designing Enterprise wide BGP Policies Using BGP Communities, BGP Load-Sharing Design.Part II Enterprise IPv6 Design ConsiderationsIPv6 Design Considerations in the Enterprise: IPv6 Deployment and Design Considerations, Considerations for Migration to IPv6 Design, IPv6 Transition Mechanisms, Final Thoughts on IPv6 Transition Mechanisms. Challenges of the Transition to IPv6: IPv6 Services, Link Layer Security Considerations. Part III Modern Enterprise Wide-Area Networks DesignService Provider-Managed VPNs:Choosing Your WAN Connection, Layer 3 MPLS VPNs, Case Study: MPLS VPN Routing Propagation, Layer 2 MPLS VPN Services. Enterprise-Managed WANs: Enterprise-Managed VPNs, GRE, Multipoint GRE, Point-to-Point and Multipoint GRE, IPsec, IPsec and dynamic VTI, DMVPN, Case Study: EIGRP DMVPN, DMVPN and Redundancy, Case Study: MPLS/VPN over GRE/DMVPN, SSL VPN. Enterprise WAN Resiliency Design: WAN Remote-Site Overview, MPLS L3 WAN Design Models, Common L2 WAN Design Models, Common VPN WAN Design Models, 3G/4G VPN Design Models, Remote Site Using Local Internet, Remote-Site LAN, Case Study: Redundancy and Connectivity, NGWAN, SDWAN, and IWAN Solution Overview, IWAN Design Overview, Enterprise WAN and Access Management. Part IV Enterprise Data Center DesignsMultitier Data Center Designs: Case Study: Small Data Centers (Connecting Servers to an Enterprise LAN), Case Study: Two-Tier Data Center Network Architecture, Case Study: Three-Tier Data Center Network Architecture.Trends and Techniques to Design Modern Data Centers: The Need for a New Network Architecture, Limitations of Current Networking Technology, Modern Data Center Design Techniques and Architectures, Multitenant Data Center. SDN:SDN characteristics, How SDN addresses current Networking Limitations, SDN Architecture Components, SDN Network Virtualization overlays. Data Center Connections:Data Center Traffic Flows, The Need for DCI, IP Address Mobility, Case Study: Dark Fiber DCI, Pseudowire DCI. Part V Design QoS for Optimized User ExperienceQoS Overview:QoS Overview, IntServ versus DiffServ, Classification and Marking, Policers and Shapers, Policing Tools: Single-Rate Three-Color Marker, Policing Tools: TwoRate Three-Color Marker, Queuing Tools, Dropping Tools. QoS design principles and best practices: QoS overview, classification and marking design principles, policing and remarking design principles, queuing design principles, dropping design principles, Per-Hop behavior queue design principles, RFC 4594 QoS Recommendation, QoS Strategy Models. Campus QoS, WAN QoS, Data Center QoS.MPLS VPN QoS Design: The Need for QoS in MPLS VPN, Layer 2 Private WAN QoS Administration, Fully Meshed MPLS VPN QoS Administration, MPLS DiffServ Tunneling Modes, Sample MPLS VPN QoS Roles. IPsec VPN QoS Design: The Need for QoS in IPsec VPN, VPN Use Cases and Their QoS Models, IPsec Refresher, Encryption and Classification: Order of Operations, MTU Considerations, DMVPN QoS Considerations. Part VI IP Multicast DesignEnterprise IP Multicast Design: How Does IP Multicast Work? Multicast Protocols, Multicast Forwarding and RPF Check, Multicast Protocol Basics, PIM-SM Overview, Multicast Routing Table, Basic SSM Concepts, Bidirectional PIM. RP discovery, Anycast RP Features, MSDP. Part VII Designing Optimum Enterprise Network SecurityDesigning Security Services and Infrastructure Protection Network Security Zoning, Designing Infrastructure Protection.Designing firewall & IPS solutions: Firewall architectures, virtualized firewalls. Case Study: Application Tier separation, Case Study: Firewalls in a Data Center, Case Study: Firewall High Availability, IPS Architectures, Case Study: Secure Campus Edge Design (Internet and Extranet Connectivity). IP Multicast Security: Multicast Security Challenges, Multicast Network Security Considerations. Designing Network Access Control Solutions:IEEE 802.1X, EAP, 802.1X supplicants, 802.1X phased deployment, Case Study: Authorization Options. Part VIII Design scenariosDesign Case Studies: 1: Enterprise Connectivity, 2: Enterprise BGP with Internet Connectivity, 3: IPv6, 4: Data Center Connectivity, 5: Resilient Enterprise WAN, 6: Secure Enterprise Network, 7: QoS in the Enterprise Network.

UNIX Virtualization and High Availability course description This course covers administering UNIX enterprise-wide with an emphasis on virtualization and high availability. What will you learn Manage Virtual Machines. Manage containers. Manage HA clusters. Manage HA cluster storage. UNIX Virtualization and High Availability course details Who will benefit: Enterprise-level UNIX professional. UNIX professionals working with virtualization and/or High availability. Prerequisites: Linux network administration 2 (LPIC-2) Duration 5 days UNIX Virtualization and High Availability course contents VIRTUALIZATION Virtualization concepts and theory Terminology, Pros and Cons of virtualization, variations of Virtual Machine monitors, migration of physical to VMs, migration of VMs between host systems, cloud computing. Xen Xen architecture, networking and storage, Xen configuration, Xen utilities, troubleshooting Xen installations, XAPI, XenStore, Xen Boot Parameters, the xm utility. KVM KVM architecture, networking and storage, KVM configuration, KVM utilities, troubleshooting KVM installations. Other virtualization solutions OpenVZ and LXC, other virtualization technologies, virtualization provisioning tools. Libvirt and Related Tools libvirt architecture, networking and storage, basic technical knowledge of libvirt and virsh, oVirt. Cloud Management Tools Basic feature knowledge of OpenStack and CloudStack, awareness of Eucalyptus and OpenNebula. Containers Containers versus VMs, Docker, Kubernetes. Load balanced clusters of LVS/IPVS, VRRP, configuration of keepalived, configuration of ldirectord, backend server network configuration. HAProxy, configuration of HAProxy. Failover clusters Pacemaker architecture and components (CIB, CRMd, PEngine, LRMd, DC, STONITHd), Pacemaker cluster configuration, Resource classes (OCF, LSB, Systemd, Upstart, Service, STONITH, Nagios), Resource rules and constraints (location, order, colocation), Advanced resource features (templates, groups, clone resources, multi-state resources), Pacemaker management using pcs, Pacemaker management using crmsh, configuration and management of corosync in conjunction with Pacemaker, other cluster engines (OpenAIS, Heartbeat, CMAN). HIGH AVAILABILITY CLUSTER STORAGE DRBD/cLVM DRBD resources, states and replication modes, configuration of DRBD resources, networking, disks and devices, configuration of DRBD automatic recovery and error handling, management of DRBD using drbdadm. drbdsetup and drbdmeta, Integration of DRBD with Pacemaker, cLVM, integration of cLVM with Pacemaker. Clustered File Systems Principles of cluster file systems. Create, maintain and troubleshoot GFS2 file systems in a cluster, create, maintain and troubleshoot OCFS2 file systems in a cluster, Integration of GFS2 and OCFS2 with Pacemaker, the O2CB cluster stack, other commonly used clustered file systems.

Search By Location
- Administration of Insulin Courses in London
- Administration of Insulin Courses in Birmingham
- Administration of Insulin Courses in Glasgow
- Administration of Insulin Courses in Liverpool
- Administration of Insulin Courses in Bristol
- Administration of Insulin Courses in Manchester
- Administration of Insulin Courses in Sheffield
- Administration of Insulin Courses in Leeds
- Administration of Insulin Courses in Edinburgh
- Administration of Insulin Courses in Leicester
- Administration of Insulin Courses in Coventry
- Administration of Insulin Courses in Bradford
- Administration of Insulin Courses in Cardiff
- Administration of Insulin Courses in Belfast
- Administration of Insulin Courses in Nottingham