- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
55930 Courses in Huntingdon delivered Online
LOOKING FOR: ADULT FICTION, NON-FICTION Una is a Rights Agent at Susanna Lea Associates and am starting to build a client list. She grew up in London and graduated from the University of Cambridge with a BA in English in 2021. At university, Una was particularly interested in contemporary West African and South Asian literature. She started as an agent's assistant at SLA London in 2022 and now handles some translation rights and provides support with editorial work and submissions. Una's favourite reads always set her at ease right away and draws her in with impressive and accessible storytelling, memorable characters or an original hook. Una enjoys writing which expands her worldview, makes her laugh out loud or keeps her on her toes with its twists and turns. She welcomes submissions from debut authors and would be keen to read across a wide range of genres and styles. She is looking for literary, upmarket and book club fiction, and is always drawn to stories that explores the challenges and complexities of love and relationships in all its forms —within families, between friends or in romantic relationships. Una loves the way in which familial relationships are dissected in The Wren, The Wren by Anne Enright and the impact of the local community in Small Worlds by Caleb Azumah Nelson. She is always drawn to novels with a strong sense of community, whether they are unified by geography, culture, or in other unexpected ways. Una has always loved reading international and translated fiction and welcomes submissions from authors writing contemporary fiction that engages with cultures and traditions from around the world, such as in voices of the deities in Freshwater by Akwaeke Emezi or the subversive tales of Sayaka Murata. She is not looking for children’s or YA titles, science fiction or high-concept fantasy, but is open to submissions from authors writing in the speculative fiction space, and books with fantastical or otherworldly elements, be that magical realism or supernatural horror, such as Mona Awad's campus novel with a twist, Bunny. Una would also love to read more writing that engages with the natural world and reminds us of the limitations of human understanding. In non-fiction, Una enjoys books that furthers her understanding of wider societal issues — nature and the environment, culture, and little-known history. Her recent non-fiction favourites are Eve by Cat Bohannon, Doppelgänger by Naomi Klein and Unearthed by Claire Ratinon. Una would like you to submit a covering letter, 1 page synopsis and the first three chapters or 5,000 words of your manuscript in a single word document. (In addition to the paid sessions, Una is kindly offering one free session for low income/under-represented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Monday 22nd September 2025

M.D.D DATING ADVICE FOR WOMEN WITH VERY LOW CONFIDENCE PACKAGE (DATING ADVICE FOR WOMEN)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
Introspective test Emotional regulation and emotional intelligence training Help in addressing pain points areas Full Makeover and beauty treatments 10 V.I.P confidence building sessions Personality test Addressing trauma issues Personal life coach available daily Behavioural pattern training Relationships analysation Happiness test Dating advice for low confidence and insecurity triggers Eradication of negative patterns Cognitive behavioural therapy https://relationshipsmdd.com/product/dating-advice-for-women-with-very-low-confidence-package/

LOOKING FOR: ADULT FICTION, NEW ADULT Rebeka Finch is a Junior Agent at the Darley Anderson Literary Agency. Alongside assisting Darley on his list of authors, Rebeka is building her own list of romance and romantasy authors, specifically for the BookTok hungry new adult/20+ markets. She is on the hunt for messy, cheesy, heartbreaking, relatable, characters and stories with romance at the very heart of the narrative. For those writing romantasy, Rebeka is looking for books that strike the perfect balance of romance, pace, action and world-building, with series potential. Importantly, she looks for strong, diverse, brave and relatable characters in these settings. People that feel like both a friend, a champion and an ally. Rebeka would like you to submit a covering letter, 1 -2 page synopsis and the first 5,000 words of your completed manuscript in a single word document. (In addition to the paid sessions, Rebeka is kindly offering one free session for low income/under-represented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Monday 22nd September 2025

Feedback Mastery Unleashed
By Mindset Leadership
Feedback Mastery Unleashed: 28 day online mini-programme to ignite high performance leadership for high achieving teams

Anti-Money Laundering (AML) Training For Support Staff Course
By DG Legal
In January 2024 alone, reports were published about the SRA taking enforcement action against 3 firms and 4 individuals for failure to comply with the Money Laundering Regulations 2017. The fines issued for these non-compliances total over £570,000 plus costs. The absence of staff training, or requirement to complete additional training, was noted in a number of these cases. Action has not only been taken against solicitors, but also other individuals who are not regulated by the SRA, whose breaches were so serious that the SRA felt compelled to take action. As all SRA enforcement action, from rebukes to fines, is published by the SRA, the potential financial and reputational impact upon firms may be felt by all staff, regardless of whether they had any direct involvement with the non-compliance. This course will cover the following to assist support staff in understanding the fundamental aspects of AML. The basics of what AML is In scope / not in scope work for AML POCA / TA PCPs - CDD & EDD Clients Risks – what could raise a risk? Reporting to the MLRO / MLCO Tipping off Target Audience The online course is suitable for support staff or legal practitioners wanting to understand the basics of AML. Resources Comprehensive and up to date course notes will be provided to all delegates which may be useful for ongoing reference or cascade training. Please note a recording of the course will not be made available. Speaker Helen Torresi, Consultant, DG Legal Helen is a qualified solicitor with a diverse professional background spanning leadership roles in both the legal and tech/corporate sectors. Throughout her career, she has held key positions such as COLP, HOLP, MLCO, MLRO and DPO for law firms and various regulated businesses and services. Helen’s specialised areas encompass AML, complaint and firm negligence handling, DPA compliance, file review and auditing, law management, and operational effectiveness in law firms, particularly in conveyancing (CQS).

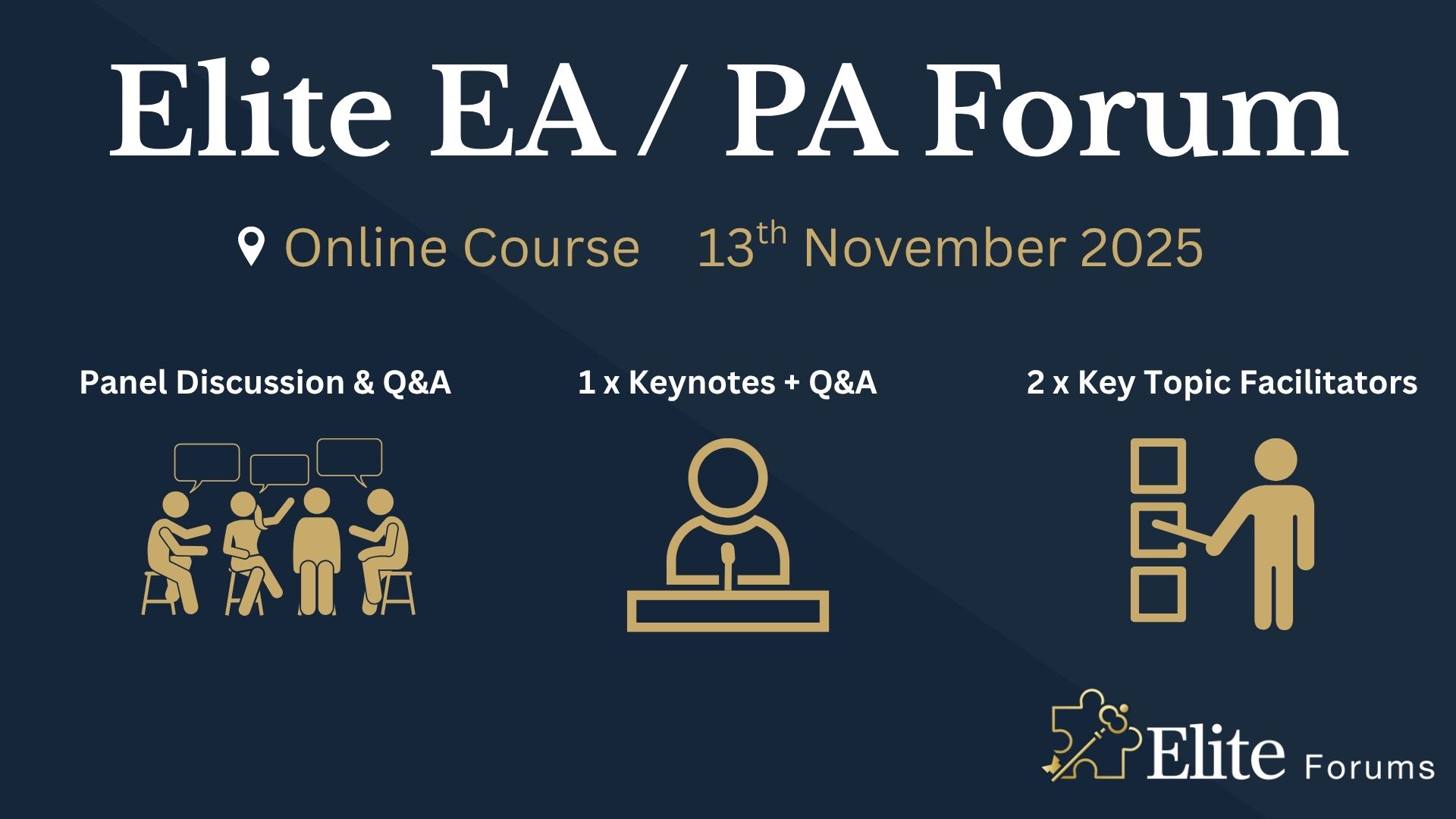
Elite EA PA Forum 🇬🇧
By Elite Forums UK
Elite EA/PA Forum We are delighted to announce the Elite EA/PA Forum for the UK & Ireland will be on the 13th November 2025. Our workshop aims to: Enhance your influence and impact by mastering assertive communication, negotiation, and self-advocacy skills. Stay composed and solution-focused in high-pressure situations with practical tools for crisis management and clear decision-making. Embrace evolving technology by understanding how AI and automation can streamline your role and boost efficiency. Future-proof your career by building strategic value, resilience, and adaptability in an ever-changing professional landscape. Keynote Address with Q&A from the audience: What to expect from Sam's Keynote: With over 30 years supporting leaders at the highest levels, Sam Cohen brings a wealth of insight, experience, and stories (the kind she can share) to the stage. From 18 years serving within The Royal Household - including as Deputy Private Secretary and Press Secretary to Her late Majesty Queen Elizabeth II - to working with The Duke and Duchess of Sussex, running the Prime Minister’s Office at Downing Street, and serving as Chief of Staff to the global CEO of Rio Tinto, Sam’s career is a masterclass in discretion, diplomacy, and delivering at the top. In this exclusive keynote, Beyond the Role, Sam will explore how Executive Assistants don’t just support leaders - they shape leadership, drive strategy, and build legacy from behind the scenes. Join us for this rare opportunity to hear from someone who’s been at the epicentre of power - and bring your questions! The keynote will include a live Q&A, where you can ask Sam about her remarkable career, leadership insights, and how to truly excel in high-performance environments. (Don’t ask her what the Queen kept in her handbag - she’s not telling.) Sam Cohen Career Bio: Sam Cohen has spent the last 30 years working to support leaders in the public and private sectors. Sam spent 18 years serving The Royal Household, as Deputy Private Secretary to Her late Majesty Queen Elizabeth II and Press Secretary to The Queen. Sam also served as Private Secretary to The Duke and Duchess of Sussex. Following this time, Sam worked as Director of the Prime Minister’s Office at Downing Street under Boris Johnson and, most recently, was Chief of Staff to the global CEO at Rio Tinto. Source: ABC News - YouTube Channel. Facilitator - AM: Monika Turner The Confident Assistant - Speak Up, Go After What You Want & Create The Future You Deserve: Develop practical strategies to negotiate workload, boundaries, and career growth with confidence. Learn assertive communication techniques to handle challenging conversations effectively. Build self-advocacy skills to articulate your value and influence outcomes in the workplace. Monika Turner Career Bio: Monika Anna Turner is an ICF-certified Leadership and Executive coach with over seven years of experience helping professionals unlock their confidence, elevate their voice, and lead with authenticity. Before stepping into coaching, she built a successful career as a Personal Assistant, Executive Assistant, and ultimately Chief Of Staff —giving her a deep understanding of the unique challenges and strengths of support roles. Originally from Poland, Monika knows firsthand what it’s like to question your voice and your value—especially in a second language. Her journey from self-doubt to self-assurance informs everything she does today. Through her coaching, she empowers assistants and leaders alike to move beyond fear, speak up and create fulfilling careers they’re proud of. Panel Fabiana Goncalves Executive Assistant to Global VP PerfectDraft & PerfectDraft Commercial Director An accomplished C-Suite Executive & Personal Assistant, I bring over a decade of experience supporting top-level leadership—including CEOs, Founders, and Executive Teams—across multinational and national organizations. I specialize in executive support that goes far beyond calendar management, contributing as a strategic partner in decision-making, operations, and leadership effectiveness. Known for my discretion, diplomacy, and operational precision, I help executives stay focused on what matters most—by anticipating needs, managing complexity, and driving efficiency in both corporate and personal domains. I bring a strategic lens to every task, balancing immediate priorities with long-term objectives. With a proactive mindset, sharp judgment, and strong communication skills, I serve as a trusted advisor and problem-solver in fast-paced, high-stakes environments. Rebecca Polson Executive Support Manager to the Chief Executive An award-winning Executive Assistant with over 10 years’ experience across the higher education, charity, private, and public sectors. Currently Executive Support Manager to the Chief Executive at Alzheimer’s Research UK, she provides high-level support in the fast-paced, mission-driven environment of the largest dementia research charity in the UK. Her previous roles include supporting senior leaders at the Natural History Museum, the Incorporated Society of Musicians, and the Royal College of Music. She brings expertise in executive support, governance, stakeholder engagement, and complex diary and project management. Named PA of the Year in 2023 and a finalist in the SecsintheCity PA of the Year Awards, she is known for her professionalism, discretion, and ability to stay ahead of the needs of the people and organisations she supports. Ola Boddington Senior Executive Assistant As a seasoned Executive Assistant, she has honed her skills in management and project planning over the years. She has worked with various organisations, including Zoa, Signal AI, and ConsenSys, where she provided high-level administrative support to senior executives. Her expertise lies in managing complex schedules, coordinating travel arrangements, and ensuring seamless communication among team members. She is also proficient in using various software tools to streamline workflows and enhance productivity. She is passionate about delivering exceptional service and contributing to the success of the teams she works with. Claudine Martin Senior Executive Assistant Claudine is a highly skilled Senior Executive Assistant, currently supporting the Head of BNY Pershing EMEA. With a distinguished career spanning nearly 17 years in the British Army, Claudine retired in 2023 at the rank of Staff Sergeant, bringing a wealth of experience in high-pressure environments and strategic operations to her current role. Throughout her military career, Claudine specialised in Human Resources, and served as the Personal Assistant to the Army Director of Engagement and Communication at the Ministry of Defence. In this capacity, she played a pivotal role in the planning and execution of significant events and initiatives, showcasing her exceptional organisational skills and attention to detail. Her dedication and professionalism were recognised when she was awarded PA of the Year in 2019 by PA Life. An advocate for the Executive Assistant profession, Claudine is also a sought-after public speaker. She regularly shares her insights at industry events, including the PA Show, and serves as an advisory board member, contributing to the ongoing development and recognition of the profession. Claudine is passionate about empowering others and has previously mentored young people through the Diana Award, a programme established in honour of Princess Diana to support disadvantaged youth. Additionally, she has participated in Fast Forward 15, a mentoring initiative aimed at women aspiring to build careers in events, hospitality, or related industries. With her extensive experience, dedication to excellence, and commitment to mentorship, Claudine continues to make a significant impact in her field and inspire the next generation of leaders. She proudly represented the UK at the Invictus Games 2023, showcasing her unwavering determination and unwavering spirit. In her spare time, Claudine enjoys park run and writing poems. The Importance of Becoming a Strategic Advisor Learn how to shift from reactive to proactive. Develop the mindset and behaviours of a strategic advisor. Understand how to add value beyond your job description. Facilitator - PM: Justin Kabbani AI Is Not Here to Replace You. It's Here to Upgrade You. We'll explore Justin's proven 3P framework: Priming – How to set up AI like a strategic advisor by feeding it context, tone and mindset Prompting – How to craft clear, structured instructions to get consistently great results Producing – How to turn AI outputs into high-leverage work that makes you stand out Your session outcomes: Real examples from admin professionals already using AI to elevate their work Prompts you can copy, adapt, and test live Interactive exercises to build confidence fast A practical challenge to implement right after the session If you’ve been overwhelmed by AI, or underwhelmed by its impact, this session will change that. You'll leave with tools you can use today, and a mindset you’ll carry forward for the rest of your career. Justin Kabbani Career Bio: Justin Kabbani is one of Australia’s most in-demand AI trainers and keynote speakers, known for making AI feel simple, powerful, and immediately useful. He’s worked with brands like Uber, Treasury Wine Estates, and Udemy, helping their teams embed AI into daily workflows, strategic planning, and executive communication. Over the past two years, Justin has trained more than 2,000 professionals across Australia and beyond, consistently earning feedback like “mind-blowing,” and “game-changing”. His signature Prime, Prompt, Produce framework has transformed how business leaders, executive assistants, marketers, and teams think, work, and communicate with AI, without needing to be “tech people.” Justin believes AI isn’t here to replace people. It’s here to take the robotic work off our plate, so we can focus on what humans do best. LinkedIn: https://www.linkedin.com/in/justinkabbani/ Website: https://justinkabbani.com/ Speed Connections Networking Session Join us for Speed Connections, a lively 30-minute networking session designed to foster meaningful connections in a fun, fast-paced environment. Every 10 minutes, attendees will be placed into new breakout rooms with small groups, giving everyone the chance to meet a diverse range of peers. Each breakout session will feature engaging prompts to spark conversations and make networking enjoyable and memorable! Who will attend this event? Executive Assistant (EA) Personal Assistant (PA) Virtual Assistant (VA) Legal Secretary Legal Executive Assistant Administrative Assistant Office Manager Health Care Office Manager Chief of Staff Additional roles may be relevant depending on role responsibilities along with development opportunities. This workshop is open to females, male including trans women/males and non-binary professionals. Group Rate Discounts To discuss our group rates in more detail, please email support@elite-forums.com and provide the following: Group Number (How many would like to attend) Event Date (If numerous dates, please advise if we are splitting attendees across multiple dates) Attendee Contact details (Or request our Group Rate Document. Complete and return - we'll sort the rest.) Group discounts are on request - see below group rate discount brackets: 🧩 You just need one piece to come together - to unlock your Elite Potential. 🔑 Media outlets/organisations will not be permitted to attend this event.
Winter Series 2025 - Organisation & Relationship Systems Coaching Training
By CRR UK
CRRUK equips professionals with the concepts, skills and tools to build conscious, intentional relationships, and to coach relationship systems of any size.

Monthly IFS Consultation Group (Autumn-Winter)
By DrMariaKaltsi
Join a supportive small group of 3-4 members maximum in monthly 90-minute sessions designed to deepen your Internal Family Systems (IFS) practice. These meetings provide a safe space to: Gain insights and perspectives on your clinical work Enhance your understanding of IFS principles Explore and work with your own internal parts as a therapist Share valuable resources and techniques £85 per month. Your booking covers the first month, with invoicing starting from the second month. Sessions are available on Mondays at 1:00 pm. Provided by Dr Maria Kaltsi, Clinical Psychologist, IFS Certified Therapist and Approved Clinical Consultant, with experience of supporting IFS trainings (including L1 and L2 trainings). For more information, please contact: mariakaltsitherapy@gmail.com

Team Leader / Supervisor Level 3 Apprenticeship
By Leadership Management International (LMI) UK
This Level 3 Apprenticeship has been designed for individuals wishing to start or advance their skills in first-line management, and will equip them with the knowledge and understanding needed to effectively provide direction, instructions and guidance to ensure the achievement of set goals.

FAA Level 2 Award In First Aid For Youth Mental Health (RQF) Classroom (1 day course), Virtual (3 x 2½ hour sessions) Gives learners knowledge of Youth Mental Health First Aid Gives learners the skills to help young people with mental health problems and improve their mental health Course Contents: What is Youth Mental Health? The role of the mental health first aider Identifying mental health conditions Recognising and managing Stress Mental health conditions Recognising a range of mental health conditions:DepressionAnxietyPsychosisEating disordersSuicideSelf-harmPost-traumatic stress disorderConduct disorders - BullyingDrugs and alcohol Mental health first aid action plan Benefits of this course: These figures, taken from the Young Minds website show clearly how many young people suffer with their mental health... One in six children aged five to 16 are identified as having a probable mental health problem That means that, on average, five children in every classroom have a mental health problem 80% of young people with mental health needs agreed that the coronavirus pandemic had made their mental health worse Suicide was the leading cause of death for males and females aged between five to 34 in 2019 Around half of 17-19 year-olds with a diagnosable mental health disorder has self-harmed or attempted suicide at some point In 2018-19, 24% of 17-year-olds reported having self-harmed in the previous year, and seven per cent reported having self-harmed with suicidal intent at some point in their lives So please, learn more about how to help these youngsters, and give them the chance to live happy, healthy lives Accredited, Ofqual regulated qualification Our Mental Health First Aid Courses are nationally recognised, Ofqual regulated qualifications accredited by First Aid Awards Ltd in association with NUCO Training. This means that you can be rest assured that your Mental Health First Aid Certificates fulfill the upcoming legal requirements and are a very good way to make sure you and your employees have a supporting workplace to deal with staff's mental health conditions. The Ofqual Register number for this course is 603/7176/6
