- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
WAN training course description A hands on Introduction to Wide Area Networks for engineers. This course covers all current major WAN technologies from a perspective of design, evaluating technologies available as well as hands on to consolidate the theory What will you learn Describe the seven-layer model and realise how it applies to the real world. Evaluate and describe WAN technologies. Describe the architecture of WANs in the core. Use WANS to interconnect LANS. WAN training course details Who will benefit: Technical staff wishing to find out more about how their WAN works. Prerequisites: Intro to data communications & networking Duration 5 days WAN training course contents Introduction LANs, MANS and WANS, protocols, the OSI seven layer model, ITU-T, ETSI, DTE, DCE, and the overall picture. WAN architectures Service providers, core, access, DTE, DCE, CPE, dialup, circuit switched, packet switched, how to choose a WAN, common bandwidths, site to site, remote access. Topologies: Star, Full mesh, partial mesh. History of WANs Before IP was ubiquitous, The PSTN, Dial up networks, modems, ISDN, Stat mux, TDM, 64k, N*64, E1, X25, Frame Relay The role of IP and routers The growth of IP, the role of routers, routing tables, routing protocols. Hands on: IP and routing. Layer 1 Physical Copper, Fibre, Wireless, Microwave, Phone lines, FTTC, FTTH, mobile networks. Service provider technologies The transport plane, SDH, SONET, DWDM. WAN access Phone lines, leased lines, xDSL, WiMax, satellite, the role of PPP. Broadband adband xDSL, ADSL, SDSL, local loops, DSLAM, DSL architecture. ATM Cell switching principles, ATM switching, Virtual paths, QOS, CBR, VBR, ABR, UBR, AAL1 to AAL5, MPOA, LANE, Voice over ATM. The Internet VPNs, IPSEC, QOS. What is MPLS? Core MPLS, MPLS and the 7 layer model, MPLS protocol, MPLS standard, MPLS runs on routers, MPLS history, Why MPLS? MPLS architecture LSRs, PE and P router roles, FEC, swapping labels, MPLS packet format, Loops, TTL control. Ethernet What is Ethernet? LANs, MANs, WANs, Ethernet and switches in the LAN. Traditional LAN/WAN integration, routers. The Ethernet interface for the WAN. Standards: Transporting carrier Ethernet.

CWSP training course description A hands-on training course concentrating solely on WiFi security with an emphasis on the delegates learning the necessary knowledge and skills to pass the CWSP exam. The course progresses from simple authentication, encryption and key management onto in depth coverage of 802.X and EAP along with many other security solutions such as access control, intrusion prevention and secure roaming. What will you learn Demonstrate the threats to WiFi networks. Secure WiFi networks. Configure: WPA2 RADIUS 802.1x EAP Pass the CWSP exam. CWSP training course details Who will benefit: Technical network staff. Technical security staff. Prerequisites: Certified Wireless Network Associate. Duration 5 days CWSP training course contents WLAN Security overview Standards, security basics, AAA, 802.11 security history. Hands on WLAN connectivity. Legacy 802.11 security Authentication: Open system, shared key. WEP. VPNs. MAC filters. SSID segmentation, SSID cloaking. Hands on Analysing 802.11 frame exchanges, viewing hidden SSIDs. Encryption Basics, AES, TKIP, CCMP, WPA, WPA2. Hands on Decrypting 802.11 data frames. 802.11 layer 2 authentication 802.1X: Supplicant, Authenticator, Authentication server. Credentials. Legacy authentication. EAP, Weak EAP protocols, Strong EAP protocols: EAP -PEAP, EAP-TTLS, EAP-TLS, EAP-FAST. Hands on Analysing 802.1X/EAP frames. 802.11 layer 2 dynamic key generation Robust Security Network. Hands on Authentication and key management. SOHO 802.11 security WPA/WPA2 personal, Preshared Keys, WiFi Protected Setup (WPS). Hands on PSK mapping. WLAN security infrastructure DS, Autonomous APs, WLAN controllers, split MAC, mesh, bridging, location based access control. Resilience. Wireless network management system. RADIUS/LDAP servers, PKI, RBAC. Hands on 802.1X/EAP configuration. RADIUS configuration. 802.11 Fast secure roaming History, RSNA, OKC, Fast BSS transition, 802.11k. Hands on Roaming. Wireless security risks Rogue devices, rogue prevention. Eavesdropping, DOS attacks. Public access and hotspots. Hands on Backtrack. WiFi security auditing Layer 1 audit, layer 2 audit, pen testing. WLAN security auditing tools. WiFi security monitoring Wireless Intrusion Detection and Prevention Systems. Device classification, WIDS/WIPS analysis. Monitoring. 802.11w. Hands on Laptop spectrum analysers. VPNs, remote access, guest access Role of VPNs in 802.11, remote access, hotspots, captive portal. Wireless security policies General policy, functional policy, recommendations.

Git and GitHub course description This course covers version control using Git but also using GUI frontends such as GitHub. The course starts with a tour of using GitHub but then quickly moves onto using git from the command line. All elements of git version control are covered including creation of repositories, adding and editing files, branches and merging, rewriting history and handling merge conflicts. Hands on sessions are used throughout the course. What will you learn Install git. Add and edit files in a repository. Create branches and perform merges. Handle merge conflicts. Git and GitHub course details Who will benefit: Anyone requiring version control. Prerequisites: None. Duration 1 day Git and GitHub course contents Introduction Version control for software, configuration management. Other uses. Version control systems. What is git? What is GitHub? Distributed version control. Comparison of git to other systems. GitHub Getting started, creating an account, account types, repositories, access control, bug tracking, feature requests. Alternatives to GitHub. Hands on Using GitHub. Installing git Linux install, Windows install, git config, levels, user.name, user.email. Hands on Installing and configuring git. Creating repositories git clone, github, git remote, git init. Hands on Creating a repository. Adding and editing files Staging and adding, git add, git commit, git push, git pull, git status, git log. Two stage process. File states: Working, staging, history, untracked. git mv, git rm, .gitignore, git diff, git difftool. Undoing changes. Hands on Adding and editing files in git. Branching and merging What is a branch, HEAD label, master branch, git branch, git checkout. Feature branches, bux fix branches, integration branches, production branches, fast forward merges, 3 way merges, git merge, git status, git log, tags. Hands on Making branches, merging. Rewriting history git reset, git rebase, advantages. Hands on Reset commits, rebase a branch. Merge conflicts What is a conflict, conflict resolution process, resolving merges, rebasing, git log, merge tools, configuring merge tools, avoiding conflicts. Hands on Merge resolution.

IV Vitamin Drip Infusion Training
By Cosmetic College
With a focus on both theory and practical, we provide a breakdown of each vitamin and quantities for attendees to thoroughly understand IV therapy and succeed in this regenerative field. Course Prerequisites This course is suitable for those with or without a medical background. It is designed to provide the student with the ability to seek employment or start their own business upon qualification. At a minimum, students will be required to be qualified for at least one of the following: Medically qualified as a nurse, doctor or dentist with current registration with the NMC, GMC or GDC. NVQ Level 3 in Beauty Therapy, ITEC or HND 12 months of needling experience 6 Months of micropigmentation experience and Anatomy & Physiology Level 3 If your qualification does not appear above, we offer a fast track access course for those completely new to the industry. Course agenda Introduction History of nutrition therapy and regulations Intravenous Micronutrient Supplementation (IMS) Essential Micronutrients IVNT protocols Safety & efficacy Practical fundamentals Combination and cocktail IV injection protocols and treatments Treatment and specific ingredients and protocols for IV nutrition Informed consent & medical history Trainers demonstration Live model delivery sessions

Overview The protocol is one of the most modern terms in terms of language but very old in terms of history as the word protocol is a development of the word of the conventions and understandings this is in the world of politics and at the international level, but within the field of business management has become the formulation of protocols is one of the important and necessary skills and very necessary for people who wish to They must take administrative duties. Through this course, we are going to introduce the rules and practices of gentle behaviour, the best practices for communication with others, and good reception, since all such related matters represent a large portion of our personality.

CWISA training course description This CWISA course covers wireless technologies with reference to IoT. It examines from an IoT perspective how wireless works, and is an excellent introduction to IoT for the wireless engineer. Topics range from wireless technologies, RF, to mobile networks, IoT, and security. What will you learn Describe wireless networking and IoT technologies. Explain basic RF communications. Plan wireless solutions. Describe how to implement wireless solutions. Use best practices in implementing wireless solutions. CWISA training course details Who will benefit: Anyone working with IoT technologies. Prerequisites: RF fundamentals. Duration 4 days CWISA training course contents Introduction to wireless technologies History of wireless, radio waves and frequencies, wireless technologies and related components, common components of wireless solutions, LAN networking requirements, Network security, Implementing wireless solutions, staging, documentation, security updates, Industry organizations, IEEE, compatibility and certification groups. Wireless network use cases Wireless BANs, Wireless PANs, Wireless LANs, Wireless MANs, Wireless WANs, Wireless sensor networks, New network driver-Internet of Things, IoT for industry (IIoT), IoT for connected vehicles, Residential environments, Retail, Education (K12), Higher education, Agriculture, Smart cities / Public access, Health care, Office buildings, Hospitality, Industry, Stadiums, arenas, and large public venues. Planning wireless solutions Identifying use cases and applications, common wireless requirements and constraints, performing a wireless system design, selecting and evaluating design parameters. RF communications RF wave characteristics, RF propagation behaviours, RF signal metrics, fundamentals of wireless modulation. other wireless carriers, common frequency bands. Radio frequency hardware Hardware levels, basic RF hardware components (circuit board level), RF link types (use category). RF device types. Mobile communications networks Mobile networks, LTE, 5G, Use cases. Short-range, low-rate, and low-power networks RF and speed, RF and range, RF and power, 802.11, 802.15.4, Bluetooth, LoRa (Long range) / LoRaWAN, ZigBee, 6LoWPAN, NB-IoT and LTE-M. Wireless sensor networks What is a Wireless Sensor Network (WSN)? WSN applications, Sensors and actuators, WSN architectures, Planning a WSN. Internet of Things (IoT) Internet of Things (IoT) defined, IoT history and its definition revisited, one more comment on the definition of IoT, IoT verticals, Oil & Gas, IoT structure/ architecture basics, IoT connected objects. Securing wireless networks Confidentiality, integrity and availability, Privacy, non-repudiation, authenticity & safety, Importance of authentication in wireless networks, Key cryptographic technologies & concepts, Authentication methods, Authorisation, OAuth 2.0 authorisation framework, monitoring. Troubleshooting wireless solutions Proper solutions design, designing and implementing wireless solutions, basic installation procedures, general configuration considerations, troubleshooting and remediation, troubleshoot common problems in wireless solutions. Programming, scripting and automation What is an API? categories of APIs, common API communication methods, choosing a language, why are we integrating systems? Application & integration architectures. Data structures & types, XML, YAML, API types.

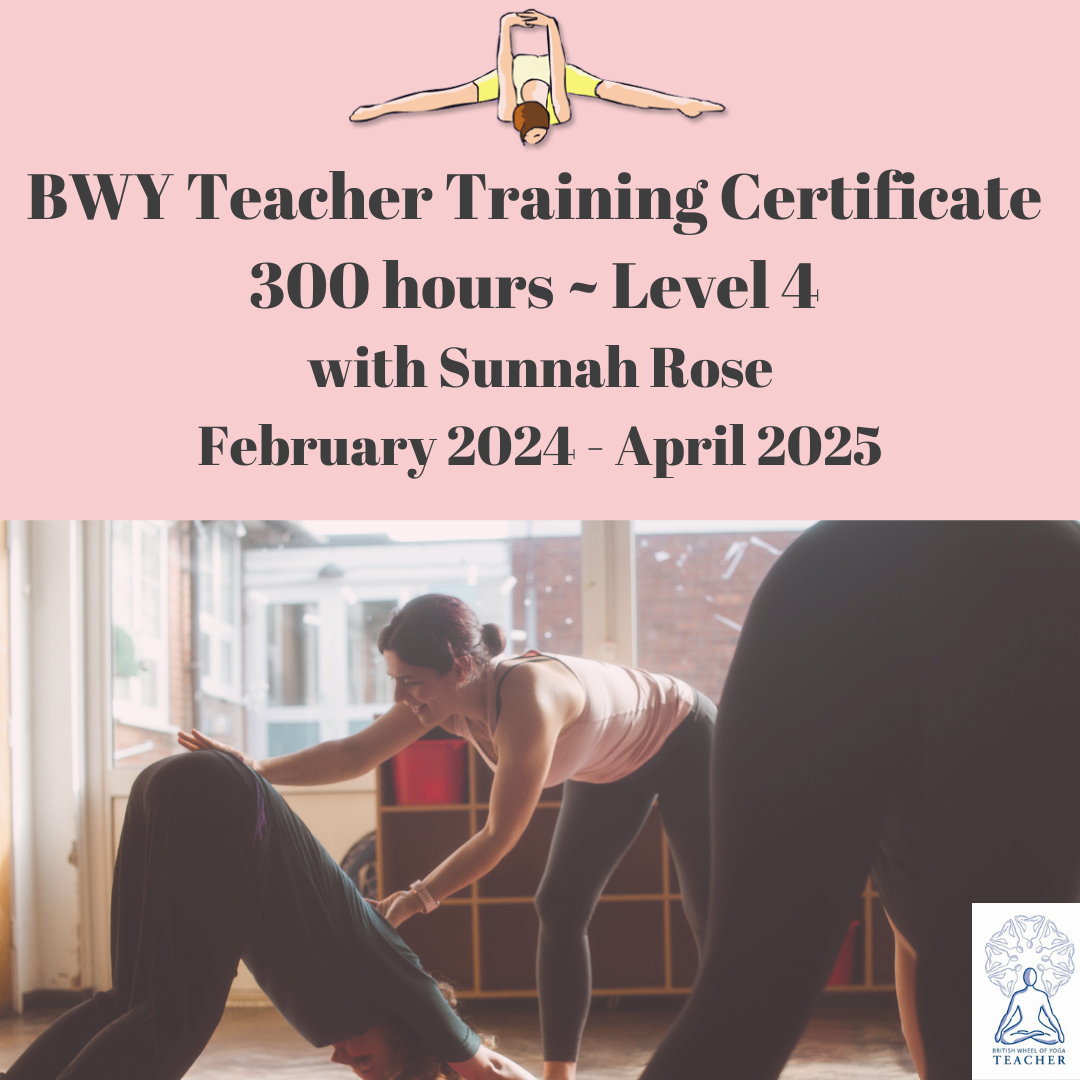
BWY Yoga Teacher Training
By Rose School Of Transformational Yoga
If you have a regular practice and are interested in becoming a Yoga Teacher than this course is for you.
Anti-racism and Diversity, Equity & Inclusion Masterclasses
By Amp Up Your Voice
www.ampupyourvoice.com

Complete JavaScript training course description A hands on course covering JavaScript programming. Core JavaScript is covered first, including the basics, arrays, functions, classes, modules and Regular expressions. Client side JavaScript is then covered including JavaScript in browsers, Scripting CSS, the jQuery library and HTML APIs. What will you learn Read JavaScript. Write JavaScript. Debug JavaScript. Complete JavaScript training course details Who will benefit: Anyone wishing to learn JavaScript. Prerequisites: None. Duration 3 days Complete JavaScript training course contents CORE JAVASCRIPT Lexical structure: Character set, comments, literals, identifiers, and reserved words, optional semicolons.. Types, values and variables: Numbers, text, boolean values, null and undefines, the global object, wrapper objects, immutable primitive values and mutable object references, type conversions, variable declaration, variable scope. Expressions and operators: Primary expressions, object and array initializers, function definition expressions, property access expressions, invocation expressions, object creation expressions, operator overview, arithmetic expressions, relational expressions, logical expressions, assignment expressions, evaluation expressions, miscellaneous operators. Statements: Expression statements, compound and empty statements, declaration statements, conditionals, loops, jumps, miscellaneous statements, summary of JavaScript statements. Objects: Creating objects, querying and setting properties, deleting properties, testing properties, enumerating properties, property getters and setters, property attributes, object attributes, serializing objects, object methods. Arrays: Creating arrays, reading and writing array elements, sparse arrays, array length, adding and deleting array elements, iterating arrays, multi-dimensional arrays, array methods, FCMAScript 5 array methods, array type, array-like objects, strings as arrays. Functions: Defining functions, invoking functions, function arguments and parameters, functions as values, functions as namespaces, closures, function properties, methods and constructor, functional programming. Classes and modules: Classes and prototypes, classes and constructors, Java-style classes in JavaScript, augmenting classes, classes and types, object oriented techniques in JavaScript, subclasses, classes in ECMAScript 5, modules. Pattern matching and regular expressions: Defining regular expressions, string methods for pattern matching, the RegExp object. JavaScript subsets and extensions: JavaScript subsets, constants and scoped variables, destructuring assignment, iteration, shorthand functions, multiple catch clauses, E4X: ECMAScript for XML. Server-side JavaScript: Scripting Java with Rhino, asynchronous I/O with node. CLIENT SIDE JAVASCRIPT JavaScript in web browsers: Client side JavaScript, embedding JavaScript in HTML, execution of JavaScript programs, compatibility and interoperability, accessibility, security, client side frameworks. The Window object: Timers, browser location and navigation, browsing history, browser screen information, dialog boxes, error handling, document elements as window properties, multiple windows and frames. Scripting Documents: Overview of the DOM, selecting document elements, document structure and traversal, attributes, element content, creating, inserting and deleting nodes. Example: generating a table of contents, document and element geometry and scrolling, HTML forms, other document features. Scripting CSS: Overview of CSS, important CSS properties, scripting inline styles, querying computed styles, scripting CSS classes, scripting stylesheets. Handling events: Types of events, registering event handlers, event handler invocation, document load events, mouse events, mousewheel events, drag and drop events, text events, keyboard events. Scripted HTTP: Using XMLHttpRequest, HTTP by <script>: JSOMP, Comet with server-sent events. The jQuery library: jQuery basics, jQuery getters and setters, altering document structure, handling events with jQuery, Animated effects, Ajax with jQuery, Utility functions, jQuery selectors and selection methods, Extending jQuery with plug-ins. The jQuery UI library. Client side storage: localStorage and sessionStorage, Cookies, IE usingData persistence, Applicatioin storage and offline webapps. Scripted media and graphics: Scripting images, Scripting audio and video, SCG:scalable vector graphics, Graphics in a <canvas>. Scripted HTTP: Using XMLHttpRequest, HTTP by <script>: JSOMP, Comet with server-sent events. The jQuery library: jQuery basics, jQuery getters and setters, altering document structure, handling events with jQuery, Animated effects, Ajax with jQuery, Utility functions, jQuery selectors and selection methods, Extending jQuery with plug-ins. The jQuery UI library. Client side storage: localStorage and sessionStorage, Cookies, IE usingData persistence, Applicatioin storage and offline webapps. Scripted media and graphics: Scripting images, Scripting audio and video, SCG:scalable vector graphics, Graphics in a <canvas>. HTMLS APIs: Geolocation, history management, cross-origin messaging, web workers, type arrays and ArrayBuffers, blobs, the filesystem API, client side databases, web sockets.

RFID training course description This training course focuses on the technologies used in Radio Frequency Identification (RFID). What will you learn Describe the RFID architecture. Design RFID systems. Evaluate tag types. Recognise common RFID problems. RFID training course details Who will benefit: RFID technologists and system engineers. Prerequisites: RF fundamentals. Duration 2 days RFID training course contents What is RFID? Review of RF basics, what is RFID, RFID history, RFID base system architecture, frequency bands used by RFID, comparison with barcodes. RFID applications Supply chain, asset tracking, theft reduction, retail, access control, tolls. Tags Tag features, types of tag, passive and active, chips, read only, read write, affixing tags, selecting location to affix a tag, tag orientation and location, tag stacking, impact of rate of movement, tag data formats. Interrogators/readers Interrogation zones, interrogator types, antennas, read distance tests, multiple interrogators, synchronisation, dense interrogator environment issues. RFID peripherals. Standards and regulations Global regulatory requirements, regional regulatory requirements, ISO, ETSI, FCC, EPC, safety regulations/issues. Testing and troubleshooting Read rate problems, improperly tagged items, tag failure. RFID system design Antenna types, interference, antenna location and spacing, how many antennas? How many interrogators? tag types, grounding considerations, cabling, site diagrams.

Search By Location
- History Courses in London
- History Courses in Birmingham
- History Courses in Glasgow
- History Courses in Liverpool
- History Courses in Bristol
- History Courses in Manchester
- History Courses in Sheffield
- History Courses in Leeds
- History Courses in Edinburgh
- History Courses in Leicester
- History Courses in Coventry
- History Courses in Bradford
- History Courses in Cardiff
- History Courses in Belfast
- History Courses in Nottingham