- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
5025 Security courses
SonicWall Network Security Professional Course - SNSP - NA
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Security professionals, System engineers, channel partners, service partners, and end users with 1+ years of experience in implementing IT security technologies (Network, Applications, and Systems) and are also SNSAcertified. Overview The students will learn how to monitor, investigate, analyze, and configure SonicWall Next-Gen firewalls running SonicOS to enable advanced functionality related to Secure and Remote Connectivity, Network Optimization, and Threat Prevention. Upon successful completion of the SNSP program, the students will be able to demonstrate SonicWall product expertise and the application skill sets required to mount a proactive, effective defense against current and evolving network and cyber security threats. A key issue affecting an organization?s business productivity and employee efficiency today is its ability to respond to dynamic changes in the cyber threat landscape. Coming up on the heels of the highly successful SNSA program launched earlier this year, SonicWall now presents the SonicWall Network Security Professional (SNSP) course, an expert-level training and certification program that builds on the enterprise security skills learned in the SNSA course. Previously known as the Network Security Advance Administration (NSAA) course, the revamped SNSP curriculum expands on the topics covered in SNSA and features advanced SonicWall firewall configuration and administration tasks aimed at helping enterprises adapt to dynamic security environments. Relevant changes to the curriculum include an enhanced and deeper scope of SonicOS 6.5.x features and functionality, as well as changes in the learning and delivery methodologies to better balance the professional needs of the students and the business requirements for network and cyber security. Course Outline Course Introduction and Overview Configuring VPN Auto Provisioning Configuring Advanced Routing Configuring Advanced Interface Settings Using SonicOS CLI Configuring Capture Client Capturing and Replaying Packets Configuring DPI-SSL/TLS Server Configuring DPI-SSH Configuring App Rules Configuring App Control Configuring Advanced High Availability Excluding Trusted Content Resolving and Reporting False Positives Configuring Content Filtering Implementing Best Practices

Cisco Implementing Automation for Cisco Security Solutions v1.0 (SAUI)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Channel and Customer Engineers Network Engineer System Engineer Wireless Engineer Consulting Systems Engineer Technical Solutions Architect Network Admisnistrator Wireless Design Engineer Network Manager Channel SEs Sales Engineer Channel AMs Account Manager Overview Upon completing this course, students will be able to meet these objectives: Understand the overall architecture of the Cisco security solutions and how APIs help enable security Understand how to use Cisco Firepower APIs Understand how pxGrid APIs function and their benefits Understand what capabilities the Cisco Stealthwatch APIs offer and construct API requests to them for configuration changes and auditing purposes Understand the features and benefits of using Cisco Stealthwatch Cloud APIs Learn how to use the Cisco Umbrella Investigate API Understand the Functionality provided by Cisco AMP and its APIs Learn how to use Cisco Threat Grid APIs to analyze, search, and dispose of threats This course demonstrates the tools and the benefits of leveraging programmability and automation in Cisco Security Solutions, including Cisco Firepower Management Center, Cisco Firepower Threat Defense, Cisco ISE, Cisco pxGrid, Cisco Stealthwatch Enterprise, Cisco Stealthwatch Cloud, Cisco Umbrella, Cisco AMP, Cisco Threat grid, and Cisco Security Management Appliances. Students will learn how to use the API for each Cisco security solution and specific applications of when the API benefits IT security content. Introducing Cisco Security APIs Role of APIs in Cisco Security Solutions Cisco Firepower, Cisco ISE, Cisco pxGrid, and Cisco Stealthwatch APIs Use cases and security workflow Consuming Cisco Advanced Malware Protection APIs Cisco AMP overview Cisco AMP endpoint API Cisco AMP use cases and workflows Discovery 1: Query Cisco AMP endpoint APIs for verifying compliance Using Cisco ISE Introducing Cisco Identity services engine Cisco ISE use cases Cisco ISE APIs Using Cisco pxGrid APIs Cisco pxGrid overview WebSockets and STOMP messaging protocol Discovery 2: Use the REST API and Cisco pxGrid with Cisco Identity services engine Using Cisco Threat Grid APIs Cisco threat grid overview Cisco threat grid API Cisco threat grid use cases and workflows Discovery 3: Construct a Python script using the Cisco threat grid API Investigating Cisco Umbrella Security Data Programmatically Cisco Umbrella investigate API overview Cisco Umbrella investigate API: Details Discovery 4: Query security data with the Cisco Umbrella investigate API Exploring Cisco Umbrella Reporting and Enforcement APIs Cisco Umbrella reporting and enforcement APIs: Overview Cisco Umbrella reporting and enforcement APIs: Deep dive Discovery 5: Generate reports using the Cisco Umbrella reporting API Automating Security with Cisco Firepower APIs Review basic constructs of Firewall policy management Design policies for automation Cisco FMC APIs in depth Discovery 6: Explore the Cisco Firepower management center API Cisco FTD automation with ansible Discovery 7: Use ansible to automate Cisco Firepower threat defense configuration Cisco FDM API in depth Discovery 8: Automate Firewall policies using the Cisco Firepower device manager API Operationalizing Cisco Stealthwatch and Its API Capabilities Cisco Stealthwatch overview Cisco Stealthwatch APIs: Details Discovery 9: Automate alarm policies and create reports using the Cisco Stealthwatch APIs Using Cisco Stealthwatch Cloud APIs Cisco Stealthwatch Cloud overview Cisco Stealthwatch Cloud APIs: Deep dive Discovery 10: Construct a report using Cisco stealthwatch Cloud APIs Describing Cisco Security Management Appliance APIs Cisco SMA APIs overview Cisco SMA API Discovery 11: Construct reports using Cisco SMA APIs

SWSA v3.0-Securing the Web with Cisco Web Security Appliance
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Security architects System designers Network administrators Operations engineers Network managers, network or security technicians, and security engineers and managers responsible for web security Cisco integrators and partners Overview After taking this course, you should be able to: Describe Cisco WSA Deploy proxy services Utilize authentication Describe decryption policies to control HTTPS traffic Understand differentiated traffic access policies and identification profiles Enforce acceptable use control settings Defend against malware Describe data security and data loss prevention Perform administration and troubleshooting The Securing the Web with Cisco Web Security Appliance (SWSA) v3.0 course shows you how to implement, use, and maintain Cisco© Web Security Appliance (WSA), powered by Cisco Talos, to provide advanced protection for business email and control against web security threats. Through a combination of expert instruction and hands-on practice, you?ll learn how to deploy proxy services, use authentication, implement policies to control HTTPS traffic and access, implement use control settings and policies, use the solution?s anti-malware features, implement data security and data loss prevention, perform administration of Cisco WSA solution, and more. Describing Cisco WSA Technology Use Case Cisco WSA Solution Cisco WSA Features Cisco WSA Architecture Proxy Service Integrated Layer 4 Traffic Monitor Data Loss Prevention Cisco Cognitive Intelligence Management Tools Cisco Advanced Web Security Reporting (AWSR) and Third-Party Integration Cisco Content Security Management Appliance (SMA) Deploying Proxy Services Explicit Forward Mode vs. Transparent Mode Transparent Mode Traffic Redirection Web Cache Control Protocol Web Cache Communication Protocol (WCCP) Upstream and Downstream Flow Proxy Bypass Proxy Caching Proxy Auto-Config (PAC) Files FTP Proxy Socket Secure (SOCKS) Proxy Proxy Access Log and HTTP Headers Customizing Error Notifications with End User Notification (EUN) Pages Utilizing Authentication Authentication Protocols Authentication Realms Tracking User Credentials Explicit (Forward) and Transparent Proxy Mode Bypassing Authentication with Problematic Agents Reporting and Authentication Re-Authentication FTP Proxy Authentication Troubleshooting Joining Domains and Test Authentication Integration with Cisco Identity Services Engine (ISE) Creating Decryption Policies to Control HTTPS Traffic Transport Layer Security (TLS)/Secure Sockets Layer (SSL) Inspection Overview Certificate Overview Overview of HTTPS Decryption Policies Activating HTTPS Proxy Function Access Control List (ACL) Tags for HTTPS Inspection Access Log Examples Understanding Differentiated Traffic Access Policies and Identification Profiles Overview of Access Policies Access Policy Groups Overview of Identification Profiles Identification Profiles and Authentication Access Policy and Identification Profiles Processing Order Other Policy Types Access Log Examples ACL Decision Tags and Policy Groups Enforcing Time-Based and Traffic Volume Acceptable Use Policies, and End User Notifications Defending Against Malware Web Reputation Filters Anti-Malware Scanning Scanning Outbound Traffic Anti-Malware and Reputation in Policies File Reputation Filtering and File Analysis Cisco Advanced Malware Protection File Reputation and Analysis Features Integration with Cisco Cognitive Intelligence Enforcing Acceptable Use Control Settings Controlling Web Usage URL Filtering URL Category Solutions Dynamic Content Analysis Engine Web Application Visibility and Control Enforcing Media Bandwidth Limits Software as a Service (SaaS) Access Control Filtering Adult Content Data Security and Data Loss Prevention Data Security Cisco Data Security Solution Data Security Policy Definitions Data Security Logs Performing Administration and Troubleshooting Monitor the Cisco Web Security Appliance Cisco WSA Reports Monitoring System Activity Through Logs System Administration Tasks Troubleshooting Command Line Interface References Comparing Cisco WSA Models Comparing Cisco SMA Models Overview of Connect, Install, and Configure Deploying the Cisco Web Security Appliance Open Virtualization Format (OVF) Template Mapping Cisco Web Security Appliance Virtual Machine (VM) Ports to Correct Networks Connecting to the Cisco Web Security Virtual Appliance Enabling Layer 4 Traffic Monitor (L4TM) Accessing and Running the System Setup Wizard Reconnecting to the Cisco Web Security Appliance High Availability Overview Hardware Redundancy Introducing Common Address Redundancy Protocol (CARP) Configuring Failover Groups for High Availability Feature Comparison Across Traffic Redirection Options Architecture Scenarios When Deploying Cisco AnyConnect© Secure Mobility Additional course details: Nexus Humans SWSA v3.0-Securing the Web with Cisco Web Security Appliance training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the SWSA v3.0-Securing the Web with Cisco Web Security Appliance course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Certified Kubernetes Security Specialist (CKS) Course
By Packt
Want to learn about Kubernetes security or need to pass the Certified Kubernetes Security Specialist (CKS) exam? You are at the right place. A hands-on course to help you develop your Kubernetes security skills. You need to have a basic understanding of Kubernetes Administrator to get the best out of this course.

CompTIA IT Fundamentals+
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course will prepare participants to take the FC0-U61 exam to obtain the IT Fundamentals+ certification and help participants learn some of the basic principles and techniques of providing PC, mobile, applications, and network support. Overview On course completion, participants will be able to: - Set up a computer workstation and use basic software applications. - Explain the functions and types of devices used within a computer system. - Apply basic computer maintenance and support principles. - Describe some principles of software and database development. - Configure computers and mobile devices to connect to home networks and to the Internet. - Identify security issues affecting the use of computers and networks. This course will prepare participants to take the FC0-U61 exam to obtain the IT Fundamentals+ certification and help participants learn some of the basic principles and techniques of providing PC, mobile, applications, and network support. 1 - Identifying Computer Hardware Identify Types of Computing Devices Identify Internal Computer Components Common Computer Connector Types Identify Common Peripheral Devices 2 - Identifying Computer Software Compare Functions and Features of Common Operating Systems Identify Application Software 3 - Setting Up a Basic Workstation Connect Hardware Install and Configure Operating Systems Install and Configure Applications Configure Accessibility Options 4 - Configuring Network Access Network Connection Types Install and Configure a SOHO Router Network and Alternative Technologies Sharing and Storage Methods 5 - Working with Files, Folders, and Applications Create Files Navigate a File Structure Manage Files and Folders Compress and Extract Files Create Screen Captures 6 - Configuring and Using Wireless Devices Configuring Wireless Devices Use Wireless Devices 7 - Securing Computing Devices Identify Security Threats Apply Security Best Practices Perform Secure Web Browsing 8 - Supporting Computers and Users Environmental and Safety Concepts Back Up and Restore Data Manage Software Implement Basic Support Measures Additional course details: Nexus Humans CompTIA IT Fundamentals Plus Certification (ITF Plus) (Exam FCO-U61) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the CompTIA IT Fundamentals Plus Certification (ITF Plus) (Exam FCO-U61) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

C)ISSA Certified Information Systems Security Auditor Mile 2
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for IS Security Officers IS Managers Risk Managers IS Systems Auditors Information Systems Owners IS Control Assessors System Managers Government Employees Overview Upon completion, Certified Information Systems Security Auditor students will be able to establish industry acceptable Cyber Security & IS management standards with current best practices and be prepared to competently take the C)ISSA exam. The Certified Information Systems Security Auditor, C)ISSA , course covers the skills and knowledge to assess vulnerabilities, report on compliance and implement controls for private and public enterprises. Many organizations require an Information System Auditor?s expert knowledge when it comes to identifying critical issues and providing effective auditing solutions. Through the use of a risk-based approach, the C)ISSA is able to implement and maintain cost-effective security controls that are closely aligned with both business and industry standards. Course Outline The Process of Auditing Information Systems Risk-Based Auditing Audit Planning and Performance IS Systems Auditor reports IT Governance and Management Systems Acquisition, Development and Implementation Systems Development Models Types of Specialized Business Applications Application Controls Information Systems Operations, Maintenance, and Support System and Communications Hardware Additional course details: Nexus Humans C)ISSA Certified Information Systems Security Auditor Mile 2 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the C)ISSA Certified Information Systems Security Auditor Mile 2 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

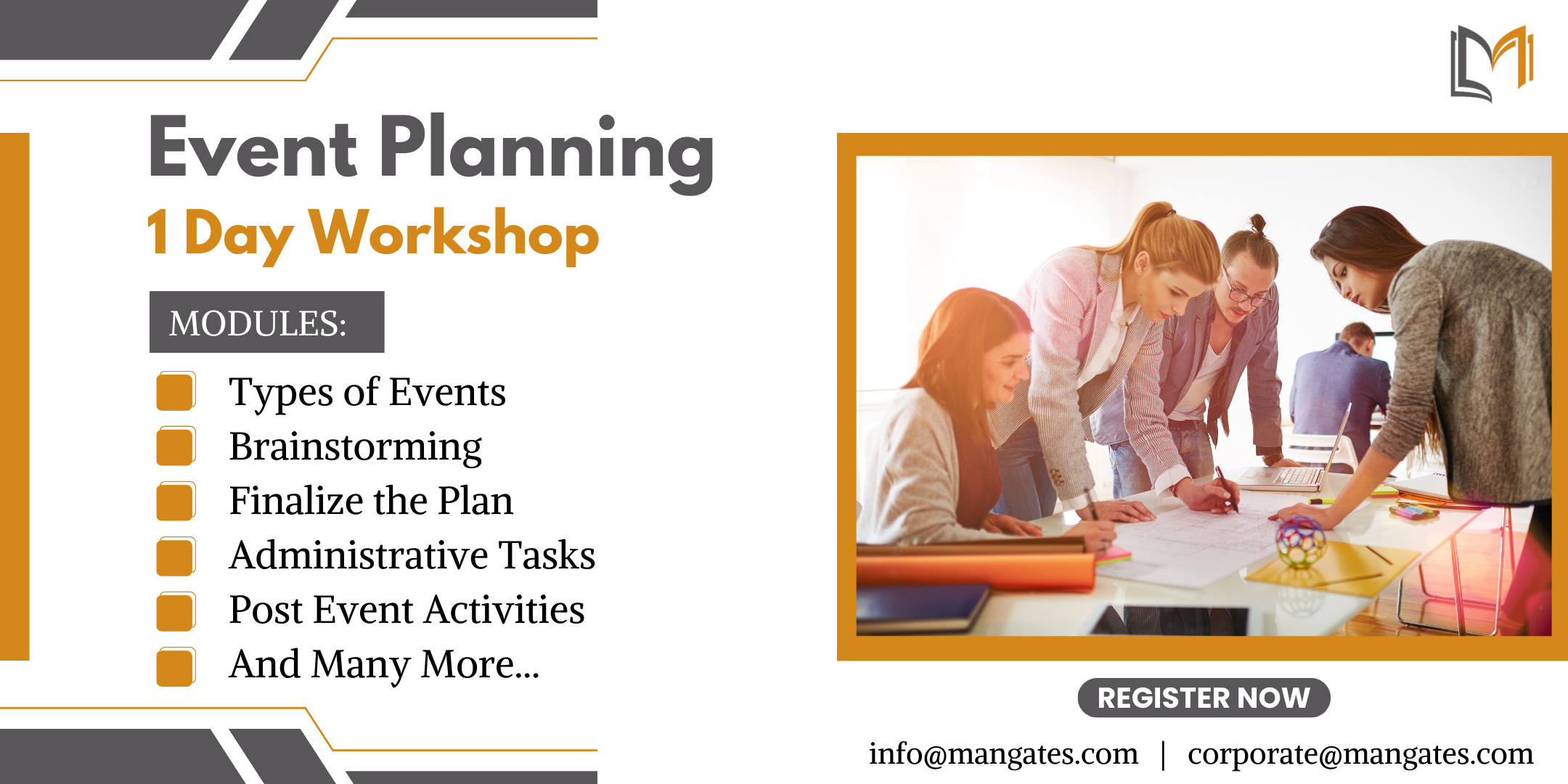
The Ultimate Guide to Event Planning - 1 Day Workshop in Bolton
By Mangates
Event Planning 1 Day Training in Bolton
CCSE Check Point Certified Security Expert
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is recommended for technical professionals who perform advanced deployment configurations of Check Point products. Overview Provide an overview of the upgrade service and options available. Explain how to perform management upgrade and migration. Articulate the process using CPUSE features. Articulate the purpose and function of Management High Availability. Explain Primary vs Secondary, Active vs Standby and Synchronization. Explain disaster recovery steps in case the primary management server becomes unavailable. Provide overview of Central Deployment in SmartConsole. Articulate an understanding of Security Gateway cluster upgrade methods. Explain about Multi Version Cluster (MVC) upgrades. Discuss Gaia Commands and how they are used. Explain the main processes on s and s. Describe how to work with scripts and SmartTasks to configure automatic actions. Explain the Management Data Plane Separation (MDPS) Explain kernel operations and traffic flow Articulate Dynamic and Updatable Objects in Security Gateways Explain the policy installation flow and files used. Describe the use of policy installation history. Explain concurrent and accelerated install policy. Describe an overview of APIs and ways to use and authenticate. Explain how to make changes in GAIA and management configuration. Explain how to install policy using API. Explain how the SecureXL acceleration technology enhances and optimizes Security Gateway performance. Describe how the CoreXL acceleration technology enhances and improves Security Gateway performance. Articulate how utilizing multiple traffic queues can make traffic handling more efficient. Discuss Site-to-Site VPN basics, deployment and communities. Describe how to analyze and interpret VPN tunnel traffic. Explain Link Selection and ISP Redundancy options. Explain tunnel management features. Discuss Check Point Remote Access solutions and how they differ from each other. Describe how client security can be provided by Remote Access . Explain authentication methods including machine authentication. Explain Multiple Entry Point (MEP). Discuss the Mobile Access Software Blade and how it secures communication and data exchange during remote connections. Learn basic concepts and develop skills necessary to administer IT security fundamental tasks. Course Outline Prepare for a Security Management Server Upgrade Upgrade the Security Management Server Deploy a Secondary Security Management Server Configure a Distributed Log Server Upgrade a Security Gateway from SmartConsole Work with the Command Line Use Scripts and SmartTasks Configure Dynamic Objects Monitor Traffic Verify Policy Installation and Status Work with Gaia and Management APIs Work with Acceleration Features Configure a Locally Managed Site to Site VPN Configure a Site to Site VPN with an Interoperable Device Configure Remote Access VPN Configure Mobile Access VPN Configure a High Availability Cluster Work with ClusterXL Configure Policy Compliance Deploy SmartEvent

Cisco Implementing Cisco Unified Communications Security v1.0 (UCSEC)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Channel Partner/Reseller Customer Employee Overview To provide learners with the necessary knowledge and skills that are common in all Cisco Unified Communications Manager deployments and additionally, those that are required to fully implement a single site solution. Implementing Cisco Unified Communications Security (UCSEC) v1.0 is a new 5-day ILT class designed to provide students with the necessary knowledge and skills to implement security features in a Cisco Unified Communications environment. Cisco Unified Communications support several features and mechanisms to secure voice signaling and communications and to mitigate attacks against Cisco Unified Communications networks. The Implementing Cisco Unified Communications Security (UCSEC) v1.0 course introduces security mechanisms and describes different implementation scenarios that increase the security level of Cisco Unified Communications networks. Course Outline Course Overview Module 1 - Vulnerabilities of Cisco Unified Communications Networks and Security Fundamentals Module 2 - Network Infrastructure Security Module 3 - Cisco Unified Communications Manager and Endpoint Security Features Module 4 - Secure Cisco Unified Communications Integration and Features

Level 3 SIA Trainer Course is combined of Level 3 Award in Education and Training (former PTLLS) Course, Level 3: Conflict Management Course and Level 3 Award for Physical Intervention Trainers in the Private Security Industry Course. These courses are specifically designed for individuals wishing to become trainers for SIA compliant courses such as: SIA Door Supervision, Security Guarding, CCTV (Public space surveillance), Conflict Management, Vehicle Immobilisation etc courses. ABOUT THIS COURSE: This course consists of following aspects: Introduction to Adult Learning Lesson planning Delivering a lesson Teaching adults Practical teaching sessions How to vary teaching techniques How to recognise and deal with potential problems Assessing how well pupils are learning Teaching equipment and aids Conflict management Physical Intervention COURSE DURATION: It has been designed to be completed by 6 days and assignment afterwards. COURSE ASSESSMENT: For AET / PTLLS, No formal examination is required for this course, but at the end of the course you need to submit portfolio. For level 3 Conflict Management Course; showcase 2 scenario based role in the class, end of the course you need to submit portfolio and they will get assessed. For Level 3 Award for Physical Intervention Trainers in the Private Security Industry Course; demonstrate the PI techniques, they will be recorded, short MCQ Test and end of the course you need to submit portfolio and they will get assessed. If you have a busy life style, you also can spread out this course in two weeks or more to meet your personal commitment. HOW MUCH THIS COURSE COST? Online Course: (AET Online) is £1100.00 (All inclusive no hidden charges). This includes AET Online course, 1 Day CM and 2 days PI training. After successful completion you will receive 3 certificates and PI Licence Agreement which is called PI Master Trainer Licence. Zoom course: (AET Zoom class) is £1150.00 (All inclusive no hidden charges). This includes 3 days AET Zoom course, 1 Day CM and 2 days PI training. After successful completion you will receive 3 certificates and PI Licence Agreement which is called PI Master Trainer Licence. Face to Face Class: (AET Face to Face) is £1200.00 (All inclusive no hidden charges). This includes 3 days AET Class, 1 Day CM and 2 days PI training. After successful completion you will receive 3 certificates and PI Licence Agreement which is called PI Master Trainer Licence.

Search By Location
- Security Courses in London
- Security Courses in Birmingham
- Security Courses in Glasgow
- Security Courses in Liverpool
- Security Courses in Bristol
- Security Courses in Manchester
- Security Courses in Sheffield
- Security Courses in Leeds
- Security Courses in Edinburgh
- Security Courses in Leicester
- Security Courses in Coventry
- Security Courses in Bradford
- Security Courses in Cardiff
- Security Courses in Belfast
- Security Courses in Nottingham