- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
163 Technology courses in Liverpool
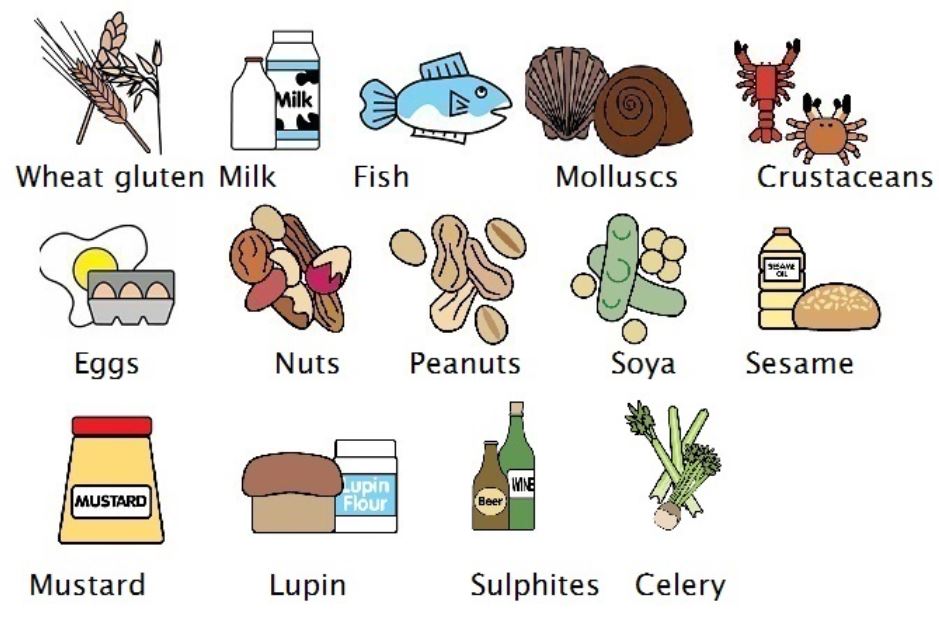
RSPH level 2 Identifying and Controlling Food Allergy Risks Training Course
By Kitchen Tonic Training Company and Food Safety Consultants
RSPH level 2 Identifying and Controlling Food Allergy Risks Training Course Do you need an allergy trainer to come to your food business and teach your staff face to face about food and drink allergens, their dangers and how to control them? Our allergy trainer can come to your business and deliver this course at your business premises. Although we are based in London, we are happy to travel and deliver this course at your business location. (Trainer travel fees may be applicable depending on your location). Staff will receive interactive training and coaching on allergens and intolerances with an experienced trainer. We can also tweak the training to include issues you would like to cover. See our website for more details. Special offer for on-site allergy training. £250 plus £20pp includes RSPH exam fees (usually £350 plus £30pp) This course is suitable for any catering business such as restaurants, pubs, hotels, cafes, catering companies, cooks, self employed, artisans, event caterers and more. This course is also important for staff who are Front of House, who take customer orders and relay the orders to cooks and chefs and other people who are preparing food for customers who have allergies and or intolerances. This is a short one day training course, typically 9am-3pm. Topics covered include- Allergens, Allergen Identification, Cross contact, Cross Contamination, Allergic Reactions, Food Intolerances, Coeliac, Anaphylaxis, Natasha's Law, UK Food Safety Regulations, Allergy Controls, Substituting ingredients, Customer Communication and what to do in an Emergency. Contact us to book training.
Overview Understand the role of corporate structure, dividends and equity indices in equity markets. Become familiar with the building blocks of repos / stock lending, futures and forwards – and how to use these products. Understand how to price, and risk manage equity swaps and dividend swaps. Gain experience in their uses in trading, corporate finance and portfolio management. Learn how to price equity options and the features that make them different from other asset classes, explore how to use these products for taking equity risk, yield enhancement and portfolio protection. Understand strategies designed to trade / hedge volatility using options. Who the course is for Risk management Finance Sales and trading Treasury Technology Financial Engineering Course Content To learn more about the day by day course content please click here To learn more about schedule, pricing & delivery options, book a meeting with a course specialist now
Stress Management and Preventing Burnout in a 24/7 World
By Elite Forums UK
Course Duration: Half-day or full-day program (with options for virtual delivery) Target Audience: Professionals, managers, leaders, and HR teams looking to build resilience, manage stress effectively, and prevent burnout in today’s always-on, high-pressure work environment. Course Objectives By the end of this course, participants will be able to: Recognise the signs and symptoms of stress and burnout. Understand the impact of chronic stress on health, performance, and well-being. Learn effective strategies for stress management and emotional regulation. Identify personal and workplace practices that reduce the risk of burnout. Develop a personal action plan for building resilience and maintaining well-being. Course Outline Module 1: Understanding Stress and Burnout What is stress? Types of stress (acute, chronic, eustress, distress) Defining burnout: symptoms, causes, and long-term effects The impact of a 24/7 world on mental health and performance How stress and burnout affect physical health, cognition, and relationships The role of work culture, technology, and societal expectations in stress Module 2: The Physiology of Stress and Burnout Understanding the body's stress response: fight or flight, cortisol, and adrenaline The effects of prolonged stress on the nervous system and health How burnout manifests in the brain and body The difference between stress and burnout: a deeper dive into emotional exhaustion, depersonalisation, and reduced personal accomplishment Module 3: Identifying Personal Stress Triggers and Early Warning Signs Conducting a stress audit: when and where does stress show up? Personal stress triggers: how work, environment, and relationships contribute Warning signs of burnout: physical, emotional, and behavioural red flags Self-assessment: Are you at risk of burnout? Understanding your personal stress responses and coping mechanisms Module 4: Effective Stress Management Techniques Mindfulness and relaxation practices: breathing exercises, meditation, and guided imagery Cognitive reframing: challenging negative thoughts and building resilience Time management and prioritisation: setting boundaries, saying no, and avoiding overwhelm Progressive muscle relaxation: tension release for mind and body Movement and exercise: how physical activity reduces stress Sleep hygiene: strategies for better rest and recovery Module 5: Building Resilience and Preventing Burnout The concept of resilience: bouncing back and growing stronger from adversity Strategies for emotional regulation: staying calm under pressure The role of social support: leaning on peers, mentors, and family Building psychological flexibility: accepting what we can’t change and focusing on what we can Creating work-life boundaries in a 24/7 world: disconnecting from work and technology Cultivating gratitude, positive psychology, and self-compassion in daily life Module 6: Creating a Sustainable Work Culture How leaders can foster a culture of well-being and prevent burnout Encouraging breaks, time off, and restorative work habits Organisational practices that support mental health: workload management, flexibility, and support resources Role of HR and leadership in promoting a healthy work-life balance The importance of feedback, recognition, and regular check-ins to prevent stress escalation Module 7: Personal Action Plan for Stress Management and Burnout Prevention Reflecting on key learnings and takeaways Developing a personal stress management toolkit Building a balanced daily routine that integrates self-care practices Creating a self-care action plan for the next 30 days Accountability partners and follow-up strategies to track progress Final thoughts: Small changes for big impact Delivery Style Interactive and experiential with a mix of individual reflection, small group discussions, and practical exercises Case studies and real-life examples to illustrate stress management strategies Guided relaxation techniques and mindfulness practices Personal assessments and action planning for immediate application Course Materials Provided Stress Management Handbook Personal Stress Audit Worksheet Relaxation and Breathing Exercise Guide Resilience Building Tools and Templates Self-Care Action Plan Template Resource list: Apps, podcasts, and books for stress management Optional Add-ons One-on-one coaching or follow-up sessions to discuss personal stress management strategies Leadership or team coaching to create a stress-resilient culture A series of wellness webinars focused on specific stress-management tools (e.g., sleep hygiene, mindfulness, movement, etc.) Ongoing email support or resource sharing to reinforce learning

Stress Management and Preventing Burnout in a 24/7 World
By Elite Forums Events
Course Duration: Half-day or full-day program (with options for virtual delivery) Target Audience: Professionals, managers, leaders, and HR teams looking to build resilience, manage stress effectively, and prevent burnout in today’s always-on, high-pressure work environment. Course Objectives By the end of this course, participants will be able to: Recognise the signs and symptoms of stress and burnout. Understand the impact of chronic stress on health, performance, and well-being. Learn effective strategies for stress management and emotional regulation. Identify personal and workplace practices that reduce the risk of burnout. Develop a personal action plan for building resilience and maintaining well-being. Course Outline Module 1: Understanding Stress and Burnout What is stress? Types of stress (acute, chronic, eustress, distress) Defining burnout: symptoms, causes, and long-term effects The impact of a 24/7 world on mental health and performance How stress and burnout affect physical health, cognition, and relationships The role of work culture, technology, and societal expectations in stress Module 2: The Physiology of Stress and Burnout Understanding the body's stress response: fight or flight, cortisol, and adrenaline The effects of prolonged stress on the nervous system and health How burnout manifests in the brain and body The difference between stress and burnout: a deeper dive into emotional exhaustion, depersonalisation, and reduced personal accomplishment Module 3: Identifying Personal Stress Triggers and Early Warning Signs Conducting a stress audit: when and where does stress show up? Personal stress triggers: how work, environment, and relationships contribute Warning signs of burnout: physical, emotional, and behavioural red flags Self-assessment: Are you at risk of burnout? Understanding your personal stress responses and coping mechanisms Module 4: Effective Stress Management Techniques Mindfulness and relaxation practices: breathing exercises, meditation, and guided imagery Cognitive reframing: challenging negative thoughts and building resilience Time management and prioritisation: setting boundaries, saying no, and avoiding overwhelm Progressive muscle relaxation: tension release for mind and body Movement and exercise: how physical activity reduces stress Sleep hygiene: strategies for better rest and recovery Module 5: Building Resilience and Preventing Burnout The concept of resilience: bouncing back and growing stronger from adversity Strategies for emotional regulation: staying calm under pressure The role of social support: leaning on peers, mentors, and family Building psychological flexibility: accepting what we can’t change and focusing on what we can Creating work-life boundaries in a 24/7 world: disconnecting from work and technology Cultivating gratitude, positive psychology, and self-compassion in daily life Module 6: Creating a Sustainable Work Culture How leaders can foster a culture of well-being and prevent burnout Encouraging breaks, time off, and restorative work habits Organisational practices that support mental health: workload management, flexibility, and support resources Role of HR and leadership in promoting a healthy work-life balance The importance of feedback, recognition, and regular check-ins to prevent stress escalation Module 7: Personal Action Plan for Stress Management and Burnout Prevention Reflecting on key learnings and takeaways Developing a personal stress management toolkit Building a balanced daily routine that integrates self-care practices Creating a self-care action plan for the next 30 days Accountability partners and follow-up strategies to track progress Final thoughts: Small changes for big impact Delivery Style Interactive and experiential with a mix of individual reflection, small group discussions, and practical exercises Case studies and real-life examples to illustrate stress management strategies Guided relaxation techniques and mindfulness practices Personal assessments and action planning for immediate application Course Materials Provided Stress Management Handbook Personal Stress Audit Worksheet Relaxation and Breathing Exercise Guide Resilience Building Tools and Templates Self-Care Action Plan Template Resource list: Apps, podcasts, and books for stress management Optional Add-ons One-on-one coaching or follow-up sessions to discuss personal stress management strategies Leadership or team coaching to create a stress-resilient culture A series of wellness webinars focused on specific stress-management tools (e.g., sleep hygiene, mindfulness, movement, etc.) Ongoing email support or resource sharing to reinforce learning

Tackling Financial Corruption
By Global Risk Alliance Ltd
This course will provide delegates involved in tackling the financial underpinning of corrupt behaviour with the knowledge, concepts and practices necessary to understand and mitigate illicit financial flows.

Train the Trainer
By Elite Forums UK
Course Duration: 2 days (or modular format over 3–4 half-day sessions) Target Audience: New or aspiring trainers, facilitators, team leads, or subject-matter experts who deliver training or knowledge-sharing sessions. Course Objectives By the end of this course, participants will be able to: Understand the principles of adult learning and training design. Confidently plan and structure engaging training sessions. Deliver content clearly using effective facilitation techniques. Manage group dynamics and encourage learner participation. Evaluate training effectiveness and improve performance. Course Outline Day 1: Designing Training for Adult Learners Module 1: Understanding the Trainer’s Role Role and responsibilities of an effective trainer Differences between training, presenting, and facilitating Characteristics of great trainers Module 2: Adult Learning Principles How adults learn: motivation, barriers, and learning preferences Learning styles and engagement strategies Applying adult learning theory to real training contexts Module 3: Training Needs Analysis Identifying learning needs and performance gaps Defining clear learning objectives Aligning training outcomes with organisational goals Module 4: Structuring a Training Session Designing training using ADDIE or the 4MAT model Creating session plans and timelines Balancing content delivery with interaction Day 2: Delivering and Evaluating Engaging Training Module 5: Facilitation Skills and Training Delivery Verbal and non-verbal communication Creating a safe and inclusive learning environment Encouraging participation and managing learner resistance Techniques for in-person and online delivery Module 6: Using Training Tools and Technology Using visuals and presentation aids effectively Incorporating activities, case studies, and role plays Facilitating discussions, group work, and Q&A Tips for hybrid and online delivery (Zoom, Teams, etc.) Module 7: Handling Group Dynamics and Challenges Managing difficult participants or situations Reading the room and adjusting on the fly Building confidence as a trainer Module 8: Evaluating Training Effectiveness Gathering and using learner feedback (Kirkpatrick Model) Self-reflection and peer observation Continual improvement of training materials and delivery Delivery Style Practical, hands-on workshops with active participation Peer feedback, group work, and presentation practice Real-time coaching and confidence building Assessment and Certification (Optional) Mini training delivery by each participant with peer and trainer feedback Completion of a training session plan Certificate of completion (customisable to organisation) Course Materials Provided Participant workbook and templates Sample training session plans and evaluation forms Trainer’s checklist and facilitation guide Resource list for further development

Train the Trainer
By Elite Forums Events
Course Duration: 2 days (or modular format over 3–4 half-day sessions) Target Audience: New or aspiring trainers, facilitators, team leads, or subject-matter experts who deliver training or knowledge-sharing sessions. Course Objectives By the end of this course, participants will be able to: Understand the principles of adult learning and training design. Confidently plan and structure engaging training sessions. Deliver content clearly using effective facilitation techniques. Manage group dynamics and encourage learner participation. Evaluate training effectiveness and improve performance. Course Outline Day 1: Designing Training for Adult Learners Module 1: Understanding the Trainer’s Role Role and responsibilities of an effective trainer Differences between training, presenting, and facilitating Characteristics of great trainers Module 2: Adult Learning Principles How adults learn: motivation, barriers, and learning preferences Learning styles and engagement strategies Applying adult learning theory to real training contexts Module 3: Training Needs Analysis Identifying learning needs and performance gaps Defining clear learning objectives Aligning training outcomes with organisational goals Module 4: Structuring a Training Session Designing training using ADDIE or the 4MAT model Creating session plans and timelines Balancing content delivery with interaction Day 2: Delivering and Evaluating Engaging Training Module 5: Facilitation Skills and Training Delivery Verbal and non-verbal communication Creating a safe and inclusive learning environment Encouraging participation and managing learner resistance Techniques for in-person and online delivery Module 6: Using Training Tools and Technology Using visuals and presentation aids effectively Incorporating activities, case studies, and role plays Facilitating discussions, group work, and Q&A Tips for hybrid and online delivery (Zoom, Teams, etc.) Module 7: Handling Group Dynamics and Challenges Managing difficult participants or situations Reading the room and adjusting on the fly Building confidence as a trainer Module 8: Evaluating Training Effectiveness Gathering and using learner feedback (Kirkpatrick Model) Self-reflection and peer observation Continual improvement of training materials and delivery Delivery Style Practical, hands-on workshops with active participation Peer feedback, group work, and presentation practice Real-time coaching and confidence building Assessment and Certification (Optional) Mini training delivery by each participant with peer and trainer feedback Completion of a training session plan Certificate of completion (customisable to organisation) Course Materials Provided Participant workbook and templates Sample training session plans and evaluation forms Trainer’s checklist and facilitation guide Resource list for further development

Work-Life Integration in the Age of Remote Everything
By Elite Forums UK
Course Duration: Half-day or full-day program (with virtual and in-person options) Target Audience: Professionals working remotely, hybrid teams, managers, HR leaders, and individuals looking to improve their work-life integration in today’s fast-paced, digital-first work environment. Course Objectives By the end of this course, participants will be able to: Understand the concept of work-life integration versus work-life balance. Recognise the challenges and benefits of working remotely or in hybrid settings. Learn practical strategies for managing boundaries, time, and energy. Cultivate habits that support both productivity and personal well-being. Apply tools to foster sustainable work-life integration in their teams and organisations. Course Outline Module 1: Rethinking Work-Life Integration The difference between work-life balance and work-life integration The challenges of work-life boundaries in a remote-first world The impact of technology on personal and professional lives Why flexibility matters: remote work as a tool for integration, not separation Module 2: Understanding Your Energy and Time Identifying personal energy patterns throughout the day Time audit: understanding how you currently allocate time and energy The role of breaks, boundaries, and rituals in energy management Tools for task prioritisation: Pomodoro, time blocking, and task batching Module 3: Managing Boundaries in a Digital World Setting and communicating clear boundaries for work and personal time Managing "always-on" culture in a remote environment Tools for setting expectations with colleagues and managers Creating a dedicated workspace and establishing personal rituals Saying no effectively: how to manage overcommitment and avoid burnout Module 4: Navigating Flexibility and Productivity The benefits and challenges of flexible working hours Time management strategies for remote and hybrid work settings Overcoming distractions: creating a productive work environment at home Staying focused and motivated without the physical office Managing work interruptions and creating space for personal time Module 5: Well-Being in Remote and Hybrid Work Importance of self-care and mental health in work-life integration Strategies for staying physically active, social, and mentally engaged remotely Building habits for sleep, mindfulness, and recovery Setting clear personal and professional goals to stay aligned with values Techniques for managing stress and avoiding burnout in a remote environment Module 6: Building a Remote-First Culture Leading with empathy: supporting remote teams’ well-being Fostering communication, trust, and accountability in hybrid teams Encouraging regular check-ins, feedback loops, and work-life check-ups Building a culture of flexibility and autonomy while maintaining performance Best practices for team collaboration and social connection in remote environments Module 7: Action Planning for Sustainable Integration Developing a personalised work-life integration plan Identifying areas of improvement: time, energy, boundaries, and well-being Setting achievable goals for short-term and long-term work-life integration Peer sharing: tips and strategies that have worked for you Building accountability structures: partners, progress tracking, and revisiting goals Delivery Style Highly interactive, with a mix of discussions, reflection exercises, and case studies Practical tools, tips, and templates that participants can apply immediately Group activities to share experiences and learn from peers Guided self-reflection and action planning for immediate impact Course Materials Provided Work-Life Integration Guide Time Audit Worksheet and Energy Mapping Tools Setting Boundaries Framework and Template Remote Work Well-Being Checklist Personal Action Plan for Sustainable Integration Resource list: Apps, podcasts, and books on work-life integration Optional Add-ons Post-course coaching or check-in sessions Customised team workshop focused on hybrid work challenges Leadership session on managing remote-first teams effectively Follow-up webinars on remote collaboration and staying connected

Work-Life Integration in the Age of Remote Everything
By Elite Forums Events
Course Duration: Half-day or full-day program (with virtual and in-person options) Target Audience: Professionals working remotely, hybrid teams, managers, HR leaders, and individuals looking to improve their work-life integration in today’s fast-paced, digital-first work environment. Course Objectives By the end of this course, participants will be able to: Understand the concept of work-life integration versus work-life balance. Recognise the challenges and benefits of working remotely or in hybrid settings. Learn practical strategies for managing boundaries, time, and energy. Cultivate habits that support both productivity and personal well-being. Apply tools to foster sustainable work-life integration in their teams and organisations. Course Outline Module 1: Rethinking Work-Life Integration The difference between work-life balance and work-life integration The challenges of work-life boundaries in a remote-first world The impact of technology on personal and professional lives Why flexibility matters: remote work as a tool for integration, not separation Module 2: Understanding Your Energy and Time Identifying personal energy patterns throughout the day Time audit: understanding how you currently allocate time and energy The role of breaks, boundaries, and rituals in energy management Tools for task prioritisation: Pomodoro, time blocking, and task batching Module 3: Managing Boundaries in a Digital World Setting and communicating clear boundaries for work and personal time Managing "always-on" culture in a remote environment Tools for setting expectations with colleagues and managers Creating a dedicated workspace and establishing personal rituals Saying no effectively: how to manage overcommitment and avoid burnout Module 4: Navigating Flexibility and Productivity The benefits and challenges of flexible working hours Time management strategies for remote and hybrid work settings Overcoming distractions: creating a productive work environment at home Staying focused and motivated without the physical office Managing work interruptions and creating space for personal time Module 5: Well-Being in Remote and Hybrid Work Importance of self-care and mental health in work-life integration Strategies for staying physically active, social, and mentally engaged remotely Building habits for sleep, mindfulness, and recovery Setting clear personal and professional goals to stay aligned with values Techniques for managing stress and avoiding burnout in a remote environment Module 6: Building a Remote-First Culture Leading with empathy: supporting remote teams’ well-being Fostering communication, trust, and accountability in hybrid teams Encouraging regular check-ins, feedback loops, and work-life check-ups Building a culture of flexibility and autonomy while maintaining performance Best practices for team collaboration and social connection in remote environments Module 7: Action Planning for Sustainable Integration Developing a personalised work-life integration plan Identifying areas of improvement: time, energy, boundaries, and well-being Setting achievable goals for short-term and long-term work-life integration Peer sharing: tips and strategies that have worked for you Building accountability structures: partners, progress tracking, and revisiting goals Delivery Style Highly interactive, with a mix of discussions, reflection exercises, and case studies Practical tools, tips, and templates that participants can apply immediately Group activities to share experiences and learn from peers Guided self-reflection and action planning for immediate impact Course Materials Provided Work-Life Integration Guide Time Audit Worksheet and Energy Mapping Tools Setting Boundaries Framework and Template Remote Work Well-Being Checklist Personal Action Plan for Sustainable Integration Resource list: Apps, podcasts, and books on work-life integration Optional Add-ons Post-course coaching or check-in sessions Customised team workshop focused on hybrid work challenges Leadership session on managing remote-first teams effectively Follow-up webinars on remote collaboration and staying connected

Food Hygiene Level 2
By Prima Cura Training
This is a full day session that will aim to provide a more in-depth understanding of Food Hygiene. It meets UK and EU legal requirements for food handlers & matches RSPH and CIEH level 2 syllabus

Search By Location
- Technology Courses in London
- Technology Courses in Birmingham
- Technology Courses in Glasgow
- Technology Courses in Liverpool
- Technology Courses in Bristol
- Technology Courses in Manchester
- Technology Courses in Sheffield
- Technology Courses in Leeds
- Technology Courses in Edinburgh
- Technology Courses in Leicester
- Technology Courses in Coventry
- Technology Courses in Bradford
- Technology Courses in Cardiff
- Technology Courses in Belfast
- Technology Courses in Nottingham