- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
260 Evaluation courses in Bristol delivered Live Online
ISO 27001 Lead Implementer
By Nexus Human
Duration 4.125 Days 24.75 CPD hours This course is intended for The job roles best suited to the material in this course are: Project managers and consultants involved in and concerned with the implementation of an ISMS, expert advisors seeking to master the implementation of an ISMS, individuals responsible for ensuring conformity to information security requirements within an organization Overview Master the concepts, approaches, methods and techniques used for the implementation and effective management of an ISMS Learn how to interpret the ISO/IEC 27001 requirements in the specific context of an organization Learn how to support an organization to effectively plan, implement, manage, monitor and maintain an ISMS Acknowledge the correlation between ISO/IEC 27001, ISO/IEC 27002 and other standards and regulatory frameworks Acquire the expertise to advise an organization in implementing Information Security Management System best practices This training course is designed to prepare you to implement an information security management system (ISMS) based on the requirements of ISO/IEC 27001. It aims to provide a comprehensive understanding of the best practices of an ISMS and a framework for its continual management and improvement. Introduction to ISO/IEC 27001 and initiation of an ISMS Training course objectives and structure Standards and regulatory frameworks Information Security Management System (ISMS) Fundamental information security concepts and principles Initiation of the ISMS implementation Understanding the organization and its context ISMS scope Planning the implementation of an ISMS Leadership and project approval Organizational structure Analysis of the existing system Information security policy Risk management Statement of Applicability Implementation of an ISMS Documented information management Selection and design of controls Implementation of controls Trends and technologies Communication Competence and awareness Security operations management ISMS monitoring, continual improvement, and preparation for the certification audit Monitoring, measurement, analysis, and evaluation Internal audit h Management review Treatment of nonconformities Continual improvement Preparing for the certification audit Certification process and closing of the training course

Building services and maintenance - best-practice (In-House)
By The In House Training Company
The importance of building services to the success of an organisation has never been greater and continues to grow. Developers and occupiers are becoming more aware of the contribution that building services make to the well being of occupants and hence their perception of the quality of the working environment. Those involved with the design, construction, maintenance and operation will increasingly be required to deliver building services that demonstrable contribution to the occupier's business. Energy efficiency, carbon management and occupant satisfaction depend substantially on the way building services are designed, managed and operated. To optimise these aspects, an informed strategic approach is essential. Tried and tested techniques and processes are available that, when applied holistically, will deliver substantial benefits. This course reviews best practice in the area and inspires participants to ensure that building services perform at their optimal level. To provide a better understanding of how building services can be designed, managed and operated to: Maximise occupant comfort, satisfaction and wellbeing Add value and contribute to the success of the business of the occupier Improve health safety Reduce operating cost, energy use, carbon emissions and environmental impact Optimise cost and value Provide strategies for continuous improvement and sustainable operation 1 Building services fundamentals The function of services in commercial buildings and their importance to the core business 2 Techniques and processes for optimising cost and value Programmed operation evaluation Continuous commissioning Lifetime product management Performance-based service Energy efficiency and the scope for environmental improvement 3 Making the business case and preparing the strategy Motivating decision-makers Empowering those who have to deliver the results Managing business risk 4 Strategy implementation and monitoring results Ensuring that rich and robust feedback is available to support continuous improvement and strategy enhancementWhen to get feedbackWhyHowWhat to do with it 5 Case histories and 'air time' Sharing experience and addressing specific issues of interest to participants Course review Close

Motivating people - skills for managers (In-House)
By The In House Training Company
This training day will help managers explore what they need to do to create a motivating environment at work and learn some theory, tools and ideas to inspire motivation at individual and team level. Motivation is a key factor in effective people management and successful team performance. It involves engaging and inspiring your people and developing them in such ways as to improve their effectiveness and thus have a greater benefit to customers. It can also involve having tough conversations with those who do not seem to be motivated. By the end of the workshop participants will be able to: Identify key motivating factors at work and learn and create ideas to better engage staff Learn a conversation tool to use for challenging discussions Explain their role in motivating staff and understand a range of techniques and approaches to use in the workplace Review learning and have an action plan to take back and implement at work 1 Welcome, housekeeping, objectives Breaking the ice Setting personal objectives 2 Group work: identifying personal motivators and where they come from 3 Defining motivation The characteristics of a motivated team Input and group discussion 4 Factors impacting on motivation at work Using pre-work to identify challenges, hotspots and obstacles Feedback in plenary Exploring the benefits of motivation that address current challenges and agreeing outcomes for change 5 Commitment vs. compliance - organisational engagement and the manager's approach to buy in 6 Team challenge task using a theory about motivation Trainer input and review in plenary 7 Group task - complete a plan for individuals identified in pre-workshop task 8 Skill / will - a motivation tool: trainer input, followed by tasks that are assessed and discussed in peer groups 1-2-1 feedback task on approaches and plans to be taken back and used at work Feedback and plenary review 9 DEAL - a conversation tool: how to construct a conversation plan about motivation with an individual Peer professional 1-2-1s to practice the discussion planned and gain feedback 10 Review, evaluation and action planning

Stress Management
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for This course is intended for anyone who wants to develop a toolbox of personal stress management skills. Overview Upon successful completion of this course, students will be able to identify the best approach to handle a stressful situation; understand what lifestyle elements, routines and relaxation techniques can help reduce stress. In this course, students will apply a three-option method to address any stressful situation. Module One: Getting Started Workshop Objectives Pre-Assignment Pre-Test Action Plan Form Evaluation Form Module Two: Understanding Stress What is Stress? What is Eustress? Understanding the Triple ?A? Approach Practical Illustration Module Two Review Questions Module Three: Creating a Stress-Reducing Lifestyle Eating Properly Exercising Regularly Sleeping Well Practical Illustration Module Three Review Questions Module Four: Altering the Situation The First A Identifying Appropriate Situations Creating Effective Actions Practical Illustration Module Four Review Questions Module Five: Avoiding the Situation The Second A Identifying Appropriate Situations Creating Effective Actions Practical Illustration Module Five Review Questions Module Six: Accepting the Situation The Third A Identifying Appropriate Situations Creating Effective Actions Practical Illustration Module Six Review Questions Module Seven: Using Routines to Reduce Stress Planning Meals Organizing Chores Using a To-Do List Practical Illustration Module Seven: Review Questions Module Eight: Environmental Relaxation Techniques Finding a Sanctuary Using Music Seeing the Humor Practical Illustration Module Eight: Review Questions Module Nine: Physical Relaxation Techniques Soothing Stretches Deep Breathing Tensing and Relaxing1 Meditation1 Practical Illustration Module Nine: Review Questions Module Ten: Coping with Major Events Establishing a Support System Creating a Plan Knowing When to Seek Help Practical Illustration Module Ten: Review Questions Module Eleven: Our Challenge to You Creating a Stress Log Week One: Recording Events1 Week Two: Identifying Stressors and Creating a Plan1 Week Three: Creating New Habits Reviewing and Evaluating Practical Illustration Module Eleven: Review Questions Module Twelve: Wrapping Up Words from the Wise Lessons Learned

EXIN Information Security Foundation based on ISO/IEC 27001 - Professional
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Security professionals. This module is intended for everyone who is involved in the implementation, evaluation and reporting of an information security program, such as an Information Security Manager (ISM), Information Security Officer (ISO) or a Line Manager, Process Manager or Project Manager with security responsibilities. Basic knowledge of Information Security is recommended, for instance through the EXIN Information Security Foundation based on ISO/IEC 27001 certification. Overview The module Information Security Management Professional based on ISO/IEC 27001 (ISMP.EN) tests understanding of the organizational and managerial aspects of information security.The subjects of this module are: Information security perspectives: business, customer, service provider/supplier Risk Management: analysis, controls, remaining risks Information security controls: organizational, technical, physical. Information security is the preservation of confidentiality, integrity and availability of information (ISO/IEC 27000 definition). Information security is gaining importance in the Information Technology (IT) world. Globalization of the economy is leading to an ever-increasing exchange of information between organizations (their staff, customers and suppliers) and an explosion in the use of networked computers and computing devices. The core activities of many companies completely rely on IT. Enterprise resource planning (ERP) management systems, the control systems that govern how a building runs or a manufacturing machine functions, day-to-day communications - everything - runs on computers. The vast majority of information - the most valuable commodity in the world - passes through IT. Information is crucial for the continuity and proper functioning of both individual organizations and the economies they fuel; this information must be protected against access by unauthorized people, protected against accidental or malicious modification or destruction and must be available when it is needed. Companies and individual users of technology are also beginning to understand how important security is and are beginning to make choices based on the security of the technology or service. Information Security Perspectives The candidate understands the business interest of information security The canidate understands the customer perspective on governance The candidate understands the supplierïs responsibilities in security assurance Risk Mangement The candidate understands the principles of risk management The candidate knows how to control risks The candidate knows how to deal with remaining risks Information Security Controls The candidate has knowledge of organizational controls The candidate has knowledge of technical controls The candidate has knowledge of physical, employment-related and continuity controls

ISO 22301 Lead Implementer
By Nexus Human
Duration 4.125 Days 24.75 CPD hours This course is intended for The job roles best suited to the material in this course are: Project managers and consultants involved in business continuity Expert advisors seeking to master the implementation of the business continuity management system Individuals responsible to maintain conformity with BCMS requirements within an organization Members of the BCMS team Overview Understand the concepts, approaches, methods, and techniques used for the implementation and effective management of a BCMS. Learn how to interpret and implement the requirements of ISO 22301 in the specific context of an organization. Understand the operation of the business continuity management system and its processes based on ISO 22301. Learn how to interpret and implement the requirements of ISO 22301 in the specific context of an organization. No two disasters in the world cause equal damage. Between the unpredictability of natural disasters, information security breaches, and incidents of different nature, preparedness can make you stand out in the crowd and predict the future of your business. In light of this, proper planning is essential to mitigating risks, avoiding consequences, coping with the negative effects of disasters and incidents, but at the same time, continuing your daily operations so that customer needs do not remain unfulfilled.This training course will prepare its participants to implement a business continuity management system (BCMS) in compliance with the requirements of ISO 22301. Attending this training course allows you to gain a comprehensive understanding of the best practices of the business continuity management system and to be able to establish a framework that allows the organization to continue operating efficiently during disruptive events Introduction to ISO 22301 and initiation of a BCMS Training course objectives and structure Standards and regulatory frameworks Business continuity management system (BCMS) Fundamental business continuity concepts and principles Initiation of the BCMS implementation Understanding the organization and its context BCMS scope Implementation plan of a BCMS Leadership and commitment Business continuity policy Risks, opportunities, and business continuity objectives Support for the BCMS Business impact analysis Risk assessment Implementation of a BCMS Business continuity strategies and solutions Business continuity plans and procedures Incident response and emergency response Crisis management Exercise programs Monitoring, measurement, analysis, and evaluation Internal audit BCMS monitoring, continual improvement, and preparation for the certification audi Management review Treatment of nonconformities Continual improvement Preparation for the certification audit Closing of the training course

GDPR Data Protection Officer
By Nexus Human
Duration 4.125 Days 24.75 CPD hours This course is intended for Managers or consultants seeking to prepare and support an organization in planning, implementing, and maintaining a compliance program based on the GDPR DPOs and individuals responsible for maintaining conformance with the GDPR requirements Members of information security, incident management, and/or business continuity teams Technical and compliance experts seeking to prepare for a data protection officer role Expert advisors involved in the security of personal data Overview Understand the concepts of the GDPR and interpret its requirements Understand the content and the correlation between the General Data Protection Regulation and other regulatory frameworks and applicable standards, such as ISO/IEC 27701 and ISO/IEC 29134 Develop the ability to inform, advise, and monitor compliance with the GDPR and cooperate with the supervisory authority Acquire the competence to perform the role and daily tasks of the data protection officer in an organizationit Considering that data breaches have become highly sophisticated in the recent years, the need for data protection has increased as well.Information Security is crucial to the success of any organization since it deals with the protection of sensitive data from unauthorized access, use, replication and destruction. As such, organizations should put in place measures and controls to manage and diminish Information Security risks and comply with GDPR requirements. In case organizations fail to comply with the GDPR requirements, the penalties can reach up to 2% of an organization?s annual turnover. Also, in case of more serious infringements, the penalties can amount to 4% of an organization?s annual revenue. The implementation of a Privacy Framework, on the other hand, will allow professionals to develop and implement reliable controls that are generally accepted.Becoming a Certified Data Protection Officer will enable you to acquire the necessary expertise to understand the risks that could have a negative impact on your organization and implement the required strategic responses based on the GDPR best practices, requirements and principles. Introduction to the GDPR concepts and principles Training course objectives and structure General Data Protection Regulation (GDPR) Core considerations for the GDPR Designation of the DPO and analysis of the GDPR compliance program Designation of the DPO Analysis of the GDPR compliance program Relationship with the top management Data protection policy Register of processing activities Risk management process DPO operations Data protection impact assessment Documentation management Evaluation of the data protection controls Data protection and technology Awareness, training, and communication Monitoring and continual improvement of GDPR compliance Incident management and personal data breaches Monitoring and measuring compliance Data protection internal audit Treatment of nonconformities Continual improvement Closing the training course

EC-Council Certified Threat Intelligence Analyst (C|TIA)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Organizations today demand a professional-level cybersecurity threat intelligence analyst who can extract the intelligence from data by implementing various advanced strategies. Such professional-level programs can only be achieved when the core of the curricula maps with and is compliant to government and industry published threat intelligence frameworks. Ethical Hackers Security Practitioners, Engineers, Analysts, Specialist, Architects, and Managers Threat Intelligence Analysts, Associates, Researchers, Consultants Threat Hunters SOC Professionals Digital Forensic and Malware Analysts Incident Response Team Members Any mid-level to high-level cybersecurity professionals with a minimum of 2 years of experience. Individuals from the information security profession and who want to enrich their skills and knowledge in the field of cyber threat intelligence. Individuals interested in preventing cyber threats. Overview This program will benefit students who are looking to build effective threat intelligence for their organization in order to combat modern-day cyber-attacks and prevent future attacks. Certified Threat Intelligence Analyst (C|TIA) is designed and developed in collaboration with cybersecurity and threat intelligence experts across the globe to help organizations identify and mitigate business risks by converting unknown internal and external threats into known threats. It is a comprehensive, specialist-level program that teaches a structured approach for building effective threat intelligence. Introduction to Threat Intelligence Understanding Intelligence Understanding Cyber Threat Intelligence Overview of Threat Intelligence Lifecycle and Frameworks Cyber Threats and Kill Chain Methodology Understanding Cyber Threats Understanding Advanced Persistent Threats (APTs) Understanding Cyber Kill Chain Understanding Indicators of Compromise (IoCs) Requirements, Planning, Direction, and Review Understanding Organization?s Current Threat Landscape Understanding Requirements Analysis Planning Threat Intelligence Program Establishing Management Support Building a Threat Intelligence Team Overview of Threat Intelligence Sharing Reviewing Threat Intelligence Program Data Collection and Processing Overview of Threat Intelligence Data Collection Overview of Threat Intelligence Collection Management Overview of Threat Intelligence Feeds and Sources Understanding Threat Intelligence Data Collection and Acquisition Understanding Bulk Data Collection Understanding Data Processing and Exploitation Data Analysis Overview of Data Analysis Understanding Data Analysis Techniques Overview of Threat Analysis Understanding Threat Analysis Process Overview of Fine-Tuning Threat Analysis Understanding Threat Intelligence Evaluation Creating Runbooks and Knowledge Base Overview of Threat Intelligence Tools Intelligence Reporting and Dissemination Overview of Threat Intelligence Reports Introduction to Dissemination Participating in Sharing Relationships Overview of Sharing Threat Intelligence Overview of Delivery Mechanisms Understanding Threat Intelligence Sharing Platforms Overview of Intelligence Sharing Acts and Regulations Overview of Threat Intelligence Integration

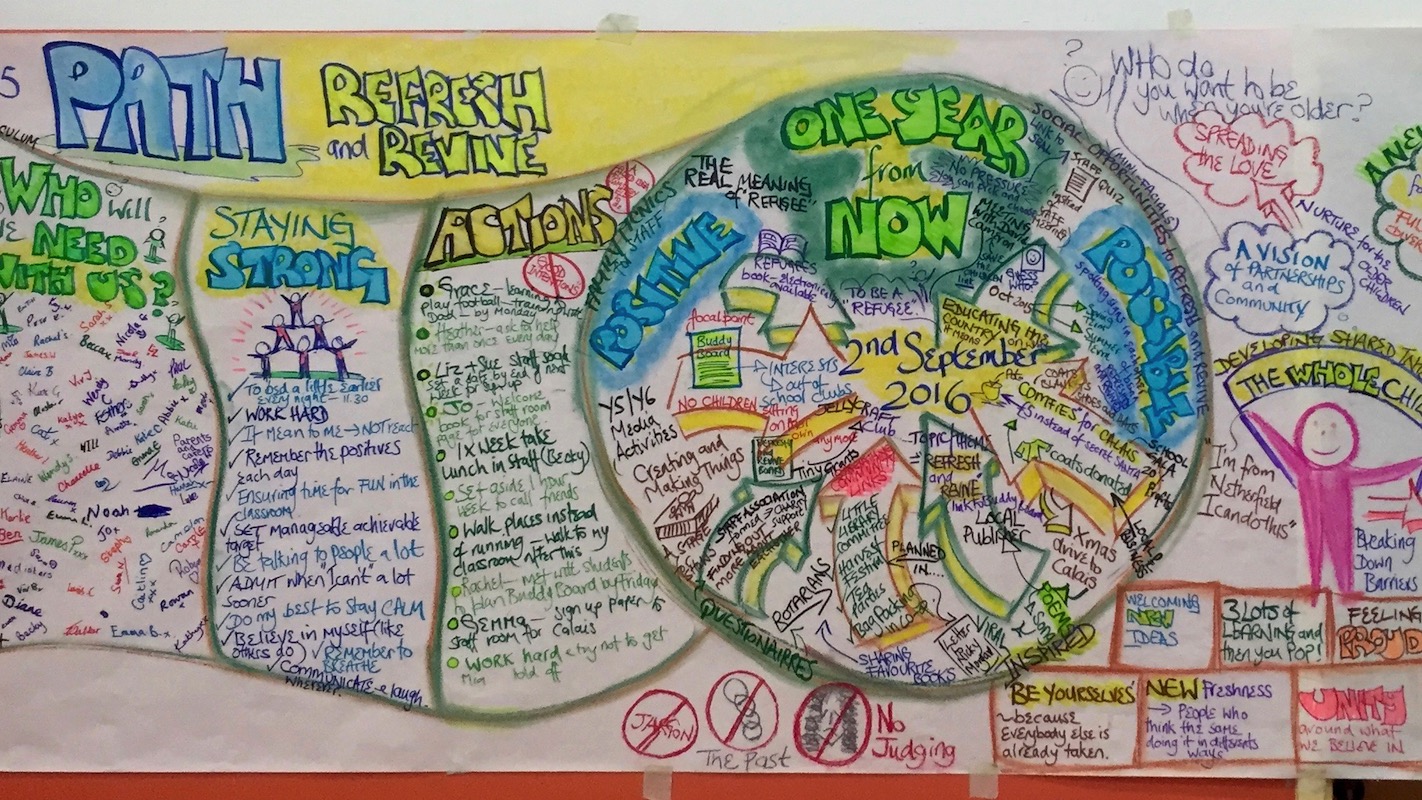
PATH – PERSON CENTRED PLANNING IN ACTION
By Inclusive Solutions
Need a PATH? A person-centred plan? This is a planning process not a training day. Let us facilitate your planning and refocus your story whilst strengthening you and your group, team, family, staff or organisation. This tool uses both process and graphic facilitation to help any group develop a shared vision and then to make a start on working out what they will need to do together to move towards that vision. Is your team or family stuck? Want to move on, but haunted by the past and cannot get any useful dialogue started about the future? Facing a challenging transition into a new school or setting? Leaving school? Bored with annual reviews, transition plans and review meetings? Want to find a way of making meetings and planning feel more real and engaging? Need an approach, which engages a young person respectfully together with his or her family and friends? Want the ultimate visual record of the process of a meeting, which will help everyone, keep track? Want to problem solve and plan for the future of a small or large group, service or organisation up to the size of an LA Give your team the opportunity to pause and reflect on what matters most to them about the work they do. The act of listening to each other creates relationship and strengthens trust and inclusion within the team – in creating a shared vision, groups of people build a sense of commitment together. They develop images of the future we want to create together, along with the values that will be important in getting there and the goals they want to see achieved along the way. Unfortunately, many people still think vision is the top leader’s job. In schools, the vision task usually falls to the Headteacher and/or the governors or it comes in a glossy document from the local authority or the DfES. But visions based on authority are not sustainable. Using the planning tool PATH (Pearpoint, Forest and OBrien 1997) and other facilitation sources we use both process and graphic facilitation to enable the group to build their picture of what they would love to see happening within their organisation/community in the future and we encourage this to be a positive naming, not just a list of the things they want to avoid. Outcomes To create a shared vision To name shared goals To enrol others To strengthen the group To explore connections and needs To specify an Action Plan To create a visual graphic record of the whole event Process Content PATH is a creative planning tool that utilises graphic facilitation to collect information and develop positive future plans. PATH goes directly to the future and implements backwards planning to create a step by step path to a desirable future. (Inclusion Press, 2000). These tools were developed by Jack Pearpoint, Marsha Forest and John O’Brien to help marginalised people be included in society and to enable people to develop a shared vision for the future. PATH can be used with individuals and their circle of support, families teams and organisations. Both MAP and PATH are facilitated by two trained facilitators – one process facilitator who guides people through the stages and ensures that the person is at the centre and one graphic facilitator who develops a graphic record of the conversations taking place in the room. Follow the link below to read a detailed thesis by Dr Margo Bristow on the use of PATH by educational Psychologists in the UK. AN EXPLORATION OF THE USE OF PATH (A PERSON-CENTRED PLANNING TOOL) BY EDUCATIONAL PSYCHOLOGISTS WITH VULNERABLE AND CHALLENGING PUPILS The findings indicate that PATH impacted positively and pupils attributed increased confidence and motivation to achieve their goals to their PATH. Parents and young people felt they had contributed to the process as equal partners, feeling their voices were heard. Improved pupil- parent relationships and parent-school relationships were reported and the importance of having skilled facilitators was highlighted. Although participants were generally positive about the process, many felt daunted beforehand, possibly due to a lack of preparation. Pre-PATHplanning and post-PATH review were highlighted as areas requiring further consideration by PATH organisers. Recommendations to shape and improve the delivery of PATH are outlined together with future research directions.