- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
5909 Computing courses in Burton Latimer delivered Online
Introduction to Android Games Development
By Compete High
Overview With the ever-increasing demand for Android Games Development in personal & professional settings, this online training aims at educating, nurturing, and upskilling individuals to stay ahead of the curve - whatever their level of expertise in Android Games Development may be. Learning about Android Games Development or keeping up to date on it can be confusing at times, and maybe even daunting! But that's not the case with this course from Compete High. We understand the different requirements coming with a wide variety of demographics looking to get skilled in Android Games Development. That's why we've developed this online training in a way that caters to learners with different goals in mind. The course materials are prepared with consultation from the experts of this field and all the information on Android Games Development is kept up to date on a regular basis so that learners don't get left behind on the current trends/updates. The self-paced online learning methodology by Compete High in this Introduction to Android Games Development course helps you learn whenever or however you wish, keeping in mind the busy schedule or possible inconveniences that come with physical classes. The easy-to-grasp, bite-sized lessons are proven to be most effective in memorising and learning the lessons by heart. On top of that, you have the opportunity to receive a certificate after successfully completing the course! Instead of searching for hours, enrol right away on this Introduction to Android Games Development course from Compete High and accelerate your career in the right path with expert-outlined lessons and a guarantee of success in the long run. Who is this course for? While we refrain from discouraging anyone wanting to do this Introduction to Android Games Development course or impose any sort of restrictions on doing this online training, people meeting any of the following criteria will benefit the most from it: Anyone looking for the basics of Android Games Development, Jobseekers in the relevant domains, Anyone with a ground knowledge/intermediate expertise in Android Games Development, Anyone looking for a certificate of completion on doing an online training on this topic, Students of Android Games Development, or anyone with an academic knowledge gap to bridge, Anyone with a general interest/curiosity Career Path This Introduction to Android Games Development course smoothens the way up your career ladder with all the relevant information, skills, and online certificate of achievements. After successfully completing the course, you can expect to move one significant step closer to achieving your professional goals - whether it's securing that job you desire, getting the promotion you deserve, or setting up that business of your dreams. Course Curriculum Module-1 First Steps with the Android SDK First Steps with the Android SDK 00:00 Module-2 Game Development 101 Game Development 101 00:00 Module-3 Android for Game Developers Android for Game Developers 00:00 Module-4 An Android Game Development Framework An Android Game Development Framework 00:00
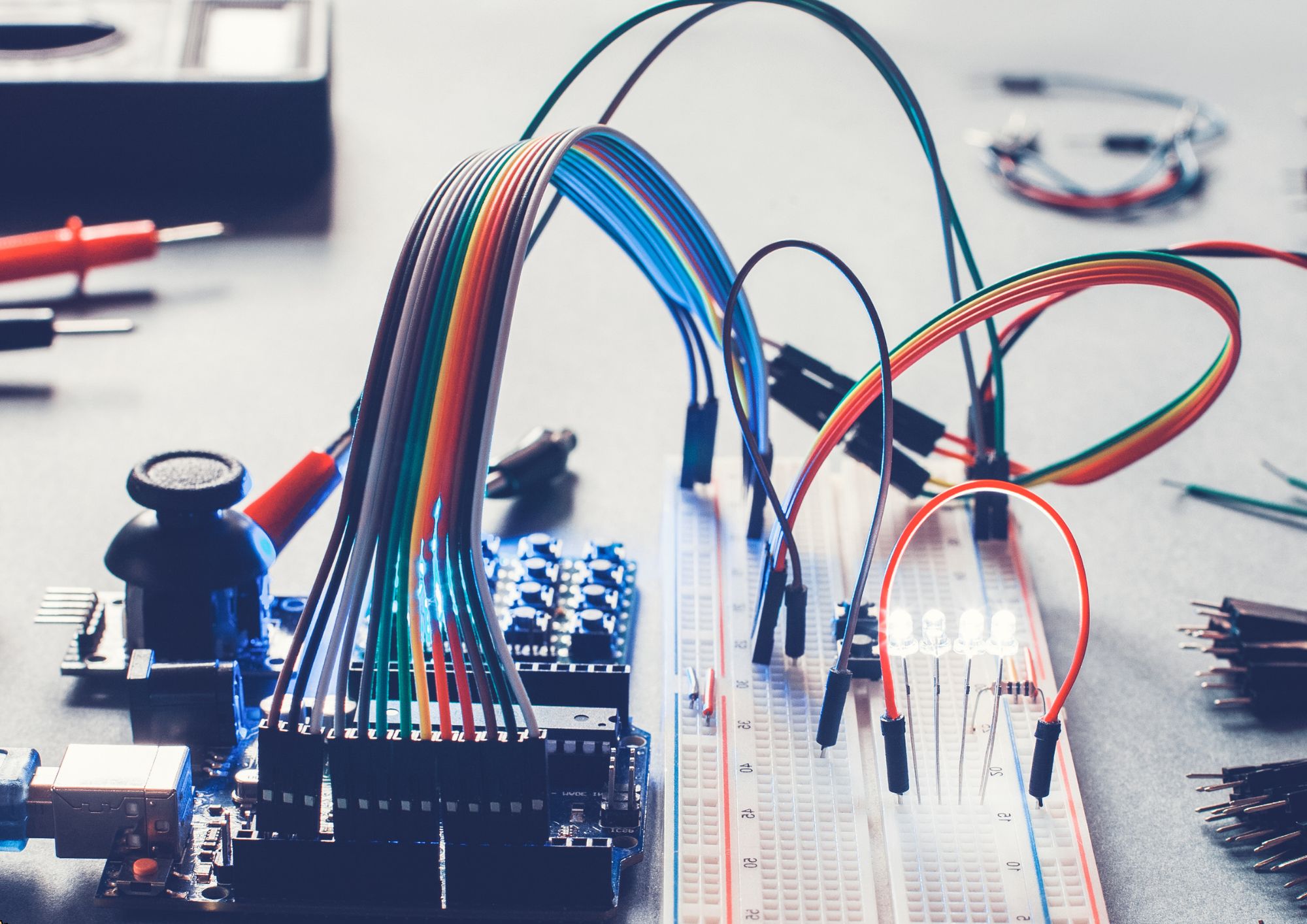
Diploma in Electrical Engineering
By Compete High
Boost your career with our Diploma in Electrical Engineering! ⚡ This self-paced online course covers essential topics like circuits, electrical machines, and power systems, helping you gain industry-relevant skills and a certificate of completion. Enrol today and take the next step in your Electrical Engineering journey! 🔌📚
Introduction to Go Lang
By Compete High
Overview With the ever-increasing demand for Go Lang in personal & professional settings, this online training aims at educating, nurturing, and upskilling individuals to stay ahead of the curve - whatever their level of expertise in Go Lang may be. Learning about Go Lang or keeping up to date on it can be confusing at times, and maybe even daunting! But that's not the case with this course from Compete High. We understand the different requirements coming with a wide variety of demographics looking to get skilled in Go Lang . That's why we've developed this online training in a way that caters to learners with different goals in mind. The course materials are prepared with consultation from the experts of this field and all the information on Go Lang is kept up to date on a regular basis so that learners don't get left behind on the current trends/updates. The self-paced online learning methodology by compete high in this Go Lang course helps you learn whenever or however you wish, keeping in mind the busy schedule or possible inconveniences that come with physical classes. The easy-to-grasp, bite-sized lessons are proven to be most effective in memorising and learning the lessons by heart. On top of that, you have the opportunity to receive a certificate after successfully completing the course! Instead of searching for hours, enrol right away on this Go Lang course from Compete High and accelerate your career in the right path with expert-outlined lessons and a guarantee of success in the long run. Who is this course for? While we refrain from discouraging anyone wanting to do this Go Lang course or impose any sort of restrictions on doing this online training, people meeting any of the following criteria will benefit the most from it: Anyone looking for the basics of Go Lang , Jobseekers in the relevant domains, Anyone with a ground knowledge/intermediate expertise in Go Lang , Anyone looking for a certificate of completion on doing an online training on this topic, Students of Go Lang , or anyone with an academic knowledge gap to bridge, Anyone with a general interest/curiosity Career Path This Go Lang course smoothens the way up your career ladder with all the relevant information, skills, and online certificate of achievements. After successfully completing the course, you can expect to move one significant step closer to achieving your professional goals - whether it's securing that job you desire, getting the promotion you deserve, or setting up that business of your dreams. Course Curriculum Module 1_ Introduction Module 1_ Introduction 00:00 Module 2_ Data Types and Variables Module 2_ Data Types and Variables 00:00 Module 3_ Conditional Statements Module 3_ Conditional Statements 00:00 Module 4_ Iteration Module 4_ Iteration 00:00 Module 5_ Functions Module 5_ Functions 00:00
Masterful WordPress 5.0 Editing Techniques
By Compete High
ð Unlock Your Website's Full Potential with 'Masterful WordPress 5.0 Editing Techniques'! ð Are you ready to elevate your WordPress editing skills to the next level? Welcome to the ultimate online course designed to empower you with the mastery of WordPress 5.0 editing techniques! ð What You'll Learn: Harness the power of the latest WordPress 5.0 features to create stunning and responsive websites effortlessly. Dive deep into the Gutenberg editor and learn advanced techniques to craft visually captivating and user-friendly content. Discover insider tips and tricks to streamline your editing process, saving you time and frustration. Customize themes and layouts like a pro, ensuring your website stands out in today's competitive online landscape. Optimize your site for SEO, speed, and user experience, boosting your online presence and visitor engagement. ð¡ Course Highlights: Comprehensive modules led by industry experts, breaking down complex concepts into easy-to-follow lessons. Hands-on exercises and practical tutorials that reinforce your learning and ensure immediate application. Access to exclusive resources, templates, and tools to enhance your WordPress editing journey. Interactive community forums for networking, collaboration, and ongoing support from fellow learners and instructors. Lifetime access to updated content, ensuring you stay ahead in the ever-evolving world of WordPress. ð Who Is This Course For? WordPress enthusiasts eager to sharpen their editing skills and unlock the full potential of WordPress 5.0. Content creators, bloggers, freelancers, and website owners seeking to enhance their online presence. Beginners looking to establish a solid foundation in WordPress editing and experienced users aiming to refine their expertise. ð Join thousands of satisfied learners who have transformed their websites with the 'Masterful WordPress 5.0 Editing Techniques' course. Don't miss this opportunity to revolutionize your web editing skills and create impactful online experiences! ð¥ Enroll today and embark on your journey towards becoming a WordPress editing virtuoso! ð¥ Course Curriculum Basic Overview 00:00 Installing WordPress 00:00 Basics of Worpress 00:00 Backing Up Your WordPress Site 00:00 Upgrading to WordPress 5.0 00:00 Finding Compatible Themes 00:00 Using the Default Theme 00:00 The Editor Layout-Part-1 00:00 The Editor Layout-Part-2 00:00 Adding Blocks 00:00 Customizing Blocks 00:00 Maniupulating Blocks 00:00 Manipulating Blocks - Part 2 00:00 Adding and Customizing Text 00:00 Adding Images 00:00 Adding Lists 00:00 Adding Videos 00:00 Adding Audio 00:00 Image Overlay 00:00 Conclusion 00:00 Advanced Overview 00:00 Quotes and Pull Quotes 00:00 Media and Text Blocks 00:00 Uploading Files 00:00 Tables 00:00 Poetry Verse Block 00:00 Adding Buttons 00:00 Adding Columns 00:00 Seperators and Spaces 00:00 Widgets 00:00 General Embed Element 00:00 Video Embeds - YouTube and Vimeo 00:00 Video Embeds - Screencast 00:00 Image Based Embeds - Imgur and Flickr 00:00 Slideshare - Speaker Desk and Presentation Based Embeds 00:00 Scrbd Embeds 00:00 Social Embeds - Facebook - Instagram - Twitter 00:00 Spotify and Soundcloud Embeds 00:00 Specialty Embeds - Meetup, Ted and Kickstarter 00:00 Conclusion - Switching To the Classic Editor 00:00

White Hat Hacking: Network Security Masterclass
By Compete High
ð Unlock the Secrets of Network Security with 'White Hat Hacking: Network Security Masterclass'! ð Are you ready to delve into the fascinating world of ethical hacking and become a master at safeguarding networks? Look no further than our comprehensive online course designed to equip you with the cutting-edge skills of a white hat hacker. ð¡ï¸ What You'll Learn: Essential Network Security Techniques: Understand the fundamentals of network security protocols and defenses. Ethical Hacking Principles: Learn how to ethically exploit vulnerabilities to fortify systems against cyber threats. Advanced Penetration Testing: Master the art of testing and securing networks from various cyber attacks. Hands-on Practical Training: Dive into real-world scenarios through interactive labs and simulations. Legal and Ethical Aspects: Discover the ethical guidelines and legal considerations in white hat hacking. ð¨âð» Who Should Enroll: IT Professionals seeking to bolster their cybersecurity skill set. Students or enthusiasts eager to explore the world of ethical hacking. Security Analysts aiming to advance their career in cybersecurity. ð Why Choose Us? Expert-Led Instruction: Learn from industry experts with years of practical experience in cybersecurity. Practical Learning: Gain hands-on experience with practical labs and real-world simulations. Flexible Learning: Access course materials anytime, anywhere, at your convenience. Certification: Earn a valuable certification upon completion, validating your expertise. ð Secure your future in cybersecurity and become a sought-after professional by enrolling in the 'White Hat Hacking: Network Security Masterclass' today! Don't wait to safeguard tomorrow's networks-start learning the art of ethical hacking now! ð Course Curriculum

iPhone Product Development Workshop
By Compete High
ð± Elevate Your Skills with the iPhone Product Development Workshop! ð Are you ready to turn your innovative ideas into remarkable iPhone apps? Unleash your creativity and master the art of iPhone product development with our comprehensive workshop designed to empower aspiring developers, entrepreneurs, and tech enthusiasts! ð What You'll Gain from Our Workshop: ð¹ In-depth understanding of iOS development principles ð¹ Hands-on experience in creating feature-rich iPhone apps ð¹ Insider insights into the latest trends and best practices in app development ð¹ Strategies for effective app monetization and market penetration ð¹ Expert guidance on optimizing user experience and interface design ð¹ Networking opportunities with like-minded individuals and industry professionals ð¨âð» Who Should Attend: Whether you're a beginner eager to kickstart your journey in app development or a seasoned developer aiming to enhance your skills, this workshop is tailored for you! Entrepreneurs seeking to understand the app development process will also find immense value in this course. ð Workshop Highlights: ð¸ Engaging live sessions with industry experts ð¸ Practical exercises and real-world case studies ð¸ Q&A sessions for personalized guidance ð¸ Access to exclusive resources and tools ð¸ Certificate of completion to showcase your newfound expertise ð¥ Limited Seats Available! Don't miss this opportunity to dive deep into the world of iPhone app development. Join us on the path to creating cutting-edge apps that stand out in the market! ð¡ Early Bird Offer: Enroll now to secure your spot and enjoy an exclusive discount! ð Register today and transform your iPhone app development skills from ordinary to extraordinary. Let's build the next big thing together! [CTA Button] Enroll Now Unlock the door to limitless possibilities in iPhone app development! ðð²â¨ Course Curriculum

Security Officer
By Compete High
ð Unlock Your Potential with the Security Officer Course! ð Are you ready to step into the world of security with confidence and authority? Look no further than our comprehensive Security Officer Course! ð In today's unpredictable world, the need for vigilant and well-trained security officers has never been greater. Whether you're considering a career change or seeking to enhance your existing skills, this course equips you with the knowledge and expertise needed to succeed in the dynamic field of security. ð¼ Why Choose Our Security Officer Course? â Comprehensive Training: Our course covers a wide range of essential topics, from threat assessment and crisis management to security protocols and emergency response strategies. â Expert Instructors: Learn from industry experts with years of experience in security operations, law enforcement, and risk management. Gain insights and practical tips that you won't find in textbooks. â Hands-On Experience: Put your knowledge into action through immersive simulations and practical exercises. Develop the confidence to handle real-world security challenges effectively. â Flexible Learning Options: Whether you prefer to study online at your own pace or participate in interactive classroom sessions, our course offers flexible learning options to suit your schedule and preferences. â Industry Recognition: Our Security Officer Course is recognized and respected by employers across various sectors, giving you a competitive edge in the job market. Who is this for? ð®âï¸ Aspiring Security Professionals: If you're passionate about maintaining safety and security in your community, this course provides the perfect foundation for launching your career in security. ð©âð¼ Career Changers: Whether you're transitioning from a different field or seeking new opportunities, our course equips you with the skills and certifications needed to pursue a rewarding career as a security officer. ð¨âð©âð§âð¦ Community Leaders: Individuals who want to make a positive impact by enhancing security measures within their neighborhoods or organizations will find this course invaluable. Career Path Upon completing our Security Officer Course, you'll be well-prepared to embark on a fulfilling career in security. Here are just a few of the exciting career paths that await you: ð¡ï¸ Security Officer: From corporate offices and retail establishments to educational institutions and government facilities, security officers play a vital role in safeguarding people and property. ð Loss Prevention Specialist: Help businesses minimize losses due to theft, fraud, and other security breaches by implementing effective loss prevention strategies and surveillance techniques. ð¨ Emergency Response Coordinator: Coordinate emergency response efforts and ensure swift and effective action in crisis situations, such as natural disasters, accidents, or security threats. ðµï¸ Private Investigator: Conduct investigations, gather evidence, and uncover valuable insights to support legal proceedings or corporate security initiatives. With the demand for skilled security professionals on the rise, there's never been a better time to invest in your future with our Security Officer Course! Don't wait-enroll today and take the first step toward a rewarding career in security. ð Remember, safety and security are not just professions-they're commitments to protecting what matters most. Join us in making a difference and becoming a trusted guardian in your community! ð Course Curriculum Chapter 01 Introduction to Security Management Chapter 01 Introduction to Security Management 00:00 Chapter 02 Security Risk Analysis and Risk Reduction Chapter 02 Security Risk Analysis and Risk Reduction 00:00 Chapter 03 Managing Security Chapter 03 Managing Security 00:00 Chapter 04 Physical Security Management Chapter 04 Physical Security Management 00:00 Chapter 05 Information Security Management Chapter 05 Information Security Management 00:00 Chapter 06 Cybersecurity Chapter 06 Cybersecurity 00:00 Chapter 07 Organisational Security Management Chapter 07 Organisational Security Management 00:00 Chapter 08 Home Security Management Chapter 08 Home Security Management 00:00

NLP Practitioner Diploma is one of our best selling and most popular course. The NLP Practitioner Diploma is organised into 02 modules and includes everything you need to become successful in this profession. To make this course more accessible for you, we have designed it for both part-time and full-time students. You can study at your own pace or become an expert in just 4hours! If you require support, our experienced tutors are always available to help you throughout the comprehensive syllabus of this course and answer all your queries through email. Why choose this course Earn an e-certificate upon successful completion. Accessible, informative modules taught by expert instructors Study in your own time, at your own pace, through your computer tablet or mobile device Benefit from instant feedback through mock exams and multiple-choice assessments Get 24/7 help or advice from our email and live chat teams Full Tutor Support on Weekdays Course Design The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of Video lessons Online study materials Mock exams Multiple-choice assessment Certification After the successful completion of the final assessment, you will receive a CPD-accredited certificate of achievement. The PDF certificate is for £9.99, and it will be sent to you immediately after through e-mail. You can get the hard copy for £15.99, which will reach your doorsteps by post. Who is this course for? NLP Practitioner Diploma is suitable for anyone who want to gain extensive knowledge, potential experience and professional skills in the related field. This is a great opportunity for all student from any academic backgrounds to learn more on this subject.

Content Management System is now the most popular computer software that is used to create and modify digital contents. This course has been illustrated to educate you on how it functions. It discusses the fundamental aspects of CMS. Hit the course to enter into the digital world. Start learning Content Management System Training that will give you enough knowledge and skills to build your dream career. About this course This Content Management System Training helps to grow your skills faster through the power of relevant content and world-class tutors. In this industry-leading bite-sized course, you will learn up-to-date knowledge in the relevant field within a few hours and get certified immediately. The modules of this course are very easy to understand and all of the topics are split into different sections. You will easily grasp and use the knowledge gained from this course in your career and go one step ahead of your competitors. The course is designed to improve your employability and provide you with the tools you need to succeed. Enrol today and start learning your essential skills. Why choose this course Earn a digital Certificate upon successful completion. Accessible, informative modules taught by expert instructors Study in your own time, at your own pace, through your computer tablet or mobile device Get 24/7 help or advice from our email and live chat teams Get full tutor support on weekdays (Monday to Friday) Course Design The Content Management System Training is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of Video lessons Online study materials Who Is This Course For:â This Content Management System Training is ideal for those who want to be skilled in this field or who wish to learn a new skill to build their dream career. If you want to gain extensive knowledge, potential experience, and be an expert in the related field then this is a great course for you to grow your career. Requirements This course is for anyone who would like to learn Content Management System Training related skills to aid his/her career path. No formal entry prerequisites are required Certification Upon successful completion of the course, you will be able to obtain your course completion e-certificate. Print copy by post is also available at an additional cost of £9.99 and PDF Certificate at £4.99. Course Content Module 1: Content Management Basics Module 2: Introduction to Content Management System (CMS) Module 3: Fundamentals of Content Management System Course Content Content Management Basics Module 1: Content Management Basics 00:18:00 Module 2: Introduction to Content Management System (CMS) 00:09:00 Module 3: Fundamentals of Content Management System 00:17:00 Order your Certificates & Transcripts Order your Certificates & Transcripts 00:00:00 Frequently Asked Questions Are there any prerequisites for taking the course? There are no specific prerequisites for this course, nor are there any formal entry requirements. All you need is an internet connection, a good understanding of English and a passion for learning for this course. Can I access the course at any time, or is there a set schedule? You have the flexibility to access the course at any time that suits your schedule. Our courses are self-paced, allowing you to study at your own pace and convenience. How long will I have access to the course? For this course, you will have access to the course materials for 1 year only. This means you can review the content as often as you like within the year, even after you've completed the course. However, if you buy Lifetime Access for the course, you will be able to access the course for a lifetime. Is there a certificate of completion provided after completing the course? Yes, upon successfully completing the course, you will receive a certificate of completion. This certificate can be a valuable addition to your professional portfolio and can be shared on your various social networks. Can I switch courses or get a refund if I'm not satisfied with the course? We want you to have a positive learning experience. If you're not satisfied with the course, you can request a course transfer or refund within 14 days of the initial purchase. How do I track my progress in the course? Our platform provides tracking tools and progress indicators for each course. You can monitor your progress, completed lessons, and assessments through your learner dashboard for the course. What if I have technical issues or difficulties with the course? If you encounter technical issues or content-related difficulties with the course, our support team is available to assist you. You can reach out to them for prompt resolution.

Master the art of hybrid team management with our comprehensive course. Learn effective techniques for transitioning, team building, and driving high performance in a hybrid work environment. Elevate your leadership skills and optimize your team’s effectiveness in today’s dynamic work landscape.
