- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
585 Courses in Liverpool delivered Live Online
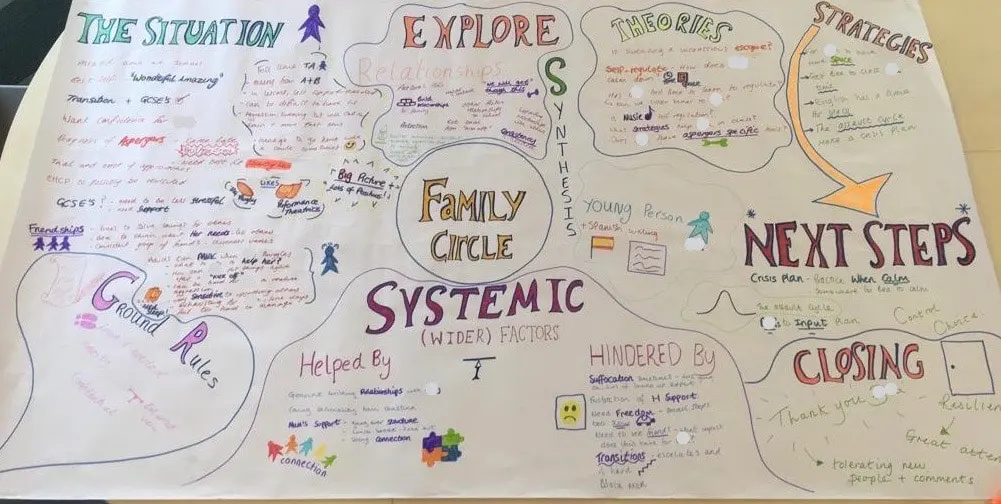
FAMILY CIRCLES
By Inclusive Solutions
Click to read more about this training, in which we demonstrate a live problem solving approach which is based on the active participation of family members. Course Category Inclusion Parents and Carers Behaviour and relationships Problem Solving Description In this training we demonstrate a live problem solving approach which is based on the active participation of family members. ‘Family Circles’ is an evolving new approach to problem solving with families and is based on our years of family work and the development and use of the Circle of Adults process. Inspired by our own Parent Solutions work and the Circle of Adults process as well as Family Group Conferencing and other Restorative Interventions we bring you Family Circles. Essentially the approach involves gathering a family together for a process that is facilitated but majors on the family members offering each other their wisdom and ideas. The approach is capacity focused, person centred approach to working with families rather than the dominant deficit oriented and ‘medical model’ of viewing and planning for or doing things to families. This training can be modelled with a group of professionals or better still with a family. In our work with families we develop the importance of naming stories or theories and seeking linkages and synthesis between what is found out and explored about the family situation and its history. We like participants to sit with the uncertainty, to reflect on the question ‘why’ but without judgement of each other. Deeper reflections may span a whole range of perspectives from ‘within person’ considerations, to situational or systemic possibilities. Health or emotional issues can be reflected on alongside organisational or transactional aspects of what is going on for the family. The better the shared understanding the better the strategy or actions which emerge from these meetings. Quality hypotheses with a close fit to reality lead to more effective implementation in the real world. We encourage ‘loose’ thinking, a search for connections, deeper listening, an ‘open mind’, speculation and exploration without moral judgements. From this stance self-reflection as well as reflection on the situation can produce remarkable insights. The quality of theories or new stories generated is directly influenced by family members’ experiences and the models of learning, behaviour and emotion, systems, educational development, change and so on that they have been exposed to. Learning Objectives To provide opportunities for: Shared problem solving in a safe exploratory climate in which the family will find its own solutions. Individuals to reflect on their own actions and strategies An exploration of whole-family processes and their impact Emotional support and shared understandings of issues at a child, parent, family, school and community level. Feed back to each other on issues, ideas and strategies that are agreed to be worth sharing with them. Who Is It For? Anyone interested in working with families in a way that builds and makes use of their capacities rather than focus on their challenges and difficulties. Social Care teams School staff Community organisers Educational Psychologists Course Content True family empowerment Deepening shared stories and understandings Facilitating groups Problem solving process Handling family group communication Allowing direct feedback and challenge between participants in a safe way Building relationships Process: Family members are welcomed: Introductions are carried out, ground rules and aims clarified whilst coffee is drunk. A recap from the last session is carried out: To follow up developments and reflections after the last meeting. One issue is selected for the main focus Issue presentation: The family member who raised the concern is asked questions to tell the ‘story’ of the issue or problem. Additional questions/information from the group about the problem are gathered: Ground rules may need to be observed carefully here. Individual participants need to be kept focused and prevented from leaping to premature conclusions or to making ‘helpful’ suggestions about strategy. Relationship aspects to the problem are explored. Metaphors and analogies are invited. How would a fly on the wall see your relationship? If you were alone together on a desert island, what would it be like? Impact of previous relationships/spillage from one relationship to another are explored. Eg what situation they are reminded of? For instance, does this situation remind you of any of those angry but helpless feelings you had with your other son when he was an adolescent? This provides opportunities to reflect on how emotions rub off on other people. The parent feels really frustrated, and on reflection we can see that so does the child System/Organisation factors (Family system/school and community systems and so on): What aspects help or hinder the problem? For instance, does the pastoral system of the local school provide space, or time and skilled personnel able to counsel this young person and work actively with their parents? Synthesis. At this stage the Graphic facilitator summarises what they have heard. They then go on to describe linkages and patterns in what they have heard. This can be very powerful. The person doing the graphic work has been able to listen throughout the presentation process and will have been struck by strong messages, emotions and images as they have arisen. The story and meaning of what is happening in the situation may become a little clearer at this point. Typical links may be ‘mirrored emotions’ strong themes such as loss and separation issues, or repeated processes such as actions triggering rejection. This step provides an excellent grounding for the next process of deepening understanding. What alternative strategies/interventions are open to be used? Brainstormed and recorded. ’Either/ors’ need to be avoided at this time also. This needs to be a shared session in which the family member who is presenting the concern contributes as much as anyone. Care is needed to ensure that this person is not overloaded with other people’s strategies. The final selection of strategy or strategies from the brainstormed list is the problem presenter’s choice. Strategies might include: a special time for the young person, a meeting with the child’s parents to explore how she is being managed at home and to share tactics, a home-school diary, counselling, or an agreed action plan that all are aware of, agreed sanctions and rewards and so forth. Strategies may productively involve processes of restitution and restoration, when ‘sorry’ is not enough. Making it right, rather than punishments or rewards, may then becomes the focus. First Steps. The problem presenter is finally asked to agree one or two first steps which they can carry out over the next 3-7 days. It can help to assign a ‘coach’ who will check in with them to ensure they have carried out the action they have named. This is a time to be very specific. Steps should be small and achievable. The person is just ‘making a start’. A phone call, or making an agreement with a key other person not present at the meeting would be ideal examples. Final reflections. Sometimes referred to as a ‘round of words’ help with closure for all involved. Reflections are on the process not the problem. In large families this is best done standing in a circle. In smaller groups all can remain sitting. Passing around a ‘listening stick’ or something similar such as a stone or light heighten the significance of the process ending and improve listening. Finally the problem presenter is handed the ‘Graphic’ this is their record of the meeting and can be rolled and presented ceremoniously by the facilitators for maximum effect! If you liked this course you may well like: Parent Solutions
SAFe for Government: In-House Training
By IIL Europe Ltd
SAFe® for Government: In-House Training Transitioning to Lean-Agile practices for building technology-based capabilities is especially challenging in the government context. But issues of legacy governance, contracting, and organizational barriers can be overcome with the right information and strategies. During this course, attendees will learn the principles and practices of the Scaled Agile Framework® (SAFe®), how to execute and release value through Agile Release Trains, and what it means to lead a Lean-Agile transformation of a program inside a government agency. Attendees gain an understanding of the Lean-Agile mindset and why it's an essential foundation for transformation. They'll also get practical advice on building high-performing, multi-vendor Agile teams and programs, managing technology investments in Lean flow, acquiring solutions with Agile contracting, launching the program, and planning and delivering value using SAFe®. Attendees also learn how specific leadership behaviors can drive successful organizational change in government. What you will Learn To perform the role of a SAFe® for Government leader, you should be able to: Transition government programs from traditional software and systems development models to Lean-Agile and DevOps mindsets, principles, and practices using SAFe® Adapt technology strategy, budgeting and forecasting, acquisition, compliance, and governance processes to flow-based practices using emerging government guidelines Organize government programs into one or more Agile Release Trains (ARTs) and execute in Program Increments (PIs) Explore Large Solution coordination in a government and multi-vendor environment Identify and internalize the mindset and leader behaviors essential to successful Lean-Agile transformation Follow success patterns for SAFe® implementations adapted to the government context Build a preliminary outline of next steps to begin and / or accelerate the SAFe® implementation in your program or agency Advancing Lean-Agile in government Embracing a Lean-Agile mindset Understanding SAFe® Principles Creating high-performing Agile teams and programs Planning with cadence and synchronization Delivering value in Program Increments Mapping the path to agency and program agility Leading successful change

Rent to Rent - A Hungry Entrepreneur Strategy
By Property SQ2
Build a rent to rent business using a proven system

Scrum Master Workshop: In-House Training
By IIL Europe Ltd
Scrum Master Workshop: In-House Training A Scrum Master helps project teams properly use the Scrum framework, increasing the likelihood of the project's overall success. Scrum Masters understand Scrum values, practices, and applications and provide a level of knowledge and expertise above and beyond that of typical project managers. Scrum Masters act as 'servant leaders', helping the rest of the Scrum Team work together and learn the Scrum framework. Scrum Masters also protect the team from both internal and external distractions. What you will Learn You'll learn how to: Comprehend the Agile Manifesto and mindset Explain the fundamental principles of Scrum Guide the Scrum team in their responsibilities Write requirements in the form of user stories Define Ready and Done Estimate using planning poker and prioritize using MoSCoW Facilitate the team through the 5 Sprint events Fulfill the role of Scrum Master in a Scrum project Create Information Radiators to enable transparency Define the structure of the retrospective Foundation Concepts Agile History, Values, and Mindset Introduction to Scrum Scrum events Scrum artifacts Scrum Roles and Responsibilities Product Owner responsibilities Scrum Master responsibilities The Team responsibilities Cross-functional Teams Building Effective Teams The Product Backlog and User Stories The Product Backlog User Stories Definition of Done Backlog grooming Estimating User Stories Story points, planning poker Prioritizing User Stories The Sprint Team capacity and velocity The Sprint Planning Meeting The Sprint Backlog The Sprint Learning to self-manage, self-organize, self-improve Sprint Review and Retrospective Project Progress and Completion The Daily Scrum The Task Board and The Burndown Chart Information Radiators Closing a Scrum Project Summary and Next Steps Review of course goals, objectives, and content

SAFe for Government: Virtual In-House Training
By IIL Europe Ltd
SAFe® for Government: Virtual In-House Training Transitioning to Lean-Agile practices for building technology-based capabilities is especially challenging in the government context. But issues of legacy governance, contracting, and organizational barriers can be overcome with the right information and strategies. During this course, attendees will learn the principles and practices of the Scaled Agile Framework® (SAFe®), how to execute and release value through Agile Release Trains, and what it means to lead a Lean-Agile transformation of a program inside a government agency. Attendees gain an understanding of the Lean-Agile mindset and why it's an essential foundation for transformation. They'll also get practical advice on building high-performing, multi-vendor Agile teams and programs, managing technology investments in Lean flow, acquiring solutions with Agile contracting, launching the program, and planning and delivering value using SAFe®. Attendees also learn how specific leadership behaviors can drive successful organizational change in government. What you will Learn To perform the role of a SAFe® for Government leader, you should be able to: Transition government programs from traditional software and systems development models to Lean-Agile and DevOps mindsets, principles, and practices using SAFe® Adapt technology strategy, budgeting and forecasting, acquisition, compliance, and governance processes to flow-based practices using emerging government guidelines Organize government programs into one or more Agile Release Trains (ARTs) and execute in Program Increments (PIs) Explore Large Solution coordination in a government and multi-vendor environment Identify and internalize the mindset and leader behaviors essential to successful Lean-Agile transformation Follow success patterns for SAFe® implementations adapted to the government context Build a preliminary outline of next steps to begin and / or accelerate the SAFe® implementation in your program or agency Advancing Lean-Agile in government Embracing a Lean-Agile mindset Understanding SAFe® Principles Creating high-performing Agile teams and programs Planning with cadence and synchronization Delivering value in Program Increments Mapping the path to agency and program agility Leading successful change

LTE Airside training course description This course provides a concise insight into the LTE airside. Key parts of the course are detailed looks at the air interface protocol stack, cell acquisition, transmission and reception of data and of he layer 1 procedures along with layer 2 procedures. What will you learn Explain the RF optimisation flowchart. Describe the importance of Reference Signal Received Power (RSRP). List many of the 3GPP recommended KPIs. Describe the concept of APN AMBR and UE AMBR within LTE. Describe the use of planning and optimisation computer tools. LTE Airside training course details Who will benefit: Anyone working with LTE. Prerequisites: Essential LTE Duration 2 days LTE Airside training course contents Introduction and review of LTE This section describes the requirements of LTE and key technical features, and reviews the system architecture. LTE Architecture, UE, E-UTRAN and EPC. Specifications. OFDMA, SC-FDMA and MIMO antennas This section describes the techniques used in the LTE air interface, notably orthogonal frequency division multiple access (OFDMA) and multiple input multiple output (MIMO) antennas. Communication techniques for fading multipath channels. OFDMA, FFT processing and cyclic prefix insertion. SC-FDMA in the LTE uplink. Multiple antenna techniques including transmit & receive diversity and spatial multiplexing. Introduction to the air interface This section covers the operation of the air interface, the channels that it uses, and the mapping to the time and frequency domains of OFDMA and SC-FDMA. Air interface protocol stack. Logical, transport and physical channels. Frame and slot structure, the resource grid. Resource element mapping of the physical channels and physical signals. LTE spectrum allocation. Cell acquisition This is the first of three sections covering the air interface physical layer. Here, we cover mobile procedures to start low-level communications with the cell, and base station transmission of the corresponding information. Primary/secondary synchronisation signals. Downlink reference signals. The master information block. Physical control format indicator channel. Organisation and transmission of the system information. Data transmission and reception In this section, we cover procedures used for data transmission and reception on the shared channels, and describe in detail the individual steps. Data transmission and reception on the uplink and downlink. Scheduling commands and grants on the PDCCH. DL-SCH and UL-SCH. Physical channel processing of the PDSCH and PUSCH. Hybrid ARQ indicators on the PHICH. Uplink control information on the PUCCH. Uplink demodulation and sounding reference signals. Additional physical layer procedure This section concludes our discussion of the air interface physical layer, by discussing a number of procedures that support its operation. Transmission of the physical random access channel. Contention and non-contention based random access procedures. Discontinuous transmission in idle and connected modes. Uplink power control and timing advance. Air interface layer 2 This section describes the architecture and operation of layer 2 of the air interface protocol stack. MAC protocol, interactions with the physical layer, use for scheduling. RLC protocol, transparent, unacknowledged and acknowledged modes. PDCP, including header compression, security functions and recovery from handover.

Executive Coaching provides a safe space for leaders to explore new ideas and techniques without judgement, fostering personal growth and benefiting the wider business. Sessions are confidential, 90 minutes long, and tailored to individual developmental needs, with a bi-weekly schedule of six sessions suggested. These sessions are conducted via Zoom, with face-to-face options available in East Anglia and London; email engage@puritas.org.uk for details.

Scrum Master and Product Owner Workshop: Virtual In-House Training
By IIL Europe Ltd
Scrum Master and Product Owner Workshop: Virtual In-House Training This workshop builds on the specific roles and responsibilities of the Product Owner and Scrum Master in a Scrum environment, and how they need to work together as part of the Scrum methodology. During these sessions, you will explore who does what before, during, and after the Scrum Sprint cycles, as well as how to make the process work best in your specific Agile environment. You will come away from this workshop with a much deeper understanding of the roles and responsibilities so that individual performance improves on the job. Improved target results include providing focused leadership, making effective decisions, guiding Agile teams, and delivering business value. Foundation Concepts Agile History, Values, and Mindset Introduction to Scrum Scrum Events Scrum Artifacts Scrum Roles and Responsibilities Scrum Roles Product Owner Responsibilities Scrum Master Responsibilities The Scrum Team Responsibilities Cross-functional Teams Product Ownership Product Ownership Vision Understand Your Customers and Market Stakeholder Management and Engagement Product Backlog What is a User Story? Epics and User Stories Acceptance Criteria Preparing User Stories for a Sprint Definition of Ready (DoR) and Definition of Done (DoD) User Story Estimation Using Planning Poker Backlog Grooming Roadmaps, Story Maps, Impact Mapping Product Backlog Prioritization, MoSCoW, Kano Analysis Technical Debt The Sprint Team Capacity and Velocity Planning Sprint Planning Meeting and Sprint Plan The Sprint: Learning to Become Self-managing, Self-organizing, Self-improving Sprint Review Meeting Retrospectives Project Progress and Completion The Daily Scrum The Task Board and The Burndown Chart Information Radiators Closing a Scrum Project Summary and Next Steps Review of course goals, objectives, and content

BGP training course description A detailed study of BGP, from the basics of how it works through to advanced issues such as route reflectors, policy, filtering, route selection and routing registries. The course culminates with a study of an industrial strength BGP template illustrating important issues such as bogon filtering. Practical hands on with routers follow the major sessions to reinforce the theory. A multiple choice exam, leading to the LAIT III certification, is available after the course. The exam consists of 60 questions and lasts 2 hours. What will you learn Connect enterprises to the Internet, and ISPs to each other. Describe how BGP works. List, describe and configure the main BGP attributes. Implement and troubleshoot BGP. Work with route aggregation and calculate CIDR prefixes in seconds. Influence traffic paths with BGP. BGP training course details Who will benefit: Anyone who will be working with BGP. Prerequisites: TCP/IP Foundation for engineers Definitive IP routing for engineers. Duration 5 days BGP training course contents Basic BGP IGPs, EGPs, What's BGP? BGP RIB, in/out process, tables peers, adding routes. Hands on Simple configuration and troubleshooting. The Internet and peering ASs, AS numbers, Internet structure, ISP types, ISP network design, IXs, peering vs. transit, public/ private peering, bi/multi-lateral peering. Hands on AS information gathering. How BGP works Incremental updates, Path vector protocols, BGP protocol stack, the BGP header, message types, NLRI, withdrawn routes, route refresh, route dampening. Hands on More troubleshooting, packet analysis. MBGP and IPv6 Multiprotocol routing, AFI, SAFI, MBGP and multicasts, IPv6, MPLS VPNs. Hands on IPv6 BGPv4 aggregation CIDR, benefits, techniques, shortcuts, configuring BGP aggregation, leaking routes. Hands on Reducing routing table size. BGP path selection BGP attributes, attribute types, route selection order, Local preference, AS prepend, MEDs. Hands on Influencing traffic with BGP. BGP routing policies What is policy? Examples, route filtering, AS filtering, REs, applying preference selectively, peer groups. Hands on Sophisticated policies. RIPE and routing registries RIRs, Allocations, assignments, PI vs. PA. Objects, RPSL, routing registry, Hands on The RIPE database. Automating BGP configuration Automation tools, whois, IRRToolSet, Bogon lists, tracking bogon lists, HTTP, Peering, routing registries, DNS. Communities What is a community? Community names, communities for: peer types and geography. RFC 1998, default communities. Hands on Setting local preference on other routers. Route servers What are route servers? LINX route servers, route server policy control, What are route collectors, Looking glasses. Hands on Setting up and working with a route server. Peer relationships IBGP, EBGP, next hop self, advertising routes into/out of BGP, synchronisation. Hands on IBGP, troubleshooting a large BGP network. Route reflectors and confederations Full mesh IBGP, Route reflectors, RR configuration and design, confederations, migration issues. Hands on RR configuration. BGP architectures Stub vs. transit AS, when to use BGP, multihoming strategies and issues, default routes. Multihop EBGP, load balancing. Hands on Multihoming. BGP security RFC 7454, security steps, BGP TTL security, filters, RPKI, ROAs, rsync, rrdp, validators. A secure BGP template. Hands on RPKI prefix validation.

LINX 3 training course description A detailed study of BGP, from the basics of how it works through to advanced issues such as route reflectors, policy, filtering, route selection and routing registries. The course culminates with a study of an industrial strength BGP template illustrating important issues such as bogon filtering. Practical hands on with routers follow the major sessions to reinforce the theory. A multiple choice exam, leading to the LAIT III certification, is available after the course. The exam consists of 60 questions and lasts 2 hours. What will you learn Connect enterprises to the Internet, and ISPs to each other. Describe how BGP works. List, describe and configure the main BGP attributes. Implement and troubleshoot BGP. Work with route aggregation and calculate CIDR prefixes in seconds. Influence traffic paths with BGP. LINX 3 training course details Who will benefit: Network engineers. Prerequisites: LAIT I and II OR CCNP and take LAIT I and LAIT II exams whilst on this course. Duration 5 days LINX 3 training course contents Basic BGP IGPs, EGPs, What's BGP? BGP RIB, in/out process, tables peers, adding routes. Hands on Simple configuration and troubleshooting. The Internet and peering ASs, AS numbers, Internet structure, ISP types, ISP network design, IXs, peering vs. transit, public/ private peering, bi/multi-lateral peering. Hands on AS information gathering. How BGP works Incremental updates, Path vector protocols, BGP protocol stack, the BGP header, message types, NLRI, withdrawn routes, route refresh, route dampening. Hands on More troubleshooting, packet analysis. MBGP and IPv6 Multiprotocol routing, AFI, SAFI, MBGP and multicasts, IPv6, MPLS VPNs. Hands on IPv6 BGPv4 aggregation CIDR, benefits, techniques, shortcuts, configuring BGP aggregation, leaking routes. Hands on Reducing routing table size. BGP path selection BGP attributes, attribute types, route selection order, Local preference, AS prepend, MEDs. Hands on Influencing traffic with BGP. BGP routing policies What is policy? Examples, route filtering, AS filtering, REs, applying preference selectively, peer groups. Hands on Sophisticated policies. RIPE and routing registries RIRs, Allocations, assignments, PI vs. PA. Objects, RPSL, routing registry, Hands on The RIPE database. Automating BGP configuration Automation tools, whois, IRRToolSet, Bogon lists, tracking bogon lists, HTTP, Peering, routing registries, DNS. Communities What is a community? Community names, communities for: peer types and geography. RFC 1998, default communities. Hands on Setting local preference on other routers. Route servers What are route servers? LINX route servers, route server policy control, What are route collectors, Looking glasses. Hands on Setting up and working with a route server. Peer relationships IBGP, EBGP, next hop self, advertising routes into/out of BGP, synchronisation. Hands on IBGP, troubleshooting a large BGP network. Route reflectors and confederations Full mesh IBGP, Route reflectors, RR configuration and design, confederations, migration issues. Hands on RR configuration. BGP architectures Stub vs. transit AS, when to use BGP, multihoming strategies and issues, default routes. Multihop EBGP, load balancing. Hands on Multihoming. BGP security RFC 7454, security steps, BGP TTL security, filters, RPKI, ROAs, rsync, rrdp, validators. A secure BGP template. Hands on RPKI prefix validation.
