- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1229 Systems courses delivered Live Online
Software development training course description This three-day MTA Training course helps you prepare for Microsoft Technology Associate Exam 98-361, and build an understanding of these topics: Core programming, Object-Oriented programming, general software development, web applications, desktop applications, and databases. This course leverages the same content as found in the Microsoft Official Academic Course (MOAC) for this exam. What will you learn Describe core programming. Explain Object Oriented programming. Describe general software development. Describe Web applications. Describe desktop applications. Explain how databases work. Software development training course details Who will benefit: Anyone looking to learn the fundamentals of software. Prerequisites: None. Duration 3 days Software development training course contents Core programming Computer storage and data types How a computer stores programs and the instructions in computer memory, memory stacks and heaps, memory size requirements for the various data storage types, numeric data and textual data. Computer decision structures Various decision structures used in all computer programming languages; If decision structures; multiple decision structures, such as Ifâ¦Else and switch/Select Case; reading flowcharts; decision tables; evaluating expressions. Handling repetition For loops, While loops, Do...While loops and recursion. Understand error handling Structured exception handling. Object-oriented programming Classes Properties, methods, events and constructors; how to create a class; how to use classes in code. Inheritance Inheriting the functionality of a base class into a derived class. Polymorphism Extending the functionality in a class after inheriting from a base class, overriding methods in the derived class. Encapsulation Creating classes that hide their implementation details while still allowing access to the required functionality through the interface, access modifiers. General software development Application life cycle management Phases of application life cycle management, software testing. Interpret application specifications Application specifications, translating them into prototypes, code, select appropriate application type and components. Algorithms and data structures Arrays, stacks, queues, linked lists and sorting algorithms; performance implications of various data structures; choosing the right data structure. Web applications Web page development HTML, CSS, JavaScript. ASP.NET web application development Page life cycle, event model, state management, client-side versus server-side programming. Web hosting Creating virtual directories and websites, deploying web applications, understanding the role of Internet Information Services. Web services Web services that will be consumed by client applications, accessing web services from a client application, SOAP, WSDL. Desktop applications Windows apps UI design guideline categories, characteristics and capabilities of Store Apps, identify gestures. Console-based applications Characteristics and capabilities of console- based applications. Windows Services Characteristics and capabilities of Windows Services. Databases Relational database management systems Characteristics and capabilities of database products, database design, ERDs, normalisation concepts. Database query methods SQL, creating and accessing stored procedures, updating and selecting data. Database connection methods Connecting to various types of data stores, such as flat file; XML file; in-memory object; resource optimisation.

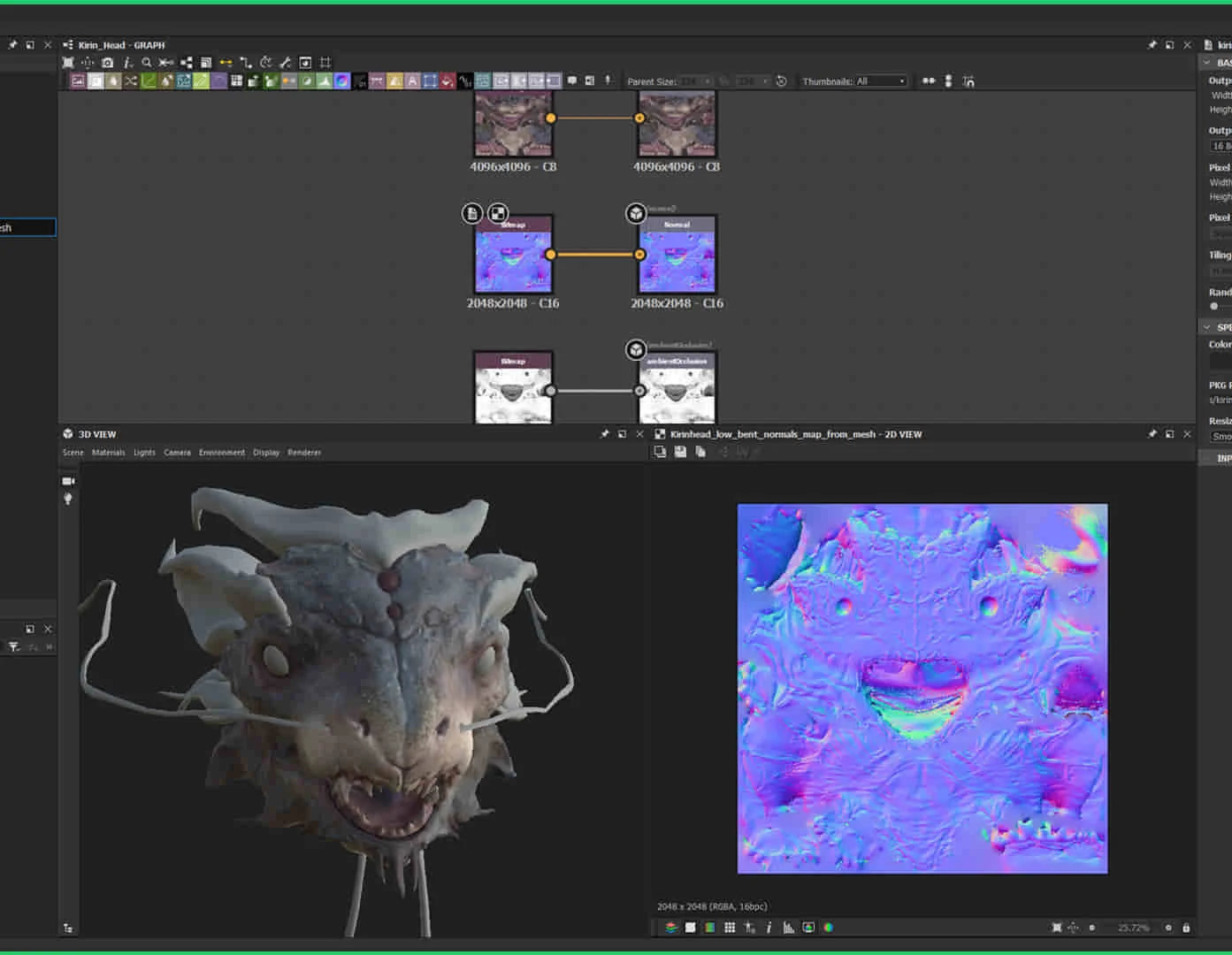
3ds Max and Unity 3D Game Designing Training Course
By ATL Autocad Training London
Who is this course for? The "3ds Max and Unity 3D Game Designing Training Course" is ideal for aspiring game designers, developers, graphic designers, students, and creative professionals. It's tailored for individuals keen on mastering 3D modeling, animation, and interactive game development using industry-standard software like 3ds Max and Unity 3D. Click here for more info: Website Scheduling: Available from Monday to Saturday, 9 a.m. to 7 p.m. Choose in-person or live online sessions over Zoom. Duration: 40 hours. Module 1: Introduction to 3ds Max (8 hours) Overview of 3ds Max interface and tools Basic 3D modeling techniques: primitives, Editable Poly, modifiers Material creation and application Introduction to lighting and rendering concepts Module 2: Advanced 3ds Max Techniques (8 hours) Advanced modeling: Splines, Loft, Extrude, and ProBoolean Animation basics: Keyframes, paths, and controllers Particle systems and dynamics Introduction to character rigging and animation Module 3: Introduction to Unity 3D (8 hours) Unity interface and project setup Importing 3D assets from 3ds Max Physics and colliders in Unity Basic scripting and interactions Module 4: Advanced Unity 3D Features (8 hours) Unity scripting: C# fundamentals Advanced physics and particle systems User interface design and implementation Integrating audio and visual effects Module 5: Game Design and Optimization (8 hours) Game design principles and mechanics Level design and interactive gameplay elements Optimizing game performance: LOD, batching, and asset optimization User testing and feedback incorporation Final Project (4 hours) Collaborative game development project using 3ds Max and Unity 3D Implementation of learned skills in a real-world scenario Presentation and feedback session Note: The course outline is designed to provide a comprehensive understanding of both 3ds Max and Unity 3D, covering fundamental and advanced topics. The final project aims to apply the acquired skills in a practical context, fostering creativity and collaboration among participants. Unity - Real-time 3D https://www.unity.com/. 3ds Max Trial https://www.autodesk.co.uk ⺠products ⺠free-trial Upon completion of the 40-hour 3ds Max and Unity 3D Game Design Masterclass, students will: Master 3D Modeling: Acquire proficient skills in creating detailed 3D models, understanding various techniques, and utilizing advanced tools in 3ds Max. Expertise in Animation: Gain expertise in animating characters and objects, employing keyframes, paths, and controllers for realistic motion. Material Creation and Texturing: Understand material creation, application, and advanced texturing techniques for creating visually appealing game assets. Unity Game Development: Learn Unity's interface, project setup, and scripting fundamentals to create interactive games. Physics and Interactivity: Explore physics systems, colliders, and interactive elements, enhancing gameplay experiences. Advanced Scripting: Develop proficiency in C# scripting, enabling the implementation of complex game mechanics and interactions. Optimization Techniques: Understand techniques to optimize game assets, improving performance and ensuring smooth gameplay. Game Design Principles: Grasp essential game design principles, including level design, user experience, and gameplay mechanics. Real-World Application: Apply learned skills in a collaborative final project, integrating 3D models, animations, scripting, and game design principles. Presentation Skills: Develop the ability to present and explain game concepts, designs, and mechanics effectively. Troubleshooting and Debugging: Gain skills in identifying and resolving common issues and errors in both 3ds Max and Unity 3D projects. Team Collaboration: Enhance teamwork and collaboration skills through the final project, working effectively with peers in a creative environment. Upon completing the course, students will have a well-rounded skill set in 3D modeling, animation, game design, and Unity development, making them proficient candidates for roles in game development studios, animation companies, or freelance projects. 3ds Max and Unity 3D Game Designing Training Course: Skills & Careers! Skills Acquired: Advanced 3D Modeling Texturing and Animation Unity 3D Game Development Lighting and Rendering Interactive UI/UX Design Career Opportunities: Game Developer 3D Modeler Texture Artist Game Tester UI/UX Designer Embrace Personalized Learning. Why Us? Discover the Benefits: One-on-One Training: Experience tailored coaching from practicing architects and designers, either face-to-face at (SW96DE) or in live online sessions. Available Monday to Saturday, 9 am to 7 pm. Customized Tutorials: Take home exclusive video tutorials crafted to enhance your learning journey. Comprehensive Resources: Access a digital reference book for thorough revision, ensuring a deep understanding of every concept. Free Ongoing Support: Enjoy continuous post-course assistance via phone or email, ensuring your success even after class completion. Flexible Syllabus: We adapt syllabus and projects to your needs, ensuring focused learning on what matters most to you. Official Certificate: Certificate upon course completion. Why Choose Us? Individualized Support: Our courses, ranging from 10 to 120 hours, offer unwavering assistance at every stage. With personalized homework assignments and free after-course support, we guide you toward mastering software with unparalleled expertise. Personal Attention, No Crowded Classrooms: Experience the intimacy of one-on-one learning. Bid farewell to crowded classrooms, ensuring you receive the undivided attention you deserve in a confident and comfortable environment. Financial Flexibility: Embarking on your educational journey shouldn't strain your finances. Diverse payment plans tailored to your needs. Explore available options and embark on your learning adventure today. Expert Instructors, Real-world Experience: Our instructors, chosen for their industry expertise and passion for teaching, are dedicated to imparting invaluable skills to eager learners.
Linux training course description A Linux foundation appropriate for all flavours of Linux, focussed on getting network engineers up and running with Linux. The command line is used throughout. The course progresses from the basics of Linux commands onto useful tools such as grep, then shell features such as piping and then onto shell scripting. Administration aspects covered are the tasks network engineers are most likely to encounter such as software installation. Hands on exercises concentrate on network related tasks such as installing net-snmp and using shell scripts to provide network automation. What will you learn Use Linux commands to perform a variety of tasks from manipulating files to handling processes. Create and edit files with vi. Work with permissions. Write simple shell scripts. Install software packages. Configure base networking. Linux training course details Who will benefit: Network engineers. Prerequisites: TCP/IP Foundation Duration 5 days Linux training course contents What is Linux? Linux distributions, open source software. Getting started Logging in, changing passwords, logging out. Hands on Basics and root access. Linux basics Command structure. The Linux manuals, basic commands (who, date, tty, uname, echo, banner...). Hands on Using the CLI. Connecting to a network IP configuration, DHCP, static addressing, routing, ifconfig, ping, netstat, traceroute, dig. Hands on Network configuration and testing. Managing Software Package Concepts, Comparison of package formats, RPM, rpm Commands, Yum, Debian Packages, dpkg, apt-cache, apt-get, dselect, aptitude, Converting Between Package Formats, Dependencies and Conflicts, Startup Script Problems, Shared Libraries, Library Management Hands on Installing network packages such as nmap and net-snmp. Processes and log files ps, kill, background processes, at, exec, priorities. Managing Linux log files. Syslogd. Setting the time. Cron and cronjobs. Managing Processes, the Kernel: The First Process. Hands on Controlling daemons and services. Setting up a TFTP server. Filesystem commands Home directories, manipulating files and directories, Filesystem layout, Pathnames, hard and symbolic links. Viewing files. Hands on Exploring the filesystem, working with network device configuration files. The Linux editors ed, vi, shell escapes, .exrc. Hands on Editing network device configuration files. Extracting data from files grep, find, cut, sort and paste⦠Hands on Working with syslog files. Permissions Theory, chmod, chown, newgrp. Hands on Handling permission problems. The shell Metacharacters, piping and redirection. Hands on Running SNMP commands and working with their output. Basic shell scripting What are shell scripts? Simple scripts, control structures. Variable. Setting variables, using variables, set, scope, export, sourcing, environmental variables, read. Positional parameters: $0 to $9, $#, $* and others. shift parameter substitution. Control statements: The test command, if , while loops, for loops, the case statement. Hands on Automating network tasks. Customising your environment Environmental variables, stty, .profile and other startup files. Hands on Customising Linux. Introduction to administration The root user, su. Managing users and groups. Hands on The power of root. Archiving files Backups, tar, cpio, dd, gzip. Hands on Working with tar files. Booting Linux and Editing Files Installing Boot Loaders, GRUB Legacy, GRUB 2, Alternative Boot Loaders, the Boot Process, Boot Messages, Runlevels and the Initialization Process, Runlevel Functions, Runlevel Services, Alternative Boot Systems , Upstart, system. Hands on Installing network services on Linux.

Classroom based, instructor led workshop with proctor at home exam. The lab-intensive Certified SOC Analyst (CSA) program emphasizes the holistic approach to deliver the advanced knowledge of how to identify, validate and defend against cyber-attacks.

Training Course for Architects & Interior Exterior Designers
By Real Animation Works
1-2-1 face to face training customised and bespoke.

MEF Carrier Ethernet training course description The course progresses from a overview of the Carrier Ethernet service and how it works onto looking at the concepts in depth. Service attributes and management follow with the course finishing with studies of practical Carrier Ethernet. What will you learn Discuss and understand key Carrier Ethernet Concepts. Understand tasks related to designing, deploying and maintaining a Carrier Ethernet network. Offer effective solutions to implementing a Carrier Ethernet enterprise network given available customer resources and requirements. Carry out informed discussions using industry Carrier Ethernet 'vocabulary. Pass the MEF CECP 2.0 professional accreditation exam. MEF Carrier Ethernet training course details Who will benefit: Anyone working with Carrier Ethernet Prerequisites: The course attendees need to be conversant with data networks, as well as Ethernet and IP technologies. Duration 5 days MEF Carrier Ethernet training course contents Section One: Introduction to Carrier Ethernet Introduction to Carrier Ethernet: What is Carrier Ethernet? Evolution, advantages, The MEF, MEF specifications; UNI, EVC, OVC, EPL/EVPL, EP-LAN/ EVP-LAN, EP-Tree/EVP-Tree, etc, overview. How Carrier Ethernet Works: Service Frame Handling. Carrier Ethernet at Customer Premises, metro and core. Carrier Ethernet Workings, UNI attributes, Service Attributes (EVC and EVC per UNI attributes), Bandwidth Profiles, service multiplexing, L2 protocol processing; Carrier Ethernet equipment, CPE, aggregation and homing nodes, core equipment; management systems. The Setting Up of a Carrier Ethernet Service: Step 1: Choose service type, EPL/EVPL, EP-LAN/EVP-LAN, EPTree/EVP-Tree, EVLine...; Step 2: CPE tasks, UNI-C tasks (UNI attributes, service attributes (EVC and EVC per UNI) and bandwidth profiles), UNI-N tasks (L2 protocol handling). Step 3: Non-CPE tasks, Access, metro and core connections set up. Section Two: Carrier Ethernet Concepts in depth Carrier Ethernet Definitions in Depth: UNI, UNI I & II, UNI-N and UNI-C, etc.; NNI/ENNI; EVC; OVC, OVC type (P2P, M2M, Rooted MP), OVC end point (root, leaf, trunk), OVC end point map, OVC end point bundling; Service types in detail, EPL/EVPL, EP-LAN/EVP-LAN, EP-Tree/EVP-Tree, EVLine, Access EPL, Access EVPL . Carrier Ethernet Service Frame Handling: Unicast, multicast and broadcast frame delivery, Tagged, untagged and priority; Tagging, C and S-Tags, 802.3, 802.1d, 802.1q, 802.1ad, 802.1ah evolution, VLAN ID translation/preservation. CoS preservation. Other Key Carrier Ethernet Concepts: MTU, MTU at UNI, MTU at ENNI; Physical Layer Attributes, FE, GbE and 10GbE, Service Multiplexing and Bundling Concept and detail, rules and implications; Hairpin Switching Managing Bandwidth in a Carrier Ethernet Network: Token Bucket Algorithm, EIR, CIR, CBS, EBS, Coupling Flag; Frame Colors, recoloring, Color Awareness attribute, Color Forwarding; Bandwidth Profiles, rules and concepts. MEF CoS identifiers, DEI bit (in S-Tag), PCP bit (in C-Tag or S-Tag), or DSCP (in IP header), Multiflow bandwidth concepts; CoS Label/Color Identification. Section Three: Carrier Ethernet Service Attributes Overview: Carrier Ethernet 2.0; Blueprint C Service Attributes: Per UNI, Physical interfaces, Frame format, Ingress/egress Bandwidth Profiles, CEVLAN ID/EVC Map, UNI protection. EVC per UNI, Ingress/egress Bandwidth Profiles, etc.; Per EVC, CEVLAN ID Preservation, CoS ID Preservation, Relationship between SLA and SLP, Class of Service, etc. OVC, ENNI, OVC End Point per UNI and OVC End Point per ENNI, Ingress/egress bandwidth profiles, etc. Section Four: Managing Carrier Ethernet Networks Overview: MEF Service Lifecycle.Carrier Ethernet maintenance: Port, Link & NE failure, Service Protection Technologies, Fault Identification and Recovery, LAG, Active/Standby EVC, Single EVC with transport protection, G.8031, G.8032, MPLS FRR. SOAMs: Connectivity fault management, connectivity Monitoring, Loopback, Linktrace; Performance Management, Frame Delay, Inter Frame Delay Variation, Availability, Frame Loss Ratio, Resiliency, HLI, DMM, DMR, SLM, SLR; Key Concepts, Single vs dual ended, ordered UNI pair calculations. LOAMs: Link discovery, link monitoring, etc. Terminology and Concepts: MEG levels, MIPs. Section Five: Practical Carrier Ethernet Carrier Ethernet Transport Technologies:Layer 1: SDH. Layer 2: Bridging, provider bridging, PBB, PBBTE. Layer 2.5: MPLS VPWS, MPLS VPLS, MPLS-TP. Carrier Ethernet Access Technologies: fiber, SDH, active fiber, PON, GPON, 10G PON, OTN, WDM; copper, PDH, G-SDSL, 10Pass-TS, HFC; packet radio. Optimising mobile backhaul with Carrier Ethernet Key challenges solutions: Market pressure, LTE evolution, elements and architecture (RAN BS, NC, GWIF.), synchronization, bandwidth management. Circuit Emulation over Ethernet: Purpose, needs and applications. Synchronization: Phased, ToD, External Reference source, SynchE ,NTP, IEEE-1588 v2/ PTP, ACR; MEF Service Definitions for emulated circuits. Applying what you know: Practical examples and scenarios, Carrier Ethernet solutions; Practice Scenarios, Given a scenario, determine appropriate Ethernet services

Geomechanics
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course This five-day course provides an intermediate level of understanding of the geomechanical factors that affect wellbore instability, sand production and hydraulic fracture design. The course is structured such that upon completion, participants will have understood the value that geomechanics can bring to drilling, completion and production operations and will be able to leverage this value wherever it applies. The course emphasis will be on integrating the topics presented through a combination of lectures, case-studies and hands-on exercises. A special focus will be on how geomechanics knowledge is extracted from routinely acquired well data and how it is applied in the prediction and prevention of formation instability. Course Highlights The course is essentially non-mathematical and makes wide use of diagrams, pictures and exercises to illustrate the essential concepts of geomechanics Essential Rock Mechanics Principles Wellbore Stability Analysis Anisotropic Rock Properties for unconventional projects Lost Circulation and Wellbore Strengthening applications Sand Production Management Input to Hydraulic Fracture design Salt instability Training Objectives By attending this training, you will be able to acquire the following: Apply the basic concepts of geomechanics to identify, predict and mitigate against formation instability during drilling, completion and production Target Audience This course is intended for Drilling Engineers, Well Engineers, Production Technologists, Completion Engineers, Well Superintendents, Directional Drillers, Wellsite Supervisors and others, who wish to further their understanding of rock mechanics and its application to drilling and completion. There is no specific formal pre-requisite for this course. However, attendees are requested to have been exposed to drilling, completions and production operations in their positions and to have a recommended minimum of 3 years of field experience. Trainer Your Expert Course Instructor is an operational geomechanics advisor with over 46 years of experience in exploration, development and production in the upstream oil and gas industry. After obtaining a BSc (Hons) Physics degree from Aberdeen University, he worked for a variety of oil service companies in wireline operations, management and formation evaluation, before joining Schlumberger in 1995. Since 2000 he has worked principally in real-time geomechanics operations and developing acousto-geomechical applications, taking on the role of geomechanics advisor and technical manager within the Europe-Africa area of operations. Before forming his own company in 2014, Your Expert Course Instructor was one of Schlumberger's principal instructors, delivering cross-discipline internal and external geomechanics training to petrophysicists, geologists, reservoir, petroleum, well construction and drilling engineers at operating company locations, training centers and operational centers worldwide. Through extensive operational and wellsite experience gained in the North Sea, Europe, Africa, South America and the Far East, he has gained a broad based knowledge of drilling, production, log data acquisition, analysis and interpretation that has allowed him to develop and deliver pragmatic solutions to the geomechanical challenges of drilling, sand production, fracturing and unconventional reservoirs, faced by operators. His principal interests include the development and application of acousto-geomechanical techniques for the evaluation of anisotropic formations and fracture systems and the identification and prevention of wellbore instability POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

Red Hat Virtualization with RHCVA Exam (RH319)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Linux system administrators, virtualization administrators, and hybrid infrastructure engineers interested in deploying large-scale virtualization solutions and managing virtual servers in their datacenters, based on the Red Hat Virtualization open virtualization management platform. Overview As a result of completing this offering, you should be able to create and deploy Red Hat Virtualization and virtual servers. Using a single, full-service management interface, Red Hat Virtualization Manager, you will be able to configure, manage, and migrate systems within the virtualization environment. In this course you will develop the skills needed to deploy, administer, and operate virtual machines in your organization using Red Hat© Virtualization. Through numerous hands-on exercises, you will demonstrate the ability to deploy and configure the Red Hat Virtualization infrastructure and use it to provision and manage virtual machines. This offering also prepares you for the Red Hat Certified Specialist in Virtualization exam.This course is based on Red Hat Enterprise Virtualization 4.3 and Red Hat Enterprise Linux© 7.6 and 8, as well as Red Hat Hyperconverged Infrastructure for Virtualization 1.6.This course covers the same material as RH318, but includes the Red Hat Certified Specialist in Virtualization exam (EX318). Red Hat Virtualization overview Explain the purpose and architecture of Red Hat Virtualization. Install and configure Red Hat Virtualization Install a minimal Red Hat Virtualization environment and use it to create a virtual machine. Create and manage datacenters and clusters Organize hypervisors into groups using datacenters and clusters. Manage user accounts and roles Configure user accounts using a central directory service, then use roles to assign access to resources based on job responsibilities. Adding physical hosts Add additional Red Hat Virtualization hosts automatically, and move and remove hosts from datacenters as needed. Scale Red Hat Virtualization infrastructure Add Red Hat Virtualization hosts automatically, configure Red Hat Enterprise Linux hosts when appropriate, and move and remove hosts from data centers as needed. Manage Red Hat Virtualization networks Separate network traffic into multiple networks on one or more interfaces to improve the performance and security of Red Hat Virtualization. Manage Red Hat Virtualization storage Create and manage data and ISO storage domains. Deploy and manage virtual machines Operate virtual machines in the Red Hat Virtualization environment. Migrate virtual machines Migrate and control automatic migration of virtual machines. Manage virtual machine images Manage virtual machine snapshots and disk images. Automating virtual machine deployment Automate deployment of virtual machines by using templates and cloud-init. Back up and upgrade Red Hat Virtualization Back up, restore, and upgrade the software in a Red Hat Virtualization environment. Explore high-availability practices Explain procedures to improve the resilience and reliability of Red Hat Virtualization by removing single points of failure and implementing high-availability features. Perform comprehensive review Demonstrate skills learned in this course by installing and configuring Red Hat Virtualization; using the platform to create and manage virtual machines; and backing up and updating components of Red Hat Virtualization.

GARDEN DESIGN TRAINING (BEGINNER TO ADVANCE LEVEL)
By Real Animation Works
Garden design face to face training customised and bespoke.

Cross Border Electricity Trading in Asia - Renewable Energy, Digital Technologies and New Operational Flexibility Solutions
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) This 3 half-day Virtual Instructor Led Training (VILT) course highlights the impact of the introduction of renewable energy, digital technologies and new operational flexibility solutions in the electricity trading market. These advancements facilitate unique opportunities and challenges for cross border trading of electricity. Most countries in Asia, have designed their own portfolio of climate actions with an accelerated penetration of renewable energy (or by importing renewable energy into their local grids). These changes are taking place at unprecedented speed and add further complexity to the operation of electricity trading markets, while presenting new opportunities. The Asian market, can tap into its vast potential of solar, wind and geothermal energy sources. A global, unified vision is emerging to support each of countries' energy needs and decarbonization goals. This VILT course will highlight priorities of each country to achieve its energy goals. The main operational flexibilities of each type of renewable resource are discussed in detail. The course also discusses the main components of Power Purchase Agreements and advancements in digitalization and how digital technologies can influence the energy market and cross border electricity trading. Key Takeaways: New Energy Market Design Cross Border Trading PPAs Mechanisms and Examples of PPAs The Increased Penetration of Renewable Resources in the Power Systems and How It Stimulates Cross Border Trading How Digital Innovation Drives Energy Markets and Cross Border Trading Training Objectives Upon completion of this VILT course, participants will be able to: Be familiar with the global vision of One Sun, One World, One Grid Understand the major trends reshaping the energy markets Learn how innovative digital technologies change the energy markets Understand why sustainable energy markets require a tighter coordination between transmission and distribution system operators Engage with each other to design the energy market of the future Target Audience This VILT course will benefit policy makers and regulators from energy agencies, transmission companies and utilities as well as power system engineers and power system operators from control centre and ISO. Training Methods The VILT will be delivered online in 3 half-day sessions comprising 4 hours per day, including time for lectures, discussion, quizzes and short classroom exercises. Course Duration: 3 half-day sessions, 4 hours per session (12 hours in total). Trainer Your expert course leader is a Utility Executive with extensive global experience in power system operation and planning, energy markets, enterprise risk and regulatory oversight. She consults on energy markets integrating renewable resources from planning to operation. She led complex projects in operations and conducted long term planning studies to support planning and operational reliability standards. Specializing in Smart Grids, Operational flexibilities, Renewable generation, Reliability, Financial Engineering, Energy Markets and Power System Integration, she was recently engaged by the Inter-American Development Bank/MHI in Guyana. She was the Operations Expert in the regulatory assessment in Oman. She is a registered member of the Professional Engineers of Ontario, Canada. She is also a contributing member to the IEEE Standards Association, WG Blockchain P2418.5. With over 25 years with Ontario Power Generation (Revenue $1.2 Billion CAD, I/S 16 GW), she served as Canadian representative in CIGRE, committee member in NSERC (Natural Sciences and Engineering Research Council of Canada), and Senior Member IEEE and Elsevier since the 90ties. Our key expert chaired international conferences, lectured on several continents, published a book on Reliability and Security of Nuclear Power Plants, contributed to IEEE and PMAPS and published in the Ontario Journal for Public Policy, Canada. She delivered seminars organized by the Power Engineering Society, IEEE plus seminars to power companies worldwide, including Oman, Thailand, Saudi Arabia, Malaysia, Indonesia, Portugal, South Africa, Japan, Romania, and Guyana. Our Key expert delivered over 60 specialized seminars to executives and engineers from Canada, Europe, South and North America, Middle East, South East Asia and Japan. Few examples are: Modern Power System in Digital Utilities - The Energy Commission, Malaysia and utilities in the Middle East, GCCIA, June 2020 Assessment of OETC Control Centre, Oman, December 2019 Demand Side management, Load Forecasting in a Smart Grid, Oman, 2019 Renewable Resources in a Smart Grid (Malaysia, Thailand, Indonesia, GCCIA, Saudi Arabia) The Modern Power System: Impact of the Power Electronics on the Power System The Digital Utility, AI and Blockchain Smart Grid and Reliability of Distribution Systems, Cyme, Montreal, Canada Economic Dispatch in the context of an Energy Market (TNB, Sarawak Energy, Malaysia) Energy Markets, Risk Assessment and Financial Management, PES, IEEE: Chicago, San Francisco, New York, Portugal, South Africa, Japan. Provided training at CEO and CRO level. Enterprise Risk methodology, EDP, Portugal Energy Markets: Saudi Electricity Company, Tenaga National Berhad, Malaysia Reliability Centre Maintenance (South East Asia, Saudi Electricity Company, KSA) EUSN, ENERGY & UTILITIES SECTOR NETWORK, Government of Canada, 2016 Connected+, IOT, Toronto, Canada September 2016 and 2015 Smart Grid, Smart Home HomeConnect, Toronto, Canada November 2014 Wind Power: a Cautionary Tale, Ontario Centre for Public Policy, 2010 POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations
