- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Personal Trainer / Fitness Instructor
By Lead Academy
Quality Guarantee: Promising training excellence, satisfaction gurantee Accredited by CPD UK & Quality License Scheme Tutor Support Unlimited support via email, till you complete the course Recognised Certification: Accepted by thousands of professional bodies Start Anytime With 1 year access to the course materials Online Learning Learn from anywhere, whenever you want This fitness trainer course will provide you with the in-depth knowledge of exercise science, anatomy and nutrition, empowering yourself to design personalised workout programs and guide clients towards their fitness goals. This course at a glance Accredited by CPD UK Endorsed by Quality Licence Scheme Identify the tools to achieve fitness goals such as losing muscle fat or living a more active life Gain knowledge about strength training, cardiovascular training, and flexibility Learn how to customise individual exercises for clients depending on their fitness goals Understand the correct postures and movements for essential exercises Learn how to design a healthy diet chart for clients Understand different workout routines and best exercises for each muscle group Know the number of hours you should workout a week Learn how to incorporate flexibility and neuromotor training in the client's workout routine Learn ways and methods to deal with client's pain points and guide them accordingly Understand the components and use of supplements Identify the process of post-workout rest and recovery to heal the body Why Personal Trainer / Fitness Instructor Course right for you? This online personal trainer course/fitness instructor course is crafted for professional trainers and aspiring personal trainers keen to give clients the true answer to their actual needs, as well as for those who want to help people lose their fat and become fit and healthy. You will discover and gain knowledge about the building blocks of effective training programs and how to create your own training programs to benefit both yourself and your clients. Upon successful completion of this course, you will understand the process of formulating a workout routine, determine the strength and fitness level of clients, and learn the concept of resistance training and cardio training. Personal Trainer / Fitness Instructor Course Details Accredited by CPD certificates are accepted by thousands of professional bodies and government regulators here in the UK and around the world. Many organisations look for employees with CPD requirements, which means, that by doing this course, you would be a potential candidate in your respective field. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. Course Curriculum Introduction Introduction Roles & Responsibilities Of A Strength Coach The Major Muscle Groups Explained Most important Muscle group overview The Different Types of Muscle Fibers Muscle Agonists & Antagonists Quadriceps Explained Hamstrings Explained Calf Muscles Explained Chest Muscles Explained Back Muscles Explained Shoulder Muscles Explained Biceps Explained Triceps Explained Abdominal Muscles Explained Muscle Growth Fundamentals Common Muscle Growth Myths Debunked Muscle Hypertrophy Explained Progressive Overload How Much Muscle Can You Gain in A Week/Month/Year Client Assessment Client Interview Estimating 1 Rep Maximum Strength Workout Design Workout Design Overview Adherence The 4 Most Important Exercises For Beginners How Many Isolation Exercises Should You Do Exercise Order Volume: How Many Sets & Reps Intensity: How Heavy Should You Train How Often Should You Train The Ideal Rest Periods Time Under Tension Explained Sample Workouts Sample Workouts Intro How To Design A Beginner Workout Plan How To Correctly Warm Up Before Lifting Weights 3 Day Beginner Routine 4 Day Routine 5 Day Routine Exercise Videos: Compound Exercises Exercise Videos Overview 5 Most Important Aspects Of Correct Lifting Form Bench Press Chest Press Machine Squats Deadlift Overhead Press Dumbbell Overhead Press Lat Pulldown Dips Barbell Row Barbell Row (Different Grip) Cable Row Iso Row Machine Exercise Videos: Isolation Exercises Sample Workouts Intro How To Design A Beginner Workout Plan How To Correctly Warm Up Before Lifting Weights 3 Day Beginner Routine 4 Day Routine 5 Day Routine Setting Up A Bodybuilding Diet Nutrition Overview Calories Explained How to determine your calorie maintenance level (TDEE) How to track calories Ideal Protein Intake Ideal Carb Intake Ideal Fat Intake What about the Remaining Calories Determining Meal Structure Quality Protein Foods Quality Carb Foods Quality Fat Foods Adjusting Your Diet For Muscle Gains Adjusting Your Diet For Weight Loss The Perfect Pre-Workout Meal The Perfect Post Workout Meal Supplements Supplements Overview Top 3 Beginner Supplements How To Use Protein Powder How To Use Creatine Beta Alanine BCAAs Rest & Recovery Recovery Overview Post Workout Recovery Routine How To Break Through A Strength Plateau How To Deload Correctly The importance of sleep 6 Tips To Fall Asleep Faster FAQ & Miscellaneous Should Men & Women Train Differently. What Should You Eat Before Bed To Build Muscle. Does Electric Muscle Stimulation (EMS) Work. What Should You Train On Your First Day At The Gym. Who should take this course? This online personal trainer course/fitness trainer course is primarily aimed at: Gym trainer Fitness Coach Fitness Enthusiasts Personal Trainer Aspiring Personal Trainer Anybody seeking to expand their fitness business Anyone interested in learning how to create a fitness workout routine However, this course is not restricted to any single profession or field of work. This course can also benefit anyone who wants to learn more about the fitness training regimen in order to incorporate it into their daily routine. Please contact us for more information. Entry Requirements There are no academic entry requirements for this personal trainer/fitness instructor course, and it is open to students of all academic backgrounds. However, you are required to have a laptop/desktop/tablet or smartphone and a good internet connection. Assessment Method This personal trainer/fitness instructor course assesses learners through multiple-choice questions (MCQs). Upon successful completion of the modules, learners must answer MCQs to complete the assessment procedure. Through the MCQs, it is measured how much a learner could grasp from each section. In the assessment pass mark is 60%. Certification Endorsed Certificate from Quality Licence Scheme After successfully passing the MCQ exam you will be eligible to order the Endorsed Certificate by Quality Licence Scheme. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. It will give you a competitive advantage in your career, making you stand out from all other applicants and employees. There is a Quality Licence Scheme endorsement fee to obtain an endorsed certificate which is £65. Certificate of Achievement from Lead Academy After successfully passing the MCQ exam you will be eligible to order your certificate of achievement as proof of your new skill. The certificate of achievement is an official credential that confirms that you successfully finished a course with Lead Academy. Certificate can be obtained in PDF version at a cost of £12, and there is an additional fee to obtain a printed copy certificate which is £35. FAQs What Does a Personal Trainer Do? A professional trainer creates exercise programs and instructs exercises to help people achieve their fitness goals, including weight loss, improving sports performance, or managing a health condition. What Qualifications Do I Need to be a Fitness Instructor? Many skills are needed to be an effective personal trainer. For example, knowledge about fitness training, passion, communication, flexibility, and motivation. If you want to achieve more, join our fitness training course. Who will be teaching this course? You will be learning to be a successful trainer by a professional trainer. He will guide you throughout the training session and teach you everything you need to become a successful fitness trainer in your respective field. Is a Fitness Instructor a HIgh-Value in the UK? Yes, they do. The personal trainer has high demand in the UK as people are becoming more conscious about their health. Thus, they often hire or contact the fitness instructor to get the proper guidelines about body fitness and all. How do I become a gym instructor? If you can pass a certain level of qualifications and training on fitness, you can become a fitness instructor. You can read our How to Become a Personal Trainer blog to learn more. How Much a Personal Trainer Earns in the UK? It depends on their qualifications and experience in the fitness industry. Physical Trainers are expected to earn between £15,000 and £60,000 annually across the UK. What qualifications do I need to work in a gym? With proper training, anyone can become a physical trainer and work in a gym. But you should have a level of qualification like a level 3 diploma in personal training to be recognised as a professional fitness instructor. What is the benefit of doing an accredited course? You will only realise the benefit of having an accredited certificate once you face the corporate world. As employees, job places, and more value the accredited certification, you must own this certificate by doing the course with us. What is a CPD Accredited Course? CPD refers to Continuing Professional Development, and the CPD-accredited course is developed for individuals who want to improve and update their skills within their professional field continuously. This certificate claims that the certificate holder's knowledge is up-to-date in their work area.

Entrepreneur Project Management Diploma Online
By Lead Academy
From this course, you will learn everything about entrepreneure project management, from market research to prototypes as well as manufacturing and distribution. This course covers the process of filling out patents, conducting competitive and market analysis, selling your invention and setting up the business model. This Course At A Glance Accredited by CPD UK Endorsed by Quality Licence Scheme Know how to validate ideas and conduct market research Learn how to protect your invention and perform prototype testing Know how to do patent filling and enforce it Discover the process of market and competitive analysis Know how to sell your invention Identify the potential buyers and the market Demonstrate the business plan and setup Understand the process of manufacturing and distribution Recognise patent, business and government agency scams Know how to build a website and launch the product Master the art of negotiation with resellers Entrepreneur Project Management Diploma Overview This Entrepreneur Project Management Diploma Online is ideal for entrepreneurs and entrepreneur project managers, as well as for people who want to gain extensive knowledge about entrepreneur project management to run their businesses smoothly. This course will assist you in acquiring the exact methods and techniques you require to effectively manage, lead, and drive your team in order to accomplish your entrepreneurial goals. Additionally, you'll learn how to handle business and patent scams, create websites, and launch products to the market. Upon successful completion of this Entrepreneur Project Management Diploma Online, you will be equipped with essential project management and entrepreneurial knowledge and skills to build your business from scratch. This course is endorsed by the Quality Licence Scheme for its high-quality, non-regulated provision and training programmes. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. This course and/or training programme is not regulated by Ofqual and is not an accredited qualification. Your training provider will be able to advise you on any further recognition, for example, progression routes into further and/or higher education. For further information please visit the Learner FAQs on the Quality Licence Scheme website. Who should take this course? This Entrepreneur Project Management Diploma Online is primarily aimed at: Entrepreneurs Project managers Team leaders Small business owners Entrepreneur project managers Anyone looking to enhance their project management skills However, this course is not restricted to any single profession or field of work. This course can also benefit anyone who wants to learn more about entrepreneur project management in order to launch their own business. Entry Requirements There are no academic entry requirements for this Entrepreneur Project Management Diploma Online, and it is open to students of all academic backgrounds. However, you are required to have a laptop/desktop/tablet or smartphone and a good internet connection. Course Curriculum Phase 1 - Idea Validation Idea Validation Checklist Market Research Prelim Patent Search Prelim Costing Concept Description Product Business Benefits What Problem Does it Solve How to Test Your Idea Industry Data Potential Distribution or Go To Market Contracts and Ndas Phase 2 - Prototype Protecting Your Invention Prototype Development and 3D Cad Design Prototype Testing Should We Do This In China Pros and Cons Product Naming Manufacturing Feasibility What is the Potential Cost to Manufacture What is the Potential Retail Cost Package Design and Costing Phase 3 - Patents What is a Patent Patent Types Patent Search REDO Patent Claims Patent Drawings Patent Filing Patent Pending, What Does That Mean IPR Patent Grant Patent Pitfalls Patent Enforcement I Have a Patent, Am I Protected Can I Go To Market Mock Assessment 1 Assessment Mock 1 Phase 4 - Business Planning Business Planning Introduction Suggested Retail Price Market Analysis Competitive Analysis Product Roadmap Distribution1 Operations Plan Go To Market or Licensing Licensing Licensing Options Phase 5 - Decision Plan Go to Market With Invention Selling Your Invention Identify Potential Buyers Identify Market Phase 6 - Business Set Up Business Plan: The Heartbeat of Your Business How Important is a Business Plan Initial Business Funding Setting Up A Business Bank Account Home Office When Do I Get a Real Office Mock Assessment 2 Assessment Mock 2 Phase 7 - Manufacturing Define Manufacturing Process Mold Design and Production Production Costs Test Production Run Packaging Design_1 Shipping Logistics Local Manufacturers Pros and Cons Phase 8 - Distribution Reseller Landscape Forecasting 3PL Negotiations Live and Die by Distribution Phase 9 - Business Scams and Pitfalls Patent Scams Renewal Based General Business Scams Government Agency Scam Phase 10 - Go To Market Website Build and Launched Manufacturer's Rep Firm Negotiation and Set Up Resellers Negotiation and Set Up Mock Assessment 3 Assessment Mock 3 Final Assessment Assessment - Entrepreneur Project Management Diploma Online Recognised Accreditation CPD Certification Service This course is accredited by continuing professional development (CPD). CPD UK is globally recognised by employers, professional organisations, and academic institutions, thus a certificate from CPD Certification Service creates value towards your professional goal and achievement. CPD certificates are accepted by thousands of professional bodies and government regulators here in the UK and around the world. Many organisations look for employees with CPD requirements, which means, that by doing this course, you would be a potential candidate in your respective field. Quality Licence Scheme Endorsed The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. It will give you a competitive advantage in your career, making you stand out from all other applicants and employees. Certificate of Achievement Endorsed Certificate from Quality Licence Scheme After successfully passing the MCQ exam you will be eligible to order the Endorsed Certificate by Quality Licence Scheme. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. It will give you a competitive advantage in your career, making you stand out from all other applicants and employees. There is a Quality Licence Scheme endorsement fee to obtain an endorsed certificate which is £65. Certificate of Achievement from Lead Academy After successfully passing the MCQ exam you will be eligible to order your certificate of achievement as proof of your new skill. The certificate of achievement is an official credential that confirms that you successfully finished a course with Lead Academy. Certificate can be obtained in PDF version at a cost of £12, and there is an additional fee to obtain a printed copy certificate which is £35. FAQs Is CPD a recognised qualification in the UK? CPD is globally recognised by employers, professional organisations and academic intuitions, thus a certificate from CPD Certification Service creates value towards your professional goal and achievement. CPD-certified certificates are accepted by thousands of professional bodies and government regulators here in the UK and around the world. Are QLS courses recognised? Although QLS courses are not subject to Ofqual regulation, they must adhere to an extremely high level that is set and regulated independently across the globe. A course that has been approved by the Quality Licence Scheme simply indicates that it has been examined and evaluated in terms of quality and fulfils the predetermined quality standards. When will I receive my certificate? For CPD accredited PDF certificate it will take 24 hours, however for the hardcopy CPD certificate takes 5-7 business days and for the Quality License Scheme certificate it will take 7-9 business days. Can I pay by invoice? Yes, you can pay via Invoice or Purchase Order, please contact us at info@lead-academy.org for invoice payment. Can I pay via instalment? Yes, you can pay via instalments at checkout. How to take online classes from home? Our platform provides easy and comfortable access for all learners; all you need is a stable internet connection and a device such as a laptop, desktop PC, tablet, or mobile phone. The learning site is accessible 24/7, allowing you to take the course at your own pace while relaxing in the privacy of your home or workplace. Does age matter in online learning? No, there is no age limit for online learning. Online learning is accessible to people of all ages and requires no age-specific criteria to pursue a course of interest. As opposed to degrees pursued at university, online courses are designed to break the barriers of age limitation that aim to limit the learner's ability to learn new things, diversify their skills, and expand their horizons. When I will get the login details for my course? After successfully purchasing the course, you will receive an email within 24 hours with the login details of your course. Kindly check your inbox, junk or spam folder, or you can contact our client success team via info@lead-academy.org
DP-203T00 Data Engineering on Microsoft Azure
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The primary audience for this course is data professionals, data architects, and business intelligence professionals who want to learn about data engineering and building analytical solutions using data platform technologies that exist on Microsoft Azure. The secondary audience for this course includes data analysts and data scientists who work with analytical solutions built on Microsoft Azure. In this course, the student will learn how to implement and manage data engineering workloads on Microsoft Azure, using Azure services such as Azure Synapse Analytics, Azure Data Lake Storage Gen2, Azure Stream Analytics, Azure Databricks, and others. The course focuses on common data engineering tasks such as orchestrating data transfer and transformation pipelines, working with data files in a data lake, creating and loading relational data warehouses, capturing and aggregating streams of real-time data, and tracking data assets and lineage. Prerequisites Successful students start this course with knowledge of cloud computing and core data concepts and professional experience with data solutions. AZ-900T00 Microsoft Azure Fundamentals DP-900T00 Microsoft Azure Data Fundamentals 1 - Introduction to data engineering on Azure What is data engineering Important data engineering concepts Data engineering in Microsoft Azure 2 - Introduction to Azure Data Lake Storage Gen2 Understand Azure Data Lake Storage Gen2 Enable Azure Data Lake Storage Gen2 in Azure Storage Compare Azure Data Lake Store to Azure Blob storage Understand the stages for processing big data Use Azure Data Lake Storage Gen2 in data analytics workloads 3 - Introduction to Azure Synapse Analytics What is Azure Synapse Analytics How Azure Synapse Analytics works When to use Azure Synapse Analytics 4 - Use Azure Synapse serverless SQL pool to query files in a data lake Understand Azure Synapse serverless SQL pool capabilities and use cases Query files using a serverless SQL pool Create external database objects 5 - Use Azure Synapse serverless SQL pools to transform data in a data lake Transform data files with the CREATE EXTERNAL TABLE AS SELECT statement Encapsulate data transformations in a stored procedure Include a data transformation stored procedure in a pipeline 6 - Create a lake database in Azure Synapse Analytics Understand lake database concepts Explore database templates Create a lake database Use a lake database 7 - Analyze data with Apache Spark in Azure Synapse Analytics Get to know Apache Spark Use Spark in Azure Synapse Analytics Analyze data with Spark Visualize data with Spark 8 - Transform data with Spark in Azure Synapse Analytics Modify and save dataframes Partition data files Transform data with SQL 9 - Use Delta Lake in Azure Synapse Analytics Understand Delta Lake Create Delta Lake tables Create catalog tables Use Delta Lake with streaming data Use Delta Lake in a SQL pool 10 - Analyze data in a relational data warehouse Design a data warehouse schema Create data warehouse tables Load data warehouse tables Query a data warehouse 11 - Load data into a relational data warehouse Load staging tables Load dimension tables Load time dimension tables Load slowly changing dimensions Load fact tables Perform post load optimization 12 - Build a data pipeline in Azure Synapse Analytics Understand pipelines in Azure Synapse Analytics Create a pipeline in Azure Synapse Studio Define data flows Run a pipeline 13 - Use Spark Notebooks in an Azure Synapse Pipeline Understand Synapse Notebooks and Pipelines Use a Synapse notebook activity in a pipeline Use parameters in a notebook 14 - Plan hybrid transactional and analytical processing using Azure Synapse Analytics Understand hybrid transactional and analytical processing patterns Describe Azure Synapse Link 15 - Implement Azure Synapse Link with Azure Cosmos DB Enable Cosmos DB account to use Azure Synapse Link Create an analytical store enabled container Create a linked service for Cosmos DB Query Cosmos DB data with Spark Query Cosmos DB with Synapse SQL 16 - Implement Azure Synapse Link for SQL What is Azure Synapse Link for SQL? Configure Azure Synapse Link for Azure SQL Database Configure Azure Synapse Link for SQL Server 2022 17 - Get started with Azure Stream Analytics Understand data streams Understand event processing Understand window functions 18 - Ingest streaming data using Azure Stream Analytics and Azure Synapse Analytics Stream ingestion scenarios Configure inputs and outputs Define a query to select, filter, and aggregate data Run a job to ingest data 19 - Visualize real-time data with Azure Stream Analytics and Power BI Use a Power BI output in Azure Stream Analytics Create a query for real-time visualization Create real-time data visualizations in Power BI 20 - Introduction to Microsoft Purview What is Microsoft Purview? How Microsoft Purview works When to use Microsoft Purview 21 - Integrate Microsoft Purview and Azure Synapse Analytics Catalog Azure Synapse Analytics data assets in Microsoft Purview Connect Microsoft Purview to an Azure Synapse Analytics workspace Search a Purview catalog in Synapse Studio Track data lineage in pipelines 22 - Explore Azure Databricks Get started with Azure Databricks Identify Azure Databricks workloads Understand key concepts 23 - Use Apache Spark in Azure Databricks Get to know Spark Create a Spark cluster Use Spark in notebooks Use Spark to work with data files Visualize data 24 - Run Azure Databricks Notebooks with Azure Data Factory Understand Azure Databricks notebooks and pipelines Create a linked service for Azure Databricks Use a Notebook activity in a pipeline Use parameters in a notebook Additional course details: Nexus Humans DP-203T00 Data Engineering on Microsoft Azure training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the DP-203T00 Data Engineering on Microsoft Azure course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

SC-100T00 Microsoft Cybersecurity Architect
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for experienced cloud security engineers who have taken a previous certification in the security, compliance and identity portfolio. Specifically, students should have advanced experience and knowledge in a wide range of security engineering areas, including identity and access, platform protection, security operations, securing data, and securing applications. They should also have experience with hybrid and cloud implementations. Beginning students should instead take the course SC-900: Microsoft Security, Compliance, and Identity Fundamentals. This is an advanced, expert-level course. Although not required to attend, students are strongly encouraged to have taken and passed another associate level certification in the security, compliance and identity portfolio (such as AZ-500, SC-200 or SC-300) before attending this class. This course prepares students with the expertise to design and evaluate cybersecurity strategies in the following areas: Zero Trust, Governance Risk Compliance (GRC), security operations (SecOps), and data and applications. Students will also learn how to design and architect solutions using zero trust principles and specify security requirements for cloud infrastructure in different service models (SaaS, PaaS, IaaS). Prerequisites Highly recommended to have attended and passed one of the associate level certifications in the security, compliance and identity portfolio (such as AZ-500T00 Microsoft Azure Security Technologies, SC-200T00: Microsoft Security Operations Analyst, or SC-300T00: Microsoft Identity and Access Administrator.) Advanced experience and knowledge in identity and access, platform protection, security operations, securing data and securing applications. Experience with hybrid and cloud implementations. 1 - Introduction to Zero Trust and best practice frameworks Zero Trust initiatives Zero Trust technology pillars part 1 Zero Trust technology pillars part 2 2 - Design solutions that align with the Cloud Adoption Framework (CAF) and Well-Architected Framework (WAF) Define a security strategy Cloud Adoption Framework secure methodology Design security with Azure Landing Zones The Well-Architected Framework security pillar 3 - Design solutions that align with the Microsoft Cybersecurity Reference Architecture (MCRA) and Microsoft cloud security benchmark (MCSB) Design solutions with best practices for capabilities and controls Design solutions with best practices for attack protection 4 - Design a resiliency strategy for common cyberthreats like ransomware Common cyberthreats and attack patterns Support business resiliency Ransomware protection Configurations for secure backup and restore Security updates 5 - Case study: Design solutions that align with security best practices and priorities Case study description Case study answers Conceptual walkthrough Technical walkthrough 6 - Design solutions for regulatory compliance Translate compliance requirements into a security solution Address compliance requirements with Microsoft Purview Address privacy requirements with Microsoft Priva Address security and compliance requirements with Azure policy Evaluate infrastructure compliance with Defender for Cloud 7 - Design solutions for identity and access management Design cloud, hybrid and multicloud access strategies (including Azure AD) Design a solution for external identities Design modern authentication and authorization strategies Align conditional access and Zero Trust Specify requirements to secure Active Directory Domain Services (AD DS) Design a solution to manage secrets, keys, and certificates 8 - Design solutions for securing privileged access The enterprise access model Design identity governance solutions Design a solution to secure tenant administration Design a solution for cloud infrastructure entitlement management (CIEM) Design a solution for privileged access workstations and bastion services 9 - Design solutions for security operations Design security operations capabilities in hybrid and multicloud environments Design centralized logging and auditing Design security information and event management (SIEM) solutions Design solutions for detection and response Design a solution for security orchestration, automation, and response (SOAR) Design security workflows Design threat detection coverage 10 - Case study: Design security operations, identity and compliance capabilities Case study description Case study answers Conceptual walkthrough Technical walkthrough 11 - Design solutions for securing Microsoft 365 Evaluate security posture for collaboration and productivity workloads Design a Microsoft 365 Defender solution Design configurations and operational practices for Microsoft 365 12 - Design solutions for securing applications Design and implement standards to secure application development Evaluate security posture of existing application portfolios Evaluate application threats with threat modeling Design security lifecycle strategy for applications Secure access for workload identities Design a solution for API management and security Design a solution for secure access to applications 13 - Design solutions for securing an organization's data Design a solution for data discovery and classification using Microsoft Purview Design a solution for data protection Design data security for Azure workloads Design security for Azure Storage Design a security solution with Microsoft Defender for SQL and Microsoft Defender for Storage 14 - Case study: Design security solutions for applications and data Case study description Case study answers Conceptual walkthrough Technical walkthrough 15 - Specify requirements for securing SaaS, PaaS, and IaaS services Specify security baselines for SaaS, PaaS, and IaaS services Specify security requirements for web workloads Specify security requirements for containers and container orchestration 16 - Design solutions for security posture management in hybrid and multicloud environments Evaluate security posture by using Microsoft Cloud Security Benchmark Design integrated posture management and workload protection Evaluate security posture by using Microsoft Defender for Cloud Posture evaluation with Microsoft Defender for Cloud secure score Design cloud workload protection with Microsoft Defender for Cloud Integrate hybrid and multicloud environments with Azure Arc Design a solution for external attack surface management 17 - Design solutions for securing server and client endpoints Specify server security requirements Specify requirements for mobile devices and clients Specify internet of things (IoT) and embedded device security requirements Secure operational technology (OT) and industrial control systems (ICS) with Microsoft Defender for IoT Specify security baselines for server and client endpoints Design a solution for secure remote access 18 - Design solutions for network security Design solutions for network segmentation Design solutions for traffic filtering with network security groups Design solutions for network posture management Design solutions for network monitoring 19 - Case study: Design security solutions for infrastructure Case study description Case study answers Conceptual walkthrough Technical walkthrough Additional course details: Nexus Humans SC-100T00 Microsoft Cybersecurity Architect training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the SC-100T00 Microsoft Cybersecurity Architect course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Have you ever faced any accident or awkward situation while you travel with your family or alone or swim in the pool? If so, lifeguards will provide you with the necessary techniques to ensure your safety. The role of a lifeguard is crucial in any emergency situation. Learn the skills you need to be a lifeguard from this Lifeguard Training course. This Lifeguard Training course has been divided into understandable and manageable sections that will help you grasp each concept- from the basic to advanced course components. Learn from industry experts today and enhance your skills and knowledge in no time. This Lifeguard Training course will increase your possibility to get your desired job and boost your personal growth. This Lifeguard Training course features easy-to-digest modules that break down each topic and ensure all our students receive an unparalleled and thorough learning experience. Our Lifeguard Training course lessons were prepared by experts and feature interactive activities. You'll learn how you can use various devices effectively from industry experts. If you want to build your career in this sector, then this Lifeguard Training course will help you to get the required skills to take the first step in the professional field. On the Lifeguard Training course, we guarantee that you will gain relevant skills and acquire tremendous knowledge on the subject. After completing the Lifeguard Training course, the certificate you'll achieve will help you land the job you want in a related field. Enjoy a pleasant and professional 100% online learning experience. Enrol in our Lifeguard Training course today and take control of your career! Learning Objectives Learn about the roles and responsibilities of a lifeguard Be able to understand the steps of CPR Provide first aid to any injured person Learn how to report any incident Be able to give security to a person in need Understand the severity of any injury Acquire the skills to bandage an injured place Be able to prevent any infection Learn to perform dressing and sterilisation process properly Who is this Course for? The Lifeguard Training course is ideal for highly aspiring individuals who wish to enhance their professional skills and train for the job they want! Also, this course is highly beneficial for people who want to have some in-depth knowledge on this topic and keep up to date with the latest information. So, you can enrol in this course if you are: Lifeguards Emergency Medical Assistant Paramedics Nurses Social Care Workers Swimmers Healthcare Professionals Coaches Study the Lifeguard Training course today and enhance your professional skillset from the comfort of your home! Entry Requirement There are no formal entry requirements for the Lifeguard Training course; with enrollment, this course is open to anyone! Anyone with a passion for learning about Lifeguard Training can enrol in this course without any hesitation. Although, the learner needs to have a good understanding of the English language to attend this course and understand what this course is about. CPD Certificate from Course Gate At the successful completion of the course, you can obtain your CPD certificate from us. You can order the PDF certificate for £4.99 and the hard copy for £9.99. Also, you can order both PDF and hardcopy certificates for £12.99. Career path This Lifeguard Training course will help you gain the necessary theoretical knowledge to excel in the relevant field. Enrol on our Lifeguard Training course now and get started on the journey of taking your career to the next level. Course Curriculum Module 01: Professional Lifeguard Professional Lifeguard 00:18:00 Module 02: Lifeguard Observation Lifeguard Observation 00:16:00 Module 03: Safety and Risk Management Safety and Risk Management 00:26:00 Module 04: Emergency Response Activity Emergency Response Activity 00:12:00 Module 05: Assists and Rescues Assists and Rescues 00:15:00 Module 06: Injury Prevention Injury Prevention 00:13:00 Module 07: First Aid First Aid 00:19:00 Module 08: Cardiac Emergencies Cardiac Emergencies 00:15:00 Certificate and Transcript Order Your Certificates or Transcripts 00:00:00

AZ-305T00 Designing Microsoft Azure Infrastructure Solutions
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for Successful students have experience and knowledge in IT operations, including networking, virtualization, identity, security, business continuity, disaster recovery, data platforms, and governance. Students also have experience designing and architecting solutions. Before attending this course, students must have previous experience deploying or administering Azure resources and strong conceptual knowledge of: Azure compute technologies such as VMs, containers and serverless solutions Azure virtual networking to include load balancers Azure Storage technologies (unstructured and databases) General application design concepts such as messaging and high availability This course teaches Azure Solution Architects how to design infrastructure solutions. Course topics cover governance, compute, application architecture, storage, data integration, authentication, networks, business continuity, and migrations. The course combines lecture with case studies to demonstrate basic architect design principles. Prerequisites Before attending this course, students must have previous experience deploying or administering Azure resources and conceptual knowledge of: Azure Active Directory Azure compute technologies such as VMs, containers and serverless solutions Azure virtual networking to include load balancers Azure Storage technologies (unstructured and databases) General application design concepts such as messaging and high availability AZ-104T00 - Microsoft Azure Administrator 1 - Design governance Design for governance Design for management groups Design for subscriptions Design for resource groups Design for resource tags Design for Azure Policy Design for role-based access control (RBAC) Design for Azure landing zones 2 - Design an Azure compute solution Choose an Azure compute service Design for Azure Virtual Machines solutions Design for Azure Batch solutions Design for Azure App Service solutions Design for Azure Container Instances solutions Design for Azure Kubernetes Service solutions Design for Azure Functions solutions Design for Azure Logic Apps solutions 3 - Design a data storage solution for non-relational data Design for data storage Design for Azure storage accounts Design for data redundancy Design for Azure Blob Storage Design for Azure Files Design for Azure managed disks Design for storage security 4 - Design a data storage solution for relational data Design for Azure SQL Database Design for Azure SQL Managed Instance Design for SQL Server on Azure Virtual Machines Recommend a solution for database scalability Recommend a solution for database availability Design security for data at rest, data in motion, and data in use Design for Azure SQL Edge Design for Azure Cosmos DB and Table Storage 5 - Design data integration Design a data integration solution with Azure Data Factory Design a data integration solution with Azure Data Lake Design a data integration and analytic solution with Azure Databricks Design a data integration and analytic solution with Azure Synapse Analytics Design strategies for hot, warm, and cold data paths Design an Azure Stream Analytics solution for data analysis 6 - Design an application architecture Describe message and event scenarios Design a messaging solution Design an Azure Event Hubs messaging solution Design an event-driven solution Design a caching solution Design API integration Design an automated app deployment solution Design an app configuration management solution 7 - Design authentication and authorization solutions Design for identity and access management (IAM) Design for Microsoft Entra ID Design for Microsoft Entra business-to-business (B2B) Design for Azure Active Directory B2C (business-to-customer) Design for conditional access Design for identity protection Design for access reviews Design service principals for applications Design managed identities Design for Azure Key Vault 8 - Design a solution to log and monitor Azure resources Design for Azure Monitor data sources Design for Azure Monitor Logs (Log Analytics) workspaces Design for Azure Workbooks and Azure insights Design for Azure Data Explorer 9 - Design network solutions Recommend a network architecture solution based on workload requirements Design patterns for Azure network connectivity services Design outbound connectivity and routing Design for on-premises connectivity to Azure Virtual Network Choose an application delivery service Design for application delivery services Design for application protection services 10 - Design a solution for backup and disaster recovery Design for backup and recovery Design for Azure Backup Design for Azure blob backup and recovery Design for Azure files backup and recovery Design for Azure virtual machine backup and recovery Design for Azure SQL backup and recovery Design for Azure Site Recovery 11 - Design migrations Evaluate migration with the Cloud Adoption Framework Describe the Azure migration framework Assess your on-premises workloads Select a migration tool Migrate your structured data in databases Select an online storage migration tool for unstructured data Migrate offline data 12 - Introduction to the Microsoft Azure Well-Architected Framework Azure Well-Architected Framework pillars Cost optimization Operational excellence Performance efficiency Reliability Security 13 - Microsoft Azure Well-Architected Framework - Cost Optimization Develop cost-management discipline Design with a cost-efficiency mindset Design for usage optimization Design for rate optimization Monitor and optimize over time 14 - Microsoft Azure Well-Architected Framework - Operational excellence Embrace DevOps culture Establish development standards Evolve operations with observability Deploy with confidence Automate for efficiency Adopt safe deployment practices 15 - Microsoft Azure Well-Architected Framework - Performance efficiency Negotiate realistic performance targets Design to meet capacity requirements Achieve and sustain performance Improve efficiency through optimization 16 - Microsoft Azure Well-Architected Framework - Reliability Design for business requirements Design for resilience Design for recovery Design for operations Keep it simple 17 - Microsoft Azure Well-Architected Framework - Security Plan your security readiness Design to protect confidentiality Design to protect integrity Design to protect availability Sustain and evolve your security posture 18 - Getting started with the Microsoft Cloud Adoption Framework for Azure Customer narrative Common blockers 19 - Prepare for successful cloud adoption with a well-defined strategy Customer narrative Capture strategic motivation Define objectives and key results Evaluate financial considerations Understand technical considerations Create a business case 20 - Prepare for cloud adoption with a data-driven plan Customer narrative 21 - Choose the best Azure landing zone to support your requirements for cloud operations Customer narrative Common operating models Design areas for Azure landing zones Design principles for Azure landing zones Journey to the target architecture Choose an Azure landing zone option Deploy the Azure landing zone accelerator Enhance your landing zone 22 - Migrate to Azure through repeatable processes and common tools Customer narrative Migration process Migration tools Common tech platforms 23 - Address tangible risks with the Govern methodology of the Cloud Adoption Framework for Azure Customer narrative Govern methodology Corporate policies Governance disciplines Deploy a cloud governance foundation The Cost Management discipline 24 - Ensure stable operations and optimization across all supported workloads deployed to the cloud Establish business commitments Deploy an operations baseline Protect and recover Enhance an operations baseline Manage platform and workload specialization 25 - Innovate applications by using Azure cloud technologies Follow the innovation lifecycle Azure technologies for the build process Infuse your applications with AI Azure technologies for measuring business impact Azure technologies for the learn process 26 - Prepare for cloud security by using the Microsoft Cloud Adoption Framework for Azure Customer narrative Methodology Security roles and responsibilities Simplify compliance and security Simplify security implementation Security tools and policies Additional course details: Nexus Humans AZ-305T00: Designing Microsoft Azure Infrastructure Solutions training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the AZ-305T00: Designing Microsoft Azure Infrastructure Solutions course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

ITIL© 4 Strategist - Direct Plan and Improve (DPI)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Delegates attending this course must have successfully achieved the ITIL 4 Foundation Qualification; your certificate must be presented as documentary evidence to gain admission to this course. Although there is no mandatory requirement, ideally candidates should have at least two years professional experience working in IT Service Management. The ITIL 4 DPI Qualification would most likely suit the following delegates: Individuals continuing of their journey in service management ITSM managers and aspiring ITSM managers Managers of all levels involved in shaping direction and strategy or developing a continually improving team Existing ITIL qualification holders wishing to develop their knowledge The above list is a suggestion only; individuals may wish to attend based on their own career aspirations, personal goals or objectives. Delegates may take as few or as many Intermediate qualifications as they require, and to suit their needs. Overview The purpose of the ITIL 4 Direct Plan and Improve Qualification is: To provide the candidate with the practical skills necessary to create a ?learning and improving? IT organization, with a strong and effective strategic direction To provide practitioners with a practical and strategic method for planning and delivering continual improvement with the necessary agility The objectives of this course are to: Understand the Key Concepts of Direct, Plan & Improve Understand the scope of what is to be directed and/or planned, and know how to use key principles and methods of direction and planning in that context Understand the role of GRC (Governance, Risk & Compliance) and know how to integrate the principles and methods into the service value system Understand and know how to use the key principles and methods of continual improvement for all types of improvements Understand and know how to use the key principles and methods of Organizational Change Management to direction, planning and improvement Understand and know how to use the key principles and methods of measurement and reporting in directing, planning and improvement Understand and know how to direct, plan and improve value streams and practices This unique and central course covers requirements in both the ITIL Managing Professional and ITIL Strategic Leader designations. As such, this course is a must-have in any ITIL 4 professional development plan. You will gain the practical skills needed to establish a ?learning and improving? IT organization that possess a strong and targeted strategic direction. This class includes an exam voucher. Prerequisites ITIL© 4 Foundation 1 - KEY CONCEPTS OF DIRECT, PLAN AND IMPROVE Knowing key terms Differentiating between principle concepts Defining the relationship of Values, Outcomes, Costs and Risks 2 - SCOPING WHAT IS TO BE DIRECTED Cascading goals and requirements Deciphering effective policies, controls and guidelines Placing decision-making authority at the correct level 3 - THE ROLE OF GRC IN THE SERVICE VALUE SYSTEM The role of risk management How governance impacts DPI Ensuring that controls are sufficient but not excessive 4 - PRINCIPLES AND METHODS FOR CONTINUAL IMPROVEMENT Leverage the ITIL CI model Identify assessment objectives and outputs Select the appropriate assessment method Prioritize desired outcomes Build, justify and advocate your business case Conduct improvement reviews and lessons learned sessions Embed CI at all levels of the service value stream 5 - APPLYING COMMUNICATION AND ORGANIZATIONAL CHANGE MANAGEMENT The nature and benefits of OCM Manage, communicate effectively, and influence stakeholders Establish valuable interfaces across the value chain 6 - EFFECTIVE MEASURING AND REPORTING Defining indicators and metrics to support objectives 7 - DIRECT, PLAN AND IMPROVE VALUE STREAMS Recognizing the differences between value streams and practices Choosing the right methods and techniques to direct, plan and improve value streams Additional course details:Notes New Horizons is an Authorised Training Organisation (ATO) for Peoplecert for ITIL4 Nexus Humans ITIL 4 Strategist Direct Plan and Improve (DPI) with Exam training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the ITIL 4 Strategist Direct Plan and Improve (DPI) with Exam course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

ITIL© 4 High Velocity IT (HVIT)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Delegates attending this course must have successfully achieved the ITIL 4 Foundation Qualification; your certificate must be presented as documentary evidence to gain admission to this course. Ideally candidates should have at least two years professional experience working in IT Service Management. The ITIL 4 HVIT Qualification would most likely suit the following delegates: Individuals continuing of their journey in service management ITSM managers and aspiring ITSM managers IT managers and practitioners involved in digital services or working in digital transformation projects, working within or towards high velocity environments Existing ITIL qualification holders wishing to develop their knowledge The above list is a suggestion only. Delegates may take as few or as many Intermediate qualifications as they require, and to suit their needs. Overview This course has been created to help IT service management practitioners working in organizations that are becoming more digitally enabled. The practitioners are familiar with traditional IT service management concepts, and now want to be able to discuss ?digital? with more confidence, to develop practical competences, and to be valued contributors in the digital domain. They want to improve how they and their co-workers: Help get customers? jobs done ? helping customers become who they seek to become Keep raising the bar ? taking things to a significantly higher level Trust and are trusted ? as professional knowledge workers in a healthy workplace Accept ambiguity and uncertainty - not scared of not knowing an answer Commit to continual learning ? all as part of their daily work The scope of the course is the primary activities in the digital value chain. In other words, what the practitioner does and which resources they use across the lifecycle of digital products, in order to: Make the right digital investments Realize and deliver digital products and services quickly Provide digital products and services that are highly resilient to disruption Ensure that the service consumer realizes value from the digital products and services Assure conformance of activities with governance, risk and compliance requirements. Understand and know how to use the key principles and methods of Organizational Change Management to direction, planning and improvement Understand and know how to use the key principles and methods of measurement and reporting in directing, planning and improvement Understand and know how to direct, plan and improve value streams and practices ITIL 4 is a framework for quality IT service management (ITSM) through proven best practice, providing practical and flexible guidance to support your organization on its journey to digital transformation while empowering your IT teams to continue to play a crucial role in the wider business strategy. This course highlights the ways in which digital organizations and digital operating models function in high-velocity environments, including the use of working practices such as Agile and Lean, and technical practices and technologies such as Cloud, Automation, and Automatic Testing. This class includes an exam voucher. Prerequisites ITIL© 4 Foundation 1 - THE NATURE OF HIGH-VELOCITY IN A DIGITAL WORLD Overview of the key ITIL 4 high-velocity terminology Understand when the transformation to high velocity IT is desirable and feasible Understand the five objectives associated with digital products ? to achieve: Valuable investments ? strategically innovative and effective application of IT Fast development - quick realization and delivery of IT services and IT-related products Resilient operations - highly resilient IT services and IT-related products Co-created value - effective interaction between service provider and consumer Assured conformance - to governance, risk and compliance (GRC) requirements. 2 - ITIL OPERATING MODEL ? DIGITAL PRODUCT LIFECYCLE Understand how high velocity IT relates to: The four dimensions of service management The ITIL service value system The service value chain The digital product lifecycle 3 - FUNDAMENTAL CONCEPTS FOR DELIVERING HVIT Understand the following concepts: Ethics Safety culture Toyota Kata Lean / Agile / Resilient / Continuous Service-dominant logic Design thinking Complexity thinking Use the principles, models and concepts to contribute to: Help get customers? jobs done Trust and be trusted Commit to performance Deal with uncertainty Improve by being inquisitive 4 - ACHIEVING VALUE WITH DIGITAL PRODUCTS Know how the service provider ensures valuable investments are achieved. Know how to use the following practices to contribute to achieving valuable investments: Portfolio management Relationship management Know how the service provider ensures fast deployment is achieved Know how to use the following practices to contribute to achieving fast deployment: Architecture management Business analysis Deployment management Service validation and testing Software development and management Know how the service provider ensures resilient operations are achieved Know how to use the following practices to contribute to achieving resilient operations: Availability management Capacity and performance management Monitoring and event management Problem management Service continuity management Infrastructure and platform management Know how the service provider ensures co-created value is achieved Know how to use the following practices to contribute to achieving co-created value with the service consumer: Relationship management Service design Service desk Know how the service provider ensures assured conformance is achieved Know how to use the following practices to contribute to achieving assured conformance: Information security management Risk management

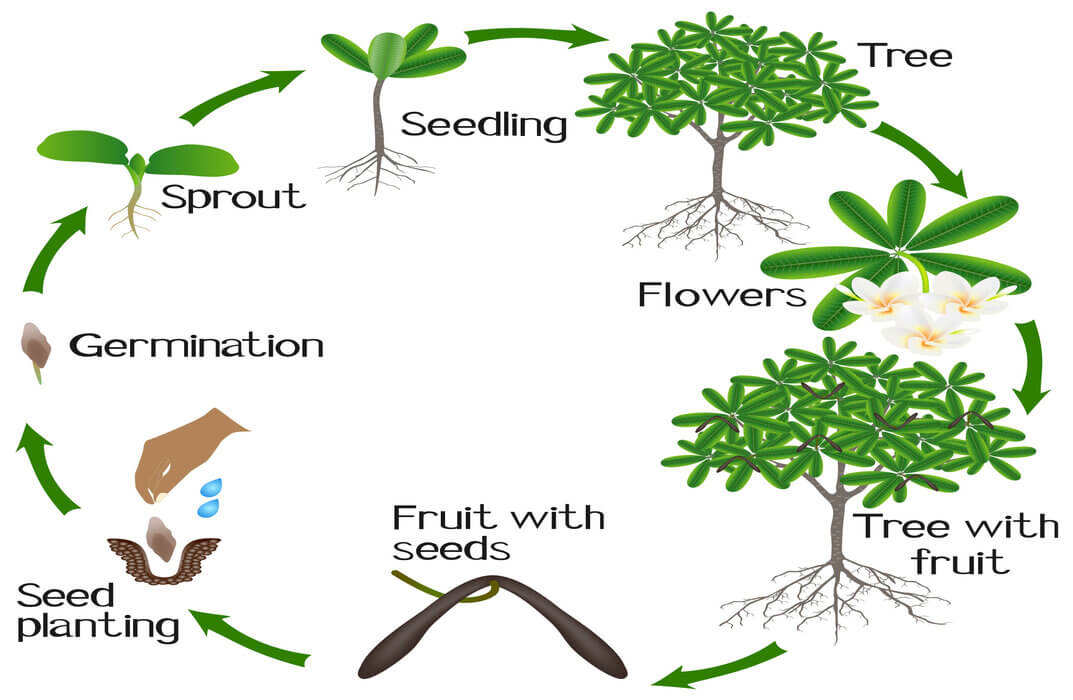
The Basics of Reproduction
By IOMH - Institute of Mental Health
Overview This The Basics of Reproduction course will unlock your full potential and will show you how to excel in a career in The Basics of Reproduction. So upskill now and reach your full potential. Everything you need to get started in The Basics of Reproduction is available in this course. Learning and progressing are the hallmarks of personal development. This The Basics of Reproduction will quickly teach you the must-have skills needed to start in the relevant industry. In This The Basics of Reproduction Course, You Will: Learn strategies to boost your workplace efficiency. Hone your The Basics of Reproduction skills to help you advance your career. Acquire a comprehensive understanding of various The Basics of Reproduction topics and tips from industry experts. Learn in-demand The Basics of Reproduction skills that are in high demand among UK employers, which will help you to kickstart your career. This The Basics of Reproduction course covers everything you must know to stand against the tough competition in the The Basics of Reproduction field. The future is truly yours to seize with this The Basics of Reproduction. Enrol today and complete the course to achieve a The Basics of Reproduction certificate that can change your professional career forever. Additional Perks of Buying a Course From Institute of Mental Health Study online - whenever and wherever you want. One-to-one support from a dedicated tutor throughout your course. Certificate immediately upon course completion 100% Money back guarantee Exclusive discounts on your next course purchase from Institute of Mental Health Enrolling in the The Basics of Reproduction course can assist you in getting into your desired career quicker than you ever imagined. So without further ado, start now. Process of Evaluation After studying the The Basics of Reproduction course, your skills and knowledge will be tested with a MCQ exam or assignment. You must get a score of 60% to pass the test and get your certificate. Certificate of Achievement Upon successfully completing the The Basics of Reproduction course, you will get your CPD accredited digital certificate immediately. And you can also claim the hardcopy certificate completely free of charge. All you have to do is pay a shipping charge of just £3.99. Who Is This Course for? This The Basics of Reproduction is suitable for anyone aspiring to start a career in The Basics of Reproduction; even if you are new to this and have no prior knowledge on The Basics of Reproduction, this course is going to be very easy for you to understand. And if you are already working in the The Basics of Reproduction field, this course will be a great source of knowledge for you to improve your existing skills and take them to the next level. Taking this The Basics of Reproduction course is a win-win for you in all aspects. This course has been developed with maximum flexibility and accessibility, making it ideal for people who don't have the time to devote to traditional education. Requirements This The Basics of Reproduction course has no prerequisite. You don't need any educational qualification or experience to enrol in the The Basics of Reproduction course. Do note: you must be at least 16 years old to enrol. Any internet-connected device, such as a computer, tablet, or smartphone, can access this online The Basics of Reproduction course. Moreover, this course allows you to learn at your own pace while developing transferable and marketable skills. Course Curriculum Section 01: Basics of Asexual Reproduction The Concept of Life Span 00:05:00 The Features of Reproduction 00:06:00 Types of Asexual Reproduction 00:13:00 Vegetative Propagation in Plants 00:10:00 Section 02: Basics of Sexual Reproduction Genetic Recombination in Prokaryotes, Flowering in angiosperms and Breeding... 00:10:00 Reproductive Cycles, Pre-fertilization and Sexuality 00:11:00 Sexuality in Organisms 00:06:00 Events of Fertilization and Post-fertilization in organisms 00:12:00
We believe that if you can breathe, then you'll enjoy the benefits of yoga, this Yoga Training Diploma Level 3 will ensure this ancient and holistic practice becomes an intrinsic part of the fitness industry. You will learn all the traditions of yoga -balance, strength, flexibility and power. So, if you are thinking to learn yoga for your personal need or just interested to pursue a career in the health and fitness industry as a yoga instructor, the Yoga Training Diploma Level 3 will be a perfect choice for you. Course Highlights The price is for the whole course including final exam - no hidden fees Accredited Certificate upon successful completion at an additional cost Efficient exam system with instant results Track progress within own personal learning portal 24/7 customer support via live chat Yoga Training Diploma Level 3 has been given CPD accreditation and is one of the best-selling courses available to students worldwide. This valuable course is suitable for anyone interested in working in this sector or who simply wants to learn more about the topic. If you're an individual looking to excel within this field then Yoga Training Diploma Level 3 is for you. We've taken this comprehensive course and broken it down into several manageable modules which we believe will assist you to easily grasp each concept - from the fundamental to the most advanced aspects of the course. It really is a sure pathway to success. All our courses offer 12 months access and are designed to be studied at your own pace so you can take as much or as little time as you need to complete and gain the full CPD accredited qualification. And, there are no hidden fees or exam charges. We pride ourselves on having friendly and experienced instructors who provide full weekday support and are ready to help with any of your queries. So, if you need help, just drop them an email and await a speedy response. Furthermore, you can check the validity of your qualification and verify your certification on our website at anytime. So, why not improve your chances of gaining professional skills and better earning potential. Assessment and Certification At the end of the course, you will be required to sit an online multiple-choice test. Your test will be assessed automatically and immediately so that you will instantly know whether you have been successful. After you have successfully passed the final exam, you will be able to order an Accredited Certificate of Achievement at an additional cost of £19 for a PDF copy and £29 for an original print copy sent to you by post or for both £39. Career Path Not only does our CPD and CiQ accredited course look good on your CV, setting you apart from the competition, it can be used as a stepping stone to greater things. Further advance your learning, launch a new career or reinvigorate an existing one. On successful completion of this course, you have the potential to achieve an estimated salary of £20,000. The sky really is the limit. Course Curriculum Yoga Introduction 01:00:00 What is Yoga? 00:30:00 Why is Yoga Beneficial? 00:45:00 Different Kinds of Yoga 00:45:00 Positions For Beginners 00:45:00 Equipment & Accessories For Yoga 01:00:00 Conclusion 00:15:00 Yoga and Meditation WHAT IS YOGA? 00:15:00 WHICH IS RIGHT FOR YOU? 00:30:00 GETTING READY 00:15:00 BEGINNING YOUR WORKOUT 01:00:00 MEDITATION 01:00:00 YOGA AND HEALING 01:00:00 Mock Exam Mock Exam - Yoga Training Diploma Level 3 00:20:00 Final Exam Final Exam - Yoga Training Diploma Level 3 00:20:00