- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1738 Basic courses in Coventry delivered Live Online
Use Cases for Business Analysis: Virtual In-House Training
By IIL Europe Ltd
Use Cases for Business Analysis: Virtual In-House Training The use case is a method for documenting the interactions between the user of a system and the system itself. Use cases have been in the software development lexicon for over twenty years, ever since it was introduced by Ivar Jacobson in the late 1980s. They were originally intended as aids to software design in object-oriented approaches. However, the method is now used throughout the Solution Development Life Cycle from elicitation through to specifying test cases, and is even applied to software development that is not object oriented. This course identifies how business analysts can apply use cases to the processes of defining the problem domain through elicitation, analyzing the problem, defining the solution, and confirming the validity and usability of the solution. What you will Learn You'll learn how to: Apply the use case method to define the problem domain and discover the conditions that need improvement in a business process Employ use cases in the analysis of requirements and information to create a solution to the business problem Translate use cases into requirements Getting Started Introductions Course structure Course goals and objectives Foundation Concepts Overview of use case modeling What is a use case model? The 'how and why' of use cases When to perform use case modeling Where use cases fit into the solution life cycle Use cases in the problem domain Use cases in the solution domain Use case strengths and weaknesses Use case variations Use case driven development Use case lexicon Use cases Actors and roles Associations Goals Boundaries Use cases though the life cycle Use cases in the life cycle Managing requirements with use cases The life cycle is use case driven Elicitation with Use Cases Overview of the basic mechanics and vocabulary of use cases Apply methods of use case elicitation to define the problem domain, or 'as is' process Use case diagrams Why diagram? Partitioning the domain Use case diagramming guidelines How to employ use case diagrams in elicitation Guidelines for use case elicitation sessions Eliciting the problem domain Use case descriptions Use case generic description template Alternative templates Elements Pre and post conditions Main Success Scenario The conversation Alternate paths Exception paths Writing good use case descriptions Eliciting the detailed workflow with use case descriptions Additional information about use cases Analyzing Requirements with Use Cases Use case analysis on existing requirements Confirming and validating requirements with use cases Confirming and validating information with use cases Defining the actors and use cases in a set of requirements Creating the scenarios Essential (requirements) use case Use case level of detail Use Case Analysis Techniques Generalization and Specialization When to use generalization or specialization Generalization and specialization of actors Generalization and specialization of use cases Examples Associating generalizations Subtleties and guidelines Use Case Extensions The <> association The <> association Applying the extensions Incorporating extension points into use case descriptions Why use these extensions? Extensions or separate use cases Guidelines for extensions Applying use case extensions Patterns and anomalies o Redundant actors Linking hierarchies Granularity issues Non-user interface use cases Quality considerations Use case modeling errors to avoid Evaluating use case descriptions Use case quality checklist Relationship between Use Cases and Business Requirements Creating a Requirements Specification from Use Cases Flowing the conversation into requirements Mapping to functional specifications Adding non-functional requirements Relating use cases to other artifacts Wire diagrams and user interface specifications Tying use cases to test cases and scenarios Project plans and project schedules Relationship between Use Cases and Functional Specifications System use cases Reviewing business use cases Balancing use cases Use case realizations Expanding and explaining complexity Activity diagrams State Machine diagrams Sequence diagrams Activity Diagrams Applying what we know Extension points Use case chaining Identifying decision points Use Case Good Practices The documentation trail for use cases Use case re-use Use case checklist Summary What did we learn, and how can we implement this in our work environment?

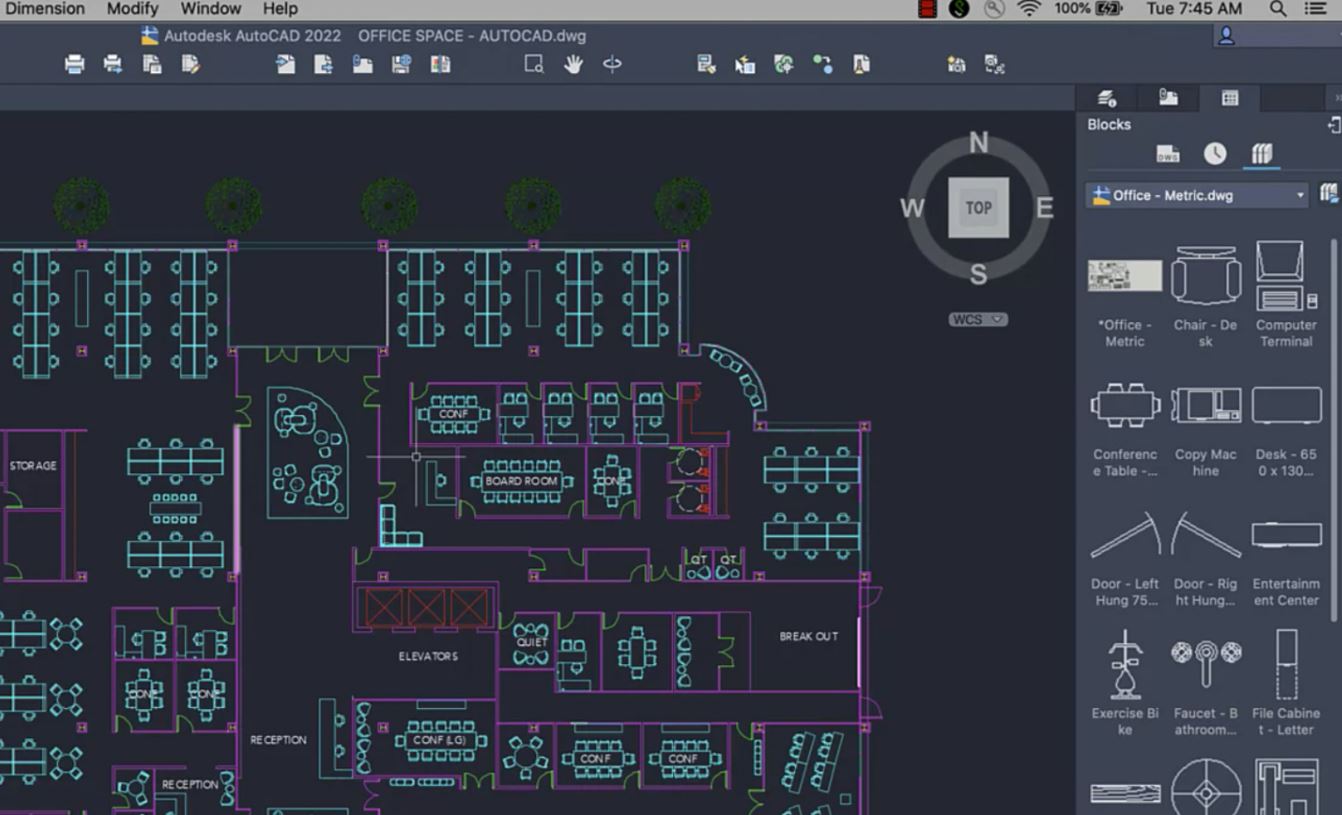
AutoCAD Mac Basics-Advanced Training
By London Design Training Courses
Why AutoCAD Mac Basics-Advanced Training Course? Click here for more info Learn 2D drawing, Plans, Sections, Elevations and advanced features. Choose in-person or live online sessions. Certified tutors, practical exercises, and career advice. Access recorded lessons and lifetime email support. Duration: 16 hrs. Method: 1-on-1, Personalized attention. Schedule: Tailor your own schedule by pre-booking a convenient hour of your choice, available from Mon to Sat between 9 am and 7 pm. AutoCAD for Mac Essentials to Advanced Training Course: Learn AutoCAD for Mac and master its popular functionalities, tailored for Mac users. Course Highlights: Thorough grounding for beginners in using AutoCAD for Mac. Develop the skills to create precise and high-quality 2D layouts and designs. Generic drawing techniques applicable to all industries. In-class or live online options available. Ideal for newcomers to AutoCAD for Mac, self-taught users, and those transitioning from other CAD tools. Autodesk Certified Tutors: Autocad Mac 1-2-1 training courses. Expert trainers with extensive experience in AutoCAD and various CAD applications. Hands-On Learning: Practical and hands-on training with demonstrations and step-by-step techniques. Support and Prerequisites: Lifetime post-course email support. Good working knowledge of the Mac OS required, no prior CAD experience needed. AutoCAD Mac Course Content: Fundamental Drawing:Creating Basic ObjectsWorking with LinesWorking with ArcsHandling Polylines Object Manipulation Techniques:Utilizing GripsMastering Object SnapsTracking Object Snap PointsEmploying Polar Tracking File Management:Saving Your WorkAuto-backupsUnderstanding Different File Formats (DXF, etc.)Disaster Recovery Accurate Object Creation:Working with UnitsUtilizing Dynamic InputUsing Inquiry Commands for Measurements Object Viewing and Navigation:Zooming TechniquesPanning Techniques Object Manipulation:Selecting Objects in the DrawingNoun/Verb SelectionQuick SelectMoving, Copying, Rotating, Mirroring, and Arraying ObjectsScaling, Trimming, and Extending Objects Organizing Drawings:Managing LayersChanging Object PropertiesExploring the Properties PaletteUsing Different Linetypes Layouts and Annotations:Working with Layouts and Page SetupsScaling Drawing ViewsAnnotating the Drawing with Text and DimensionsCreating MultileadersApplying Hatching to Objects Reusable Content:Creating and Inserting Blocks and SymbolsUsing Tool PalettesWorking with Groups Paper Space and Model Space: Understanding Model Space and Paper Space Creating Layouts and Managing Viewports Setting Viewport Scales Plotting and Output: Plotting Drawings Generating PDF Output Handling Multiple Sheet Drawings Using Plotstyles Drawing Templates and AutoCAD Tools: Creating Drawing Templates Exploring AutoCAD Toolsets Advance Plans, Sections, Elevations and Construction detailing. This course provides comprehensive instruction in AutoCAD, equipping participants with essential skills to create and manage drawings effectively for various design projects.
Coaching Skills for HR Professionals - ILM Recognised
By British School of Coaching
A practical programme for HR professionals who are keen to develop a coaching style of interaction either within their teams and/or with business stakeholders. Develop skills in taking a more engaging, non-directive approach to supporting your business and to encouraging a coaching style of communication in your organisation.

Basic Python syntax and principles of Object Orientated Programming. Most attendees are in-work IT Professional. Private individuals are also very welcome. Evening courses also running. Our Style: Hands-on, Practical Location: Online, Instructor-led Download: anaconda.com Duration: 6 weeks, 1 evening per week, 6pm - 8pm Times: arrange a time for your time zone

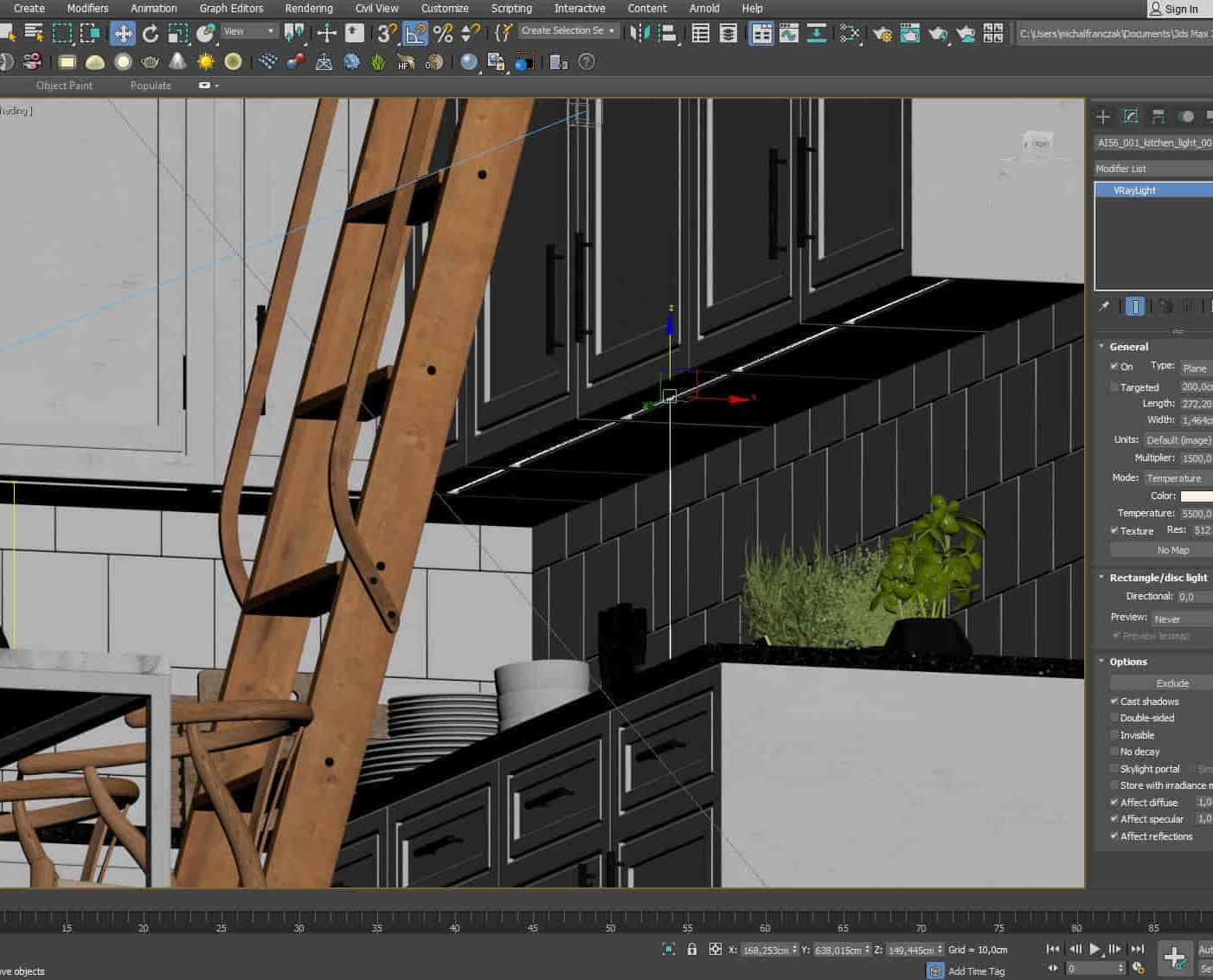
Film and Game Design Training Classes
By ATL Autocad Training London
Who is this course for? Film and Game Design Training Classes is tailored for individuals passionate about 3D for Games. Ideal for those in London seeking specialized skills for lucrative job opportunities in the gaming industry. Software we teach: 3ds max or Maya, Vray, After effects and Photoshop. Check our Website Duration: 40 hours. 1-on-1 Training. When can I book: 9 am - 4 pm (Choose your preferred day and time once a week). Monday to Saturday: 9 am - 7 pm (Flexible timing with advance booking). Course Title: Film & Game Design Training Classes Option A - 40-Hour Program: Option A offers comprehensive training for aspiring film and game designers, covering vital industry software and skills. Module 1: 3ds Max and Advanced Animation (20 hours) - Introduction to 3ds Max: Interface overview. - Basic 3D Modeling: Creating simple 3D objects. - Advanced 3D Modeling: Complex modeling techniques. - Texturing and Materials: Applying textures and materials. - Lighting and Rendering: Scene lighting and rendering setup. - Character Animation: Rigging and animating characters. - Advanced Animation Techniques: Keyframes, motion paths, and more. - Scene Composition: Assembling complex scenes. Module 2: Vray (6 hours) - Vray Introduction: Understanding Vray renderer. - Lighting with Vray: Creating realistic lighting setups. - Material Creation: Crafting materials for realistic surfaces. - Rendering with Vray: Optimization and execution. Module 3: Photoshop (6 hours) - Photoshop Basics: Navigating the interface. - Image Editing: Crop, resize, and enhance. - Layer Management: Working with layers. - Text and Typography: Adding and manipulating text. - Photo Manipulation: Advanced image techniques. - Creating Visual Assets: Designing textures and graphics. Module 4: After Effects: Video and Sound Editing (8 hours) - Introduction to After Effects: Interface overview. - Video Editing: Cut, trim, and arrange video clips. - Transitions and Effects: Apply visual effects and transitions. - Sound Editing: Add and edit audio tracks. - Motion Graphics: Create motion graphics and titles. - Exporting and Rendering: Prepare projects for final output. Film & Game Design Training Course Information Are you ready to explore our Training Course for Film & Game Designers? Here's a comprehensive overview to guide you through: When Can I Book This Training Course? Personalize your training with our flexible 1-on-1 sessions. Tailor your schedule by pre-booking your preferred hours. Available Monday to Saturday, 9 a.m. to 7 p.m. For phone bookings, call 02077202581. Training Duration The course spans 40 hours, allowing flexibility for your ideal schedule. Training Method Experience 1-on-1 training, in-person Face to Face or Live Online. Expect personalized attention, tailored content, flexible learning, and individual support. Opt for Live Online 1-on-1 sessions via Zoom for convenience. Enroll Today Ready to start your exciting journey? Click the link below to enroll in our 1-on-1 Course. Film & Game Design Training Overview In our comprehensive training program for film and game designers, refine your skills using industry-leading software tools. This prepares you to bring your creative visions to life. Option A: 3ds Max and Advanced Animation (20 hours) Vray (6 hours) Photoshop (6 hours) Aftereffects: Video and Sound Editing (8 hours) Option B: Maya and Advanced Animation (20 hours) Vray (6 hours) Photoshop (6 hours) Aftereffects: Video and Sound Editing (8 hours) Both options offer flexibility for Mac and Windows operating systems, ensuring accessibility for all learners. Key Benefits Price Assurance: Exceptional value for your film and game design career investment. One-on-One Training: Customized learning for your unique style. Flexible Scheduling: Choose your training time, available Monday to Sunday, 9 am to 8 pm. Lifetime Email and Phone Support: Ongoing assistance beyond training for your career growth. Computer Configuration Assistance: Guidance for seamless software installation. Referral Benefits: Special discounts for referrals and savings on group training. Embark on a transformative journey and unlock your potential in the thrilling fields of film and game design!

TRAINING FOR FILM & GAME DESIGNERS One to One Online or Face to Face
By Real Animation Works
Film and VFX face to face training customised and bespoke. One to One Online or Face to Face

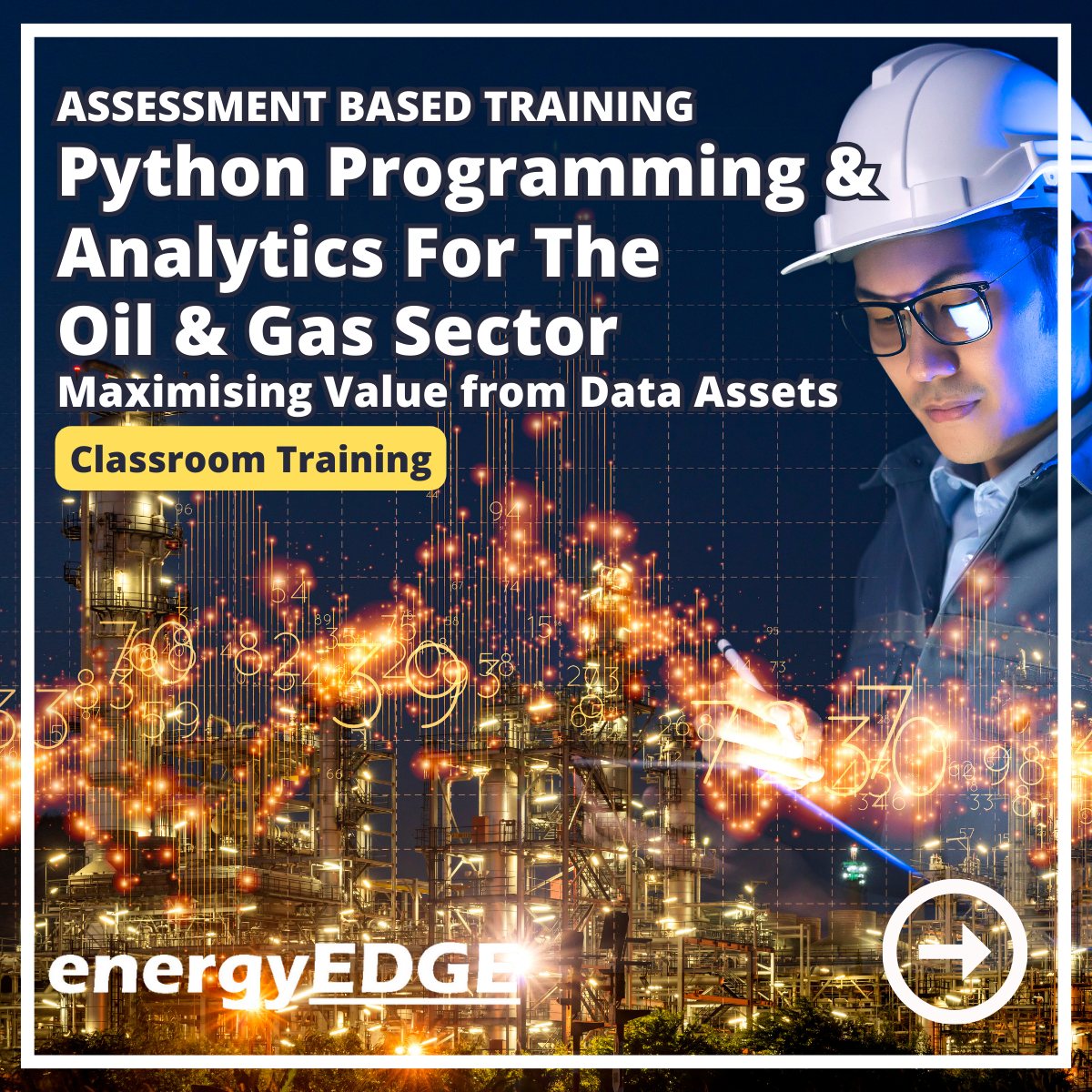
Assessment Based Training - Python Programming & Analytics for the Oil & Gas Sector - Maximising Value from Data Assets
By EnergyEdge - Training for a Sustainable Energy Future
Maximize the value of data assets in the oil and gas sector with EnergyEdge's assessment-based training course on Python programming and analytics.
Personalized AutoCAD Training for Interior Designers: Live Online and One-to-One
By Real Animation Works
Autocad face to face training customised and bespoke. In-person
3D Studio Max and CAD Courses 1 on 1
By ATL Autocad Training London
These courses are designed for aspiring 3D artists, students, graduates, creative professionals, CAD designers, and anyone passionate about 3D art. Whether you're looking to launch a career, enhance existing skills, or explore new creative avenues, our courses provide comprehensive training tailored to various skill levels and interests. Check our Website Duration: 16 hours Method: 1-on-1 and Tailored content Dates and Times: Select your preferred hour from Monday to Saturday, available between 9 am and 7 pm. CAD and 3D Studio Max Training Course Duration: 16 hours Course Outline: Introduction to AutoCAD Familiarizing yourself with the AutoCAD interface Navigating the drawing environment Mastering fundamental 2D geometry creation Exploring essential drawing tools and commands Introduction to blocks and symbols for efficient design Advanced AutoCAD Techniques Delving into advanced drawing methods Proficiently manipulating and editing 2D geometry Crafting custom symbols and blocks for enhanced productivity Working with text and annotations for clear communication Utilizing layers and line types for organized design 3D Modeling in AutoCAD Venturing into the world of 3D modeling Precision crafting of 3D solids and surfaces Seamless modification and manipulation of 3D geometry Crafting custom materials and textures for realistic designs Effective utilization of AutoCAD's lighting and camera systems Introduction to 3ds Max Embracing the 3ds Max interface and configuring the workspace Proficiency in navigating within 3ds Max Understanding the viewport for optimized design Exploring basic 3D modeling techniques in 3ds Max Materials and Textures in 3ds Max Application and modification of textures for enhanced designs Mastering the art of UVW mapping for precise texturing Utilizing the material editor for creative freedom Crafting custom materials aligned with your design vision Harnessing the power of Vray materials for lifelike renders Lighting in 3ds Max Introduction to various lighting techniques Grasping light properties for impactful designs Strategic setup of lights to enhance scenes Illuminating scenes with Vray lights Cameras in 3ds Max Mastery of camera systems in 3ds Max Exploring camera properties for cinematic effects Creating animations with cameras for dynamic scenes Utilizing Vray cameras for stunning renders Rendering in 3ds Max Unveiling the art of rendering Utilizing Vray Global Illumination for realistic lighting Leveraging Vray Physical Cameras for precise control Enhancing scenes with Vray HDRI Lighting Following a Vray Rendering Workflow for professional results Advanced Modeling Techniques Proficiency in crafting complex geometry Utilizing modifiers for intricate designs Exploring polygonal modeling for versatile creations Creating both organic and inorganic models with expertise Unleashing the potential of advanced modeling techniques Projects Application of acquired skills to create real-world scenes Designing a detailed interior scene with meticulous attention Crafting a visually impactful exterior scene Creating a complex scene featuring multiple objects and materials Course Requirements: A computer with AutoCAD and 3ds Max installed Basic knowledge of computer operations A keen interest in 2D and 3D modeling and design Course Goals: Upon course completion, you will possess a comprehensive understanding of AutoCAD and 3ds Max, enabling you to craft intricate 3D scenes enriched with advanced materials, textures, lighting, and rendering. These newfound skills empower you to advance your capabilities in both 2D and 3D modeling and rendering. Upon successful completion of this comprehensive AutoCAD and 3ds Max training, participants will attain the following skills: AutoCAD Proficiency: Mastery of 2D geometry, drawing tools, and symbols. Advanced AutoCAD Techniques: Expertise in editing, custom blocks, text, and layers. 3D Modeling in AutoCAD: Competence in crafting 3D solids, textures, and lighting. Introduction to 3ds Max: Proficient navigation of the interface and fundamental 3D modeling. Materials and Textures: Application and customization of textures using Vray. Lighting and Cameras: Mastery of lighting and camera systems within 3ds Max. Rendering: Production of high-quality renders through Vray. Advanced Modeling: Proficiency in handling complex geometry and creating organic models. Real-World Projects: Capability to design interiors, exteriors, and intricate scenes. Skills Acquired: Mastering 3D Modeling Techniques in 3D Studio Max Advanced Texturing and Material Application Skills Proficiency in Lighting and Rendering Techniques Expertise in Animation and Keyframe Techniques Comprehensive Scene Composition and Camera Setup Knowledge Career Opportunities: Senior 3D Modeler Experienced CAD Designer Lighting and Rendering Specialist Animation Director Architectural Visualization Expert Upon completing our 3D Studio Max and CAD Courses, students will acquire advanced 3D modeling, animation, and CAD design skills, paving the way for rewarding careers in roles such as Senior 3D Modeler, CAD Designer, Lighting Specialist, Animation Director, and Architectural Visualization Expert. You will gain access to the following benefits: An Autocad and 3ds Max Certificate of Attendance. A comprehensive PDF training guide for 3ds Max and CAD. Real-time feedback during sessions, with the option to record them as video archives. We offer the following advantages: Price guarantee to ensure the best value for your investment. Personalized one-on-one training for focused learning. Flexible scheduling options available seven days a week, from 9 am to 7 pm. Lifetime email and phone support for ongoing assistance. Assistance with software installation and computer setup. Referral discounts and special offers on group training courses.
Garden Design Courses with Vectorworks Training Program
By ATL Autocad Training London
Why Choose Garden Design Courses with Vectorworks Training Program? Designed to enhance your skills in crafting stunning garden designs. Led by certified tutors. From 2D layouts to 3D landscapes and detailed plans and visualizations. Check our Website Details: 1-on-1 training. Customize your schedule, available Mon to Sat 9 am and 7 am Call 02077202581 to book your session over the phone. Duration: 16 hours. "You can divide this over multiple days to suit your schedule." Approach: 1-on-1 in-person or live online. Course Duration: 16 hours Course Description: This advanced Vectorworks course is tailored for individuals who already possess basic knowledge of the software and wish to enhance their skills to become proficient users. Participants will learn more advanced 2D and 3D techniques, including advanced 3D modeling, rendering, visualization, and customizing Vectorworks to suit their specific needs and workflows. The course will cover topics such as creating custom tools, working with planting plans, and integrating with AutoCAD. Course Outline: Module 1: Vectorworks Interface and Basic Concepts - Understanding the Vectorworks interface and palettes - Opening, saving, and managing files - Creating and editing objects and shapes - Utilizing Undo/Redo and Snaps for precision - Applying graphic attributes and working with dimensions Module 2: Modeling and Drawing Techniques - Exploring advanced tools and commands in detail - Integrating with AutoCAD and data exchange - Creating, modifying, and editing text - Utilizing callout text tool for annotations - Organizing information using design layers and classes Module 3: Working with Buildings and Models - Utilizing design layers and sheet layers for architectural projects - Assigning objects to layers and classes - Working with viewports and sheet layers for presentation - Drawing buildings, including walls and roofs - Setting up and rendering perspective views Module 4: Creating Site and Landscape Plans - Importing land surveys or architects' files - Drawing site surveys and working with hard landscape elements - Adding and customizing plantings using the plant tool - Editing plant definitions and creating custom plant symbols - Generating plant schedules and reports Module 5: Vectorworks Architect Features - Setting up files and scaling the drawing - Customizing text styles and dimension standards - Working with scanned images and creating site models - Designing floors, doors, and windows using standard Vectorworks elements - Creating and managing title blocks, labels, notes, and keynotes Module 6: Working Drawings and Final Project - Developing the final project with 2D and 3D elements - Applying site modifiers and stairs to the design - Generating printing layouts for presentations - Creating working drawings with detailed plans and elevations Download Vectorworks Trial https://www.vectorworks.net/trial Learning Outcomes: Master Vectorworks Tools: Proficiency in Vectorworks software, specializing in garden design features. Comprehensive Garden Design Skills: Expertise in 2D/3D modeling, plant selection, hardscapes, and irrigation systems. Professional Documentation: Create precise construction documents and visually compelling presentations. Collaboration and Project Management: Understand collaborative workflows, project management, and client communication. Job Opportunities: Landscape Designer/Architect: Design aesthetically pleasing and functional gardens for residential and commercial spaces. Garden Consultant/Horticulturist: Provide expert advice on plant selection, garden health, and sustainable practices. Entrepreneur/Educator: Start your own garden design business or teach garden design principles and techniques. Elevate your career with the Vectorworks Garden Design Course! Vectorworks Garden Design Mastery Course Course Enrollment Details: Unlock a personalized learning journey with our flexible 1-on-1 training sessions. Customize your schedule by reserving a time slot at your convenience, available Monday to Saturday between 9 a.m. and 7 p.m. Call 02077202581 to book your session over the phone. Training Duration: 16 hours. "You can divide these 16 hours over multiple days to suit your schedule." Training Approach: Experience tailored 1-on-1 sessions, either in-person or live online, providing individualized attention, customized content, flexible pacing, and comprehensive support. Live online 1-on-1 sessions via Zoom are also available. Course Overview: The Vectorworks Garden Design Mastery Course is meticulously crafted to empower participants with the expertise needed to craft exquisite garden designs using Vectorworks software. Guided by certified tutors and industry professionals, this program delivers a profound understanding of Vectorworks tools specifically tailored for garden design, enabling you to transform your landscaping ideas into breathtaking realities. Throughout the course, delve into the specialized features and functionalities of Vectorworks tailored for garden design. From 2D layouts to intricate 3D landscapes, master the art of utilizing Vectorworks to create detailed plans, visualize designs, and produce impeccable documentation for your garden projects. Tailored Training Excellence: Personalized One-to-One Guidance: Experience individualized coaching with undivided attention and customized instruction. Flexible Scheduling: Choose your preferred training slots, tailored to your schedule, even on weekends and late evenings. Post-Course Support and Comprehensive Materials: Access free online support post-training and receive detailed PDF notes and handouts for effective learning. Recognition of Achievement: Earn a Certificate of Attendance upon course completion, validating your expertise. Affordable Learning Solutions: Enjoy budget-friendly training rates without compromising on the quality of education. Tech Assistance and Referral Benefits: Receive software setup support and unlock referral discounts by recommending friends. Group Learning Perks and Tailored Courses: Avail special discounts for group sessions and experience customized training designed just for you. Elevate your skills affordably with our flexible schedules and personalized support.
