- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
2189 Courses delivered Live Online
BOHS P304 Online - COSHH - Fundamentals of Risk Assessment and Control
By Airborne Environmental Consultants Ltd
BOHS P304 is designed to give practical guidance on assessing the health risks caused by hazardous substances, in order to meet the requirements of the Control of Substances Hazardous to Health (COSHH) Regulations 2002 for a 'suitable and sufficient' risk assessment.

AWS Technical Essentials
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for Individuals responsible for articulating the technical benefits of AWS services Individuals interested in learning how to get started with using AWS SysOps Administrators, Solution Architects and Developers interested in using AWS services Overview Recognize terminology and concepts as they relate to the AWS platform and navigate the AWS Management Console. Understand the foundational services, including Amazon Elastic Compute Cloud (EC2), Amazon Virtual Private Cloud (VPC), Amazon Simple Storage Service (S3), and Amazon Elastic Block Store (EBS). Understand the security measures AWS provides and key concepts of AWS Identity and Access Management (IAM). Understand AWS database services, including Amazon DynamoDB and Amazon Relational Database Service (RDS). Understand AWS management tools, including Auto Scaling, Amazon CloudWatch, Elastic Load Balancing (ELB), and AWS Trusted Advisor. AWS Technical Essentials introduces you to AWS services, and common solutions. It provides you with fundamental knowledge to become more proficient in identifying AWS services. It helps you make informed decisions about IT solutions based on your business requirements and get started working on AWS. Prerequisites Working knowledge of distributed systems Familiarity with general networking concepts Working knowledge of multi-tier architectures Familiarity with cloud computing concepts 1 - AWS introduction and history AWS Global Infrastructure Demonstration: AWS Management Console 2 - AWS Storage Identify key AWS storage options Describe Amazon EBS Create an Amazon S3 bucket and manage associated objects 3 - Compute, network and storage services Amazon Elastic Compute Cloud (EC2) Amazon Virtual Private Cloud (VPC) Amazon Simple Storage Service (S3) Amazon Elastic Block Store (EBS) Demonstration: Amazon Simple Storage Service (S3) Hands-on lab: Build your VPC and launch a web server 4 - AWS Security, AWS Identity and Access Management (IAM) AWS Identity and Access Management (IAM) Demonstration: AWS Identity and Access Management (IAM) 5 - Compute Services & Networking Identify the different AWS compute and networking options Describe an Amazon Virtual Private Cloud (VPC) Create an Amazon EC2 instance Use Amazon EBS with Amazon EC2 6 - Managed Services & Database Describe Amazon DynamoDB Understand key aspects of Amazon RDS Launch an Amazon RDS instance 7 - Databases (RDS, DynamoDB) SQL and NoSQL databases Data storage considerations Hands-on lab: Build your database server and connect to it 8 - AWS elasticity and management tools Auto scaling Load balancing Cloud Watch Trusted Advisor Hands-on lab: Scale and load balance your architecture 9 - Deployment and Management Identify what is CloudFormation Describe Amazon CloudWatch metrics and alarms Describe Amazon Identity and Access Management (IAM)

Cross Border Electricity Trading in Asia - Renewable Energy, Digital Technologies and New Operational Flexibility Solutions
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) This 3 half-day Virtual Instructor Led Training (VILT) course highlights the impact of the introduction of renewable energy, digital technologies and new operational flexibility solutions in the electricity trading market. These advancements facilitate unique opportunities and challenges for cross border trading of electricity. Most countries in Asia, have designed their own portfolio of climate actions with an accelerated penetration of renewable energy (or by importing renewable energy into their local grids). These changes are taking place at unprecedented speed and add further complexity to the operation of electricity trading markets, while presenting new opportunities. The Asian market, can tap into its vast potential of solar, wind and geothermal energy sources. A global, unified vision is emerging to support each of countries' energy needs and decarbonization goals. This VILT course will highlight priorities of each country to achieve its energy goals. The main operational flexibilities of each type of renewable resource are discussed in detail. The course also discusses the main components of Power Purchase Agreements and advancements in digitalization and how digital technologies can influence the energy market and cross border electricity trading. Key Takeaways: New Energy Market Design Cross Border Trading PPAs Mechanisms and Examples of PPAs The Increased Penetration of Renewable Resources in the Power Systems and How It Stimulates Cross Border Trading How Digital Innovation Drives Energy Markets and Cross Border Trading Training Objectives Upon completion of this VILT course, participants will be able to: Be familiar with the global vision of One Sun, One World, One Grid Understand the major trends reshaping the energy markets Learn how innovative digital technologies change the energy markets Understand why sustainable energy markets require a tighter coordination between transmission and distribution system operators Engage with each other to design the energy market of the future Target Audience This VILT course will benefit policy makers and regulators from energy agencies, transmission companies and utilities as well as power system engineers and power system operators from control centre and ISO. Training Methods The VILT will be delivered online in 3 half-day sessions comprising 4 hours per day, including time for lectures, discussion, quizzes and short classroom exercises. Course Duration: 3 half-day sessions, 4 hours per session (12 hours in total). Trainer Your expert course leader is a Utility Executive with extensive global experience in power system operation and planning, energy markets, enterprise risk and regulatory oversight. She consults on energy markets integrating renewable resources from planning to operation. She led complex projects in operations and conducted long term planning studies to support planning and operational reliability standards. Specializing in Smart Grids, Operational flexibilities, Renewable generation, Reliability, Financial Engineering, Energy Markets and Power System Integration, she was recently engaged by the Inter-American Development Bank/MHI in Guyana. She was the Operations Expert in the regulatory assessment in Oman. She is a registered member of the Professional Engineers of Ontario, Canada. She is also a contributing member to the IEEE Standards Association, WG Blockchain P2418.5. With over 25 years with Ontario Power Generation (Revenue $1.2 Billion CAD, I/S 16 GW), she served as Canadian representative in CIGRE, committee member in NSERC (Natural Sciences and Engineering Research Council of Canada), and Senior Member IEEE and Elsevier since the 90ties. Our key expert chaired international conferences, lectured on several continents, published a book on Reliability and Security of Nuclear Power Plants, contributed to IEEE and PMAPS and published in the Ontario Journal for Public Policy, Canada. She delivered seminars organized by the Power Engineering Society, IEEE plus seminars to power companies worldwide, including Oman, Thailand, Saudi Arabia, Malaysia, Indonesia, Portugal, South Africa, Japan, Romania, and Guyana. Our Key expert delivered over 60 specialized seminars to executives and engineers from Canada, Europe, South and North America, Middle East, South East Asia and Japan. Few examples are: Modern Power System in Digital Utilities - The Energy Commission, Malaysia and utilities in the Middle East, GCCIA, June 2020 Assessment of OETC Control Centre, Oman, December 2019 Demand Side management, Load Forecasting in a Smart Grid, Oman, 2019 Renewable Resources in a Smart Grid (Malaysia, Thailand, Indonesia, GCCIA, Saudi Arabia) The Modern Power System: Impact of the Power Electronics on the Power System The Digital Utility, AI and Blockchain Smart Grid and Reliability of Distribution Systems, Cyme, Montreal, Canada Economic Dispatch in the context of an Energy Market (TNB, Sarawak Energy, Malaysia) Energy Markets, Risk Assessment and Financial Management, PES, IEEE: Chicago, San Francisco, New York, Portugal, South Africa, Japan. Provided training at CEO and CRO level. Enterprise Risk methodology, EDP, Portugal Energy Markets: Saudi Electricity Company, Tenaga National Berhad, Malaysia Reliability Centre Maintenance (South East Asia, Saudi Electricity Company, KSA) EUSN, ENERGY & UTILITIES SECTOR NETWORK, Government of Canada, 2016 Connected+, IOT, Toronto, Canada September 2016 and 2015 Smart Grid, Smart Home HomeConnect, Toronto, Canada November 2014 Wind Power: a Cautionary Tale, Ontario Centre for Public Policy, 2010 POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

Scrum Master Exam Prep: Virtual In-House Training
By IIL Europe Ltd
Scrum Master Exam Prep: Virtual In-House Training This workshop prepares you for the Scrum.org Professional Scrum Master (PSM)™ I certification. A voucher for the exam and the access information you will need to take the exam will be provided to you via email after you have completed the course. NOTE: If you have participated in any of IIL's other Scrum workshops, you can bypass this program and focus on reading/studying the Scrum Guide and taking practice exams from Scrum.org. A Scrum Master helps project teams properly use the Scrum framework, increasing the likelihood of the project's overall success. Scrum Masters understand Scrum values, practices, and applications and provide a level of knowledge and expertise above and beyond that of typical project managers. Scrum Masters act as 'servant leaders', helping the rest of the Scrum Team work together and learn the Scrum framework. Scrum Masters also protect the team from both internal and external distractions. The Professional Scrum Master™ I (PSM I) certificate is a Scrum.org credential that enables successful candidates to demonstrate a fundamental level of Scrum mastery. PSM I credential holders will grasp Scrum as described inThe Scrum Guide™1 and recognize how those concepts can be applied. They will also share a consistent terminology and approach to Scrum with other certified professionals. What you will Learn You'll learn how to: Successfully prepare for the Scrum.org PSM I exam Comprehend the Agile Manifesto and mindset Explain the fundamental principles of Scrum, including events, artifacts, and roles Guide the Scrum team in their responsibilities Define Ready and Done Write requirements in the form of user stories Estimate using planning poker and prioritize using MoSCoW Facilitate the team through the 5 Sprint events Fulfill the role of Scrum Master in a Scrum project Create Information Radiators to enable transparency Define the structure of the retrospective Getting Started Introductions Workshop orientation Exam prep preview Foundation Concepts Agile History, Values, and Mindset Introduction to Scrum Scrum events Scrum artifacts Scrum Roles and Responsibilities Product Owner responsibilities Scrum Master responsibilities The Team responsibilities Cross-functional teams Building effective teams The Product Backlog and User Stories The Product Backlog User Stories Definition of Done Backlog grooming Estimating User Stories Story points, planning poker Prioritizing User Stories The Sprint Team capacity and velocity The Sprint Planning Meeting The Sprint Backlog The Sprint Learning to self-manage, self-organize, self-improve Sprint Review and Retrospective Project Progress and Completion The Daily Scrum The Task Board and The Burndown Chart Information Radiators Closing a Scrum Project Summary and Next Steps Review of course goals, objectives, and content Exam prep next steps

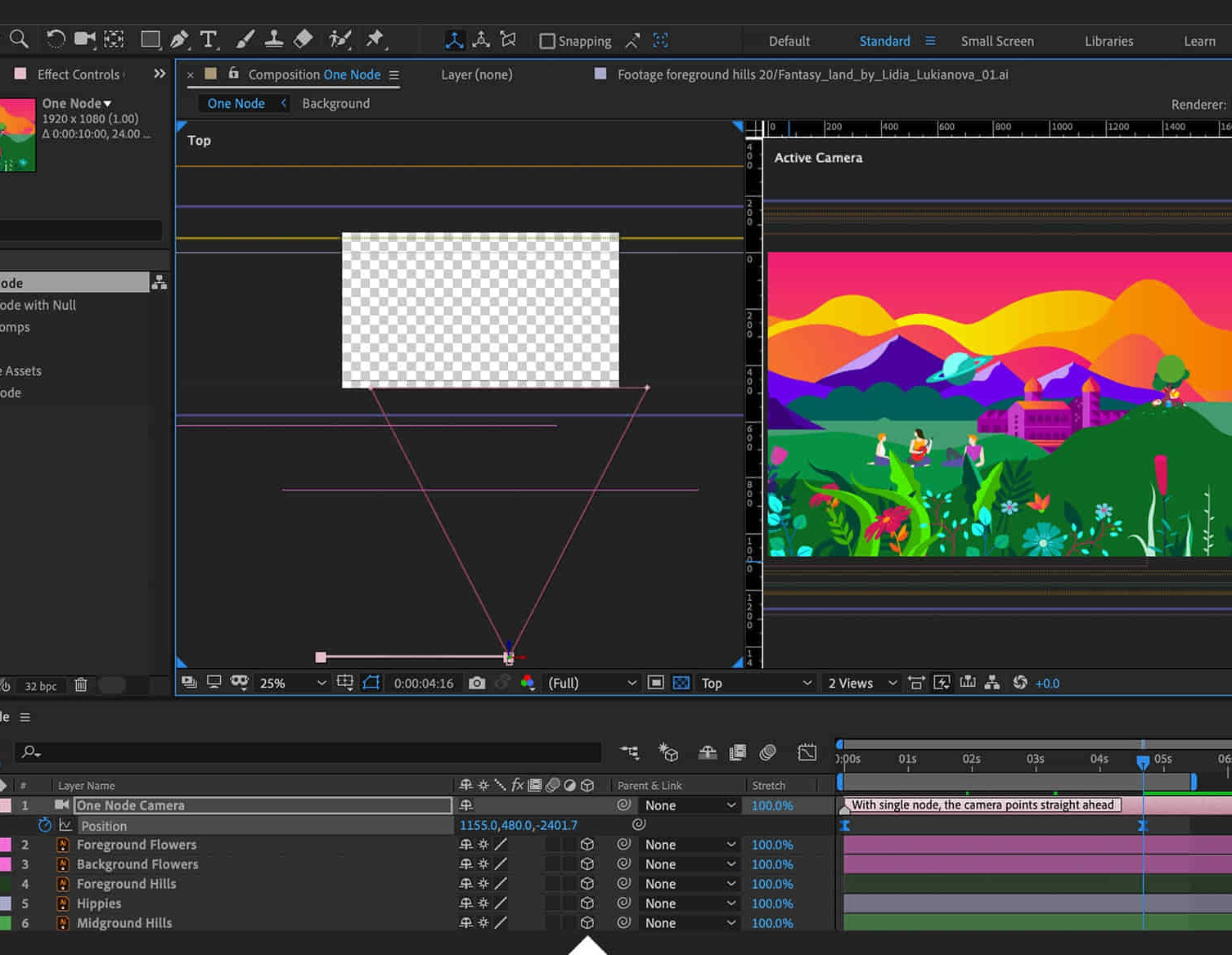
Adobe After Effects Beginners to Advanced Course
By ATL Autocad Training London
Adobe After Effects Beginners to Advanced Course Tailored for motion graphics designers basic to expert level. Explore advanced topics including motion tracking, green screen compositing, text animation, and techniques like expressions. Learn animations based on geometric proportions in our Advanced Motion Methods module. Click here for more info: Website Duration: 40 hours Approach: 1-on1 sessions and Customized content. Schedule: Choose your own day and time. Mon to Sat between 9 am and 5 pm. Module 1: Introduction to After Effects Exploring Adobe After Effects Navigating the Interface Configuring Preferences Utilizing Auto-Save Feature Module 2: Projects and Compositions Creating New Projects/Compositions Importing and Organizing Assets Working with Layers Module 3: Animation Techniques Keyframe Essentials Motion Paths and Modifications Graph Editor Insights Motion Control Tools Module 4: Layer Management Organizing and Navigating Layers Layer Visibility and Locking Switches and Modes in Detail Module 5: Shape Manipulation Shape Layers Fundamentals Creating and Animating Shapes Anchor Point Adjustment Module 6: Effects Mastery Applying and Customizing Effects Exploring Various Effects Examples Module 7: Masks and Track Mattes Mask Creation and Animation Track Matte Techniques Module 8: Text and Typography Animation Working with Text Layers Text Animation Presets Layer Styles for Typography Module 9: Exporting Your Creations Export Options Overview Direct Export from After Effects Utilizing Media Encoder After Effects https://www.adobe.com By the end of this 40-hour After Effects training, you will: Master Essentials: Understand fundamental and advanced After Effects features for diverse projects. Create Impactful Visuals: Craft compelling motion graphics, animations, and visual effects. Expert Animation Skills: Perfect keyframing, motion paths, and dynamic animations. Streamlined Workflow: Organize projects efficiently, ensuring smooth project execution. Creative Expression: Manipulate shapes, animate text, apply effects, and create masks creatively. Professional Exporting: Master export techniques for various platforms and media. Confidence and Expertise: Solve challenges confidently, applying skills in real-world projects. Industry-Ready: Gain skills applicable in filmmaking, animation, marketing, and creative sectors. Ongoing Support: Access post-training support for continued assistance. Certification: Receive a recognized certification, enhancing your professional profile. Course Title: Adobe After Effects Comprehensive Training Key Details: Duration: 40 hours Learning Approach: Personalized Training: Tailored content with 1-2-1 sessions. Flexible Schedule: Choose hours between 9 am and 7 pm, Monday to Saturday. Method: Hands-on learning with step-by-step demonstrations. Course Highlights: Master Essential Tools: From basics to advanced features for motion graphics and visual effects. Expert Guidance: Certified trainers provide personalized attention. Creative Animation: Learn advanced animation techniques, motion paths, and effects application. Efficient Workflow: Optimize project organization, layer management, and export techniques. Real-World Projects: Apply skills in filmmaking, animation, marketing, and more. Post-Training Support: Lifetime access to email and phone assistance for continued guidance. Certification: Receive a recognized certificate upon course completion. Benefits: Industry-Relevant Skills: Gain expertise for diverse creative sectors. Unleash Creativity: Craft compelling motion graphics, animations, and visual effects. Confidence in Execution: Solve challenges confidently with real-world application. Professional Recognition: Enhance your profile with a certified After Effects proficiency. Course Materials and Certification: Upon enrollment, you will receive a valuable After Effects training guide in PDF format, serving as a useful resource during and after the course. Additionally, upon successful completion, you'll be awarded an e-certificate, validating your achievement in the Adobe After Effects training program. Post-Course Support: Rest assured, you'll have access to lifetime email support from your dedicated After Effects trainer, providing assistance for any inquiries or challenges arising after the course. Prerequisites and Software Version: No prior After Effects knowledge is required for enrollment. The training is tailored for After Effects 2023, with techniques applicable to recent software releases. Whether you're a Windows or Mac user, the training suits your needs. Our Guarantees: We prioritize your satisfaction with our double guarantee - a price assurance ensuring the best value for your investment and a training guarantee ensuring you master essential concepts and skills.
Certified GDPR Foundation
By Training Centre
The GDPR Foundation training enables delegates to understand how to define and implement a privacy compliance framework aligned to best practice. During this training course, you will be able to understand the fundamental privacy principles and become familiar with the role of the Data Protection team and the DPO. About This Course At Foundational level, candidates prove they have understood the fundamental methodologies, requirements, best practice and management approach of a Privacy Compliance Framework. Learning principles; Understand the General Data Protection Regulation requirements and the fundamental principles of privacy Understand the obligations, roles and responsibilities of the Data Protection Officer Understand the concepts, approaches, methods and techniques to effectively participate in the implementation process of a compliance framework with regard to the protection of personal data. Educational approach; Lecture sessions are illustrated with practical questions and examples Practical exercises include examples and discussions Practice tests are similar to the Certification Exam Course Agenda Day 1: Introduction to GDPR and Data Protection Principles Day 2: The General Data Protection Regulation requirements and Certification Exam Prerequisites There are no prerequisites for this course. What's Included? Refreshments & Lunch (Classroom courses only Course Slide Deck CPD Certificate Who Should Attend? Individuals involved in the processing of Personal Data and Information Security Individuals seeking to gain knowledge about the main privacy principles Individuals interested to pursue a career in Data Protection Provided by This course is Accredited by NACS and Administered by the IECB Assessment Delegates sit a combined exam, consisting of in-course quizzes and exercises, as well as a final 40 question, multiple choice exam on Day 2 of the course. The overall passing score is 70%, to be achieved within the 60 minute time allowance. Exam results are provided within 24 hours, with both a Certificate and a digital badge provided as proof of success.

Professional Certificate in User Research
By UX Design Institute
The industry standard course in UX research Master the research skills that make UX professionals so valuable. Become a confident, credible and effective user researcher with a globally recognised qualification. Who is it for? UX professionals Aspiring UX researchers Duration 16 weeks Commitment 3 hours per week Format Online, self-paced with live support and mentoring Why take this user research course: Gain the most in-demand skills* and boost your career in a thriving industry. Learn a complete range of UX research methods. Expand your toolkit to conduct high-quality research at pace. Become an insights expert. Translate findings into actionable insights and communicate them with conviction. Showcase your expertise. Build a professional user research portfolio and earn a university credit-rated qualification. Get the confidence to succeed. Count on our mentors, career advisors and student community throughout your journey. *Research is one of the top 10 most in-demand skills globally (LinkedIn, 2023). A comprehensive, in-depth curriculum This user research course has been created and validated by experts in UX research. It is credit-rated by Glasgow Caledonian University. Self-paced learning gives you the flexibility to study in your own time. Monthly deadlines and submissions give you structure and accountability. The best of both worlds. Module 1 Introduction to user research Understand the role of a UX researcher. Explore the types, methods and ethics of research. Module 2 Planning the research Learn how to build a research plan, collaborate with stakeholders, recruit participants and manage data. Module 3 Fundamental user research skills Master the core skills of interviewing and usability testing. Learn how to moderate and take notes. Module 4 Expanding your toolkit Explore qualitative research methods like ethnography, contextual enquiry, service safaris and diary studies. Module 5 Analysing qualitative research Learn to analyse research data and translate it into user goals, affinity diagrams, personas and journey maps. Module 6 Quantitative research Learn to design, conduct and analyse online surveys, A/B tests and more. Module 7 Communicating the research Learn how to report and present your findings with confidence. Module 8 AI for user research Explore how AI tools can assist researchers. Project Portfolio project Build a professional portfolio to showcase your research expertise.

AWS Security Essentials
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for Security IT business-level professionals interested in cloud security practices Security professionals with minimal to no working knowledge of AWS Overview Assimilate Identify security benefits and responsibilities of using the AWS Cloud Describe the access control and management features of AWS Explain the available methods for providing encryption of data in transit and data at rest when storing your data in AWS. Describe how to secure network access to your AWS resources Determine which AWS services can be used for monitoring and incident response This course covers fundamental AWS cloud security concepts, including AWS access control, data encryption methods, and how network access to your AWS infrastructure can be secured. Based on the AWS Shared Security Model, you learn where you are responsible for implementing security in the AWS Cloud and what security-oriented services are available to you and why and how the security services can help meet the security needs of your organization. Prerequisites Working knowledge of IT security practices and infrastructure concepts, familiarity with cloud computing concepts 1 - Security on AWS Security design principles in the AWS Cloud AWS Shared Responsibility Model 2 - Security OF the Cloud AWS Global Infrastructure Data center security Compliance and governance 3 - Security IN the Cloud ? Part 1 Identity and access management Data protection essentials Lab 01 ? Introduction to security policies 4 - Security IN the Cloud ? Part 2 Securing your infrastructure Monitoring and detective controls Lab 02 ? Securing VPC resources with Security Groups 5 - Security IN the Cloud ? Part 3 DDoS mitigation Incident response essentials Lab 03 ? Remediating issues with AWS Config Conformance Packs 6 - Course Wrap Up AWS Well-Architected tool overview Next Steps Additional course details: Nexus Humans AWS Security Essentials training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the AWS Security Essentials course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

IJSEC - Introduction to Juniper Security
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Operators of Juniper Networks security solutions, including network engineers, administrators, support personnel, and resellers. Overview Identify high-level security challenges in today's networks. Identify products that are incorporated into the Juniper Connected Security solution. Explain the value of implementing security solutions. Explain how Juniper Connected Security solves the cyber security challenges of the future. Explain the SRX Series devices and the added capabilities that next-generation firewalls provide. Explain traffic flows through the SRX Series devices. List the different security objects and how to create them. Describe interface types and perform basic interface configuration tasks. Describe the initial configuration for an SRX Series device. Explain security zones. Describe screens and their use. Explain address objects. Describe services and their use. Describe the purpose for security policies on an SRX Series device. Describe zone-based policies. Describe global policies and their use. Explain unified security policies. Configure unified security policies with the J-Web user interface. Describe IDP signatures. Configure an IDP policy using predefined templates with the J-Web user interface. Describe the use and configuration of the integrated user firewall feature. Describe the UTM security services List the available UTM services on the SRX Series device. Configure UTM filtering on a security policy with the J-Web user interface. Explain Sky ATP's use in security. Describe how Sky ATP and SRX Series devices operate together in blocking threats. Describe NAT and why it is used. Explain source NAT and when to use it. Explain destination NAT and when to use it. Explain static NAT and its uses. Describe the operation and configuration the different types of NAT. Identify various types of VPNs. Describe IPsec VPNs and their functionality. Describe how IPsec VPNs are established. Describe IPsec traffic processing. Configure IPsec VPNs with the J-Web user interface. Describe and configure proxy IDs and traffic selectors with the J-Web user interface. Monitor IPsec VPNs with the J-Web user interface. Describe the J-Web monitoring features. Explain the J-Web reporting features. Describe the Sky Enterprise service and how it can save resources. Explain the functionality of Junos Space Security Director. This course is designed to provide students with the foundational knowledge required to work with SRX Series devices. This course will use the J-Web user interface to introduce students to the Junos operating system. Module 1: COURSE INTRODUCTION COURSE INTRODUCTION Module 2: Juniper Security Concept Security Challenges Security Design Overview Juniper Connected Security Module 3: Juniper Connected Security ? SRX Series Devices Connected Security Interfaces Initial Configuration LAB 1: Initial Configuration Module 4: Security Objects Security Zone Objects Security Screen Objects Security Address Objects Security Services Objects LAB 2: Creating Security Objects with J-Web Module 5: Security Policies Security Policy Overview Zone-Based Policies Global Security Policies Application Firewall with Unified Security Policies LAB 3: Creating Security Policies with J-Web Module 6: Security Services ? IDP and User Firewall IDP Security Services Integrated User Firewall LAB 4: Adding IDP and User Firewall Security Services to Security Policies Module 7: Security Services ? UTM Content Filtering Web Filtering Antivirus Antispam LAB 5: Adding UTM Security Services to Security Policies Module 8: Juniper Connected Security ? Sky AT Sky ATP Overview Blocking Threats Lab 6: Demonstrating Sky ATP Module 9: Network Address Translation NAT Overview Source NAT Destination NAT Static NAT Lab 7: Implementing Network Address Translation Module 10: IPsec VPN Concepts VPN Types Secure VPN Requirements IPsec Tunnel Establishment IPsec Traffic Processing Module 11: Site-to-Site VPNs IPsec Configuration IPsec Site-to-Site Tunne Lab 8: Implementing Site-to-Site IPsec VPNs Module 12: Monitoring and Reporting J-Web monitoring options J-Web Reporting options Lab 9: Using Monitoring and Reporting Appendix A: SRX Series Hardware Appendix D: Sky Enterprise Services Appendix B: Virtual SRX Appendix EJunos Space Security Director Appendix CCLI Prime

