- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
37194 Design courses in Mountsorrel delivered Online
Have you ever wondered how young minds blossom? Imagine nurturing that curiosity and igniting a lifelong love of learning. The Early Years Primary Teaching course equips you with the skills to become an Early Years Practitioner (EYP), shaping the future generation. Explore the EYFS framework, discover effective teaching methods, and gain the knowledge to navigate the world of primary education. This course is your springboard to a rewarding career filled with laughter, discovery, and the joy of making a difference. Learning Outcomes Gain a comprehensive understanding of the Early Years Foundation Stage framework and its role in child development. Develop a toolkit of engaging teaching techniques specifically designed for young learners. Explore the various types of schools in the UK and the unique needs of each environment. Master the fundamentals of teaching core subjects like English, mathematics, and science in the primary years. Build the confidence to support children with special educational needs or disabilities (SEND). Why buy this Early Years Primary Teaching? Unlimited access to the course for a lifetime. Opportunity to earn a certificate accredited by the CPD Quality Standards and CIQ after completing this course. Structured lesson planning in line with industry standards. Immerse yourself in innovative and captivating course materials and activities. Assessments designed to evaluate advanced cognitive abilities and skill proficiency. Flexibility to complete the Course at your own pace, on your own schedule. Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience. Unlock career resources for CV improvement, interview readiness, and job success. Certification After studying the course materials of the Early Years Primary Teaching there will be a written assignment test which you can take either during or at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £5.99. Original Hard Copy certificates need to be ordered at an additional cost of £9.60. Who is this course for? Individuals with a passion for early childhood education Those seeking a fulfilling career change Anyone considering a postgraduate qualification in Initial Teacher Training (ITT) Early Years professionals looking to enhance their skillset Individuals aiming to secure rewarding primary teaching jobs Prerequisites This Early Years Primary Teaching does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Early Years Primary Teaching was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Career path Early Years Practitioner (EYP): £24,000 - £30,000 Per Annum Primary School Teacher: £25,714 - £41,778 Per Annum Teaching Assistant: £20,000 - £28,000 Per Annum Special Educational Needs Coordinator (SENCO): £38,000 - £56,000 Per Annum Educational Psychologist: £40,000 - £70,000 Per Annum Headteacher: £60,000 - £100,000 Per Annum Course Curriculum Module 01: Primary Education in the UK Primary Education in the UK 00:17:00 Module 02: Responsibilities, Qualifications and Skills Responsibilities, Qualifications and Skills 00:16:00 Module 03: Initial Teacher Training Initial Teacher Training 00:23:00 Module 04: Types of Schools in the UK Types of Schools in the UK 00:15:00 Module 05: Importance of Early Years in Development Importance of Early Years in Development 00:19:00 Module 06: EYFS Teaching Techniques EYFS Teaching Techniques 00:14:00 Module 07: Child Development Child Development 00:13:00 Module 08: Teaching Primary English Teaching Primary English 00:23:00 Module 09: Teaching Primary Mathematics Teaching Primary Mathematics 00:37:00 Module 10: Teaching Primary Science, Design and Technology Teaching Primary Science, Design and Technology 00:30:00 Module 11: Teaching Other Primary Subjects Teaching Other Primary Subjects 00:28:00 Module 12: Children Having Special Education Needs or Disabilities Children Having Special Education Needs or Disabilities 00:16:00 Module 13: EYFS Framework EYFS Framework 00:12:00 Module 14: Self-Management and Dealing with Stress Self-Management and Dealing with Stress 00:15:00 Assignment Assignment - Early Years Primary Teaching 00:00:00 Recommended Materials Workbook - Early Years Primary Teaching 00:00:00

ITIL 4 Strategist: Direct, Plan and Improve: In-House Training
By IIL Europe Ltd
ITIL® 4 Strategist: Direct, Plan and Improve: In-House Training The ITIL® 4 Strategist: Direct, Plan, and Improve course is based on the ITIL® 4 Strategist Direct, Plan, and Improve candidate syllabus from AXELOS. This course is based on the ITIL® 4 Strategist: Direct, Plan and Improve IT exam specifications from AXELOS. With the help of ITIL® 4 concepts and terminology, exercises, and examples included in the course, candidates acquire the relevant knowledge required to pass the certification exam. This course provides the practical skills necessary to create a 'learning and improving' IT organization, with a strong and effective strategic direction. It was designed to provide practitioners with a practical and strategic method for planning and delivering continual improvement with necessary agility. It covers both practical and strategic elements, making it the universal module that is a key component to both ITIL® 4 Managing Professional and ITIL® 4 Strategic Leader streams. What You Will Learn At the end of this course, participants will be able to: Understand the key concepts of direction, planning, improvement Understand the scope of what is to be directed and/or planned and know how to use key principles and methods of direction and planning in that context Understand the role of GRC and know how to integrate the principles and methods into the service value system Understand and know how to use the key principles and methods of continual improvement for all types of improvements Understand and know how to use the key principles and methods of Communication and Organizational Change Management to direction, planning and improvement Understand and know how to use the key principles and methods of measurement and reporting in direction, planning, and improvement Understand and know how to direct, plan, and improve value streams and practices Course Introduction Let's Get to Know Each Other Course Overview ITIL® 4 Certification Scheme Course Learning Objectives Course Components Course Agenda Exercises Case Study: Axle Car Hire Case Study: HandyPerson on Demand Exam Details Core Concepts of DPI Key Terms Covered in the Module Module Learning Objectives Basics of Direction Basics of Planning Basics of Improvement Other Core Elements DPI through Service Value Chain and Guiding Principles Key Terms Covered in the Module Module Learning Objectives DPI of the SVS DPI of Guiding Principles Role of Direction in Strategy Management Key Terms Covered in the Module Introducing Strategy Management Developing Effective Strategies Implementation of Strategies Key Terms Covered in the Module Module Learning Objectives Managing Risks Making Decisions through Portfolio Management Directing via Governance, Risk, and Compliance (GRC) Introduction to Assessment and Planning Key Terms Covered in the Module Module Learning Objectives Core Concepts of Assessment Conducting Effective Assessments Core Concepts of Planning Assessment and Planning through VSM Key Terms Covered in the Module Module Learning Objectives Introducing VSM Developing Value Stream Maps Knowing More About VSM Measurement, Reporting, and Continual Improvement Key Terms Covered in the Module Module Learning Objectives Measurement and Reporting Alignment of Measurements and Metrics Success Factors and Key Performance Indicators Continual Improvement Measurements and Continual Improvement through Dimensions and SVS Key Terms Covered in the Module Module Learning Objectives Measurements for the Four Dimensions Continual Improvement of the Service Value Chain and Practices OCM Principles and Methods Key Terms Covered in the Module Module Learning Objectives Basics of OCM OCM throughout DPI and Service Value Chain Resistance and Reinforcement Communication Principles and Methods Key Terms Covered in the Module Module Learning Objectives Basics of Effective Communication Communication with Stakeholders SVS Development Using Four Dimensions Key Terms Covered in the Module Module Learning Objectives Organizations and People in the SVS Partners and Suppliers in the SVS Value Streams and Processes in the SVS Information and Technology in the SVS

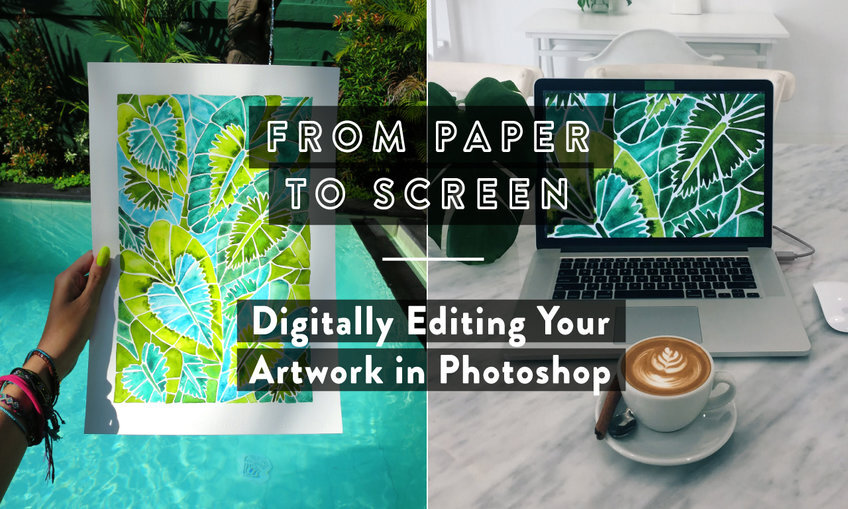
From Paper to Screen: Digitally Editing Your Artwork in Photoshop
By iStudy UK
Learn how to digitally transform your artwork and take your most coveted designs from screen to paper under the guidance of expert artist and designer Cat Coquillette. With years of experience behind her and a portfolio of stunning illustrations, Cat will take you step-by-step through the full process, including how to fuse multiple scans of artwork into one image and remove the paper background. You will gain the most in-demand creative editing skills, exploring colour variations, patterns, templates and advanced enhancement techniques to turn your artwork into instant high-res best-sellers. Turn your passion into a passive income business today and start selling your pieces online in no time! Course Highlights From Paper to Screen: Digitally Editing Your Artwork in Photoshop is an award-winning and best-selling course that has been awarded CPD Certification & IAO accreditation. It is the most suitable course for anyone looking to work in this field or relevant sector. This training program is considered one of the top-trending courses in the UK, helping students to familiarise with the topic and gain the necessary skills to perform well in this field. We have organised the course into several specific modules, teaching you everything you need to become successful in this profession. To provide you with ease of access, this course is designed for both part-time and full-time students. You can become accredited in just 20/30 hours, with the freedom to study at your own pace. We have experienced tutors who will help you throughout the comprehensive syllabus of this course and answer all your queries through email. For further clarification, you will be able to recognise your qualification by checking the validity from our dedicated website. Why You Should Choose the From Paper to Screen Course Lifetime access to the course No hidden fees or exam charges CPD Accredited certification on successful completion Full Tutor support on weekdays (Monday - Friday) Efficient exam system, assessment and instant results Download Printable PDF certificate immediately after completion Obtain the original print copy of your certificate, dispatched the next working day for as little as £9. Improve your earning potential and secure a successful career in your chosen field. Who is this Course for? The From Paper to Screen: Digitally Editing Your Artwork in Photoshop course is CPD certified and IAO accredited. This makes it perfect for anyone trying to learn potential professional skills. As there is no experience and qualification required for this course, it is available for all students from any academic backgrounds. Requirements Our From Paper to Screen: Digitally Editing Your Artwork in Photoshop course is fully compatible with any kind of device. Whether you are using a Windows computer, Mac, smartphone or tablet, you will get the same experience while learning. Besides that, you will be able to access the course with any kind of internet connection from anywhere at any time, without any kind of limitation. Career Path On successful completion, you will be ready to enter the relevant job market and will have the necessary knowledge and skills required to carve a successful career in this sector. All our Diplomas are CPD and IAO accredited and can be added to your CV/resume to ensure you will stand out in the crowd and to prospective employers. Artwork in Photoshop 1. Intro FREE 00:03:00 2. Scanning Your Artwork 00:02:00 3. Cleaning Up Your Work in Photoshop 00:16:00 4. Color Exploration - Digitally Editing in Photoshop 00:07:00 5. Creating Patterns 00:11:00 6. Resizing for Various Template Dimensions 00:04:00 7. Final Tips 00:01:00 DigitalGuide-CatCoq 00:05:00
The Node JS: API Development with Swagger Interface Description Language course provides comprehensive training in creating APIs using Node.js and Swagger Interface Description Language. Participants will learn to develop robust APIs, design API specifications using Swagger, handle authentication, and implement API security. This course offers practical insights into building efficient APIs for web applications. Learning Outcomes: Understand the fundamentals of API development and its significance in web applications. Learn to set up and configure Node.js for building APIs. Explore the Swagger Interface Description Language for designing API specifications. Develop RESTful APIs using Node.js and Swagger for effective communication between applications. Implement authentication mechanisms and secure APIs using JWT (JSON Web Tokens). Master error handling and validation techniques for ensuring reliable API performance. Gain insights into API documentation and automatic generation using Swagger tools. Create interactive API documentation and test APIs using Swagger UI. Why buy this Node JS: API Development with Swagger Interface Description Language? Unlimited access to the course for forever Digital Certificate, Transcript, student ID all included in the price Absolutely no hidden fees Directly receive CPD accredited qualifications after course completion Receive one to one assistance on every weekday from professionals Immediately receive the PDF certificate after passing Receive the original copies of your certificate and transcript on the next working day Easily learn the skills and knowledge from the comfort of your home Certification After studying the course materials of the Node JS: API Development with Swagger Interface Description Language there will be a written assignment test which you can take either during or at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £5.99. Original Hard Copy certificates need to be ordered at an additional cost of £9.60. Who is this course for? Web developers interested in enhancing their API development skills. Node.js enthusiasts looking to build efficient and secure APIs. Backend developers aiming to understand Swagger for API specification. Software engineers seeking to master API authentication and security. Professionals wanting to improve their web application development knowledge. Prerequisites This Node JS: API Development with Swagger Interface Description Language does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Node JS: API Development with Swagger Interface Description Language was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Career path Node.js Developer: Specialize in building web applications using Node.js and APIs. Backend Developer: Design and implement APIs to support various web applications. API Developer: Develop, maintain, and optimize APIs for seamless data exchange. Web Application Developer: Create robust and efficient web applications using APIs. Software Engineer: Leverage API development skills for software product development. Course Curriculum Unit 01: Course Introduction Module 01: Introduction 00:01:00 Module 02: Goals & Prerequisites 00:03:00 Module 03: About the Instructor 00:01:00 Module 04: Open API Specification (OAS), Swagger & Node.js 00:09:00 Unit 02: Introduction to Swagger Module 01: Http and Swagger 00:09:00 Module 02: Swagger Tools 00:06:00 Module 03: Setup 00:06:00 Unit 03: Open API Specification (OAS) Module 01: Project Configuration 00:08:00 Module 02: Intro to Swagger Editor 00:06:00 Module 03: Project Explanation + GET Endpoint 00:13:00 Module 04: POST Endpoint 00:06:00 Module 05: PUT + DELETE Endpoint 00:08:00 Module 06: Challenge: Comments Endpoints 00:17:00 Unit 04: Node.js & Swagger Module 01: Get 00:11:00 Module 02: Post 00:08:00 Module 03: Put 00:07:00 Module 04: Delete 00:06:00 Module 05: Challenge: Add comment logic 00:18:00 Module 06: Deploy API in Heroku 00:06:00 Unit 05: Swagger Authorization with Json Web Tokens Module 01: Introduction to Json Web Tokens 00:07:00 Module 02: Authentication with Swagger and JWT 00:07:00 Unit 06: Final words Module 01: Thank you! 00:01:00 Assignment Assignment - Node JS: API Development with Swagger Interface Description Language 00:00:00

CILT (UK) Level 5 Professional Diploma in Logistics and Transport
By The Business School (UK) Ltd
The CILT(UK) Level 5 Professional Diploma in Logistics and Transport (QCF) is designed to enhance new and existing expertise in the supply chain, passenger transport, road freight or transport planning environments as well as developing core management skills.

Data Protection in the Workplace
By OnlineCoursesLearning.com
This course gives an exhaustive outline of information insurance necessities in the working environment. The course starts by giving an overall outline of information assurance. Like its advantages, and key realities about the Data Protection Act. The course additionally turns out how to assemble an information security strategy for your organization just as telling you how to react to data demands. Information insurance is a vital part of pretty much every working environment. Most organizations have some close to home information or touchy information with respect to every last one of their clients and representatives. Figuring out how to make a powerful information assurance strategy just as the accepted procedures you should utilize when managing private information is the most ideal approach to guarantee consistence with the Data Protection Act. What's Covered in the Course? Data about the Data Protection Act, including the rights stood to people and the duties presented onto associations The conditions that are joined to the social occasion, preparing, and support of information What is expected of your organization on the off chance that you need to impart information to different branches in your association The four fundamental parts of information security The most effective method to build up an ideal information assurance strategy that addresses your association's issues The means you should take to deal with demands for data from people Advantages of Taking This Course Finding out about the Data Protection Act and the advantages of consistence Acquiring knowledge into the rights stretched out to people under the Data Protection Act with respect to the treatment of their own and touchy information Understanding the commitments associations should meet on the off chance that they need to gather, use, and keep up close to home or touchy information Securing data about how to appropriately impart information to others inside your association without abusing the demonstration Acquiring significant data about the advancement of an extensive information security strategy Who can take the course? Any individual who has a premium in becoming familiar with this topic is urged to take the course. There are no passage necessities to take the course. What is the design of the course? The course is separated into 6 individual modules. Every module takes somewhere in the range of 5 and an hour on normal to consider. In spite of the fact that you are allowed to spend so a lot or as brief period as you feel vital on every module, essentially sign all through the course whenever it might suit you. Where/when would i be able to contemplate the course? You can consider the course any time you like. Just sign all through the online course as frequently as you require. The course is viable with all PCs, tablet gadgets and advanced mobile phones so you can even investigation while moving! Is there a test toward the finish of the course? Whenever you have finished all modules there is a various decision test. The inquiries will be on a scope of subjects found inside the modules. The test, similar to the course, is on the web and can be taken a period and area based on your personal preference. What is the finish mark for the last assessment? The breeze through mark for the assessment is 70%. On the off chance that you don't finish the assessment first time you will get further freedoms to step through the exam again after additional examination. There are no restrictions to the occasions you can step through the exam. All test retakes are incorporated inside the cost of the course. When will I get my endorsement? Whenever you have finished your test you can sign in to your record and download/print your endorsement any time you need it. What amount of time does it require to finish the course? We gauge that the course will require around 3 hours to finish altogether, in addition to an extra 30 minutes for the finish obviously test. Course Content Module 1: Benefits of Good Data Safety and the Data Protection Act Module 2: Conditions and Permissible Reasons to Access Data Module 3: The General Data Protection Regulation Module 4: Data Sharing and Security Module 5: Creating a Data Protection Policy Module 6: Managing Requests for Personal Data Course Detail Course Access: Lifetime Tests Included: Yes Similarity: All significant gadgets and programs

Gym Instructor Training: Building Fitness Programs for Clients (QLS Endorsed)
By Imperial Academy
Level 5 QLS Diploma Course | QLS Endorsed Certificate Included | 10 CPD Courses & PDF Certificates | 200 CPD Points

EPCIC Contract Drafting and Management: With Essential Elements of International Contract Laws
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course In turbulent times for the entire Energy Sector, Oil & Gas E & P segments are coming under tremendous pressure to reinvigorate. Oil Majors like Shell Plc are no longer termed as Oil & Gas Company but also branded as SHELL Energy, with technology at its forefront. The Risks, Scope and Context of Engineering, Procurement, Construction, Installation and Commissioning (EPCIC) Projects is evolving rapidly. Thus, the success of a project is dependent on the practical 'know how' in scoping, contract drafting, negotiation and execution competencies. Understanding the essential ingredients of contracts and mastering the international contracting principles will equip the participants to identify vague and ambiguous clauses, avoid dangerous and often hidden terms, and better understand the controlling position in a project. In this 3 full-day course, the participants will find out how to negotiate legacy contracts where parties are not allowed to edit any clauses during the bidding process. The participants will learn from the Case Law Reports and analysis to take home lessons learned from bitter experiences of their peers in the industry. It is designed to help those who need a solution to manage current contractual issues or those who execute contracts regularly and want to be more proficient in managing their contracts and projects, with changing contexts. The course is developed with the underlying objectives for the participants to: Enhance their current knowledge of the legal principles governing international Contracts from formation, execution to breaches, redresses and dispute resolution either as a party or as a consortium member or as a coverture. Manage Consortium and Joint Venture Partners inter-relationship and contractual responsibilities. Identify dangerous exposures due to joint and severally liable requirements of consortium-based contracts. Effectively Manage Risks of Projects, with Enforceable Contract Documents, by learning the purpose and potential benefits of maintaining evidence in compliance to the contract clauses. Learn the Contract Enforcement Nuggets of Owners and the Variation Claims Strategies of the Contractors. Allocation of contract management related roles / assignments and WBS within consortium partners for effective project management and profitable results. Use of Contract Terms & Conditions for enhancing project performance, monitoring, reporting, and achieving timely completion, thereby avoiding delays and disputes. This course can also be offered through Virtual Instructor Led Training (VILT) format. Training Objectives Upon completion of the course, the participants will have learnt: Project management strictly in accordance with the contract and the corporate strategies. How to ensure that Variations Order claims are appropriately managed in turnkey and lump-sum contracts. Manage contemporary challenges and market factors with direct or indirect impact on the contracts. Managing all members of the Supply Chain from vendors to logistics services providers. Cost Engineering and Performance Management. How to manage Consortium Partners, Contractors, and Owner's representatives. When and how to obtain / grant extension of time (EOT) and costs. Ability to identify rights and obligations of each party to a contract instead of making subjective decisions. Ability to be firm in negotiations without violating terms of the agreements. Ability to spot different legal systems, contract laws and arbitration rules. Ability to negotiate and avoidance of disputes and resolution in amicable manner, in accordance with the provisions of the contract. Competency in developing and maintaining documentary evidence and traceability for all works executed during the project. Target Audience This course is specially curated for professionals from International Oil & Gas Industries including Offshore & Marine Sectors. They include the heads of strategic business units, contracts managers, project directors, project managers, general managers, corporate legal counsels, procurements and supply chain managers, lawyers and legal professionals engaged in the EPCIC Segments of the Oil & Gas Industry. Course Level Intermediate Trainer Principal Management Consultant Chartered Valuer and Appraiser (CVA) FACICA | FAMTAC | FAIADR | M.S.I.D | Member, AIEN LL.M. (IP Law), M. Sc. (Maritime Studies), M. Tech (Knowledge Engineering), MBA, First Class CoC (MCA, UK), B. E. (Elect) Your expert course leader, during the last 47 year period, has worked and consulted in the industry verticals encompassing: Technology, Oil & Gas Exploration & Production, Petrochemical Process Plants and Power Plant Construction Projects, Logistics & Warehousing, Marine, Offshore, Oil & Gas Pipelines, Infrastructure Development Projects (Ports, Offshore Supply Bases, Oil & Gas Terminals and Airports etc), EPCIC Contracts, and Shipyards, in South East Asia, Africa, Middle East, Americas and Europe. He serves as the Principal Management Consultant with a management consultancy in Hong Kong and Singapore, specialising in the fields of corporate management consultancy, international contracts reviews and alternative dispute resolutions services. He undertakes special assignments for conducting audits and valuation of intangible properties involving proprietary processes for licensed production, and licensing of intellectual property rights (IP Rights) in patents, trademarks, and industrial designs. He is frequently engaged for assignments like due diligence, acquisitions, mergers, resolving various operational issues, technology transfer and agency services contracts reviews, cost controls, and enhancement of Supply Chain Management. He has been conferred the credentials of Chartered Valuer & Appraiser (CVA) by SAC and IVAS, in accordance with the international valuation standards setting body IVSC. His consulting experience includes Charterparty Management, Business Process Re-engineering, Diversifications, Corporate Development, Marketing, Complex Project Management, Feasibility Studies, Dispute Resolutions and Market Research. He has successfully assisted Marine and offshore E & P clients in managing contractual disputes arising from various international contracts for upgrading & conversion projects. He continues to be actively engaged in claims reviews, mediation, arbitration, litigation, and expert witness related assignments, arising from international contracts and Charterparty Agreements. He graduated with a Bachelor's degree in Electrical Engineering, MBA in General Management, Master of Technology in Knowledge Engineering, Master of Science in Maritime Studies, and LL.M. (IP Law). He also holds professional qualifications in Business Valuations and Appraisers for CVA, arbitration, law, and marine engineering, including the Chief Engineer's First-Class Certificate of Competency (MCA, UK). He is further qualified and accredited as Certified International Arbitrator, Chartered Arbitrator, Sports arbitrator under CAS Rules, WIPO Neutral, Australian Communications and Media Authority (ACMA) Bargaining Code Arbitrator, Accredited Adjudicator and Accredited Mediator (Malaysia). He is admitted to the international panels of arbitrators and neutrals with WIPO, Geneva; ACICA, AMTAC and ACMA, Australia; BVIAC (British Virgin Islands); JIAC (Jamaica); HKIAC Hong Kong; AIAC, Malaysia; AIADR, Malaysia; KCAB, Seoul, South Korea; ICA, Delhi, India; ICC (Singapore); SISV, Singapore; SCMA, Singapore; SCCA, Saudi Arabia; VIAC Vienna, Austria; Thailand Arbitration Centre (THAC), and Mediator with AIAC Malaysia, CMC, and SIMI Singapore. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

Natural Gas & LNG Sales Agreements
By EnergyEdge - Training for a Sustainable Energy Future
Enhance your knowledge of natural gas and LNG sales agreements with EnergyEdge course. Enroll now to gain valuable industry knowledge and skills.

Level 4 Logistics Management
By Training Tale
Do you want to start a career in Logistics Management? Are you interested in learning the Logistics management skills and knowledge needed for this role but do not know where to start? To expand your professional career, enrol in this Level 4 Logistics Management course right now. This Level 4 Logistics Management course is designed to provide you with a solid understanding of logistics, ensuring that you are familiar with the components of a logistics system as well as the many types of logistics management. The course will also introduce you to the topic of business logistics and the goals of logistics management. This Level 4 Logistics Management Course comprises a series of easy-to-digest, in-depth lessons that will offer you a deep, expert level of knowledge. This course will provide you with the skills you need to land your dream job. Enrol now and start learning. Learning Outcomes After completing this Level 4 Logistics Management course, you will be able to - Describe logistics management as well as what it entails. Build a strong logistics system. Describe supply chain management and supply chain movement. Know about sourcing, purchasing, and procurement. Explain various distribution networks. Keep track of your supplier relationships. Investigate resource management and planning. Recognize the connection between transportation and logistics. Why Choose Level 4 Logistics Management Course from Us Self-paced course, access available from anywhere. Easy to understand, high-quality study materials. Course developed by industry experts. MCQ quiz after each module to assess your learning. Automated and instant assessment results. 24/7 support via live chat, phone call or email. Free PDF certificate as soon as completing the course. >> Courses are included in this Level 4 Logistics Management Bundle Course Course 01: Level 4 Logistics Management Course 02: Level 7 Diploma in Leadership and Management Course Course 03: Level 7 Business Management Course Course 04: Level 7 Diploma in Facilities Management Course Course 05: Level 5 Negotiation Skills Course Course 06: Level 5 Diploma in Business Analysis Course 07: Level 4 Time Management Course Course 08: Level 3 Business Administration Course 09: Level 2 Diploma in Business Administration ***Other Benefits of Level 4 Logistics Management Bundle*** Free 9 PDF Certificate Lifetime Access Free Retake Exam Tutor Support [ Note: Free PDF certificate as soon as completing the this Level 4 Logistics Management course ] Course Curriculum Level 4 Logistics Management Module 01: An Overview of Logistics Management Module 02: Logistics, the Supply Chain and Competitive Strategy Module 03: Product Design, Cleaner Production and Packaging Module 04: Sustainable Purchasing and Procurement Module 05: Sustainable Warehousing Module 06: Understanding Customer Service Module 07: Basic Inventory Planning and Management Module 08: Freight Transport Management Module 09: Reverse Logistics and Recycling >> --------------------- << Assessment Method After completing each module of the Logistics Management Course, you will find automated MCQ quizzes. To unlock the next module, you need to complete the quiz task and get at least 60% marks. Certification After completing the MCQ/Assignment assessment for this Logistics Management course, you will be entitled to a Certificate of Completion from Training Tale. The certificate is in PDF format, which is completely free to download. A printed version is also available upon request. It will also be sent to you through a courier for £13.99. Who is this course for? This Level 4 Logistics Management is perfect for - Job Seekers Student Fresh Graduate Organisational Manager Company Owner Requirements There are no specific requirements for Level 4 Logistics Management course because it does not require any advanced knowledge or skills. Certificates Certificate of completion Digital certificate - Included
