- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
299 Aid courses in Cardiff delivered Live Online
IATP - Asbestos Awareness Online
By Airborne Environmental Consultants Ltd
If you have no intention of removing asbestos but work on buildings built or refurbished before the year 2000, asbestos could be present. You will need awareness training so you know how to avoid the risks. Asbestos awareness training should be given to employees whose work could foreseeably disturb the fabric of a building and expose them to asbestos or who supervise or influence the work. In particular, it should be given to those workers in the refurbishment, maintenance and allied trades where it is foreseeable that ACMs may become exposed during their work.

Quarterly Mental health First Aider Facilitated Forum with a Registered Mental Health Nurse
By Mindmaps Wellbeing
Providing Guidance & Support for MHFAiders: giving reassurance they are not alone. Our MHFAider guidance & support forums are tailored to provide MHFAiders with the clarity they need to excel in their role. We believe it's important to offer a safe space for MHFAiders to discuss their role, while staying up to date with the latest best practices and information. Mental Health First-Aiders and Champions forum for open discussions, guidance, support, and focus topic learning with a registered Mental Health Nurse.

The project management toolkit (In-House)
By The In House Training Company
The aim of this course is to provide project managers, project engineers and project support staff with a toolkit they can use on their projects. The tools range from the simple that can be used on all projects to the advanced that can be used where appropriate. This programme will help the participants to: Identify and engage with stakeholders Use tools for requirements gathering and scope management Produce better estimates using a range of techniques Develop more reliable schedules Effectively manage delivery DAY ONE 1 Introduction Overview of the programme Review of participants' needs and objectives 2 Stakeholder management Using PESTLE to aid stakeholder identification Stakeholder mapping The Salience model Stakeholder engagement grid 3 Requirements management Using prototypes and models to elucidate requirements Prioritising techniques Roadmaps Requirements traceability 4 Scope management Work breakdown structures Responsibility assignment matrix 5 Delivery approaches Sequential Agile 6 Estimating Comparative estimating Parametric Bottom-up Three-point estimating Delphi and Planning Poker Creating realistic budgets DAY TWO 7 Scheduling Critical path analysis Smoothing and levelling Timeboxing Team boards Monte Carlo simulations Probability of completion 8 People management Situational Leadership The Tuckman model Negotiation Conflict management Belbin 9 Monitoring and control Earned value management 10 Course review and action planning Identify actions to be implemented individually Conclusion PMI, CAPM, PMP and PMBOK are registered marks of the Project Management Institute, Inc.

C)TIA - Certified Threat Intelligence Analyst Mile 2
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for IS Security Officers IS Managers Risk Managers Auditors Information Systems Owners IS Control Assessors System Managers Government Employees Overview Upon completion, Certified Threat Intelligence Analyst students will be able to proactively collect threat data and implement strategies to limit exposure to those threats. Additionally, they will be prepared to take the C)TIA exam Everywhere you turn today, you hear about the need for threat intelligence analysis! However, in some cases, it is just a buzzword, while in other cases, threat intelligence is being touted as the remedy toward advanced persistent threats. The real question is, how do we leverage threat intelligence to reduce network vulnerabilities without wasting time and money? The answer is simple, Mile2?s Certified Threat Intelligence Analyst course. Mile2?s CTIA course will help security professionals learn how to make good use of the many sources of threat intelligence. It will aid an individual to understand what threat sources are helpful, which specific threats are targeted and which ones may need minor adjustments to monitor within your organization. Mile2?s CTIA course focuses heavily on hands-on labs, concentrating on discerning and interpreting threats and responding to them.ÿ The CTIA course focuses overall on current significant threats, threat actors, and identification procedures so that cyber-security professionals can implement the best policies and procures for their organizational security posture. Once complete, the student will be competent toward improving a company?s existing security infrastructure. Policies and methodologies learned in the CTIA will allow the student to use threat intelligence concepts to decrease overall company risk. Course Outline Threat Intelligence Basics Cyber Threats Threat Actors Case Studies Threat Identification Proactive Approach

IATP - Asbestos Awareness refresher
By Airborne Environmental Consultants Ltd
If you have no intention of removing asbestos but work on buildings built or refurbished before the year 2000, asbestos could be present. You will need awareness training so you know how to avoid the risks. Asbestos awareness training should be given to employees whose work could foreseeably disturb the fabric of a building and expose them to asbestos or who supervise or influence the work. In particular, it should be given to those workers in the refurbishment, maintenance and allied trades where it is foreseeable that ACMs may become exposed during their work.

IATP - Asbestos Awareness Online refresher
By Airborne Environmental Consultants Ltd
If you have no intention of removing asbestos but work on buildings built or refurbished before the year 2000, asbestos could be present. You will need awareness training so you know how to avoid the risks. Asbestos awareness training should be given to employees whose work could foreseeably disturb the fabric of a building and expose them to asbestos or who supervise or influence the work. In particular, it should be given to those workers in the refurbishment, maintenance and allied trades where it is foreseeable that ACMs may become exposed during their work.

The Mechanics of Mediumship Spring
By The Psychic Medium Handbook
The Mechanics of Mediumship. A beginners guide to everything you need to know. How to become a professional psychic medium. Able to give short, accurate, evidential messages. This course runs over 5 weeks and during our time together we will explore five easy to follow parts. 1: What mediumship is and the different types, including your role as a professional medium and the differences between working in the psychic modality and when you are connected to spirit. 2: Activating and building your power within, and the difference between meditation, and attunement both to the spirit world and using your psychic modality. 3: The six different senses available to you, which are your strongest and whether you are perceiving them objectively or subjectively. 4: What is and what is not evidence in mediumship, understanding the different types of evidence available and defining practical and emotional evidence. 5: Surrendering to spirit, building confidence to receive specific unique information, and understanding the reasons why you receive a no response. Guidance on making positive, strong, statements filling your sitter with confidence, building a truly extraordinary professional reading.

The Mechanics of Mediumship
By The Psychic Medium Handbook
The Mechanics of Mediumship. A beginners guide to everything you need to know. How to become a professional psychic medium. Able to give short, accurate, evidential messages. This course runs over 5 weeks and during our time together we will explore five easy to follow parts. 1: What mediumship is and the different types, including your role as a professional medium and the differences between working in the psychic modality and when you are connected to spirit. 2: Activating and building your power within, and the difference between meditation, and attunement both to the spirit world and using your psychic modality. 3: The six different senses available to you, which are your strongest and whether you are perceiving them objectively or subjectively. 4: What is and what is not evidence in mediumship, understanding the different types of evidence available and defining practical and emotional evidence. 5: Surrendering to spirit, building confidence to receive specific unique information, and understanding the reasons why you receive a no response. Guidance on making positive, strong, statements filling your sitter with confidence, building a truly extraordinary professional reading.

Securing UNIX systems training course description This course teaches you everything you need to know to build a safe Linux environment. The first section handles cryptography and authentication with certificates, openssl, mod_ssl, DNSSEC and filesystem encryption. Then Host security and hardening is covered with intrusion detection, and also user management and authentication. Filesystem Access control is then covered. Finally network security is covered with network hardening, packet filtering and VPNs. What will you learn Secure UNIX accounts. Secure UNIX file systems. Secure UNIX access through the network. Securing UNIX systems course details Who will benefit: Linux technical staff needing to secure their systems. Prerequisites: Linux system administration (LPIC-1) Duration 5 days Securing UNIX systems course contents Cryptography Certificates and Public Key Infrastructures X.509 certificates, lifecycle, fields and certificate extensions. Trust chains and PKI. openssl. Public and private keys. Certification authority. Manage server and client certificates. Revoke certificates and CAs. Encryption, signing and authentication SSL, TLS, protocol versions. Transport layer security threats, e.g. MITM. Apache HTTPD with mod_ssl for HTTPS service, including SNI and HSTS. HTTPD with mod_ssl to authenticate users using certificates. HTTPD with mod_ssl to provide OCSP stapling. Use OpenSSL for SSL/TLS client and server tests. Encrypted File Systems Block device and file system encryption. dm-crypt with LUKS to encrypt block devices. eCryptfs to encrypt file systems, including home directories and, PAM integration, plain dm-crypt and EncFS. DNS and cryptography DNSSEC and DANE. BIND as an authoritative name server serving DNSSEC secured zones. BIND as an recursive name server that performs DNSSEC validation, KSK, ZSK, Key Tag, Key generation, key storage, key management and key rollover, Maintenance and resigning of zones, Use DANE. TSIG. Host Security Host Hardening BIOS and boot loader (GRUB 2) security. Disable useless software and services, sysctl for security related kernel configuration, particularly ASLR, Exec-Shield and IP / ICMP configuration, Exec-Shield and IP / ICMP configuration, Limit resource usage. Work with chroot environments, Security advantages of virtualization. Host Intrusion Detection The Linux Audit system, chkrootkit, rkhunter, including updates, Linux Malware Detect, Automate host scans using cron, AIDE, including rule management, OpenSCAP. User Management and Authentication NSS and PAM, Enforce password policies. Lock accounts automatically after failed login attempts, SSSD, Configure NSS and PAM for use with SSSD, SSSD authentication against Active Directory, IPA, LDAP, Kerberos and local domains, Kerberos and local domains, Kerberos tickets. FreeIPA Installation and Samba Integration FreeIPA, architecture and components. Install and manage a FreeIPA server and domain, Active Directory replication and Kerberos cross-realm trusts, sudo, autofs, SSH and SELinux integration in FreeIPA. Access Control Discretionary Access Control File ownership and permissions, SUID, SGID. Access control lists, extended attributes and attribute classes. Mandatory Access Control TE, RBAC, MAC, DAC. SELinux, AppArmor and Smack. etwork File Systems NFSv4 security issues and improvements, NFSv4 server and clients, NFSv4 authentication mechanisms (LIPKEY, SPKM, Kerberos), NFSv4 pseudo file system, NFSv4 ACLs. CIFS clients, CIFS Unix Extensions, CIFS security modes (NTLM, Kerberos), mapping and handling of CIFS ACLs and SIDs in a Linux system. Network Security Network Hardening FreeRADIUS, nmap, scan methods. Wireshark, filters and statistics. Rogue router advertisements and DHCP messages. Network Intrusion Detection ntop, Cacti, bandwidth usage monitoring, Snort, rule management, OpenVAS, NASL. Packet Filtering Firewall architectures, DMZ, netfilter, iptables and ip6tables, standard modules, tests and targets. IPv4 and IPv6 packet filtering. Connection tracking, NAT. IP sets and netfilter rules, nftables and nft. ebtables. conntrackd Virtual Private Networks OpenVPN server and clients for both bridged and routed VPN networks. IPsec server and clients for routed VPN networks using IPsec-Tools / racoon. L2TP.

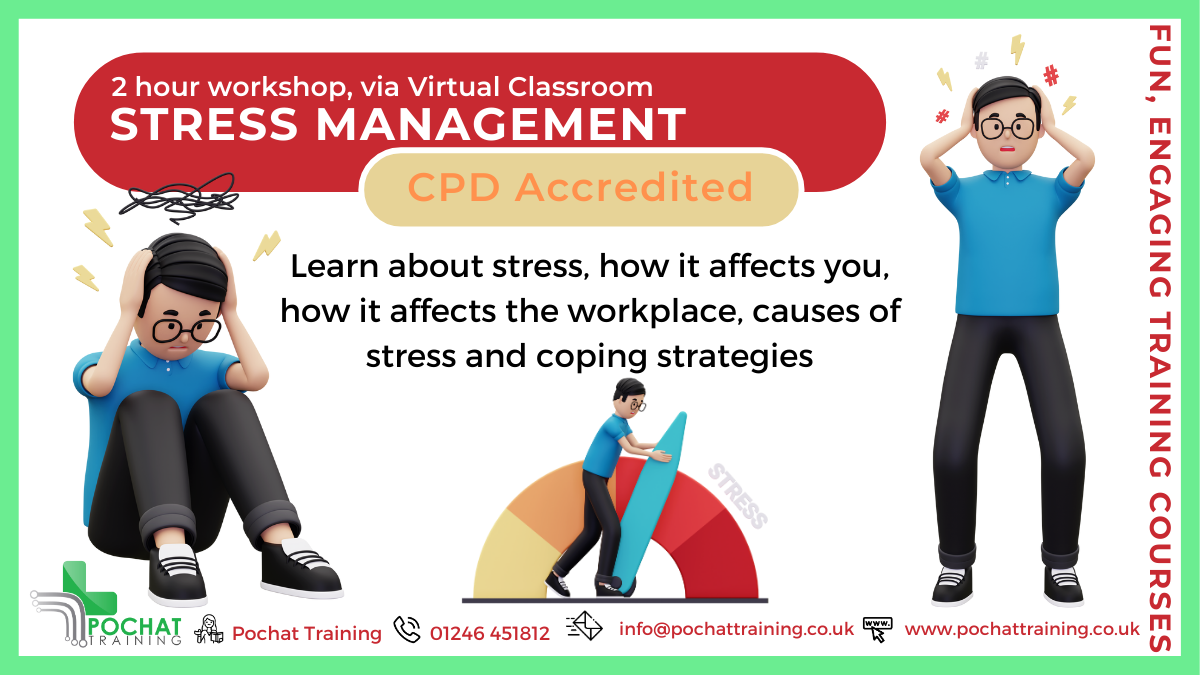
Tackle Stress Before It Tackles You! Work-related stress affects 875,000 people every year, and its impacts go beyond the workplace—affecting your mind, body, and personal life. But it doesn’t have to be this way. Join our Stress Management Workshops to: ✔️ Understand the difference between stress and pressure ✔️ Learn the causes of stress in and out of the workplace ✔️ Discover practical coping strategies and build mental resilience These workshops are packed with insights, tools, and strategies to help you take control of your stress levels and improve your well-being—personally and professionally. There are two different ones to choose from - a 2 hour workshop and a 4 hour workshop! Course Contents of 2 hour course: What is Stress Stress versus Pressure Statistics Absenteeism, Presenteeism and Leaveism Workplace Causes of Stress Personal Causes of Stress Short-Term and Long-Term Effects of Stress Coping Strategies Mental Resilience Benefits of this Workshop: In 2022/23. 875,000 people suffered from work-related stress, depression or anxiety The affects of stress are far reaching, affecting one's mind, body, social and personal life Become more aware of what stresses you, what is does to you and find ways to reduce those stress levels