- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
LEARN TO FOCUS ON INTERPERSONAL SKILLS, BEHAVIOR, AND ENVIRONMENT AND HOW TO PROMOTE DIVERSITY-POSITIVE INTERACTIONS. You will be able to focus on interpersonal skills, behavior, and environment, to see how they promote diversity-positive interactions, as well as learn causes for discriminatory practices and create an action plan for increasing workplace acceptance and harmony. Uncover and discard beliefs and attitudes that foster or block progress. By discovering your strengths as well as liabilities, you can build on the positive and move toward minimizing the negative. As a result, you will gain greater personal and professional satisfaction. PART I – BROADENING THE VIEW Find new perspectives and ways to turn challenges into opportunities. Become skilled at ways to further develop self-awareness and sensitivity. PART II – FAIR STANDARDS Learn about how attitudes expressed in speech and behavior promote or hinder a positive work environment. Determine and apply steps for getting past prejudice for greater productivity. PART III – ORGANIZATIONAL UNITY Discover value in diverse perspectives and personalities and their benefits. Strategize ways to strengthen relationships and turn negative into positive interactions. ATTENDEES WILL BE ABLE TO: Discover new ways to “see things differently;” Use Emotional Intelligence to strengthen relationships and increase awareness of self and others; Define Diversity and uncover ways in which it is significantly useful in an organization; Develop best practices (rooted in honor and law) to use Diversity in planning, problem solving, and decision-making); Manage conflict through unity, using the organization’s mission, vision, values, and goals; and Understand and communicate value to staff. Online Class—Diversity – Building a Thriving Business Environment is a 4-hour interactive virtual class. Register for this class and you will be sent ONLINE login instructions prior to the class date. Improving Communications brought our organization to realize how important our employees—our people—are to Baystate Dental. By helping us to develop a more thoughtful and sensitive nature, we now relate better with each other and our patients. Dr. Kevin Coughlin, DMD, FAGD, MBABaystate Dental
Clinical Coach Standardisation Event March 2025
By Samantha Morgan-Hourd
Clinical coach standardisation events
Digital CCTV and Remote Access Course
By Hi-Tech Training
The Digital CCTV & Remote Access course is designed to give participants a practical knowledge of integrating Analogue and Digital technologies in addition to access and control from remote locations such as laptops, tablets and mobile phones.

Driver CPC - 1 Day Periodic 7 Hour Course/ Vehicle Marshall, Banksman and Working at Height
By Total Compliance
Driver CPC - 1 Day Periodic 7 Hour Course Vehicle Marshall, Working at Height 1. Vehicle Marshall/Banksman Training: Learn the critical health and safety responsibilities involved in manoeuvring vehicles safely during loading and unloading operations. The course covers the safe use of work equipment and best practices for guiding vehicles as a Banksman. 2. Working at Height Training: Gain knowledge on how to work safely at height, understand the risks involved, and learn how to use the appropriate safety equipment to prevent accidents. Driver CPC Periodic Training: Complete 7 hours of mandatory training to count towards your Driver Certificate of Professional Competence (CPC) periodic requirement, helping you stay compliant and up to date with industry standards. Register now for this valuable training! Please review our Terms and Conditions for more information.
Level 3 Training: Domestic Abuse Response
By Restored
We're passionate about equipping churches to respond to domestic abuse. Our Domestic Abuse Awareness course will help you explore key questions around the issue of domestic abuse, like how to recognise the signs of domestic abuse, why domestic abuse happens, and how to start supporting survivors.

Her Biz: Free Women's Start-up Programme (Kent & E.Sussex) - March 2025
5.0(1)By Let’s Do Business Group
Are you thinking about setting up a new business? Her Biz, the 'virtual' Women's Start-Up programme is returning to support aspiring female entrepreneurs in East Sussex and Kent.

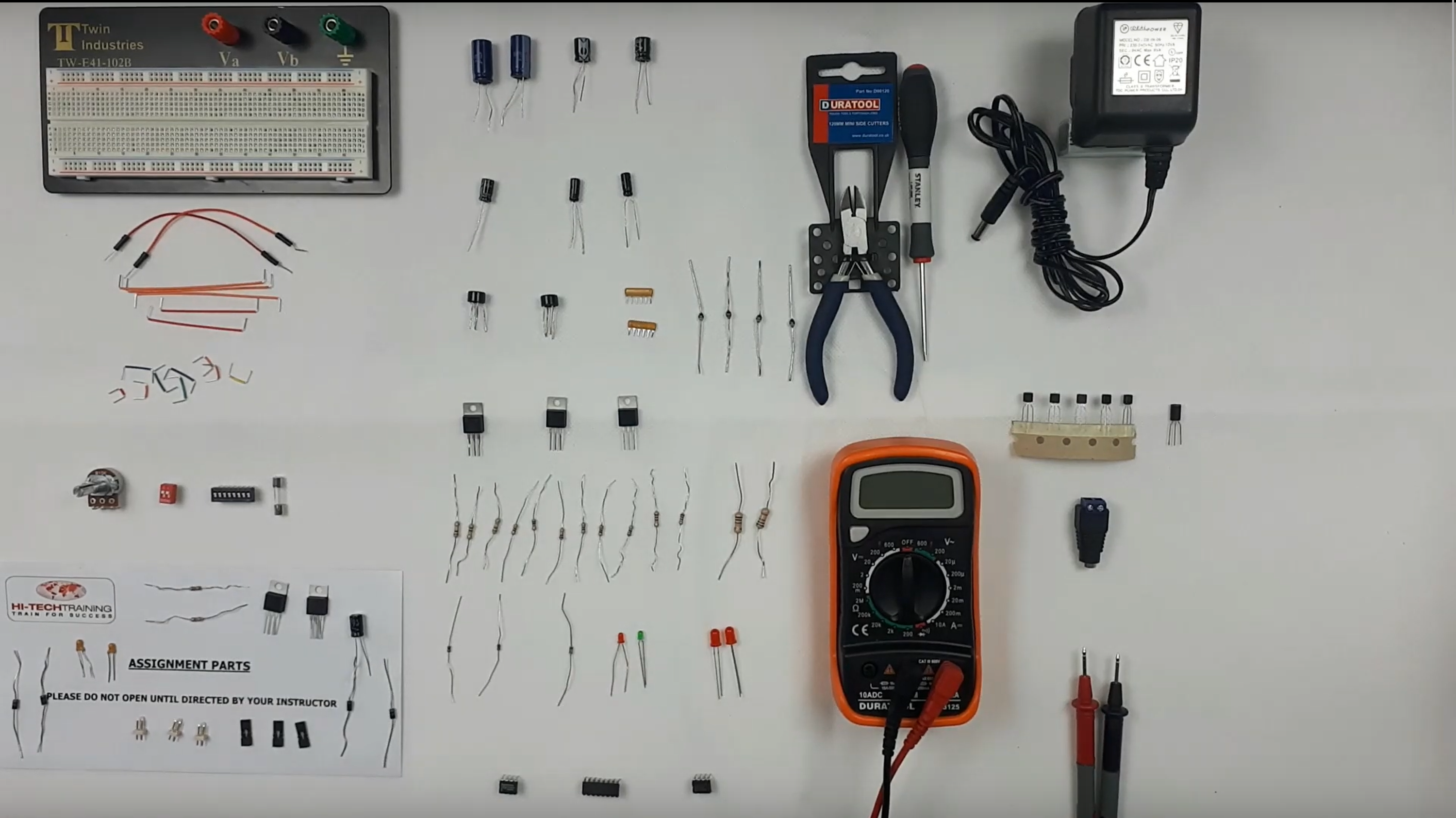
Electronics Repair 2 Course
By Hi-Tech Training
Electronics Equipment Repair 2 (Online Virtual Classroom) is a follow on course to Electronics Equipment Repair 1. This course builds on the skills gained and enables participants to build, test and fault-find more complex Analogue Electronic circuits
MI Skills Club for Educational Psychologists (MISC)
By The Ed Psych Coach
If you have already undertaken some training in Motivational Interviewing (at least half a day)*, you are welcome to join our MI Skills Club (MISC), which is a free community group for Educational Psychologists wishing to practise their MI skills within a small and friendly group. Because MI is a conversational style, rather than a discrete skill, it is not something that can be mastered by attending a one-off training session. While MI is a learnable approach, it takes practice, reflection and supervision to improve. Learning MI on your own is hard, and receiving objective feedback and expert feedback are helpful in developing and maintaining competence in MI (Miller & Rollnick, 2023). Cathy Atkinson and Fi Coley, who are both members of the Motivational Interviewing Network of Trainers (MINT), are collaborating to build an MI Learning Community for EPs. MINT (2019) defines a learning community as a network of practitioners interested in the same topic, and the community can serve as both a resource and a forum for developing practice. In each 90-minute online session we will focus on one small aspect of MI (micro-skills practice) and use breakout rooms with small groups to practice skills and give /receive supportive feedback. This event is open to Educational Psychologists, Trainee Educational Psychologists, and Assistant Psychologists. We are unable to accommodate aspiring EPs at this event. *If you are just starting out on your MI journey, or you would like to refresh your skills, you can join our one-day Introduction and Refresher training on Friday 27th September 2024 - Motivational Interviewing for Ed Psychs: Introduction and Refresher Tickets, Fri 27 Sep 2024 at 09:00 | Eventbrite