- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1686 Environment courses in Llantrisant delivered Live Online
Level 7 Diploma In Risk Management Pathway To MSc In Risk Management
4.9(261)By Metropolitan School of Business & Management UK
Level 7 Diploma In Risk Management Pathway To MSc In Risk Management Level 7 Diploma in Risk Management (QCF) – 6 - 8 Months Credits: 120 Credits The objective of the Level 7 Diploma in Risk Management is to provide learners with the skills and understanding of risk management that align with good strategic decision making to maintain organisations’ competitive advantage. The OTHM Level 7 Diploma in Risk Management programme provides an in-depth understanding of risk and its application in practice both for financial and non-financial organisations. Learners will learn both theoretical and practical understanding of risk including risk measurement and modelling. This programme is a Pathway programme to MSc in Risk Management. Course Details The Level 7 Diploma in Risk Management qualification consists of 6 mandatory units making a combined total of 120 credits, 1200 hours Total Qualification Time (TQT) and 600 Guided Learning Hours (GLH) for the completed qualification.Modules (120 Credits): Principles of Risk Management Strategic Risk Management Responsible Leadership and Governance Organisational and Environmental Risk Risk Analysis and Modelling Advanced Research Methods Accreditation All MSBM courses are accredited by the relevant partners and awarding bodies. Please refer to MSBM accreditation in about us for more details. University Progression University Top-up On completion of this course, students have the opportunity to complete a Master degree programme from a range of UK universities. The top-up programme can be studied online or on campus. The top-up comprises the final 60 credits which consist of either a dissertation or a dissertation and one module. (The course tuition fee listed above does NOT include the top-up fees) University Progression Click here to see University routes and fee information for progression. Entry Requirements For entry onto the Level 7 Diploma in Risk Management leading to the MSc in Risk Management qualification, learners must possess: An honours degree in related subject or UK level 6 diploma or equivalent overseas qualification i.e. Bachelors Degree or Higher National Diploma OR Mature learners (over 25) with at least 5 years of management experience if they do not possess the above qualification (this is reviewed on a case by case basis) Workshops Workshops are conducted by live webinars for all students. Visa Requirements There is no Visa requirement for this programme.

CompTIA Advanced Security Practitioner (CASP+)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is targeted toward an IT Professional that has the technical knowledge and skills required to conceptualize, design, and engineer secure solutions across complex enterprise environments. Students should have a minimum of 10 years experience including at least 5 years of hands-on technical security experience. Overview Upon successful completion of this course, students will be able to: Identify enterprise security fundamentals. Apply enterprise security technology solutions. Implement security design and solutions. Manage risk, policies and procedures within an enterprise. Integrate security solutions within an enterprise. Conduct security research and analysis. In this course, students will examine advanced security concepts, principles, and implementations that pertain to enterprise level security. Prerequisites CompTIA Cybersecurity Analyst (CySA+) Certification 1 - Enterprise Security Architecture The Basics of Enterprise Security The Enterprise Structure Enterprise Security Requirements 2 - Enterprise Security Technology Common Network Security Components and Technologies Communications and Collaboration Security Cryptographic Tools and Techniques Advanced Authentication 3 - Enterprise Resource Technology Enterprise Storage Security Issues Distributed, Shared, and Virtualized Computing Cloud Computing and Security 4 - Security Design and Solutions Network Security Design Conduct a Security Assessment Host Security 5 - Application Security Design Application Security Basics Web Application Security 6 - Managing Risk, Security Policies, and Security Procedures Analyze Security Risk Implement Risk Mitigation Strategies and Controls Implement Enterprise-Level Security Policies and Procedures Prepare for Incident Response and Recovery 7 - Enterprise Security Integration The Technology Life Cycle Inter-Organizational Change Integrate Enterprise Disciplines to Achieve Secure Solutions 8 - Security Research and Analysis Perform an Industry Trends and Impact Analysis Perform an Enterprise Security Analysis

Taking Your Book To School – Walkie-talkie Style!
By Isobel Kent
Taking Your Book To School® Walkie-talkie Style! Access to me for a full day, 9–5, to move your book closer to school. So, you’ve written a children's book and now you’re trying to get it from your shelf to the classroom and into the hands of children … Now what? You know that schools are the gatekeepers of your target market: children and their families and you know that teachers and school visits should be on your radar. How do you get in, though?
Windows and Microsoft Office Basics
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for This course is intended for individuals who want to gain basic introductory knowledge of working of OLL. Overview Upon successful completion of this course, students will be able to attend class in the OLL environment without difficulties. In this course, students will learn to navigate and work in the OLL environment. Intro to OLL Environment Participation buttons Working in the lab environment Basic Windows 7 Skills Managing working with multiple program Task Bar/Start Bar Files & Folders Copy Files to New Folders Search Basic Word 2010 Skills Word 2010 Interface (Ribbon, Quick Access Toolbar, Different Views, Zoom, and Navigating a document) Create a new document Format a document Edit a document Save and Print Basic Excel 2010 Skills Excel 2010 Interface (Ribbon, Quick Access Toolbar, Different Views, Zoom, And Navagating a document) Create a new workbook Enter and edit data Basic Formulas and Functions save and Print

Certified Information Systems Auditor (CISA)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The intended audience for this course is information systems security professionals, internal review auditors, and other individuals who have an interest in aspects of information systems audit, controls, and security. Overview Upon successful completion of this course, students will be able to: - implement information systems audit services in accordance with information systems audit standards, guidelines, and best practices. - evaluate an organizations structure, policies, accountability, mechanisms, and monitoring practices. - evaluate information systems acquisition, development, and implementation. - evaluate the information systems operations, maintenance, and support of an organization; and evaluate the business continuity and disaster recovery processes used to provide assurance that in the event of a disruption, IT services are maintained. - define the protection policies used to promote the confidentiality, integrity, and availability of information assets. In this course, students will evaluate organizational policies, procedures, and processes to ensure that an organizations information systems align with its overall business goals and objectives. 1 - The Process of Auditing Information Systems ISACA Information Systems Auditing Standards and Guidelines Fundamental Business Processes Develop and Implement an Information Systems Audit Strategy Plan an Audit Conduct an Audit The Evidence Life Cycle Communicate Issues, Risks, and Audit Results Support the Implementation of Risk Management and Control Practices 2 - IT Governance and Management Evaluate the Effectiveness of IT Governance Evaluate the IT Organizational Structure and HR Management Evaluate the IT Strategy and Direction Evaluate IT Policies, Standards, and Procedures Evaluate the Effectiveness of Quality Management Systems Evaluate IT Management and Monitoring of Controls IT Resource Investment, Use, and Allocation Practices Evaluate IT Contracting Strategies and Policies Evaluate Risk Management Practices Performance Monitoring and Assurance Practices Evaluate the Organizations Business Continuity Plan 3 - Information Systems Acquisition, Development, and Implementation Evaluate the Business Case for Change Evaluate Project Management Frameworks and Governance Practices Development Life Cycle Management Perform Periodic Project Reviews Evaluate Control Mechanisms for Systems Evaluate Development and Testing Processes Evaluate Implementation Readiness Evaluate a System Migration Perform a Post-Implementation System Review 4 - Information Systems Operations, Maintenance, and Support Perform Periodic System Reviews Evaluate Service Level Management Practices Evaluate Third-Party Management Practices Evaluate Operations and End User Management Practices Evaluate the Maintenance Process Evaluate Data Administration Practices Evaluate the Use of Capacity and Performance Monitoring Methods Evaluate Change, Configuration, and Release Management Practices Evaluate Problem and Incident Management Practices Evaluate the Adequacy of Backup and Restore Provisions 5 - Protection of Information Assets Information Security Design Encryption Basics Evaluate the Functionality of the IT Infrastructure Evaluate Network Infrastructure Security Evaluate the Design, Implementation, and Monitoring of Logical Access Controls Risks and Controls of Virtualization Evaluate the Design, Implementation, and Monitoring of Data Classification Process Evaluate the Design, Implementation, and Monitoring of Physical Access Controls Evaluate the Design, Implementation, and Monitoring of Environmental Controls

Getting to grips with GCSE History At GLA Tutors, we are dedicated to helping students excel in their GCSE History examinations. Our experienced tutors are passionate about history and committed to providing comprehensive support aligned with the AQA examination board's specification. Let's explore the breakdown of the AQA GCSE History specification: Paper 1: Understanding the Modern World This paper focuses on key historical events and developments from the 20th century. Our tutors will guide students through topics such as the origins of World War I, the Treaty of Versailles, the rise of Hitler and the Nazis, the Cold War, and the civil rights movement. We provide in-depth analysis, engaging discussions, and access to a wide range of historical sources to help students develop a deep understanding of these crucial events. Paper 2: Shaping the Nation In this paper, students will explore the history of Britain from medieval times to the present day. Our tutors will delve into topics such as the Norman Conquest, the Tudors, the Industrial Revolution, the British Empire, and the impact of immigration. We provide comprehensive guidance on key historical figures, significant events, and the social, political, and economic changes that shaped the nation. Through interactive lessons and engaging activities, we help students develop a strong grasp of British history. Historical Investigation This component allows students to conduct an in-depth investigation on a topic of their choice. Our tutors will provide guidance on selecting a suitable topic, conducting research, analysing sources, and presenting findings. We help students develop critical thinking skills, research methodology, and the ability to construct coherent and well-supported arguments. This component allows students to develop their historical research skills while exploring a topic of personal interest. At GLA Tutors, we foster a supportive and inclusive learning environment, where students can explore and deepen their understanding of history. Our tutors provide personalised one-on-one sessions, group discussions, and access to a range of learning resources to cater to each student's unique needs. Beyond the specification, we encourage critical thinking, historical empathy, and the ability to analyse and interpret historical sources. We also focus on developing strong exam techniques, essay writing skills, and effective revision strategies to maximise exam success. Join us at GLA Tutors and embark on a transformative journey in GCSE History. Our tutors are here to guide you towards academic excellence, a deeper appreciation for the past, and the ability to critically analyse historical events and their impact on the world today. Feel free to explore our website for more information or reach out to us with any questions you may have. We can provide assistance for everything you need to prepare students for exams, including: past papers, mark schemes and examiners’ reports specimen papers and mark schemes for new courses exemplar student answers with examiner commentaries high quality revision guides

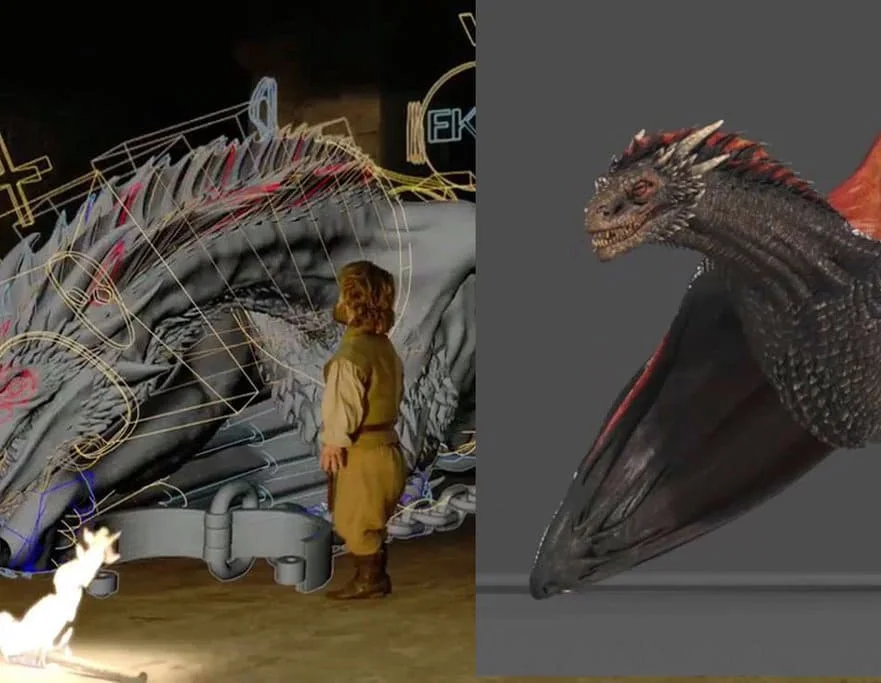
Diploma in Visual Effects for Film and Television Animation
By ATL Autocad Training London
Who is this course for? The Diploma in Visual Effects for Film and Television Animation is tailored for individuals aspiring to work in the Visual Effects, TV, Film, and 3D animation industry. Gain essential skills necessary for a successful career in these fields. Click here for more info: Website Duration: 120 hours of 1-on-1 Training. When can I book: 9 am - 4 pm (Choose your preferred day and time once a week). Monday to Saturday: 9 am - 7 pm (Flexible timing with advance booking). Course Overview for a 120-Hour Diploma Program in Game Design and Development Term 1: Introduction to Game Design and 3D Modeling (40 hours) Module 1: Introduction to Game Design (1 hour) Understanding the game development industry and current trends Exploring game mechanics and fundamental design principles Introduction to the game engines and tools utilized in the program Module 2: 3D Modeling with 3ds Max (25 hours) Familiarization with 3ds Max and its user interface Mastering basic modeling techniques like box modeling and extrusion Advanced modeling skills including subdivision and topology Texturing and shading techniques tailored for game development Module 3: Character Design and Animation (10 hours) Introduction to character design and its developmental process Creating and rigging characters specifically for games Keyframe animation techniques for character movement Term 2: Game Development and Unity 3D (40 hours) Module 4: Unity 3D Basics (20 hours) Navigating Unity 3D and understanding its interface Grasping fundamental game development concepts within Unity Creating game objects, writing scripts, and designing scenes Introduction to scripting using C# Module 5: Advanced Game Development with Unity 3D (10 hours) Constructing game mechanics including UI, scoring, and game states Working with physics and collision systems in Unity Crafting intricate game environments and level designs Module 6: Game Assets with Photoshop (10 hours) Exploring Photoshop tools and features for game asset creation Crafting game elements such as textures, sprites, and icons Optimizing assets for seamless integration into game development Term 3: Advanced Game Design and Portfolio Development (40 hours) Module 7: Advanced Game Design (20 hours) Delving into advanced game design concepts like balancing and difficulty curves Understanding player psychology and methods for engaging audiences Implementing game analytics and user testing for refinement Module 8: Portfolio Development (24 hours) Building a comprehensive portfolio showcasing acquired skills Effective presentation techniques for showcasing work Establishing a professional online presence and networking strategies Final Project: Creating and presenting a collection of best works in collaboration with tutors and fellow students Please note: Any missed sessions or absence without a 48-hour notice will result in session loss and a full class fee charge due to the personalized one-to-one nature of the sessions. Students can request pauses or extended breaks by providing written notice via email. What can you do after this course: Software Proficiency: Master industry-standard design tools for architectural and interior projects. Design Expertise: Develop a deep understanding of design principles and spatial concepts. Visualization Skills: Acquire advanced 2D/3D rendering and virtual reality skills for realistic design representation. Communication and Collaboration: Enhance communication skills and learn to collaborate effectively in design teams. Problem-Solving: Develop creative problem-solving abilities for real-world design challenges. Jobs and Career Opportunities: Architectural Visualizer Interior Designer CAD Technician Virtual Reality Developer 3D Modeler Project Coordinator Freelance Designer Visualization Consultant Students can pursue these roles, applying their expertise in architectural and interior design across various professional opportunities. Course Expectations: Maintain a dedicated notebook to compile your study notes. Schedule makeup sessions for any missed coursework, subject to available time slots. Keep meticulous notes and maintain a design folder to track your progress and nurture creative ideas. Allocate specific time for independent practice and project work. Attain certification from the esteemed professional design team. Post-Course Proficiencies: Upon successful course completion, you will achieve the following: Develop confidence in your software proficiency and a solid grasp of underlying principles. Demonstrate the ability to produce top-tier visuals for architectural and interior design projects. Feel well-prepared to pursue positions, armed with the assurance of your software expertise. Continued Support: We are pleased to offer lifetime, complimentary email and phone support to promptly assist you with any inquiries or challenges that may arise. Software Accessibility: Access to the required software is available through either downloading it from the developer's website or acquiring it at favorable student rates. It is important to note that student software should be exclusively utilized for non-commercial projects. Payment Options: To accommodate your preferences, we provide a range of payment options, including internet bank transfers, credit cards, debit cards, and PayPal. Moreover, we offer installment plans tailored to the needs of our students. Course Type: Certification. Course Level: Basic to Advanced. Time: 09:00 or 4 pm (You can choose your own day and time once a week) (Monday to Friday, 09 am to 7 pm, you can choose anytime by advance booking. Weekends can only be 3 to 4 hrs due to heavy demand on those days). Tutor: Industry Experts. Total Hours: 120 Price for Companies: £3500.00 (With VAT = £4200) For Companies. Price for Students: £3000.00 (With VAT = £3600) For Students.
Developing Applications with Google Cloud
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Application developers who want to build cloud-native applications or redesign existing applications that will run on Google Cloud Platform Overview This course teaches participants the following skills: Use best practices for application development. Choose the appropriate data storage option for application data. Implement federated identity management. Develop loosely coupled application components or microservices. Integrate application components and data sources. Debug, trace, and monitor applications. Perform repeatable deployments with containers and deployment services. Choose the appropriate application runtime environment; use Google Container Engine as a runtime environment and later switch to a no-ops solution with Google App Engine flexible environment. Learn how to design, develop, and deploy applications that seamlessly integrate components from the Google Cloud ecosystem. This course uses lectures, demos, and hands-on labs to show you how to use Google Cloud services and pre-trained machine learning APIs to build secure, scalable, and intelligent cloud-native applications. Best Practices for Application Development Code and environment management. Design and development of secure, scalable, reliable, loosely coupled application components and microservices. Continuous integration and delivery. Re-architecting applications for the cloud. Google Cloud Client Libraries, Google Cloud SDK, and Google Firebase SDK How to set up and use Google Cloud Client Libraries, Google Cloud SDK, and Google Firebase SDK. Lab: Set up Google Client Libraries, Cloud SDK, and Firebase SDK on a Linux instance and set up application credentials. Overview of Data Storage Options Overview of options to store application data. Use cases for Google Cloud Storage, Cloud Firestore, Cloud Bigtable, Google Cloud SQL, and Cloud Spanner. Best Practices for Using Cloud Firestore Best practices related to using Cloud Firestore in Datastore mode for:Queries, Built-in and composite indexes, Inserting and deleting data (batch operations),Transactions,Error handling. Bulk-loading data into Cloud Firestore by using Google Cloud Dataflow. Lab: Store application data in Cloud Datastore. Performing Operations on Cloud Storage Operations that can be performed on buckets and objects. Consistency model. Error handling. Best Practices for Using Cloud Storage Naming buckets for static websites and other uses. Naming objects (from an access distribution perspective). Performance considerations. Setting up and debugging a CORS configuration on a bucket. Lab: Store files in Cloud Storage. Handling Authentication and Authorization Cloud Identity and Access Management (IAM) roles and service accounts. User authentication by using Firebase Authentication. User authentication and authorization by using Cloud Identity-Aware Proxy. Lab: Authenticate users by using Firebase Authentication. Using Pub/Sub to Integrate Components of Your Application Topics, publishers, and subscribers. Pull and push subscriptions. Use cases for Cloud Pub/Sub. Lab: Develop a backend service to process messages in a message queue. Adding Intelligence to Your Application Overview of pre-trained machine learning APIs such as Cloud Vision API and Cloud Natural Language Processing API. Using Cloud Functions for Event-Driven Processing Key concepts such as triggers, background functions, HTTP functions. Use cases. Developing and deploying functions. Logging, error reporting, and monitoring. Managing APIs with Cloud Endpoints Open API deployment configuration. Lab: Deploy an API for your application. Deploying Applications Creating and storing container images. Repeatable deployments with deployment configuration and templates. Lab: Use Deployment Manager to deploy a web application into Google App Engine flexible environment test and production environments. Execution Environments for Your Application Considerations for choosing an execution environment for your application or service:Google Compute Engine (GCE),Google Kubernetes Engine (GKE), App Engine flexible environment, Cloud Functions, Cloud Dataflow, Cloud Run. Lab: Deploying your application on App Engine flexible environment. Debugging, Monitoring, and Tuning Performance Application Performance Management Tools. Stackdriver Debugger. Stackdriver Error Reporting. Lab: Debugging an application error by using Stackdriver Debugger and Error Reporting. Stackdriver Logging. Key concepts related to Stackdriver Trace and Stackdriver Monitoring. Lab: Use Stackdriver Monitoring and Stackdriver Trace to trace a request across services, observe, and optimize performance.

Carbon Capture, Utilization & Storage (CCUS)
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) This 5 half-day Virtual Instructor Led Training (VILT) course covers carbon capture and geological storage of carbon dioxide. Burning fossil fuels for energy is a major source of carbon dioxide emissions to the atmosphere. Most anthropogenic (man-made) carbon dioxide is emitted by coal-fired or gas-fired power plants, and significant quantities of carbon dioxide are emitted through the production and separation of carbon dioxide-rich natural gas and industries such as cement, iron and steel. Carbon Capture Utilization and Storage, or CCUS, involves the long-term storage of captured carbon dioxide emissions in subsurface geologic formations. This VILT course covers all aspects of CCUS including transport, storage and monitoring, economics and community engagement. It explores in detail the challenges of the current technology of geological storage, monitoring and verification including examples from working projects around the world. Many of these technologies are commonly employed by the petroleum industry. Successful deployment of CCUS will also require economic incentives, appropriate regulation, clarity on liability issues and acceptance by the community. These aspects of CCUS, and the corresponding opportunities for appropriately skilled organisations and individuals also will be discussed. Course Content at a Glance Context for CCS/CCUS as An Emissions-reduction Measure Principles of Geological Storage Finding Geological Storage Sites Stationary Sources of Carbon Dioxide for Capture Carbon Dioxide Capture Technologies Compression and Transport of Carbon Dioxide Economics of CCS/CCUS Community, Safety, Legal & Regulatory Issues Risk Assessment Training Objectives Upon completion of this VILT course, participants will be able to: Identify the need for Carbon Capture and Storage (CCS) Outline the key steps in the Carbon Capture and Storage process Distinguish between reservoir rocks and sealing rocks Describe the importance of permeability and porosity to storing carbon dioxide Contrast the geological structures and trapping mechanisms for storing carbon dioxide Describe the changes in geologically stored carbon dioxide over time Outline the monitoring techniques employed to ensure the carbon dioxide is safely stored Appreciate the industrial applications of carbon dioxide capture Recognize the scale of industry required for transporting and storing carbon dioxide Describe economic considerations for CCS/CCUS Outline the economic and environmental opportunities and challenges with using carbon dioxide injection in a range of applications Explain the challenges of regulatory frameworks and public acceptance in a CCS/CCUS project Identify potential risks of a CCS/CCUS project Outline the risk assessment and management process Target Audience This VILT course is ideally suited for a technical audience - geoscientists, petroleum and chemical engineers - as well as for economists, regulators, legal staff and managers wishing to learn more about the details of both the technical, regulatory and socio-economic aspects of carbon capture and storage. Participants should have: Experience with oil and gas, coal or other energy projects Basic understanding of the energy industry Course Level Intermediate Trainer Your first expert course leader spent 18 years in the Petroleum Industry before joining academia, in both technical and managerial roles with Shell, Arco and Vico. He has received numerous awards, including Distinguished Service, Honorary member and Special Commendation awards from the American Association of Petroleum Geologist (AAPG) and was AAPG's International Vice-President and recently chairman of AAPG's House of Delegates (the Associations Parliamentary body). He is an SPE Distinguished Lecturer (DL) and has served as DL for several other professional organisations, including, AAPG, IPA and PESA. He is currently a Professor of Petroleum Geology and Engineering at the Australian School of Petroleum, University of Adelaide. He holds the South Australia State Chair in Carbon Capture & Storage (CCS) and is also presently Distinguished Scientist of the Cooperative Research Centre for Greenhouse Gas Technologies (CO2CRC), having served earlier as the Storage Program Manager and Chief Scientist. Your second expert course leader has a wide and deep knowledge of major capture technologies: solvent, membrane and adsorption based technologies and has developed pathways for retrofitting CO2 capture and storage (CCS) to fossil fuel-based power plants. He has been actively engaged in Post-combustion capture project management and demonstration projects in Victoria's Latrobe Valley on CO2 capture and hydrogen production, and on CO2 capture using membrane contactor technology. He has led various feasibility studies for the Asian Development Bank on CO2 Capture at Indian Oil Corporation's refineries, for JPOWER on hydrogen production from Victorian brown coal and for Kawasaki on incorporation of CCS in hydrogen production from fossil fuel. He has authored multiple peer reviewed journal articles, co-authored various confidential reports on CO2 capture, utilization and hydrogen production and utility, and has presented his work at various conferences, symposiums and seminars. He has a PhD in Chemical Engineering from Monash University Australia and a Master of Technology in Process Engineering from Indian Institute of Technology Delhi India. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations