- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
2552 Courses in Cardiff delivered Live Online
3ds max and Arnold Rendering one to one.
By Real Animation Works
Realistic rendering course with 3ds max and Arnold.

TOGAF® EA Course - Foundation and Practitioner (Level 1 and 2)
By Advised Skills
This course is designed to enable candidates to develop the knowledge of the terminology and basic concepts of TOGAF Standard, 10th Edition and principles of Enterprise Architecture. Candidates will also be able to analyze and apply knowledge of TOGAF Standard.

Critical Thinking and Creative Problem Solving (Virtual)
By IIL Europe Ltd
Critical Thinking and Creative Problem Solving (Virtual) Two critical skillsets for the future of work are critical thinking and creative problem solving. These modes of working and thinking intersect and overlap; both are necessary and both can be taught. Having the ability to exercise creativity while at the same time applying structure and discipline to the thinking process is a key competency in the twenty-first century workplace. This course explores the interplay between critical and creative thinking, and the necessity of each to effective problem solving and decision making. Participants will learn a variety of techniques to apply critical thinking to real-life scenarios. They will experiment with different problem-solving approaches and will learn about cognitive influences on our decisions and choices. The course delves into the business value of creativity and involves participants in actively integrating criticality, creativity, and problem solving. What you will Learn At the end of this program, you will be able to: Explain basic concepts of problem solving Infer types of cognitive biases that impact decision making Utilize types of root cause analysis Differentiate among obstacles to sound decision making Apply a variety of problem-solving approaches / processes to existing challenges Evaluate alternative solution methods using various techniques Analyze real world problem scenarios to determine the lateral thinking type needed to address them Getting Started Foundation Concepts Definitions Thinking modes and cognitive bias Basic problem-solving framework Problem Definition and Solution Generation Root cause analysis Basic problem-solving obstacles Generating alternative solutions Evaluating Alternatives Critical thinking guidelines Obstacles to sound decision making Tools for evaluating alternatives Exploring Lateral Thinking Problem-solving challenge Workplace application Summary and Next Steps

Transitioning into Leadership for an IT Manager
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for IT Professionals who expect to or who have recently transitioned into a management role will benefit from this course. Overview Make a smooth transition into management Develop your authentic leadership style Engage and empower staff to achieve excellence Build high-performing, collaborative teams Apply delegation best practices Attract and retain great staff From developing an inspiring vision and empowering members to reach it, to meeting deadlines, and evaluating results. This course will teach students the skills and behaviors needed to successfully transition into an IT manager role. Private classes on this topic are available. We can address your organization?s issues, time constraints, and save you money, too. Contact us to find out how. 1. Making the Transition into Leadership Defining Success Developing Leadership Competencies Acting as Leader, Liaison, Figurehead. Monitor, Disseminator, and Spokesperson Allocating Resources Acting Entrepreneurially Negotiating and Handling Disturbances 2. Building Trust, Engagement and Involvement Applying SCARF Leading by Example with the 5 Components of Emotional Intelligence - Self-Awareness, Self-Regulation, Motivation, Empathy, and Social Skill Engaging, Involving, and Motivating Others The 4 Disciplines of Motivation - Behavioral, Cognitive, Psychodynamic, and Humanistic Working with Differing Personality Styles Developing Your Leadership Psychological Toolkit Discovering and Meeting Stakeholder Expectations 3. Collaboration & Teams Creating, Facilitating, and Maintaining Teams Building a Team through Culture, Human to Human Relationships, Effective Communication, and Setting and Meeting Goals & Objectives Modern, Autonomous, Self-Organizing, and Cross-Functional Teams 4. Building People with Challenging Work Willingness to Delegate Delegating Successfully - Preparing and Researching, Clarifying the Intent of the Task, Planning Your Delegation, Delegating Responsibility and Empowering Your Staff to Take Action, and Providing Ongoing Support and Oversight 5. Attracting and Keeping Great People Managing Performance Knowing Your Staff Checking Assumptions Engaging Your Team Leading and Coaching for Success Managing Disruption

Game Designing Training Course 3ds Max and Unity 3D (Live Online Only)
By London Design Training Courses
Why Learn Game Designing Training Course 3ds Max and Unity 3D? Click for more info Learn Game Designing with 3ds Max and Unity 3D for industry demand, 3d and 2d skills, game design, AR/VR projects, game programming, and 3d visualization. Enhance your career in the thriving gaming and interactive media industry. Duration: 40 hrs. Method: 1-on-1 & Tailored content. Schedule: Tailor your own schedule by pre-booking a convenient hour of your choice, available from Mon to Sat 9 am and 7 pm. Explore the World of Unity 3D with Our Training Courses Unity is a robust cross-platform game development engine, responsible for creating a significant portion of the world's games. Learn ultimate game development platform to build top-notch 3D & 2D games, deployable on mobile, desktop, VR/AR, consoles, or the Web. The opportunities are limitless. Led by certified and experienced Unity instructors, our training courses are filled with practical, real-world exercises. 40-hour Game Designing Training Course with 3ds Max and Unity 3D: Course Overview: Module 1: Introduction to 3ds Max and Unity 3D (4 hours) Get acquainted with 3ds Max and Unity 3D interfaces and workflows Efficiently set up and manage projects Master importing and handling assets Module 2: 3D Modeling with 3ds Max (8 hours) Dive into 3D modeling techniques Create stunning 3D models using 3ds Max Explore polygonal, spline, and NURBS modeling Enhance models with textures and materials Module 3: Animation and Rigging with 3ds Max (8 hours) Understand animation techniques in 3ds Max Rig 3D models for smooth animations Bring creations to life with keyframe animation Employ procedural animation methods Export animations for Unity 3D integration Module 4: Game Design with Unity 3D (8 hours) Learn the Unity 3D game engine Grasp essential game mechanics and concepts Create and manage game scenes and levels Master control of game objects and components Utilize physics and collision detection for immersive experiences Module 5: Scripting and Programming with Unity 3D (8 hours) Introduce Unity 3D scripting with C# Understand variables, data types, and functions in C# Control game objects and components using C# Explore game loops and events for interactive gameplay Module 6: User Interfaces and Audio with Unity 3D (4 hours) Design captivating user interfaces within Unity 3D Implement interactive buttons, sliders, and input fields Elevate games with audio import and editing Control sound effects and background music Module 7: Optimization and Deployment (4 hours) Master game optimization in Unity 3D Enhance game performance through scripting techniques Build and test games for various platforms Publish games on the web or app stores Game Designing Training Course 3ds Max and Unity 3D (Live Online Only): Explore advanced 3ds Max techniques for modeling, lighting, and cameras Dive into character animation for lifelike characters Enhance Unity 3D skills with real-time development and game authoring settings Unity - Real-time 3D Development Platform: Unlock Your Creativity https://www.unity.com/ Create 3D, 2D, VR & AR Experiences For Any Industry: Games, Auto, AEC, Film, And More. Complete Solution To Develop Better, Iterate Faster, And Grow Your Business. Amazing Games. Immersive Experiences. Multi-Platform Support. 3ds Max Free Trial | Autodesk Download a free 30-day trial of 3ds Max, 3D modeling, and rendering software for design visualization, games, and animation.

S4F20 SAP Business Processes in Management Accounting
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Application Consultant Business Analyst Business Process Owner / Team Lead / Power User Help Desk / COE Support Program / Project Manager Overview This course will prepare you to: Describe the motivation for SAP S/4HANA Enterprise Management Provide an overview of basic business processes in the main components of Financial Accounting with SAP S/4HANA Participants of this course will gain an overview of the Financial Accounting capabilities of SAP S/4HANA. You will learn how SAP S/4HANA covers the Financial Accounting related business requirements and how the fundamental business processes and tasks are executed in the system. General Ledger Accounting, Accounts Payable, Accounts Receivable, Asset Accounting and Bank Accounting and their integration are all discussed in this course. Especially if you are new to Financial Accounting in SAP S/4HANA, this course is the right starting point for you. If you plan to take the academy and certification for Financial Accounting, this course will help you to better understand the certification courses. For the actual certification, it is recommended, but not mandatory. Overview of SAP S/4HANA Providing an Overview of the SAP S/4HANA Using the SAP Fiori Front-En Overview of Financial Accounting (FI) in SAP S/4HANA Outlining Financial Accounting (FI) Components in SAP S/4HANA General Ledger (G/L) Accounting Outlining Organizational Elements in Financial Accounting (FI) Maintaining G/L Master Records Posting Transactions in the G/L Accounts Payable Maintaining Vendor Master Records Maintaining Accounts Payable Transactions Managing the Integration between Accounts Payable and Materials Management Performing Accounts Payable Closing Operations Accounts Receivable Maintaining Customer Master Records Managing Accounts Receivable Transactions Managing Customer Correspondence Creating Accounts Receivable Dispute Cases Managing the Integration between Accounts Receivable and Sales Order Management Performing Accounts Receivable Closing Operations Asset Accounting Maintaining Asset Master Records Executing Asset Transactions Executing Asset Accounting Period-End Closing Activitie Bank Accounting Maintaining Bank Accounting Master Records Managing Bank Accounting Transactions Closing Operations in General Ledger Accounting Performing General Ledger (G/L) Closing Operations Additional course details: Nexus Humans S4F20 SAP Business Processes in Management Accounting training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the S4F20 SAP Business Processes in Management Accounting course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

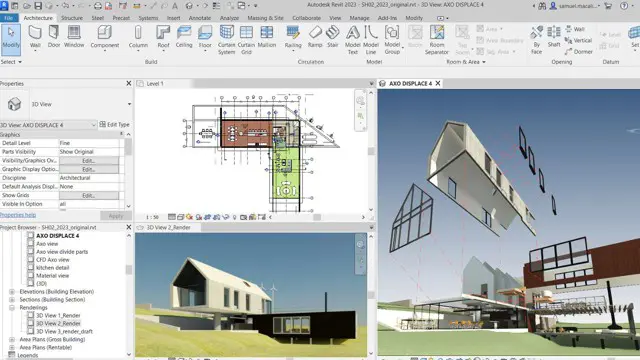
Revit One to One Basic to Advance Weekends Online or Face to Face
By Real Animation Works
Revit face to face training customised and bespoke. Online or Face to Face
Carrying out successful property valuations/marketing appraisals
By Mark Bentley PPNAEA (Mark Bentley Ltd)
By the end of the course you will have picked up numerous tips and guidance and advice to help you carry out great property valuations/market appraisal's which will help you improve you conversion rate and win more clients.

SharePoint - Advanced Site Owner (Modern Experience)
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for This course is designed for students who already have experience creating Modern SharePoint sites and populating them with content, who want to learn advanced features to extend SharePoint's capabilities, make information easier to find and manage, use SharePoint features to improve governance and compliance, and improve the security of information and services within the SharePoint environment. Overview Create a custom site template to reduce the time spent creating similarly configured SharePoint sites. Configure managed metadata, including custom term sets, content types, and metadata-based navigation. Control access through permissions. Improve overall security of sites, lists, libraries, folders, list items, and documents. Microsoft© SharePoint©, in conjunction with the Microsoft 365? productivity and office automation suite, provides tools to create and manage a corporate intranet, facilitate content sharing and collaboration, and enable users to create, access, store, and track documents and data in a central location. Users who already have experience as SharePoint site members and owners may be ready to move on to more advanced site-building tasks such as using custom site templates, custom themes, applying advanced permissions settings, improving security, and preparing sites to support governance and compliance. Advanced site builders may be ready to undertake more advanced site management tasks, working in conjunction with their SharePoint Administrator to create and use custom site templates, term sets and metadata, manage information governance and compliance, and get deeper into SharePoint security configuration. This course focuses on these advanced site-building and administration tasks. Prerequisites To ensure your success in this course, you should have SharePoint site user skills such as the ability to view and enter data in SharePoint lists and libraries, and to navigate a typical SharePoint site. You should also have intermediate site builder skills such as the ability to create a SharePoint site, apply a site template, populate sites with pages, create lists and libraries, and connect a site to a hub site. NOTE: This course was developed using Microsoft 365 Business Standard edition. If you opt to use one of the Enterprise editions, be sure to key the course activities before you deliver the class so you will be able to anticipate any differences that students might see with the edition you use. Lesson 1: Creating Custom Site Templates Topic A: Prepare a Site Script Topic B: Generate and Use a Custom Site Template Lesson 2: Managing Content Services Topic A: Plan and Configure Managed Metadata Topic B: Create and Manage Content Types Topic C: Use Managed Metadata for Navigation and Filtering Lesson 3: Controlling Access Through Permissions Topic A: Assign Permissions Topic B: Manage Permissions Inheritance Lesson 4: Improving Security Topic A: Manage Access at the Site Level Topic B: Manage Access at the Tenant Level

Managing Conflict
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for This course is intended for any business professional who encounters conflict in the workplace. Overview Recognize the impact of conflict in the workplace by identifying your personal reaction and developing a healthy attitude toward conflict. Analyze conflict by assessing the situation and identifying the source of the conflict. Utilize effective communication techniques to manage conflict in a proactive manner. Resolve conflict by evaluating approaches, and determining and implementing an action plan with the best solution. An organization improves its likelihood of success by effectively managing conflict. As a leader within your organization, you share in that responsibility. This course will help you cultivate the skills necessary to help manage conflict and ultimately to decrease the presence of conflict in the workplace. Private classes on this topic are available. We can address your organization?s issues, time constraints, and save you money, too. Contact us to find out how. 1. Recognizing the Impact of Conflict Identify Your Personal Reaction to Conflict Develop a Healthy Attitude Toward Conflict 2. Analyzing Conflict Assess the Situation Identify the Source of the Conflict 3. Dealing with Conflict Listen Actively Communicate Effectively Respond to Negative Tactics Avoid Conflict Escalation 4. Resolving Conflict Evaluate Approaches to Conflict Resolution Determine the Best Solution Implement an Action Plan Additional course details: Nexus Humans Managing Conflict (Second Edition) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Managing Conflict (Second Edition) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
