- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
367 Courses in Nottingham delivered Live Online
Preventive and Predictive Maintenance
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) Preventive and Predictive maintenance are not new concepts. Both have been used across industry all over the world and when done properly, can yield impressive results (cost reductions of 20% or greater and a leap forward in equipment reliability and performance are very achievable). However, for every company using these concepts effectively, there are many others who are not. This 8 half-day Virtual Instructor Led Training (VILT) course has been derived from the Plant Performance Improvement Road Map developed by practitioners that guarantee the reliability of your operations. The VILT training focuses on how to improve profitability of any business by identifying the right maintenance strategy for any equipment. The aim of the VILT training is to help practitioners run programmes that will deliver real benefits as fast as possible with minimum zero wasted effort. The VILT training will also cover the core principles of Reliability Centred Maintenance, Total Productive Maintenance and Six Sigma and the increasingly important role of operations in achieving optimised asset performance. This is a certified course with the option of sitting for a short exam on the final day of the course to give participants the opportunity to gain a Certificate from petroEDGE and the Carcharodon Maintenance Academy. Training Objectives Master the critical skills by acquiring the following: An understanding of how maintenance can add profit The ability to develop improvement programmes that deliver maximum benefit in the shortest time A fundamental understanding of the principles of Preventive, Predictive and other maintenance types A practical understanding of the latest methods of solving problems at root cause level An appreciation of maintenance methodologies such as Reliability Centred Maintenance Strategies for ensuring your company gets value for money from your Contractors How to use the Maintenance Model of Excellence and Plant Performance Improvement Road Map Target Audience This VILT course has been designed for maintenance managers and engineers, reliability professionals, planners, project engineers, operations team members, and functional specialists. Training Methods The VILT course will be delivered online in 8 half-day sessions comprising 4 hours per day, with 2 breaks of 10 minutes per day. Course Duration: 8 half-day sessions, 4 hours per session (32 hours in total). Trainer Your expert course leader is an award-winning consultant and trainer with 30 years' experience in maintenance and reliability improvement. He has worked across five continents, in a wide variety of environments from the world's largest oil refinery to a small drinks production line. He has 10 years of maintenance management experience in the process industry, so he brings a very practical approach to training. He moved into consulting with ABB Eutech as their global maintenance specialist where he led maintenance and reliability best practice panels, delivered a wide range of maintenance improvement projects and trained other consultants. He is a fully qualified CMRP professional, an approved SMRP* Proctor, authorised to conduct CMRP exams and a globally respected maintenance consultant and best practice trainer. He founded his consultancy and training business in 2002 to focus on maintenance and reliability improvement. As part of this, he developed a range of maintenance 'models of excellence' with inputs from authors, international lecturers and some of the world's leading consultants and operators. His work has been recognised as being at the leading edge of industry best practice, winning independent awards such as the UK Chemical Industries Association 'Excellence in Engineering' award. He remains close to the industry as a respected specialist helping operating companies to achieve changes in performance. This ongoing field work enables him to continue to refine and extend best practice and the learning from this is continually fed into his training. His unique experience of facilitating two major turnarounds when the Coronavirus escalated into lockdown have given him a unique insight into how events of this type can disrupt maintenance. Moreover, his involvement in developing management processes and leading a Coronavirus response on a major industrial asset means he can talk with direct experience about how to cope and innovate in this global pandemic. *SMRP refers to Society of Maintenance and Reliability Professionals. PetroEdge is not affiliated with SMRP POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

Leadership Excellence for Senior Management
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Mid- and upper-level managers looking to hone their senior management skills will benefit from this course. Overview Use wisdom and understanding to lead others Deliver constructive critiques to your staff More effectively coach and mentor your staff Develop new managers Better motivate your staff Navigate organizational politics To maximize performance and foster a healthy environment, senior managers must also motivate others, nurturing and utilizing the distinctive skills of each team member. Private classes on this topic are available. We can address your organization?s issues, time constraints, and save you money, too. Contact us to find out how. Prerequisites While there are no prerequisites for this course, please ensure you have the right level of experience to be successful in this training. 1. Leading Others Comparing Vertical and Lateral Hierarchies- Leading in Different Structures of Command and Control Leveraging Your Organization\'s Structure Knowing Your Employees - Developing Empathy Beginning with the End in Mind and Back-Casting to the Desired Future State Setting S.M.A.R.T. Goals Earning Your Team\'s Trust with Honesty, Reliability, Availability, and Openness 2. Strategies for Course Correction Lighting a Fire- Motivating, Guiding, and Inspiring Resolving Conflict- Forcing, Accommodating, Avoiding, Compromising, and Collaborating Changing the Script- Trusting Your Team, Empowering Delegation, Celebrating Success, and Building & Reinforcing Your Team Defining Team Roles and Creating a Balanced Team 3. Effective Coaching and Mentoring Providing Clear and Timely Feedback Creating a Supportive Environment Building a Mentorship Plan - Mentoring for Success 4. Training New Managers Preparing, Developing, and Supporting New Managers Defining and Building Competencies Documenting Best Practices while Rewarding and Emulating Effective Managers Encouraging a Peer Network 5. Motivation Understanding the 8 Level Hierarchy of Needs Managing Across Generations Applying the CARE Model 6. Organizational Politics Being Politically Savvy, Ethical, and Effective Building Political Intelligence Understanding the Landscape 7. The Big Picture Thinking Through the Elements of Management

Coal Power Plant Life Cycle Management and Flexible Operations in Energy Transition - Decommissioning, Preservation, Repurposing and Recommissioning
By EnergyEdge - Training for a Sustainable Energy Future
Enhance your knowledge in coal power plant life cycle management and flexible operations with EnergyEdge. Learn about decommissioning, preservation, repurposing, and recommissioning.

CertNexus Certified Cyber Secure Coder (CSC-210)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is designed for software developers, testers, and architects who design and develop software in various programming languages and platforms, including desktop, web, cloud, and mobile, and who want to improve their ability to deliver software that is of high quality, particularly regarding security and privacy. This course is also designed for students who are seeking the CertNexus Cyber Secure Coder (CSC) Exam CSC-210 certification Overview In this course, you will employ best practices in software development to develop secure software.You will: Identify the need for security in your software projects. Eliminate vulnerabilities within software. Use a Security by Design approach to design a secure architecture for your software. Implement common protections to protect users and data. Apply various testing methods to find and correct security defects in your software. Maintain deployed software to ensure ongoing security... The stakes for software security are very high, and yet many development teams deal with software security only after the code has been developed and the software is being prepared for delivery. As with any aspect of software quality, to ensure successful implementation, security and privacy issues should be managed throughout the entire software development lifecycle. This course presents an approach for dealing with security and privacy throughout the entire software development lifecycle. You will learn about vulnerabilities that undermine security, and how to identify and remediate them in your own projects. You will learn general strategies for dealing with security defects and misconfiguration, how to design software to deal with the human element in security, and how to incorporate security into all phases of development. Identifying the Need for Security in Your Software Projects Identify Security Requirements and Expectations Identify Factors That Undermine Software Security Find Vulnerabilities in Your Software Gather Intelligence on Vulnerabilities and Exploits Handling Vulnerabilities Handle Vulnerabilities Due to Software Defects and Misconfiguration Handle Vulnerabilities Due to Human Factors Handle Vulnerabilities Due to Process Shortcomings Designing for Security Apply General Principles for Secure Design Design Software to Counter Specific Threats Developing Secure Code Follow Best Practices for Secure Coding Prevent Platform Vulnerabilities Prevent Privacy Vulnerabilities Implementing Common Protections Limit Access Using Login and User Roles Protect Data in Transit and At Rest Implement Error Handling and Logging Protect Sensitive Data and Functions Protect Database Access Testing Software Security Perform Security Testing Analyze Code to find Security Problems Use Automated Testing Tools to Find Security Problems Maintaining Security in Deployed Software Monitor and Log Applications to Support Security Maintain Security after Deployment

Natural Gas & LNG Sales Agreements
By EnergyEdge - Training for a Sustainable Energy Future
Enhance your knowledge of natural gas and LNG sales agreements with EnergyEdge course. Enroll now to gain valuable industry knowledge and skills.

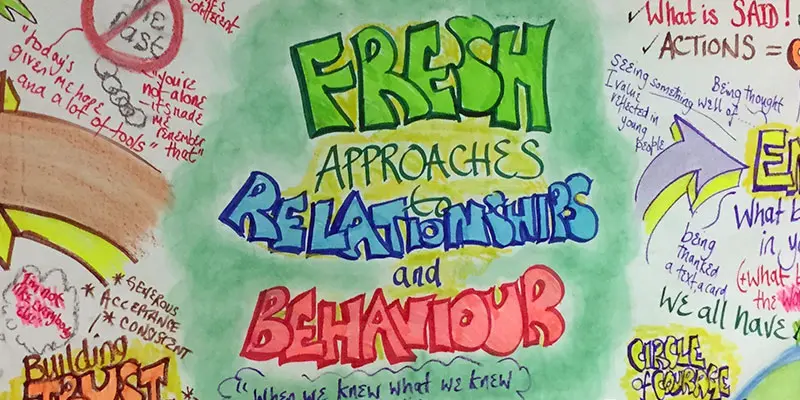
BEHAVIOUR: FRESH APPROACHES TO BEHAVIOUR AND RELATIONSHIPS
By Inclusive Solutions
This is our lead workshop/training day on behaviour and relationship work in Primary and Secondary schools and Academies, as well as Early Years, FE and adult settings and is both a values primer and a practical guide to successful innovative strategies for improving behaviour and strengthening relationships for challenging children and people of all ages. Course Category Behaviour and Relationships Meeting emotional needs Early Years Inclusion Description This is our lead workshop/training day on behaviour and relationship work in schools and other settings and is both a values primer and a practical guide to successful innovative strategies for improving behaviour and strengthening relationships for challenging children and young people of all ages. Not just another day on ‘Behaviour Management’ – our ‘Fresh Approaches to Behaviour and Relationships’ day goes well beyond a rewards and sanctions approach to ‘behaviour’. We will be focused on those young people for whom rewards and punishments do not always work and who confuse the adults who work with them. We aim to take a relationships based approach and to give those attending an opportunity to think more deeply about why young people do the things they do and what our part as adults is in creating, sustaining and changing these behaviours. The day gives those present opportunities to reflect on their attitudes and practice in relation to children’s behaviour and relationship building. If your usual approaches to managing behaviour aren’t working with particular individuals then take a tour through this range of cutting edge strategies for bringing about positive behaviour change, and for meeting challenging emotional needs. Testimonials ‘Thank you so much for the excellent training day you delivered last week. I found the whole experience quite uplifting and inspirational.’ ‘Thought provoking and empowering. Probably the best training day we’ve had in school’ ‘There was already evidence on the first day of school for pupils that staff were adopting a different approach. Thank you so much for helping us to make a difference.’ ‘Today has to have been one of the very best INSET days I have personally been to – full of practical tips and techniques to use in the classroom; and also proof that this approach does work in practice. It really was inspirational and an excellent start to the term.’ ‘Very motivating and exciting course.’ ‘Another fantastic Colin and Derek training session’ ‘Enjoyed this course very much. Derek and Colin worked very hard and I understood it. Thank you.’ Learning Objectives Reinforce and affirm good practice Re-energise, stimulate and challenge thinking about inclusion of challenging young people and children Increased understanding about behaviour and emotions Increased confidence in managing challenging pupils in childcare settings mainstream schools Access to a wider range of practical strategies to impact on behaviour problems Opportunity to reflect on professional attitudes and behaviour towards families and children and young people Learn new skills and processes to make inclusion successful Who Is It For ? Primary and secondary staff teams All Childcare Providers – Out of School club staff/Childminders/Youth Workers Early years and school based practitioners Heads and deputies SENCOs Advanced skills teachers Primary and secondary teachers Year Managers Parents Local authority support services Course Content The course answers the questions: Are there any new ways to include our most challenging young people? Should we focus on behaviour or relationships? How do we go about including high profile children or young people? Can we find an alternative to exclusion? What would a relationship policy look like? The following are some of the key themes and tools we are likely to explore during the day Getting the welcome right for the most challenging Encouraging – getting the best from the most challenging- Circle of Courage – belonging-achievement-generosity – independence Active listening – Listening to the person underneath the behaviour Compass of Shame – which directions do children and young people head when they feel shame? And what helps children work through these feelings in more healthy ways? Involving other children and young people in solutions and interventions – Circles of friends: peer support, counselling and mediation Team Problem Solving – Solution Circles: a 30 minute group problem solving process to get Teams ‘unstuck’ and to generate positive first action steps Circle of Adults: a process that ‘listens deeper’ to generate reflective problem solving creating lasting behaviour change and effective behaviour intervention plans. A particularly valuable process for those looking to enhance their leadership and facilitation skills Restorative justice and restitution: principles and practice of this approach to repairing harm and restoring relationships without reliance on punishment Understanding the effects of Separation, Loss, Trauma and Neglect on children’s learning and relationships in school and what adults can do to reach and support these children
Interior Design Visualization Professional Certificate
By ATL Autocad Training London
Who is this course for? The Interior Design Visualization Professional Certificate is perfect for individuals aspiring to launch their interior design business. Learn essential skills in AutoCAD, SketchUp, Photoshop, InDesign, Vray, and 3ds Max. If you prefer to book over the phone, simply call 02077202581. Click here for more info: Website Duration: 120 hours. 1-on-1 Training. When can I book: (Choose your preferred day and time once a week). Monday to Saturday: 9 am - 7 pm (Flexible timing with advance booking). Module 1: Introduction to Interior Design Visualization (4 hours) Understanding the Significance of Visualization in Interior Design Familiarity with Software Used: AutoCAD, 3ds Max, SketchUp, V-Ray, Photoshop, and InDesign Workflow Overview and Best Practices for Interior Design Visualization Module 2: AutoCAD for Interior Design (16 hours) Basics of AutoCAD and Its Interface Utilizing Drawing and Editing Tools for Accurate Floor Plans and Elevations Creating and Modifying 2D and 3D Objects Application of Layers, Line Types, and Hatches for Clarity Precision in Measurements and Annotations Module 3: 3ds Max for Interior Design (16 hours) Introduction to 3ds Max Interface Furniture, Fixtures, and Architectural Element Modeling Techniques Material and Texture Application for Realism Lighting Strategies for Interior Scenes V-Ray Introduction for High-Quality Rendering Scene Setup and Camera Placement for Effective Visualization Module 4: SketchUp for Interior Design (12 hours) Introduction to SketchUp and Its Interface Creating 3D Models of Interiors, Furniture, and Objects Enhancing Visuals with Materials and Textures Efficient Use of SketchUp Plugins and Extensions Seamless File Exchange Between SketchUp and Other Software Module 5: V-Ray for Interior Design Rendering (12 hours) Principles of Photorealistic Rendering Installation and Setup of V-Ray in 3ds Max and SketchUp Configuring V-Ray Settings for Optimal Rendering Advanced Material Application for Realistic Surfaces Lighting Techniques for Atmosphere and Mood Creation Module 6: Photoshop for Interior Design Visualization (12 hours) Introduction to Photoshop Interface Image Enhancement: Color, Contrast, and Saturation Adjustments Post-Processing Effects for a Polished Look Integration of 2D Elements like Textures and Patterns Creating Composite Images Using Multiple Render Passes Module 7: InDesign for Portfolio Presentation (8 hours) Introduction to InDesign Interface Designing a Visually Appealing Portfolio Layout Effective Organization and Presentation of Interior Design Visualizations Integration of Images, Text, and Graphics for Cohesive Portfolios Portfolio Export for Print and Digital Distribution Module 8: Project Work and Final Presentation (4 hours) Application of Learned Skills on a Comprehensive Interior Design Visualization Project Refinement and Polish under Instructor's Guidance Preparation and Delivery of Final Presentation Showcasing the Project Note: The course outline encompasses 80 instructional hours. The actual duration may vary based on class pace and additional practice and project work. Final Project (With Full-Time Tutor Assistance): Students will develop and present their best work in a final presentation at the end of the course. Projects are to be submitted via email to training@realanimationworks.com, and timely submission is crucial to avoid delays or interruption of sessions. Please be aware: Failure to attend a session or notify us of absence within 48 hours of the session time results in session loss and full class fee charges due to the personalized nature of the sessions. Students can request breaks or extended pauses by providing written notice through email. Benifits and Jobs after this course: Master Design Tools: Proficiency in AutoCAD, 3ds Max, SketchUp, V-Ray, Photoshop, and InDesign for interior design visualizations. Advanced 3D Skills: Expertise in detailed 3D modeling, realistic rendering, and precise lighting techniques. Portfolio Development: Create compelling portfolios using InDesign, blending images and text professionally. Career Opportunities: Interior Visualization Specialist 3D Modeler Architectural Visualizer Interior Design Consultant Digital Content Creator Freelance Interior Visualizer Virtual Reality Designer Educator/Trainer Certificate Program in Interior Design Visualization: Maintain a dedicated notebook for effective organization of study notes. Schedule makeup sessions for missed coursework, subject to available time slots. Keep detailed records and create a specialized design folder to monitor progress and nurture creative ideas. Allocate focused time for self-guided practice and project work. Receive certification from our esteemed professional design team upon successful completion of the program. Post-Program Achievements: Upon completion of the certificate program, you will: Gain confidence in software proficiency and a strong understanding of underlying principles. Demonstrate the ability to create high-quality visual representations for architectural and interior design projects. Feel well-prepared for career opportunities, backed by your software expertise. Ongoing Support: We are pleased to offer lifelong complimentary email and phone support, ensuring swift assistance with any inquiries or challenges you may face. Software Access: Access to necessary software is available via download from the developer's website or at student-friendly rates. Please note that student software usage is limited to non-commercial projects. Payment Flexibility: Choose from various payment options including internet bank transfers, credit cards, debit cards, and PayPal. Additionally, we offer installment plans tailored to our students' needs.

Effective Personal Productivity
By Leadership Management International (LMI) UK
Effective Personal Productivity will help you in four crucial areas: Become highly organised and effective in your own area of day-to-day responsibility. Set and track personal and team goals, manage priorities and hit project deadlines. Improve delegation and communication skills, ensuring the right work is done the right way by the right people. Identify areas for continual improvement in and outside of work and implement strategies to maintain a healthy, well-balanced life.

MENTAL HEALTH – UNDERSTANDING AND MEETING NEEDS
By Inclusive Solutions
In this course we explore Mental Health and address how such needs can be met in mainstream classrooms. Course Category Behaviour and Relationships Meeting Emotional Needs Description This is our lead workshop/training day on understanding mental health, behaviour and relationship work in schools other settings and is both a values primer and a practical guide to successful innovative strategies for improving behaviour and strengthening relationships for challenging children and young people of all ages. Not just another day on ‘Behaviour Management’ – Our Mental Health Day goes well beyond a rewards and sanctions approach to ‘behaviour’. We will be focused on those young people for whom rewards and punishments do not always work and who confuse the adults who work with them. We aim to take a relationships-based approach and to give those attending an opportunity to think more deeply about why young people do the things they do and what our part as adults is in creating, sustaining and changing these behaviours. The day gives those present opportunities to reflect on their attitudes and practice in relation to children’s behaviour and relationship building. If your usual approaches to managing tackling mental health needs aren’t working with particular individuals then take a tour through this range of cutting edge strategies for bringing about positive behaviour change, and for meeting challenging emotional needs Learning Objectives reinforce and affirm good practice re-energise, stimulate and challenge thinking about inclusion of challenging pupils and children increased understanding of mental health increased confidence in managing challenging pupils in mainstream schools access to a wider range of practical strategies to impact on behaviour problems opportunity to reflect on professional attitudes and behaviour towards mental health in families and pupils Who Is It For ? Anyone concerned with understanding and meeting emotional and mental health needs Course Content Circle of Courage – belonging-achievement-generosity – independence – model for understanding mental health Compass of Anxiety – understanding and going deeper Active listening – Listening to the person underneath the behaviour Involving other children and young people in solutions and interventions - Circles of friends: peer support, counselling and mediation Team Problem Solving – Solution Circles: a 30 minute group problem solving process to get Teams ‘unstuck’ and to generate positive first action steps Restorative justice and restitution: principles and practice of this approach to repairing harm and restoring relationships without reliance on punishment Understanding the effects of Separation, Loss, Trauma and Neglect on children’s learning and relationships in school and what adults can do to reach and support these children

Architecting on AWS
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is intended for solutions architects, solution-design engineers, developers seeking an understanding of AWS architecting and individuals seeking the AWS Solutions Architect-Associate certification. Overview Identify AWS architecting basic practices. Explore using the AWS management tools: The AWS Console, Command Line Interface (CLI), and CloudFormation in a lab environment. Examine the enforcement of accounts security using policies. Identify the elements that build an elastic, secure, virtual network that includes private and public subnets. Practice building an AWS core networking infrastructure. Determine strategies for a layered security approach to Virtual Private Cloud (VPC) subnets. Identify strategies to select the appropriate compute resources based on business use-cases. Practice building a VPC and adding an Elastic Cloud Compute (EC2) instance in a lab environment. Practice installing an Amazon Relational Database Service (RDS) instance and an Application Load Balancer (ALB) in the VPC you created. Compare and contrast AWS storage products and services, based on business scenarios. Compare and contrast the different types of AWS database services based on business needs. Practice building a highly available, auto-scaling database layer in a lab. Explore the business value of AWS monitoring solutions. Identify the role of monitoring, event driven load balancing, and auto scaling responses, based on usage and needs. Identify and discuss AWS automation tools that will help you build, maintain and evolve your infrastructure. Discuss network peering, VPC endpoints, gateway and routing solutions based on use-cases. Discuss hybrid networking configurations to extend and secure your infrastructure. Discuss the benefits of microservices as an effective decoupling strategy to power highly available applications at scale. Explore AWS container services for the rapid implementation of an infrastructure-agnostic, portable application environment. Identify the business and security benefits of AWS serverless services based on business examples. Practice building a serverless infrastructure in a lab environment. Discuss the ways in which AWS edge services address latency and security. Practice building a CloudFront deployment with an S3 backend in a lab environment. Explore AWS backup, recovery solutions, and best practices to ensure resiliency and business continuity. Build a highly available and secure cloud architecture based on a business problem, in a project-based facilitator-guided lab. Architecting on AWS is for solutions architects, solution-design engineers, and developers seeking an understanding of AWS architecting. In this course, you will learn to identify services and features to build resilient, secure and highly available IT solutions on the AWS Cloud. Architectural solutions differ depending on industry, types of applications, and business size. AWS Authorized Instructors emphasize best practices using the AWS Well-Architected Framework, and guide you through the process of designing optimal IT solutions, based on real-life scenarios. The modules focus on account security, networking, compute, storage, databases, monitoring, automation, containers, serverless architecture, edge services, and backup and recovery. At the end of the course, you will practice building a solution and apply what you have learned with confidence. Prerequisites AWS Cloud Practitioner Essentials classroom or digital training, or Working knowledge of distributed systems Familiarity with general networking concepts Familiarity with IP addressing Working knowledge of multi-tier architectures Familiarity with cloud computing concepts 0 - Introductions & Course Map review Welcome and course outcomes 1 - Architecting Fundamentals Review AWS Services and Infrastructure Infrastructure Models AWS API Tools Securing your infrastructure The Well-Architected Framework Hands-on lab: Explore Using the AWS API Tools to Deploy an EC2 Instance 2 - Account Security Security Principals Identity and Resource-Based Policies Account Federation Introduction to Managing Multiple Accounts 3 - Networking, Part 1 IP Addressing Amazon Virtual Private Cloud (VPC), Patterns and Quotas Routing Internet Access Network Access Control Lists (NACLs) Security Groups 4 - Compute Amazon Elastic Cloud Compute (EC2) EC2 Instances and Instance Selection High Performance Computing on AWS Lambda and EC2, When to Use Which Hands-On Lab: Build Your Amazon VPC Infrastructure 5 - Storage Amazon S3, Security, Versioning and Storage Classes Shared File Systems Data Migration Tools 6 - Database Services AWS Database Solutions Amazon Relational Database Services (RDS) DynamoDB, Features and Use Cases Redshift, Features, Use Cases and Comparison with RDS Caching and Migrating Data Hands-on Lab: Create a Database Layer in Your Amazon VPC Infrastructure 7 - Monitoring and Scaling Monitoring: CloudWatch, CloudTrail, and VPC Flow Logs Invoking Events 8 - Automation CloudFormation AWS Systems Manager 9 - Containers Microservices Monitoring Microservices with X-Ray Containers 10 - Networking Part 2 VPC Peering & Endpoints Transit Gateway Hybrid Networking Route 53 11 - Serverless Architecture Amazon API Gateway Amazon SQS, Amazon SNS Amazon Kinesis Data Streams & Kinesis Firehose Step Functions Hands-on Lab: Build a Serverless Architecture 12 - Edge Services Edge Fundamentals Amazon CloudFront AWS Global Accelerator AWS Web Application Firewall (WAF), DDoS and Firewall Manager AWS Outposts Hands-On Lab: Configure an Amazon CloudFront Distribution with an Amazon S3 Origin 13 - Backup and Recovery Planning for Disaster Recovery AWS Backup Recovery Strategie Additional course details: Nexus Humans Architecting on AWS training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Architecting on AWS course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
