- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
How to achieve a successful return to work
By Pamela Rose - Fatigue Coach
If you’ve had to take time off from your job for months or even years, contemplating a return to work can be difficult. How do you know if you’re ready? Are you well enough to return full-time or do you need to negotiate a phased approach? And what can you do to make sure the return itself goes as successfully as possible? This webinar starts to answer those questions - and many more! Content If you’ve had to take time off from your job for months or even years, contemplating a return to work can be difficult. How do you know if you’re ready? Are you well enough to return full-time or do you need to negotiate a phased approach? And what can you do to make sure the return itself goes as successfully as possible? I’ve helped many people in your situation find the right way to tackle their return to work, guiding them as they gauged if they were ready - and then advising them as to the best way to start approaching things with their employer. I very much enjoy helping my clients with this stage of their recovery journey, as it means things are going really well for them!I share so much value in this session! I've taken my experience of helping many, many people navigate this milestone and turned my best advice into a single session for you to benefit from.The event itself was a live webinar held in July 2023. This is your chance to purchase the recording of the webinar itself (1 hour)) and a written capture of the Q&A sessions held afterwards. My full client schedule means I won't be running this as a live event again for a while, so this is your chance to purchase it 'on demand' and benefit from the help I give at the time you need it (now!).Topics coveredHaving helped so many people, I’ve seen how successfully things go when certain elements are carefully thought through and put into place, and I share my Top Five pieces of advice with you at this live webinar. I talk about: How to know if/when you’re ready to start seriously considering a return to work Questions to ask yourself if you think you need to consider a change of career How to broach the topic of a phased return with your employer My experience of how Occupational Health (or similar functions) can help or hinder - and how to make sure it’s the former! Things to consider and address up-front to ensure your first couple of weeks go as well as they can. I also share some smart actions that you can put in place way before you're even contemplating going back to work, in order to smooth the way for a successful return when you're ready. So please don't think this webinar won't be useful to you if you know you've got a way to go yet. Not only will you be able to put these smart early actions in place, you'll also have a much clearer idea about how you'll manage your return when you're ready - helping you feel more confident and reduce any concerns sneaking in. You'll be able to relax knowing you'll be able to tackle things properly when the time's right.Please note that although the guidance and tips I give are not restricted to those who have office-based jobs, many of the examples I use are linked to office-based scenarios. This is because it's usually the case that the majority of attendees are indeed office-based (or similar). Please be assured that the majority of the tips I give can be refined and tailored to returning to any type of job.Although best known for the help I give to those experiencing extreme fatigue conditions such as ME/CFS, fibromyalgia and long covid, this session is relevant to anyone contemplating a return to work after an extended period of sick leave. Especially if you feel you'll need to negotiate a phased return. For example, after being diagnosed with an autoimmune condition, recovering from a major operation, or perhaps having completed a successful programme of cancer treatment.Please don't assume that the low price of this product in any way reflects a lack of valuable content. I could have priced it much higher, but I'm keen to help as many people as possible navigate this important milestone.
Utilize Facebook Ads for Marketing Mastery
By Compete High
ð Unlock the Power of Facebook Ads for Unstoppable Marketing Success! ð¯ Are you ready to take your marketing strategies to the next level and harness the immense potential of Facebook Ads? Look no further! Introducing our comprehensive online course: 'Utilize Facebook Ads for Marketing Mastery.' ð¥ Why Choose This Course? With over 2.8 billion active users, Facebook offers an unparalleled platform for reaching your target audience. This course is your definitive guide to leveraging Facebook Ads effectively, whether you're a novice or an experienced marketer looking to refine your skills. ð¡ What You'll Learn: â Step-by-step guidance on setting up and optimizing Facebook Ad campaigns. â Strategies to identify and target your ideal audience for maximum engagement and conversions. â Advanced tactics to create compelling ad creatives that captivate and convert. â Techniques to analyze metrics and fine-tune your ads for exceptional ROI. â Proven methods to scale your campaigns and skyrocket your business growth. ð Course Highlights: ð Expert-led modules designed for all levels of expertise. ð Real-world case studies and practical examples for hands-on learning. ð¬ Interactive Q&A sessions to address your specific queries. ð Insider tips and industry secrets shared by seasoned marketing professionals. ð Certification upon completion to showcase your expertise. ð Join thousands of successful marketers who have transformed their businesses using our actionable strategies and unparalleled insights. ð¢ Limited Time Offer: Enroll now to secure your spot and embark on your journey toward mastering Facebook Ads for unparalleled marketing success! ð Don't miss out! Seize this opportunity to dominate the digital landscape with targeted, high-converting Facebook Ads. Enroll today and watch your business soar to new heights! [Enroll Now Button] ð Visit our website for more information and testimonials from our thriving community of successful marketers. Let's elevate your marketing game together! Course Curriculum Module 1-Thank You For Enrolling! How Is The Class Setup For Your Maximum Return Thank You For Enrolling! How Is The Class Setup For Your Maximum Return 00:00 Module 2-Best Facebook Marketing Strategy For 2017 Best Facebook Marketing Strategy For 2017 00:00 Module 3-Best Easy Facebook Marketing Strategy For 2017 Best Easy Facebook Marketing Strategy For 2017 00:00 Module 4-Best Facebook Messaging Strategy For 2017 Best Facebook Messaging Strategy For 2017 00:00 module 5-Within 5 Minutes, Positive Replies Come Back Within 5 Minutes, Positive Replies Come Back 00:00 Module 6-The Best Facebook Marketing Happens With My Profile The Best Facebook Marketing Happens With My Profile 00:00 Module 7-Facebook Groups Are Powerful For Networking And Learning Facebook Groups Are Powerful For Networking And Learning 00:00 Module 8-What Works Best For Marketing With Facebook Pages What Works Best For Marketing With Facebook Pages 00:00 Module 9-Facebook Page Insights Tutorial Facebook Page Insights Tutorial 00:00 Module 10-Facebook Page Post Creation Tutorial Facebook Page Post Creation Tutorial 00:00 Module 11-Facebook Page Profile Picture And Cover Photo Creation Facebook Page Profile Picture And Cover Photo Creation 00:00 Module 12-Facebook Page Profile Picture And Cover Photo Creation Facebook Page Profile Picture And Cover Photo Creation 00:00 Module 13-Start Learning About Facebook Ads Here Start Learning About Facebook Ads Here 00:00 Module 14-The Best Facebook Ad I Ever Created On 10,000 Tested The Best Facebook Ad I Ever Created On 10,000 Tested 00:00 Module 15-Scaling Up The Best Facebook Ad I Ever Created Scaling Up The Best Facebook Ad I Ever Created 00:00 Module 16-How I Analyze And Improve My Ads Over Time How I Analyze And Improve My Ads Over Time 00:00 Module 17-Getting A Facebook Ad Mainstream And Expanding Targeting Getting A Facebook Ad Mainstream And Expanding Targeting 00:00 Module 18-Making An Ideal Offer For Facebook Ads Making An Ideal Offer For Facebook Ads 00:00 Module 19-Facebook Ads Tutorial From August 2016 Facebook Ads Tutorial From August 2016 00:00 Module 20-Facebook Ads Power Editor Tutorial Draft Lesson 00:00 Module-21 Boosting A Post With A Page Post Engagement Ad Boosting A Post With A Page Post Engagement Ad 00:00 Module 22-Why I Took A Month Off Of Advertising On Facebook Why I Took A Month Off Of Advertising On Facebook 00:00 Module 23-The Benefits Of Taking A Break From Facebook Ads The Benefits Of Taking A Break From Facebook Ads 00:00 Module 24-The Best I Can Do Is Make A Business I Would Enjoy Working With As A Customer The Best I Can Do Is Make A Business I Would Enjoy Working With As A Customer 00:00 Module 25-7.2 Million Views On My Most Viral Video On Facebook 7.2 Million Views On My Most Viral Video On Facebook 00:00 Module 26-Give And Take On Facebook Give And Take On Facebook 00:00 Module 27-Live Questions And Answers About Facebook, Youtube, And Working Online Live Questions And Answers About Facebook, Youtube, And Working Online 00:00 Module 28-Start Listening To My Facebook Marketing And Advertising Audio Lectures Here Start Listening To My Facebook Marketing And Advertising Audio Lectures Here 00:00 Module 29-Starting With Why! Starting With Why! 00:00 Module 30-Understand How You Act As A User And You Will See What You Can Do As A Giver! Understand How You Act As A User And You Will See What You Can Do As A Giver! 00:00 Module-31 All Feedback Received Is Helpful! All Feedback Received Is Helpful! 00:00 Module 32-What Works On You Might Work On Others! What Works On You Might Work On Others! 00:00 Module 33-What Is Working The Very Best Today For Me On Facebook What Is Working The Very Best Today For Me On Facebook 00:00 Module 34-Lipstick On A Pig! Lipstick On A Pig! 00:00 Module 35-Case Study With A Shop Owner Case Study With A Shop Owner 00:00 Module 36-What Is The Most Powerful Way To Use Facebook For Getting Organic Reach What Is The Most Powerful Way To Use Facebook For Getting Organic Reach 00:00 Module 37-Video Is The Most Powerful Form Of Communication Online Today Video Is The Most Powerful Form Of Communication Online Today 00:00 Module 38-How To Make Magnificent Videos On Facebook! How To Make Magnificent Videos On Facebook! 00:00 Module 39-The Power Of Producing Videos Daily! The Power Of Producing Videos Daily! 00:00 Module 40-How Easy Is It To Start Making Videos On Facebook How Easy Is It To Start Making Videos On Facebook 00:00 Module 41-Branding On Facebook Branding On Facebook 00:00 Home 42-The Importance Of Knowing Exactly Who The Potential Client Is The Importance Of Knowing Exactly Who The Potential Client Is 00:00 Module 43-Personal Facebook Profiles Have Amazing Power! Personal Facebook Profiles Have Amazing Power! 00:00 Module 44-My Personal Profile Helped Me Start And Grow My Business First My Personal Profile Helped Me Start And Grow My Business First 00:00 Module 45-Working At The Right Pace Working At The Right Pace 00:00 M0dule 46-How To Know If I Am Working On The Right Pace! How To Know If I Am Working On The Right Pace! 00:00 Module 47-Facebook Groups Are The Easiest Way To Reach The Newsfeed Facebook Groups Are The Easiest Way To Reach The Newsfeed 00:00 Module 48-Facebook Groups Help Make Personal Connections And Are Great For Learning! Facebook Groups Help Make Personal Connections And Are Great For Learning! 00:00 Module 49-Facebook Pages And Advertising Explained Facebook Pages And Advertising Explained 00:00 Module 50-Your First Facebook Page Likes Should Be Friends And Family Your First Facebook Page Likes Should Be Friends And Family 00:00 Module 51-My Ideal Facebook Marketing And Advertising Strategy My Ideal Facebook Marketing And Advertising Strategy 00:00 Module 52-Daily Progress Rather Than Perfection! Daily Progress Rather Than Perfection! 00:00 Module 53-Alternatives To Making Videos Alternatives To Making Videos 00:00 Module 54-The Best Tips And Tricks I Know For Facebook The Best Tips And Tricks I Know For Facebook 00:00

How to start exercising when you have fatigue
By Pamela Rose - Fatigue Coach
We hear how helpful it is to exercise regularly for health and wellbeing. But when you have fatigue it can be difficult to know if this is going to help or hinder. And suspecting it could be the latter, then when is it the right time to start to feel confident about moving more...and gradually starting to exercise? How this webinar will help you I've helped hundreds of people to navigate this element of their recovery journey and I've used this experience to share in this webinar the most successful ways to plan for, and introduce, movement and exercise. Who is this webinar for? Anyone who thinks they might be nearing a stage where exercise could well be possible again and are keen to ensure it goes well! Whether the goal be to walk, swim, cycle etc. Please note: This event isn't about how to re-condition and move from severe fatigue to achieving some level of activity. That requires careful 1:1 guidance via my coaching service. This webinar is for those who have a base level of activity but want to be smart about where to build from there. My help is relevant to anyone tackling a fatigue recovery journey - whether that be due to ME/CFS, Long Covid etc, or perhaps post-operative recovery. Basically, anyone who has - or has had - an energy-related issue that's meant they have to be very careful about what they commit to doing each day. What topics do you cover? How to spot when you're doing well enough to start thinking about exercising again How to feel confident about starting to do more The types of exercise that seem to go well at first Guidance and tips about HOW to start incorporating exercising into your recovery plan This is a recording of a live webinar that I held a short time ago. After the main presentation we held a Q&A session, and by purchasing this recording you'll also have access to a written capture of the questions asked, and my responses. Contents The webinar recording In this 49 minute video, hear me give advice and tips on how to tackle these tricky communication situations: Communicating your situation to those you live with/are close to - in a way that goes well, and doesn't negatively impact your health/symptoms How to talk to people who are 'helpfully' trying to tell you how to cure yourself (when you know it's wrong!) Socialising with friends when you have fatigue Navigating conversations at large events (weddings, parties etc) How to talk to people who don't understand fatigue (or even believe in it) How to start exercising webinar.mp4 48 mins104 MB A copy of the slides I presented How to start exercising with fatigue.pdf 1.38 MB The Q&A digest This is a written capture of the Q&A discussion, held after my main presentation. I didn't record the Q&A in order to allow those who attended live to feel comfortable switching their cameras on and participating in the discussion. I hope you find this written summary helpful. How to start exercising when you have fatigue.pdf 147 KB
When a Loved One has fatigue...how to help them, and yourself.
By Pamela Rose - Fatigue Coach
A fatigue-related condition doesn’t only impact the life of the person who's ill, it often changes things for you, their loved ones. Adjusting to this can be tough for you, and it can be difficult to know how to best help them.This webinar will increase your understanding of what life feels like for your loved one, and help you know how to support them on their recovery journey, while looking after yourself too. Why can this help me? The person you love and care for is still there, they just can’t live the life they used to be able to live - not for now, anyway. It’s very possible for them to achieve improvements and even full recovery, but it takes time, patience and a lot of adjustment. One of the most important things someone with extreme fatigue must do is reprioritise what they use their valuable energy on. They have to make sensible decisions around what they should do every single day, and that’s bound to impact you too. They might also experience emotional ups and downs that you’re not used to them displaying. Adjusting to this can be tough for those of you who are supporting them, as can knowing how you can best help them. This webinar will help you process how this is affecting your life too, and give you guidance around how to best support your loved one on their recovery journey, while looking after yourself too. Contents A quick introduction!Loved ones intro.mov 2 mins 140 MB The webinar recordingvideo1931976197.mp4 51 mins 74.3 MB The Q&A digestA written capture of our Question & Answer discussion.Q&A capture from 2310.pdf 207 KB A copy of the slides I presentedLoved ones_slides1023.pdf 1.35 MB A final thought from me...loved ones outro.mov 4 mins228 MB
Web Development Intermediate Level is one of our best selling and most popular course. The Web Development Intermediate Level is organised into 3 modules and includes everything you need to become successful in this profession. To make this course more accessible for you, we have designed it for both part-time and full-time students. You can study at your own pace or become an expert in just 34 hours! If you require support, our experienced tutors are always available to help you throughout the comprehensive syllabus of this course and answer all your queries through email. Why choose this course Earn an e-certificate upon successful completion. Accessible, informative modules taught by expert instructors Study in your own time, at your own pace, through your computer tablet or mobile device Benefit from instant feedback through mock exams and multiple-choice assessments Get 24/7 help or advice from our email and live chat teams Full Tutor Support on Weekdays Course Design The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of Video lessons Online study materials Mock exams Multiple-choice assessment Certification After the successful completion of the final assessment, you will receive a CPD-accredited certificate of achievement. The PDF certificate is for £9.99, and it will be sent to you immediately after through e-mail. You can get the hard copy for £15.99, which will reach your doorsteps by post. Who is this course for? Web Development Intermediate Level is suitable for anyone who want to gain extensive knowledge, potential experience and professional skills in the related field. This is a great opportunity for all student from any academic backgrounds to learn more on this subject.

HVAC (Heat, Ventilation & Air Conditioning) Technician & Operator Training
By Compete High
🔥 Ready to launch your career in HVAC (Heat, Ventilation & Air Conditioning)? Learn how to install, maintain, and troubleshoot HVAC systems with our expert-led online training! 🎓

Dog Grooming Training
By Compete High
🐶✨ Ready to master the art of Dog Grooming? Whether you're a pet owner or an aspiring professional, our Dog Grooming Training Course will teach you essential grooming techniques, health and safety tips, and breed-specific styles—all at your own pace! 🛁✂️🐾

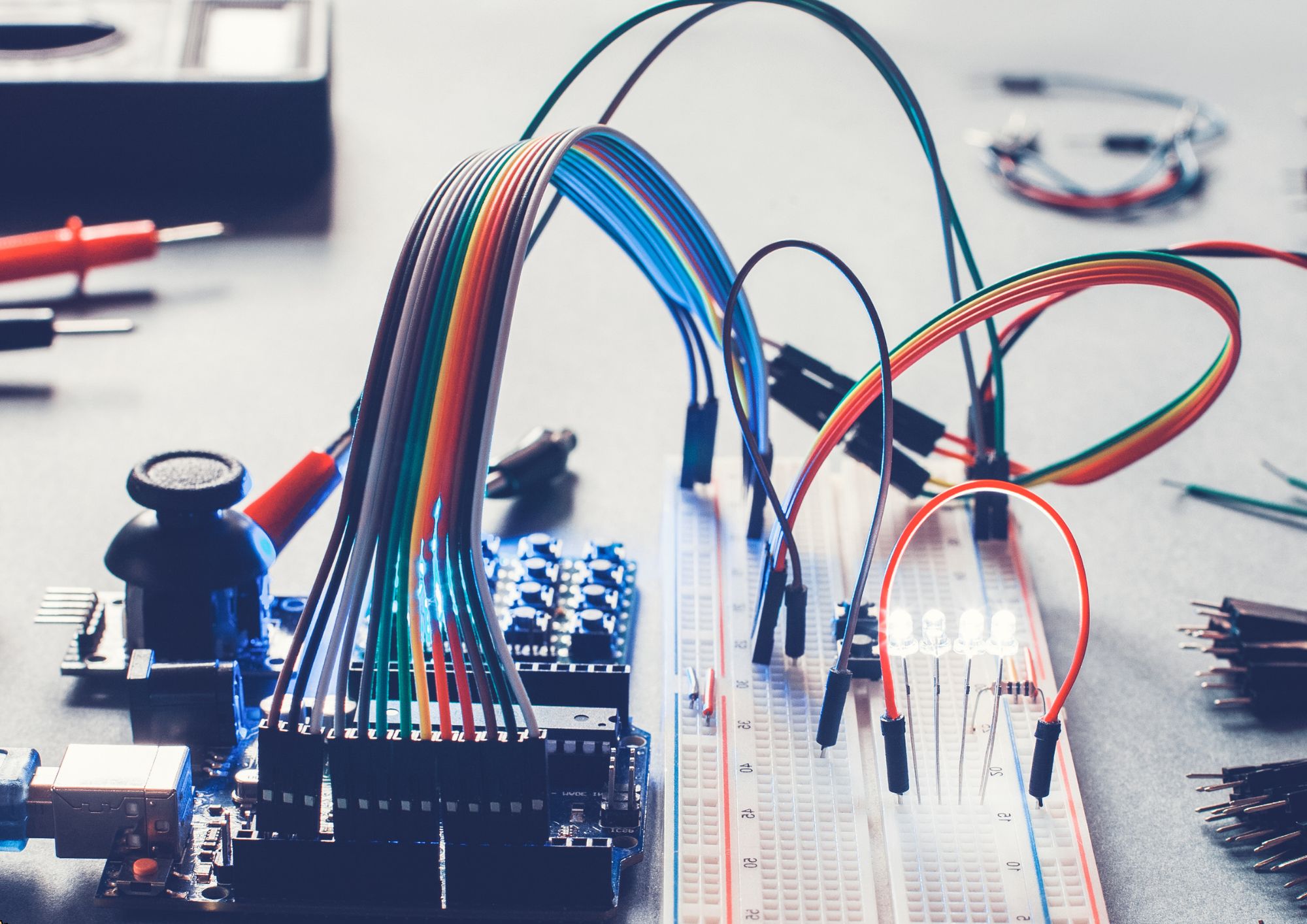
Diploma in Electrical Engineering
By Compete High
Boost your career with our Diploma in Electrical Engineering! ⚡ This self-paced online course covers essential topics like circuits, electrical machines, and power systems, helping you gain industry-relevant skills and a certificate of completion. Enrol today and take the next step in your Electrical Engineering journey! 🔌📚
Electrical Safety Management
By Compete High
This Electrical Safety Management Training provides job-ready skills, expert insights, and a certification that helps you establish a safe and compliant working environment. Enrol now and take control of electrical safety in your workplace! 🚀

Impact of Domestic Abuse in the Workplace (Silver Standard)
By Safe Space Consultancy
Creating safer, more aware workplaces through expert-led training covering domestic abuse, stalking, sexual harassment and safeguarding. Silver Package - CPD Accredited Our Silver Package offers a comprehensive, full-day training programme designed to equip your team with the essential knowledge and tools to address domestic abuse in the workplace. This package includes: Whole-Day Training 4 Seminars delivered in one full day or in flexible segments - comprising four expert-led seminars Topics covered: Understanding Domestic Abuse in the Workplace Understand the definitions, forms, and prevalence of domestic abuse and its direct and indirect impact on the workplace. Developing and Implementing Domestic Abuse Policies & Procedures Guidance on developing and embedding clear, effective domestic abuse policies aligned with best practice and legal responsibilities. Recognising the Signs of Abuse Guidance on developing and embedding clear, effective domestic abuse policies aligned with best practice and legal responsibilities. How to Support an Employee Build skills in approaching sensitive conversations, offering support without judgement, and connecting individuals to appropriate help. Ongoing Support – Up to 6 hours of tailored support spread over a 6-month period to help with policy implementation, staff queries, or further guidance. There are 5 CPD Credits awarded with this course. Certificates will be issued upon completion. This package is ideal for organisations seeking to build a safer, more supportive workplace culture. Please contact julie@safespaceconsultancy.org for further information or to access a FREE 30 Minute Consultation
