- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
313 Windows courses delivered Live Online
Data Analysis and Visualization with Microsoft Excel
By Mpi Learning - Professional Learning And Development Provider
This course is designed for students who already have foundational knowledge and skills in Excel and who wish to perform robust and advanced data and statistical analysis with Microsoft Excel using PivotTables, use tools such as Power Pivot and the Data Analysis ToolPak to analyze data and visualize data and insights using advanced visualizations in charts and dashboards in Excel.
TS619G IBM Spectrum Protect version 8.1.12 Implementation and Administration
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Implementers and administrators who are new to IBM Spectrum Protect data management. Overview Describe the purpose of IBM Spectrum Protect Install and configure the IBM Spectrum Protect components Use the administrative and client interfaces Discuss storage methodology options and create storage pool Customize data movement and retention policies to meet business requirements Configure the IBM Spectrum Protect database and storage pools for protection Optimize client configuration Perform backup, restore, archive and retrieve operations Organize daily tasks required to protect the IBM Spectrum Protect environment Automate and monitor client and administrative tasks and events IBM Spectrum Protect 8.1.12 is a data backup and recovery solution designed to help you manage your data retention, reduce the cost of storage, and provide appropriate recovery point objectives to meet any service level agreement. IBM Spectrum Protect offers improved efficiency and flexibility using object-based data management and policy driven retention.This five-day course will focus on implementation and basic administration of an IBM Spectrum Protect environment. The hands-on lab exercises are performed on a Windows 2016 environment. The course materials include examples of AIX and Linux commands, when different from Windows. Unit 1 Concepts and components Unit 2 Installation and configuration Unit 3 Interfaces and monitoring Unit 4 Storage pools and devices Unit 5 Policy management, data movement, and expiration Unit 6 Server database and storage pool management Unit 7 Client configuration and management Unit 8 Client data protection Unit 9 Daily operations and maintenance Unit 10 Schedules and reports Additional course details: Nexus Humans TS619G IBM Spectrum Protect version 8.1.12 Implementation and Administration training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the TS619G IBM Spectrum Protect version 8.1.12 Implementation and Administration course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

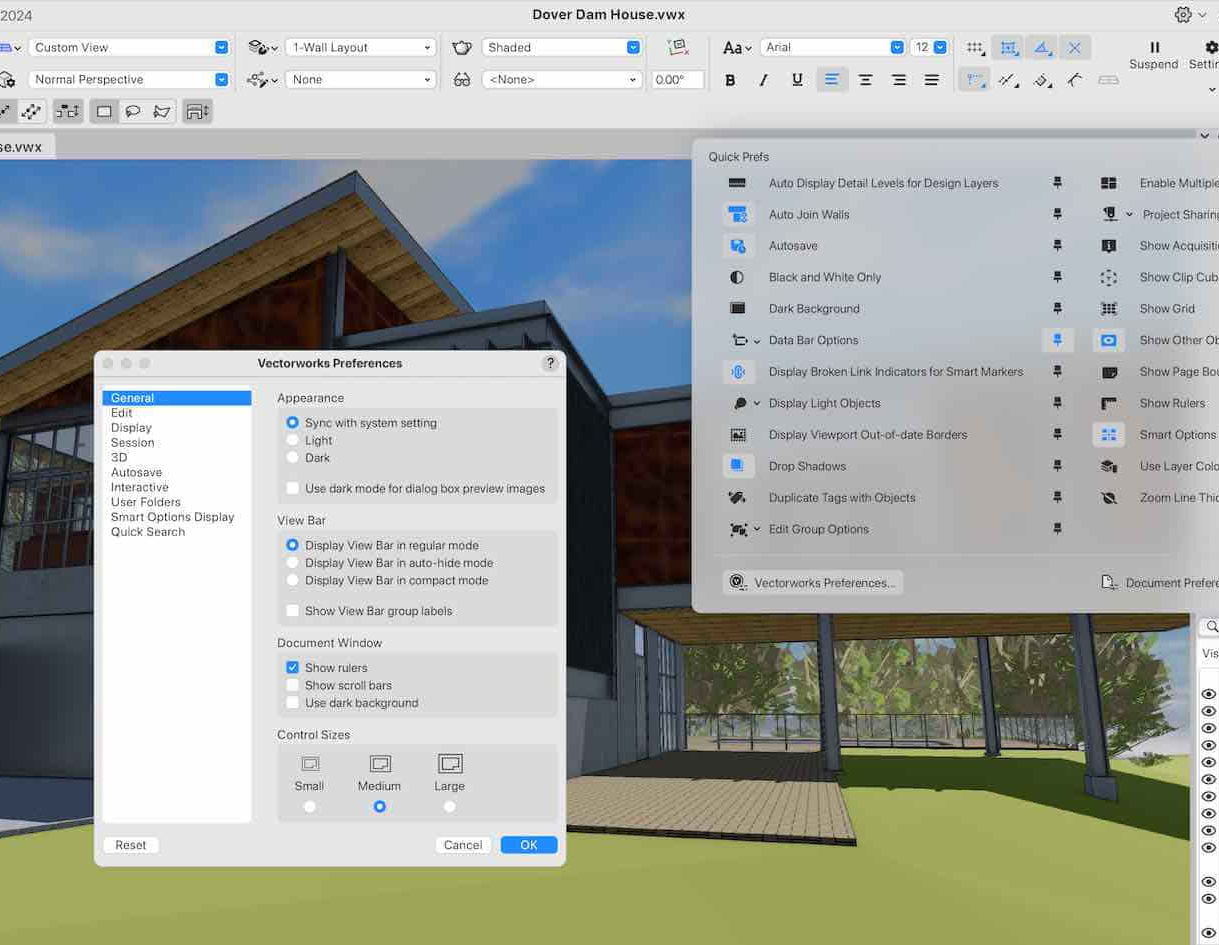
Vectorworks 2D Basics Level Training Course
By ATL Autocad Training London
Why Vectorworks 2D Basics Level Training Course? Vectorworks excels in 2D design, delivering exceptional results and serving as a robust 2D design tool. The Fundamentals course provides customizable tools for precise 2D drawings, while VectorWorks Architect streamlines the process with user-friendly, easy-to-learn tools. Click here for more info: Website Course Details: 10 hrs, Flexible 1-on-1 sessions, in-person or online. 9 am and 7 pm (Mon-Sat).10 hours, split as needed for your schedule. Module 1: Understanding CAD and Vectorworks The Role of CAD in Design Introduction to Vectorworks Software Module 2: Setting Up Your Workspace Workspace Configuration Basic Options and Preferences Module 3: Foundational Drawing Skills Drawing Techniques Selecting Objects Module 4: Advanced Object Editing Combining Shapes Mirroring Objects Rotating Objects Grouping Objects Module 5: Precision Drawing and Scaling Working with Scale Setting Preferences Saving Templates Module 6: Accurate Object Placement Drawing Precision Moving Objects Precisely Module 7: Advanced Editing Techniques Using Fillet Employing Offset Module 8: Introduction to Object Attributes and Groups Basic Attributes Editing Object Groups Module 9: Duplicating Objects Linear Duplicates Rectangular Duplicates Circular Duplicates Module 10: Creating Room Plans Designing Walls Incorporating Windows and Doors Module 11: Room Plan Development Room Plan Drawing Methods Module 12: Utilizing Additional Attributes Hatch Patterns Gradients Image Fills Module 13: Drawing Elevations Elevation Techniques Effective Methods Module 14: Importing Images for Graphics Graphic Illustration Image Integration Module 15: Symbols and Resource Management Creating Symbols Introduction to Resource Browser Module 16: Organizing Drawings with Design Layers Design Layer Usage Module 17: Labeling Drawings and Title Blocks Drawing Labels Title Block Text Module 18: Plotting and Printing User Interface and Terminology Printing Techniques Module 19: Creating Drawing Sheets A1, A2, and A3 Sheets Module 20: Utilizing Viewports Multiple Views Module 21: Professional Model Presentation Paper Space Presentation Converting to PDFs Module 22: Managing Files and Projects Module 23: Displaying Objects and Terminology Module 24: Objects and Data Management Module 25: Precise Object Placement Object Snaps Quick Select Module 26: Dividing and Measuring Objects Module 27: Dimensioning and Annotation Module 28: Working with Text Module 29: Custom Tool Palettes Module 30: Organizing Tool Palettes Module 31: Effective Tool Palette Usage Module 32: Standard Views and Drawing Techniques Module 33: Drawing Curves Arcs, Donuts, and Ellipses Module 34: Real-World Units and Measurements Module 35: Object Manipulation Changing Object Angles Module 36: File Management Saving, Exiting, and Opening Projects Module 37: Creating Mirror Images Module 38: Introduction to 3D Modeling Creating Extrusions Basic 3D Concepts Outcomes and Vectorworks Jobs: Vectorworks Proficiency: Gain expertise in using Vectorworks software for design tasks. 2D Design Skills: Create accurate 2D drawings and architectural plans. Advanced Editing: Efficiently manipulate and edit objects in your designs. Precision Drawing: Develop skills for precise scaling and drawing. These skills open doors to careers in design, architecture, engineering, entertainment, and more. Potential Jobs: Architectural Drafter Interior Designer Landscape Designer AD Technician Graphic Designer Construction Estimator Product Designer Set Designer Event Planner Urban Planner Vectorworks 2D Training Course Our Vectorworks training is thoughtfully designed to educate and inspire designers at every skill level. Whether you're just starting or a seasoned pro, our courses will furnish you with fresh skills, streamline your workflows, and unleash the full potential of your Vectorworks software. Online Training Choices Tailored Online Sessions: Customized training sessions tailored to your specific requirements and skill level. Virtual Classroom: Participate in interactive virtual classes from the convenience of your workspace. Getting Started Guides: Comprehensive guides to assist you in navigating the fundamentals of Vectorworks. In-Person Training Opportunities Customized On-Site Sessions: Hands-on training delivered directly to your office or at regional events. One-to-One: Engage in interactive learning at our training locations. Download Vectorworks https://www.vectorworks.net Personalized One-on-One Training: Get individualized attention and customized instruction. Flexible Scheduling: Choose your preferred training time and day to suit your schedule. Post-Course Assistance: Access free online support after course completion. Comprehensive Learning Materials: Receive PDF notes and handouts to enhance your learning. Certificate of Completion: Earn a recognition certificate upon successfully finishing the course. Affordable Rates: Enjoy cost-effective training rates. Software Setup Assistance: Receive help setting up the software on your computer. Referral Benefits: Recommend a friend and receive discounts on future courses. Group Training Discounts: Special discounts available for group training sessions. Convenient Availability: Access training sessions from Monday to Sunday, with extended hours. Tailored Training: Receive customized, bespoke training tailored to your specific requirements.
AUTOCAD Training for Both MAC and PC Users
By Real Animation Works
Face to Face Training Customised and Bespoke.

RUM120 - Real User Monitor 9.x Essentials Workshop
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for New users of Real User Monitor (RUM) 9.1, including: Database Administrators System Administrators Network Administrators Operations Managers Availability Engineers Overview At the end of the course, you should be able to: Describe the architecture of a RUM implementation Install and configure the RUM Windows Probe Install and configure the RUM Engine Configure RUM monitoring of a three-tier application (web, application, and database server) from BSM Explain RUM reporting data Size and tune RUM Configure RUM monitoring for secure web applications that use SSL Java Key Store (JKS) Troubleshoot RUM issues using the RUM logs This course is designed for users who have working experience with Business Service Management (BSM). This course is designed for users who have working experience with Business Service Management (BSM).

EC-Council Certified Security Specialist (ECSS)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for ECSS is designed for anyone who wants to enhance their skills and make a career in information security, network security, and computer forensics fields. It can be IT Specialists, Network Administrators, or System Administrators. Overview Upon successful completion of this course, students will learn: Key issues plaguing the information security, network security, and computer forensics. Fundamentals of networks and various components of the OSI and TCP/IP model. Various network security protocols. Various types of information security threats and attacks, and their countermeasures. Social engineering techniques, identify theft, and social engineering countermeasures. Different stages of the hacking cycle Identification, authentication, and authorization concepts Different types of cryptography ciphers, Public Key Infrastructure (PKI), cryptography attacks, and cryptanalysis tools. Fundamentals of firewall, techniques for bypassing firewall, and firewall technologies such as Bastion Host, DMZ, Proxy Servers, Network Address Translation, Virtual Private Network, and Honeypot. Fundamentals of IDS and IDS evasion techniques. Data backup techniques and VPN security. Wireless Encryption, wireless threats, wireless hacking tools, and Wi-Fi security. Different types of web server and web application attacks, and countermeasures. Fundamentals of ethical hacking and pen testing. Incident handling and response process. Cyber-crime and computer forensics investigation methodology. Different types of digital evidence and digital evidence examination process. Different type of file systems and their comparison (based on limit and features). Gathering volatile and non-volatile information from Windows and network forensics analysis mechanism. Steganography and its techniques. Different types of log capturing, time synchronization, and log capturing tools. E-mails tracking and e-mail crimes investigation. Writing investigation report. This is an entry-level security program covering the fundamental concepts and giving a holistic overview of the key components of information security, computer forensics, and network security. Course Outline Information Security Fundamentals Networking Fundamentals Secure Network Protocols Information Security Threats and Attacks Social Engineering Hacking Cycle Identification, Authentication, and Authorization Cryptography Firewalls Intrusion Detection System Data Backup Virtual Private Network Wireless Network Security Web Security Ethical Hacking and Pen Testing Incident Response Computer Forensics Fundamentals Digital Evidence Understanding File Systems Windows Forensics Network Forensics and Investigating Network Traffic Steganography Analyzing Logs E-mail Crime and Computer Forensics Writing Investigative Report Additional course details: Nexus Humans EC-Council Certified Security Specialist (ECSS) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the EC-Council Certified Security Specialist (ECSS) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

20703-1 Administering System Center Configuration Manager
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is for experienced information technology (IT) professionals, typically described as Enterprise Desktop Administrators (EDAs). These EDAs deploy, manage, and maintain PCs, devices, and applications across medium, large, and enterprise organizations. A significant portion of this audience uses, or intends to use, the latest release of Configuration Manager to manage and deploy PCs, devices, and applications. Overview After completing this course, students will be able to: •Analyze data by using queries and reports. •Prepare a management infrastructure, including configuring boundaries, boundary groups, and resource discovery, and integrating mobile-device management with Microsoft Exchange Server. •Deploy and manage the Configuration Manager client. •Configure, manage, and monitor hardware and software inventory, and use Asset Intelligence and software metering. •Identify and configure the most appropriate method to distribute and manage content used for deployments. •Distribute, deploy, and monitor applications for managed users and systems. •Maintain software updates for PCs that Configuration Manager manages. •Implement Endpoint Protection for managed PCs. •Manage configuration items, baselines, and profiles to assess and configure compliance settings and data access for users and devices. •Configure an operating-system deployment strategy by using Configuration Manager. •Manage and maintain a Configuration Manager site. In this course, students will learn day-to-day management tasks, including how to manage applications, client health, hardware and software inventory, operating system deployment, and software updates by using Configuration Manager. You also will learn how to optimize System Center Endpoint Protection, manage compliance, and create management queries and reports. Managing computers and mobile devices in the enterprise Overview of systems management by using enterprise management solutions Overview of the Configuration Manager architecture Overview of the Configuration Manager administrative tools Tools for monitoring and troubleshooting a Configuration Manager site Lab : Exploring the Configuration Manager tools Analyzing data using queries, reports, and CMPivot Introduction to queries Configuring SQL Server Reporting Services Analyzing the real-time state of a device by using CMPivot Lab : Creating and running queries Lab : Configuring SSRS Lab : Analyzing the real-time state of a device by using CMPivot Preparing the Configuration Manager management infrastructure Configuring site boundaries and boundary groups Configuring resource discovery Organizing resources using device and user collections Lab : Configuring boundaries and resource discovery Lab: Configuring user and device collections Deploying and managing the Configuration Manager client Overview of the Configuration Manager client Deploying the Configuration Manager client Configuring and monitoring client status Managing client settings and performing management operations Lab : Deploying the Microsoft System Center Configuration Manager client software Lab: Configuring and monitoring client status Lab : Managing client settings Managing inventory for PCs and applications Overview of inventory collection Configuring hardware and software inventory Managing inventory collection Configuring software metering Configuring and managing Asset Intelligence Lab : Configuring and managing inventory collection Lab : Configuring software metering Lab : Configuring and managing Asset Intelligence Distributing and managing content used for deployments Preparing the infrastructure for content management Distributing and managing content on distribution points Lab : Distributing and managing content for deployments Deploying and managing applications Overview of application management Creating applications Deploying applications Managing applications Deploying virtual applications by using System Center Configuration Manager (Optional) Deploying and managing Windows Store apps Lab : Creating and deploying applications Lab : Managing application supersedence and removal Lab : Deploying virtual applications by using Configuration Manager (Optional) Lab : Using Configuration Manager to deploy Windows Store apps Maintaining software updates for managed PCs The software updates process Preparing a Configuration Manager site for software updates Managing software updates Configuring automatic deployment rules Monitoring and troubleshooting software updates Enabling third-party updates Lab : Configuring the site for software updates Lab : Deploying and managing software updates Implementing Endpoint Protection for managed PCs Overview of Endpoint Protection in Configuration Manager Configuring, deploying, and monitoring Endpoint Protection policies Configuring and deploying advanced threat policies Lab : Implementing Microsoft System Center Endpoint Protection Lab : Implementing advanced threat policies Managing compliance and secure data access Overview of Compliance Settings Configuring compliance settings Viewing compliance results Managing resource and data access Lab : Managing compliance settings Managing operating system deployment An overview of operating system deployment Preparing a site for operating system deployment Deploying an operating system Managing Windows as a service Lab : Preparing the site for operating -system deployment Lab : Deploying operating -system images for bare-metal installations Managing and maintaining a Configuration Manager site Configuring role-based administration Configuring Remote Tools Overview of Configuration Manager site maintenance Backing up and recovering a Configuration Manager site Lab : Configuring role-based administration Lab : Configuring Remote Tools Lab : Maintaining a Configuration Manager site Additional course details: Nexus Humans 20703-1 Administering System Center Configuration Manager training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the 20703-1 Administering System Center Configuration Manager course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Oracle 12c Administration I
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is for all Oracle Professionals. Specifically Database Administrators, Web Server Administrators, System Administrators, CIOs and other IT Management Professionals. Overview Upon successful completion of this course, students will be able to understand configuration for installation, configuration of a host system, using Oracle Restart framework, troubleshooting tips, how the database fits with other systems, internals of the database, database failures and other topics. In this course, students will focus on configuration on supported systems. Also how the database fits in with other systems. Oracle Database Architercture Overview The Database Instance Database Memory Structures Database Process Structures Database Storage Architecture Oracle Clusterware Configuring the Host for Standalone Installlation Host Configuration Overview Choosing a Database Host Choosing an Operating System Proprietary Unix vs Open-Source Linux Making the OS Selection Prepare an Oracle LINUX Installation Perform Oracle LINUX Installation Configure the LINUX Host Step 1 - Confirm General System Requirements Step 2 - Confirm The Operating System Platform Step 3 - Confirm LINUX Package Requirements Step 4 - Confirm Network Configuration Configure Host for Virtualization VM Technologies Configure Oracle Linux for Virtualization Step 1 - Download Linux Updates Step 2 - Check Linux Kernel Step 3 - Download Latest yum Configuration File Step 4 - Enable Oracle Linux Add-ons Step 5 - Install VirtualBox Oracle Optimal Flexible Architecture OFA Goals ORACLE_BASE ORACLE_HOME Database Files Multiple ORACLE_HOMEs Databse Software Upgrades Mutliple Oracle Software Installations GRID Infrastructure Configuration Configure the Linux Installation About ASM Devices Configure Linux Devices for ASM Partioning a Device Oracle ASMLib Configue MS Windows Devices GRID Infrastructure Installation Perform the Installation Download Unpack the Installation Package Launch the Installation Session The Installation Dialog Verify the Installation Operating System Confirmation Oracle Utilities Setup SQL*Plus Confirmation Using EM Cloud Control Troubleshooting Problems DATABASE Installation Configuraion Configure a Linux Installation System Groups & Users Configure Kernel Parameters Create the Physical Directories Configure MS Windows Installation Prerequisite Checks & Fixup Utility DATABASE Installation ABOUT THE INSTALLATION The Installation Tools About The Installation Dialog The Installation Session Log PERFORM INSTALLATION ON LINUX Download Unpack The Installation Files Set Environment Variables Launch The Installation SERVER CLASS INSTALLATION DIALOG More About The Global Database Name About Enterprise Manager Cloud Control Secure The New Database PERFORM INSTALLATION ON WINDOWS Launch The Installation POST---INSTALLATION CONFIGURATION Required Environment Variables Defining The Environment Variables About SSH VERIFY THE INSTALLATION SQL*PlusConfirmation Operating System Confirmation Firewall Configuration Accessing EM Database Express Creating Databses Using DBCA About DBCA DBCA Templates Are You Sure? DEFAULT CONFIGURATION DATABASE ADVANCED MODE DATABASE File Location Variables Database Vault and Label Security CONFIGURE AN EXISTING DATABASE DELETE A DATABASE MANAGE TEMPLATES MANUALLY CREATE A DATABASE The CREATE DATABASE Command Using Oracle Restart WHAT IS ORACLE RESTART? What Oracle Restart Does Is Oracle Restart Deprecated? Registering With Oracle Restart More About srvctl Terminal Session Configuration COMPONENT STATUS USING SRVCTL Database Status Grid Infrastructure Status Oracle Home Status CONFIGURATION USING SRVCTL Examining A Database Configuration Examining The Listener Configuration Examining The ASM Configuration Manual Registration ListenerConfiguration Modification Database ConfigurationModification STARTUP/SHUTDOWN USING SRVCTL Why Use srvctl? MANAGING ORACLE RESTART Obtaining Oracle Restart Status Start/Stop Oracle Restart Preparing for a Database Upgrade What is a Database Upgrade? Database Upgrade Methods Real World Database Upgrade Develop A Database Upgrade Plan ABOUT THE DATABASE VERSION Direct Upgrade The COMPATIBLE Database Parameter PRE-UPGRADE PREPARATIONS Oracle Warehouse Builder Oracle Label Security (OLS) Oracle Database Vault Locating The Older Database Installations THE PRE-UPGRADE INFORMATION TOOL Pre-Upgrade Information Tool Files Run The Pre---Upgrade Information Tool Examining The Pre---Upgrade Information Tool Results Upgrade to Oracle Databse 12c Launch DBUA Database Upgrade Dialog Post-Upgrade Tasks Post-Upgrade Checklist Enable Unified Auditing Migrate to Unified Auditing Database Parameter Changes Enable New Features Source Destination Specific Post-Upgrade Tasks Oracle Architecture: The Systems Infrastructure About Enterprise Architectures The Relational Database Legacy Computing Models The Multi-Tiered Computing Model Scaling Up Cloud-Based Deployment ORACLE INFRASTRUCTURE ECOSYSTEM USING ORACLE ENTERPRISE MANAGER More About EM Using EM Database Express Using EM Cloud Control Oracle Architecture: The Database Host The Database Server Stack PROCESSOR LAYER CPU Resources Memory Resources I/O & STORAGE PROCESSING OS LAYER PROCESSING MODES DATABASE SERVER VIRTUALIZATION STORAGE VIRTUALIZATION ORACLE DATABASE SERVER STACK ORACLE ENGINEERED SYSTEMS Oracle Exadata Database Platform Exalogic Cloud Machine Exalytics BI Machine Oracle Architecture: Princilples & Technology Concepts Grid Computing Principles Why Grid Computing? What Is Grid Computing? PARALLELIZATION PRINCIPLES Hardware Parallelization Grid Computing Devices Clustered Database Servers CLOUD COMPUTING PRINCIPLES Multi-Tenancy Oracle Architecture: The RDBMS Installation & the Database Instance The Database Server Software Database Versions & Releases Database Editions Using PRODUCT_COMPONENT_VERSION View The Core Database Components Using V$VERSION View Understanding The Database Version Number The COMPATIBLE Database Parameter DATABASE INSTANCE ELEMENTS Individual Elements Of A Database Instance Physical Database Elements An Operational Database installation DATABASE INSTANCE CONFIGURATIONS Single Instance Parameter Files & Instance Configuration MAX_STRING_SIZE Parameter Example Independent Instances Clustered Instances The Database Instance In A Multi-tenant Configuration RECONFIGURING A DATABASE INSTANCE Static Vs. Dynamic Parameters Dynamic Parameter Setting Parameter Setting Scope Parameter Setting Level Setting Upgrade Related Parameters DATABASE COMPONENTS Advanced Data Functionality Components Security Components High-Performance Components Administration Components Database F

Introduction to Linux Systems Administration (TTLX2220)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This is an introductory-level systems administration course geared for Systems Administrators and users who wish to learn how to how to install, configure and maintain an Enterprise Linux system in a networked environment. Overview This course is about 50% lab to lecture ratio, combining expert instructor-led discussions with practical hands-on skills that emphasize current techniques, best practices and standards. Working in this hands-on lab environment, guided by our expert practitioner, attendees will explore Installing the Linux operating system and configuring peripherals Performing and modifying startup and shutdown processes Configuring and maintaining basic networking services Creating and maintaining system users and groups Understanding and administering file permissions on directories and regular files Planning and creating disk partitions and file systems Performing maintenance on file systems Identifying and managing Linux processes Automating tasks with cron Performing backups and restoration of files Working with system log files Troubleshooting system problems Analyzing and taking measures to increase system performance Configuring file sharing with NFS Configuring Samba for file sharing with the Windows clients Setting up a basic Web server Understanding the components for setting up a LAMP server Implementing basic security measures Linux System Administration is a comprehensive hands-on course that teaches students how to install, configure and maintain an Enterprise Linux system in a networked environment. This lab-intensive class explores core administrative tasks such as: creating and managing users, creating and maintaining file systems, determining and implementing security measures and performing software installation and package management. Linux networking topics include installing and supporting SSH, NFS, Samba and the Apache Web server. Students will explore common security issues, as well as several tools, such as the PAM modules that help secure the operating system and network environment. Upon successful completion of this course, students will be prepared to maintain Linux systems in a networked business environment. Although the course includes installing and configuring a CentOS 7 / RHEL 7 Linux system, much of the course content also applies to Oracle, Ubuntu, Scientific and other current versions of mainstream Linux distributions. Labs include user and group maintenance, system backups and restoration, software management, administration tasks automation, file system creation and maintenance, managing remote access, working with cron, and configuring basic file sharing and Web services, as well as working with system logging utilities such as rsyslog and much more. System Administration Overview UNIX, Linux and Open Source Duties of the System Administrator Superusers and the Root Login Sharing Superuser Privileges with Others (su and sudo Commands) TCP/IP Networking Fundamentals Online Help Installation and Configuration Planning: Hardware and Software Considerations Site Planning Installation Methods and Types Installation Classes Partitions Logical Volume Manager - LVM File System Overview Swap Partition Considerations Other Partition Considerations The Linux Boot Loader: grub Software Package Selection Adding and Configuring Peripherals Printers Graphics Controllers Basic Networking Configuration Booting to Recovery Mode Booting and Shutting Down Linux Boot Sequence The systemd Daemon The systemctl Command Targets vs. Run Levels Modifying a Target Service Unit Scripts Changing System States Booting into Rescue Mode Shutdown Commands Managing Software and Devices Identifying Software Packages Using rpm to Manage Software Using yum to Manage Software Installing and Removing Software Identifying Devices Displaying Device and System Information (PCI, USB) Plug and Play Devices Device Configuration Tools Managing Users and Groups Setting Policies User File Management The /etc/passwd file The /etc/shadow file The /etc/group file The /etc/gshadow file Adding Users Modifying User Accounts Deleting User Accounts Working with Groups Setting User Environments Login Configuration Files The Linux File System Filesystem Types Conventional Directory Structure Mounting a File System The /etc/fstab File Special Files (Device Files) Inodes Hard File Links Soft File Links Creating New File Systems with mkfs The lost+found Directory Repairing File Systems with fsck The Journaling Attribute File and Disk Management Tools Linux File Security File Permissions Directory Permissions Octal Representation Changing Permissions Setting Default Permissions Access Control Lists (ACLs) The getfacl and setfacl commands SUID Bit SGID Bit The Sticky Bit Controlling Processes Characteristics of Processes Parent-Child Relationship Examining Running Processes Background Processes Controlling Processes Signaling Processes Killing Processes Automating Processes cron and crontab at and batch System Processes (Daemons) Working with the Linux Kernel Linux Kernel Components Types of Kernels Kernel Configuration Options Recompiling the Kernel Shell Scripting Overview Shell Script Fundamentals Bash Shell Syntax Overview Shell Script Examples System Backups Backup Concepts and Strategies User Backups with the tar Command System Backup Options The xfsdump and xfsrestore Commands Troubleshooting the System Common Problems and Symptoms Troubleshooting Steps Repairing General Boot Problems Repairing the GRUB 2 Boot Loader Hard Drive Problems Restoring Shared Libraries System Logs and rsyslogd Basic Networking Networking Services Overview NetworkManager Introduction Network Configuration Files Locations and Formats Enabling and Restarting Network Services with systemtcl Configuring Basic Networking Manually Configuring Basic Networking with NetworkManager LAMP Server Basics LAMP Overview Configuring the Apache Web Server Common Directives Apache Virtual Hosting Configuring an Open Source Database MySQL MariaDB PHP Basics Perl CGI Scripting Introduction to System Security Security Overview Maintaining System Security Server Access Physical Security Network Security Security Tools Port Probing with nmap Intrusion Detection and Prevention PAM Security Modules Scanning the System Maintaining File Integrity Using Firewalls Introduction to firewalld The Samba File Sharing Facility Configure Samba for Linux to Linux/UNIX File Sharing Configure Samba for Linux to Windows File Sharing Use the smbclient Utility to Transfer Files Mount/Connect Samba Shares to Linux and Windows Clients Networked File Systems (NFS) Using NFS to Access Remote File Systems Configuring the NFS Server Configuring the NFS Client Exporting File Systems from the NFS Server to the NFS Client

CE121 IBM DB2 SQL Workshop
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for This basic course is for everyone needing to write, support, or understand SQL queries. This includes but is not limited to end-users, programmers, application designers, database administrators, and system administrators who do not yet have knowledge of Overview Code SQL statements to retrieve data from a DB2 or Informix table, including the SELECT, FROM, WHERE, GROUP BY, HAVING and ORDER BY clauses Code inner joins and non-correlated subqueries Use SQL arithmetic operations Use scalar and column functions Use UNION and UNION ALL INSERT, UPDATE and DELETE rows Code simple CREATE TABLE and CREATE VIEW statements This course is appropriate for customers working in all DB2 environments, that is, z/OS, VM/VSE, iSeries, Linux, UNIX, and Windows. It is also appropriate for customers working in an Informix environment. Outline Introduction Simple SQL Queries Retrieving Data from Multiple Tables Scalar Functions and Arithmetic Column Functions and Grouping UNION and UNION ALL Using Subqueries Maintaining data
