- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
11520 Professional Skills Course (PSC) courses
Developing Successful Interpersonal Skills
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for Managers and other professionals who want to gain the critical skills to successfully interact with or lead others through cooperative teamwork, as well as those desiring to improve their overall communication skills will benefit from this course. Overview Recognize the difference between hearing and listening Enhance interpersonal relationships through the use of verbal and non-verbal communication Apply techniques to move towards high-quality conversation Create a positive impression through a powerful introduction Influence others through sharing perspectives and opinions constructively Use logic and emotion to persuade and collaborate Identify ways of sharing thoughts and opinions constructively Prepare for and conduct simple negotiations This course will prepare students for the collaborative situations inherent in every facet of business, whether working with colleagues, partners, vendors, or clients. Private classes on this topic are available. We can address your organization?s issues, time constraints, and save you money, too. Contact us to find out how. 1. The Importance of Interpersonal Skills 2. Verbal Communication Techniques Hearing versus Actively Listening Connecting with Powerful Communication 3. Non-Verbal Communication Understanding the Elements of Vocal Delivery Interpreting and Applying Body Language Building Self-Awareness 4. Creating a Powerful First Impression Creating a Powerful Introduction Cultivating Your Impact 5. The Art of Conversation Mastering the 4 Levels of a Conversation Moving a Conversation Along Applying Tools for Deepening Conversation 6. Influence and Persuasion Influencing Others Seeing the Other Side Building Bridges Extending Your Influence 7. Interacting Positively Applying Logic and Owning Emotions Disagreeing Constructively Bringing People to Your Side Building Consensus 8. Negotiation Basics Planning for Negotiation Managing the 4 Stages of Negotiation Arriving at an Agreement Additional course details: Nexus Humans Developing Successful Interpersonal Skills training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Developing Successful Interpersonal Skills course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

This is course will give you EVERYTHING you need to become a VTCT Level 3 Qualified Skin Specialist. Why do you need THIS course? Previously the beauty industry had very lax regulation and you could start your business with just CPD accreditation. However, insurance companies, professional skin care brands and professional equipment providers are now looking for qualifications like VTCT as these are a set standard that require assignments and exams at a very minimum of Level 2 and in most cases Level 3. This means a combination of both VTCT and CPD means your business will meet industry standards What is the difference between CPD and VTCT? Qualifications are listed on the Regulated Qualifications Framework (RQF), which is the national framework of UK qualifications, and the certificate of achievement is issued by an Awarding Organisation. Your certificate means you are ‘qualified’ in that subject CPD is a piece of training developed by an individual or organisation that sits outside the regulated qualifications framework. It confers a skill not a qualification. Treatments such as dermaplaning can only be completed as a CPD therefore a combination of both VTCT and CPD will increase your revenue. You will gain the following; Level 3 Access to Aesthetic Therapies- This has Level 2 Facial Therapy within it making the course suitable for complete beginner. Full content list is below. Advanced Skin Care Diploma Microdermabrasion LED Light Therapy Dermaplaning Chemical Peels. Microneedling Nano Needling If you prefer one treatment at a time then we offer this too. You can find all our courses here We also offer the Level 4 Qualified Skin Specialist Course Please confirm dates and availability with us prior to purchasing Who Is This Course Suitable For? This course is perfect for those who are beginners with no experience. However, the course can be tailored for those who have partial qualifications/ accreditation and would like to become a qualified Level 3 practitioner. Course Content You will cover; VTCT (ITEC) Level 3 Certificate in Access to Aesthetic Therapies This qualification is based on the National Occupational Standards (NOS) for relevant principles of beauty therapy and includes all the required elements to achieve a measurable and comparable qualification, which will facilitate further and additional study at levels 4 and above. Learners must achieve all mandatory units which include: – Health and safety – Facial therapy – Consultation and client care – Anatomy, physiology and pathology – Electrical therapies Throughout this qualification, learners will develop their knowledge and understanding of relevant anatomy and physiology and health and safety pertaining to level 2 and 3 therapies. They will also develop the knowledge, understanding and skills to consult with clients and analyse their skin to help facilitate the provision of facial therapies. In parallel, learners will develop their communication and customer service skills, all of which are valued highly by employers. Advanced Skin Care Diploma Microdermabrasion LED Light Therapy (full course content can be found here) Dermaplaning (full course content can be found here) Chemical Peels. (full course content can be found here) Microneedling Nano Needling (full course content can be found here) A full start up equipment kit will be available to purchase on training. Details will be provided upon booking. Course Duration & Cost You will be registered onto online portal with easy access for viewing of tutorials reducing time in the centre. You will be required to do home study of treatment theory as well as assignments before you attend the practical training. This will allow more time to work on models and get hands on experience. The Qualified Level 3 Skin Specialist course is a combination of the Advanced Skin Care Diploma and VTCT (ITEC) Level 3 Certificate in Access to Aesthetic Therapies and you will be required to be in the centre for 4 intensive practical days £3200 Why Choose Us? This course will allow you to offer the most on trend and in demand treatments that are results driven. The key to a successful business is to offer services that clients will want to keep coming back for. All of the treatments within this diploma have proven results which will support you in customer retention. We do not offer online courses for treatments that require the skill that can only be performed in front an experienced trainer. We ensure we offer a practical course that allows you to work on 2 models per treatment. We want you to be confident in the skill so you can start your business straight away. We are not an Academy and we take pride in this. This means we offer more than just training you in a skill. We understand how difficult and overwhelming it can be to start a new business and our ethos is to provide guidance and support to get you started. All our sessions have an option of 1-2-1 sessions for a personalised experience and have a maximum of 4 students per session. Your journey with us doesn’t end in the practical training session. When you train with Elixir Skin Training you become a part of our brand. We stay in touch with all our graduates and provide that motivation to get you going, which you will not find in large Academies. Quality of training is important but so is what comes after- we support you in every aspect because we want to see you build your business. Categories: Advanced Skin Care Courses, Combined Courses, ofqual, Training

Certified Data Centre Expert (CDCE)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The primary audience for this course is any IT, facilities or data centre professional, who are involved in the design/build, renovation or relocation of a mission-critical data centre. Overview This 5-day course is designed to prepare participants to analyse a given business case and perform technical evaluation for a project plan and a set of designs for the implementation of a mission critical data centre. The course also engages participants in product evaluations and demonstrates how to select equipment and develop equipment test scripts (IET) and integrated performance and validation testing (IPVT). CDCE© builds upon knowledge gained in CDCP and CDCS courses. Participants who pass the exam will join the industry's elite data centre project design experts. CDCE© is the highest level training in the EPI Design and Build training track under the EPI Data Centre Training Framework. Participants must hold a valid CDCS certificate in order to be able to register for the CDCE class. CDCE© is the premier certification for data centre professionals in the data centre design/build and related fields. Data Centre Life Cycle Data centre lifecycle stages and phases Exercise: Stage/Phase/Milestone/Document mapping Design Preparation Creation of a SON ? Statement Of Need Technology review Conceptual sizing How to calculate for computer room space How to calculate facility space How to calculate incoming power Exercise: Conceptual sizing building and power Analysing capacity of existing facility Analysing investment options Site selection Permits and approvals Exercise: Site selection Conceptual design Budget and project timeline Business case preparation Project delivery structure Project management options Project manager and team Design Planning OSRA?Operational Systems Requirement Analysis TFRA?Technical Facilities Requirement Analysis Operations and maintenance review RFP?Request For Proposal process Vendor selection Design Development Project planning Design development PDR ? Preliminary Design Review Equipment selection FDR/V ? Final Design Review/Validation Exercise: Full design validation of power, cooling, floor plans, fire suppression Design freeze and LLTI Creation of construction documents BOM/BOQ ? Bill Of Material/Bill Of Quantity Exercise: Equipment selection Acquire Requirements of purchase orders Shipping terms FWT/FAT ? Factory Witness Test/Factory Acceptance Test Sequencing Incoming goods inspection and handling Asset management Construct Temporary essential services Erection of the building Permanent essential services Building inspection Snag list COF?Certificate Of Fitness Fit-Out Fit-Out Builders cleaning As-Built Drawings Test & Commissioning IET?Individual Equipment Test IPVT/IST?Integrated Performance Verification Test/Integrated Systems Test Common mistakes with IET/IPVT Deep cleaning Exercise: IET/IPVT scripting Hand-Over Facility hand-over requirements and documents PCC?Practical Completion Certificate DLP?Defect Liability Period Defect Management ICT Systems Installation ICT Systems Testing Hand-Over/DLP Expiry FCC?Final Completion Certificate Retirement Reasons and definitions of retirement Building the business case and project plan Sequencing Transfer of site Demolishing of site Legal matters FCC?Final Completion Certificate Exam: Certified Data Centre Expert (CDCE©) The CDCE© exam is in two parts: Part A is a 90-minute closed book exam, with 60 multiple-choice questions. For Part A, the candidate requires a minimum of 45 correct answers to pass the exam. Part B is a 90-minute closed book exam, with 25 open questions. For Part B the candidate needs to obtain a minimum of 75% to pass. Additional course details: Nexus Humans Certified Data Centre Expert (CDCE) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Certified Data Centre Expert (CDCE) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

ICA International Diploma in Managing Sanctions Risk
By International Compliance Association
ICA International Diploma in Managing Sanctions Risk Sanctions are a crucial instrument in the international battle against financial crime proliferation, terrorism and human rights abuses. It's a complex area and those who manage the risk need the right combination of knowledge, capabilities and behaviours to do so effectively. Technical skills - develop a deeper understanding of sanctions architecture, screening and the control framework; enrich your professional skillset Critical thinking - enhance your judgment-making and problem-solving skills Collaboration and communication - ensure a joined-up approach in your management of sanctions cases Flexibility and adaptability - be prepared to respond to fast-changing regimes and rules Leadership - be empowered to make effective decisions quickly and manage resources appropriately This course is awarded in association with Alliance Manchester Business School, the University of Manchester. Through this Level 6- Advanced qualification you will learn: Global sanctions architecture - Sanctions in context How sanctions regimes are implemented Evolving scope of sanctions - A changing tool Sector-based sanctions Identifying higher risk jurisdictions and activities Transparency, control, and ownership Licensing and permissible payments Management of global exposure to unilateral and regional sanctions Developing the control framework Sanctions screening Incident management and holding of sanctioned funds Sanctions lifting and roll back

CertNexus Certified CyberSec First Responder (CFR-410)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed primarily for cybersecurity practitioners preparing for or who currently perform job functions related to protecting information systems by ensuring their availability, integrity, authentication, confidentiality, and non-repudiation. It is ideal for those roles within federal contracting companies and private sector firms whose mission or strategic objectives require the execution of Defensive Cyber Operations (DCO) or DoD Information Network (DoDIN) operation and incident handling. This course focuses on the knowledge, ability, and skills necessary to provide for the defense of those information systems in a cybersecurity context, including protection, detection, analysis, investigation, and response processes. Overview In this course, you will identify, assess, respond to, and protect against security threats and operate a system and network security analysis platform. You will: Assess cybersecurity risks to the organization. Analyze the threat landscape. Analyze various reconnaissance threats to computing and network environments. Analyze various attacks on computing and network environments. Analyze various post-attack techniques. Assess the organization's security posture through auditing, vulnerability management, and penetration testing. Collect cybersecurity intelligence from various network-based and host-based sources. Analyze log data to reveal evidence of threats and incidents. Perform active asset and network analysis to detect incidents. Respond to cybersecurity incidents using containment, mitigation, and recovery tactics. Investigate cybersecurity incidents using forensic analysis techniques. This course covers network defense and incident response methods, tactics, and procedures that are in alignment with industry frameworks such as NIST 800-61r2 (Computer Security Incident Handling Guide), US-CERT's National Cyber Incident Response Plan (NCIRP), and Presidential Policy Directive (PPD)-41 on Cyber Incident Coordination. It is ideal for candidates who have been tasked with the responsibility of monitoring and detecting security incidents in information systems and networks, and for executing standardized responses to such incidents. The course introduces tools, tactics, and procedures to manage cybersecurity risks, defend cybersecurity assets, identify various types of common threats, evaluate the organization's security, collect and analyze cybersecurity intelligence, and remediate and report incidents as they occur. This course provides a comprehensive methodology for individuals responsible for defending the cybersecurity of their organization. This course is designed to assist students in preparing for the CertNexus CyberSec First Responder (Exam CFR-410) certification examination. What you learn and practice in this course can be a significant part of your preparation. In addition, this course and subsequent certification (CFR-410) meet all requirements for personnel requiring DoD directive 8570.01-M position certification baselines: CSSP Analyst CSSP Infrastructure Support CSSP Incident Responder CSSP Auditor The course and certification also meet all criteria for the following Cybersecurity Maturity Model Certification (CMMC) domains: Incident Response (IR) Audit and Accountability (AU) Risk Management (RM) Lesson 1: Assessing Cybersecurity Risk Topic A: Identify the Importance of Risk Management Topic B: Assess Risk Topic C: Mitigate Risk Topic D: Integrate Documentation into Risk Management Lesson 2: Analyzing the Threat Landscape Topic A: Classify Threats Topic B: Analyze Trends Affecting Security Posture Lesson 3: Analyzing Reconnaissance Threats to Computing and Network Environments Topic A: Implement Threat Modeling Topic B: Assess the Impact of Reconnaissance Topic C: Assess the Impact of Social Engineering Lesson 4: Analyzing Attacks on Computing and Network Environments Topic A: Assess the Impact of System Hacking Attacks Topic B: Assess the Impact of Web-Based Attacks Topic C: Assess the Impact of Malware Topic D: Assess the Impact of Hijacking and Impersonation Attacks Topic E: Assess the Impact of DoS Incidents Topic F: Assess the Impact of Threats to Mobile Security Topic G: Assess the Impact of Threats to Cloud Security Lesson 5: Analyzing Post-Attack Techniques Topic A: Assess Command and Control Techniques Topic B: Assess Persistence Techniques Topic C: Assess Lateral Movement and Pivoting Techniques Topic D: Assess Data Exfiltration Techniques Topic E: Assess Anti-Forensics Techniques Lesson 6: Assessing the Organization's Security Posture Topic A: Implement Cybersecurity Auditing Topic B: Implement a Vulnerability Management Plan Topic C: Assess Vulnerabilities Topic D: Conduct Penetration Testing Lesson 7: Collecting Cybersecurity Intelligence Topic A: Deploy a Security Intelligence Collection and Analysis Platform Topic B: Collect Data from Network-Based Intelligence Sources Topic C: Collect Data from Host-Based Intelligence Sources Lesson 8: Analyzing Log Data Topic A: Use Common Tools to Analyze Logs Topic B: Use SIEM Tools for Analysis Lesson 9: Performing Active Asset and Network Analysis Topic A: Analyze Incidents with Windows-Based Tools Topic B: Analyze Incidents with Linux-Based Tools Topic C: Analyze Indicators of Compromise Lesson 10: Responding to Cybersecurity Incidents Topic A: Deploy an Incident Handling and Response Architecture Topic B: Mitigate Incidents Topic C: Hand Over Incident Information to a Forensic Investigation Lesson 11: Investigating Cybersecurity Incidents Topic A: Apply a Forensic Investigation Plan Topic B: Securely Collect and Analyze Electronic Evidence Topic C: Follow Up on the Results of an Investigation Additional course details: Nexus Humans CertNexus Certified CyberSec First Responder (CFR-410) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the CertNexus Certified CyberSec First Responder (CFR-410) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

EC-Council Certified Ethical Hacker (CEH) v12
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The Certified Ethical Hacking v12 course will significantly benefit security officers, auditors, security professionals, site administrators, and anyone who is concerned about the integrity of the network infrastructure. Overview Information security controls, laws, and standards. Various types of footprinting, footprinting tools, and countermeasures. Network scanning techniques and scanning countermeasures Enumeration techniques and enumeration countermeasures Vulnerability analysis to identify security loopholes in the target organization?s network, communication infrastructure, and end systems. System hacking methodology, steganography, steganalysis attacks, and covering tracks to discover system and network vulnerabilities. Different types of malware (Trojan, Virus, worms, etc.), system auditing for malware attacks, malware analysis, and countermeasures. Packet sniffing techniques to discover network vulnerabilities and countermeasures to defend against sniffing. Social engineering techniques and how to identify theft attacks to audit human-level vulnerabilities and social engineering countermeasures. DoS/DDoS attack techniques and tools to audit a target and DoS/DDoS countermeasures. Session hijacking techniques to discover network-level session management, authentication/authorization, and cryptographic weaknesses and countermeasures. Webserver attacks and a comprehensive attack methodology to audit vulnerabilities in webserver infrastructure, and countermeasures. Web application attacks, comprehensive web application hacking methodology to audit vulnerabilities in web applications, and countermeasures. SQL injection attack techniques, injection detection tools to detect SQL injection attempts, and countermeasures. Wireless encryption, wireless hacking methodology, wireless hacking tools, and Wi-Fi security tools. Mobile platform attack vector, android vulnerability exploitations, and mobile security guidelines and tools. Firewall, IDS and honeypot evasion techniques, evasion tools and techniques to audit a network perimeter for weaknesses, and countermeasures. Cloud computing concepts (Container technology, serverless computing), the working of various threats and attacks, and security techniques and tools. Penetration testing, security audit, vulnerability assessment, and penetration testing roadmap. Threats to IoT and OT platforms and defending IoT and OT devices. Cryptography ciphers, Public Key Infrastructure (PKI), cryptography attacks, and cryptanalysis tools. CEH provides an in-depth understanding of ethical hacking phases, various attack vectors, and preventative countermeasures. It will teach you how hackers think and act maliciously so you will be better positioned to setup your security infrastructure and defend against future attacks. An understanding of system weaknesses and vulnerabilities helps organizations strengthen their system security controls to minimize the risk of an incident. CEH was built to incorporate a hands-on environment and systematic process across each ethical hacking domain and methodology, giving you the opportunity to work towards proving the required knowledge and skills needed to achieve the CEH credential. You will be exposed to an entirely different posture toward the responsibilities and measures required to be secure. Now in its 12th version, CEH continues to evolve with the latest operating systems, tools, tactics, exploits, and technologies. 1 - Introduction to Ethical Hacking Information Security Overview Cyber Kill Chain Concepts Hacking Concepts Ethical Hacking Concepts Information Security Controls Information Security Laws and Standards 2 - 2 - Foot-printing and Reconnaissance Footprinting Concepts Footprinting through Search Engines Footprinting through Web Services Footprinting through Social Networking Sites Website Footprinting Email Footprinting Who is Footprinting DNS Footprinting Network Footprinting Footprinting through Social Engineering Footprinting Tools Footprinting Countermeasures 3 - Scanning Networks Network Scanning Concepts Scanning Tools Host Discovery Port and Service Discovery OS Discovery (Banner Grabbing/OS Fingerprinting) Scanning Beyond IDS and Firewall Draw Network Diagrams 4 - Enumeration Enumeration Concepts NetBIOS Enumeration SNMP Enumeration LDAP Enumeration NTP and NFS Enumeration SMTP and DNS Enumeration Other Enumeration Techniques Enumeration Countermeasures 5 - Vulnerability Analysis Vulnerability Assessment Concepts Vulnerability Classification and Assessment Types Vulnerability Assessment Solutions and Tools Vulnerability Assessment Reports 6 - System Hacking System Hacking Concepts Gaining Access Escalating Privileges Maintaining Access Clearing Logs 7 - Malware Threats Malware Concepts APT Concepts Trojan Concepts Virus and Worm Concepts Fileless Malware Concepts Malware Analysis Countermeasures Anti-Malware Software 8 - Sniffing Sniffing Concepts Sniffing Technique: MAC Attacks Sniffing Technique: DHCP Attacks Sniffing Technique: ARP Poisoning Sniffing Technique: Spoofing Attacks Sniffing Technique: DNS Poisoning Sniffing Tools Countermeasures Sniffing Detection Techniques 9 - Social Engineering Social Engineering Concepts Social Engineering Techniques Insider Threats Impersonation on Social Networking Sites Identity Theft Countermeasures 10 - Denial-of-Service DoS/DDoS Concepts DoS/DDoS Attack Techniques BotnetsDDoS Case Study DoS/DDoS Attack Tools Countermeasures DoS/DDoS Protection Tools 11 - Session Hijacking Session Hijacking Concepts Application Level Session Hijacking Network Level Session Hijacking Session Hijacking Tools Countermeasures 12 - Evading IDS, Firewalls, and Honeypots IDS, IPS, Firewall, and Honeypot Concepts IDS, IPS, Firewall, and Honeypot Solutions Evading IDS Evading Firewalls IDS/Firewall Evading Tools Detecting Honeypots IDS/Firewall Evasion Countermeasures 13 - Hacking Web Servers Web Server Concepts Web Server Attacks Web Server Attack Methodology Web Server Attack Tools Countermeasures Patch Management Web Server Security Tools 14 - Hacking Web Applications Web Application Concepts Web Application Threats Web Application Hacking Methodology Web API, Webhooks, and Web Shell Web Application Security 15 - SQL Injection SQL Injection Concepts Types of SQL Injection SQL Injection Methodology SQL Injection Tools Evasion Techniques Countermeasures 16 - Hacking Wireless Networks Wireless Concepts Wireless Encryption Wireless Threats Wireless Hacking Methodology Wireless Hacking Tools Bluetooth Hacking Countermeasures Wireless Security Tools 17 - Hacking Mobile Platforms Mobile Platform Attack Vectors Hacking Android OS Hacking iOS Mobile Device Management Mobile Security Guidelines and Tools 18 - IoT and OT Hacking IoT Hacking IoT Concepts IoT Attacks IoT Hacking Methodology IoT Hacking Tools Countermeasures OT Hacking OT Concepts OT Attacks OT Hacking Methodology OT Hacking Tools Countermeasures 19 - Cloud Computing Cloud Computing Concepts Container Technology Serverless Computing Cloud Computing Threats Cloud Hacking Cloud Security 20 - Cryptography Cryptography Concepts Encryption Algorithms Cryptography Tools Public Key Infrastructure (PKI) Email Encryption Disk Encryption Cryptanalysis Countermeasures Additional course details: Nexus Humans EC-Council Certified Ethical Hacker (CEH) v.12 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the EC-Council Certified Ethical Hacker (CEH) v.12 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

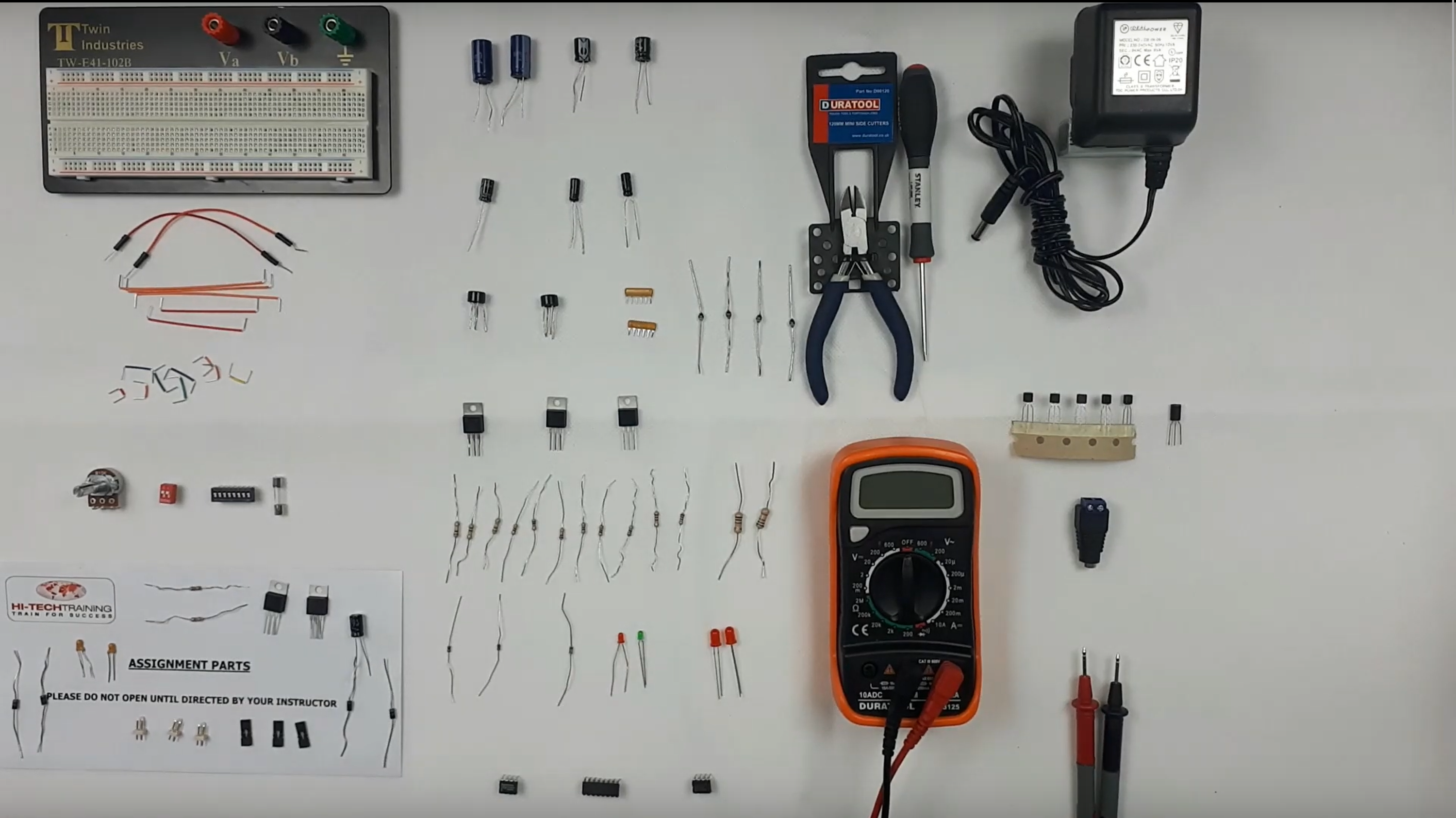
Electronics Repair 2 Course
By Hi-Tech Training
Electronics Equipment Repair 2 (Online Virtual Classroom) is a follow on course to Electronics Equipment Repair 1. This course builds on the skills gained and enables participants to build, test and fault-find more complex Analogue Electronic circuits
CompTIA PenTest+ (PenTest)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for IT professionals who want to develop penetration testing skills to enable them to identify information-system vulnerabilities and effective remediation techniques for those vulnerabilities. Target students who also need to offer practical recommendations for action to properly protect information systems and their contents will derive those skills from this course. This course is also designed for individuals who are preparing to take the CompTIA PenTest+ certification exam PT0-002, or who plan to use PenTest+ as the foundation for more advanced security certifications or career roles. Individuals seeking this certification should have three to four years of hands-on experience performing penetration tests, vulnerability assessments, and vulnerability management. Overview After completing this course, you will be able to plan, conduct, analyze, and report on penetration tests, including the ability to: Plan and scope penetration tests. Conduct passive reconnaissance. Perform non-technical tests to gather information. Conductive active reconnaissance. Analyze vulnerabilities. Penetrate networks. Exploit host-based vulnerabilities. Test applications. Complete post-exploit tasks. Analyze and report pen test results. Security remains one of the hottest topics in IT and other industries. It seems that each week brings news of some new breach of privacy or security. As organizations scramble to protect themselves and their customers, the ability to conduct penetration testing is an emerging skill set that is becoming ever more valuable to the organizations seeking protection, and ever more lucrative for those who possess these skills. In this course, you will be introduced to some general concepts and methodologies related to pen testing, and you will work your way through a simulated pen test for a fictitious company. 1 - Outline Lesson 1: Scoping Organization/Customer Requirements Lesson 2: Defining the Rules of Engagement Lesson 3: Footprinting and Gathering Intelligence Lesson 4: Evaluating Human and Physical Vulnerabilities Lesson 5: Preparing the Vulnerability Scan Lesson 6: Scanning Logical Vulnerabilities Lesson 7: Analyzing Scanning Results Lesson 8: Avoiding Detection and Covering Tracks Lesson 9: Exploiting the LAN and Cloud Lesson 10: Testing Wireless Networks Lesson 11: Targeting Mobile Devices Lesson 12: Attacking Specialized Systems Lesson 13: Web Application-Based Attacks Lesson 14: Performing System Hacking Lesson 15: Scripting and Software Development Lesson 16: Leveraging the Attack: Pivot and Penetrate Lesson 17: Communicating During the PenTesting Process Lesson 18: Summarizing Report Components Lesson 19: Recommending Remediation Lesson 20: Performing Post-Report Delivery Activities Additional course details: Nexus Humans CompTIA Penetration Testing Certification (PenTest Plus) - (Exam PT0-002) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the CompTIA Penetration Testing Certification (PenTest Plus) - (Exam PT0-002) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

MB-500T00 Dynamics 365 - Finance and Operations Apps Developer
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Microsoft Dynamics 365 Finance and Operations Apps Developers Overview By the end of this course, you will learn to develop fully realized solutions by using standardized application coding patterns. In this course, you will learn the tasks needed to fulfill the role of developer in Dynamics 365 Finance and Operations Apps. The Dynamics 365 for Finance and Operations (FO) developer is a key technical resource that implements and extends the application to meet the requirements of the business. Module 1: Overview & Architecturen Explore the ecosystem and main components Explore the technical architecture Explore design and deployment considerations Module 2: Developer Tools Manage implementations by using Lifecycle Services Manage source code by using version control Customize by using Visual Studio Module 3: Solution Design Implement application lifecycle management Module 4: AOT Elements Build extended data types and enumerations Build tables Build forms and optimize form performance Create classes Create other user interface elements Module 5: Code Development & Testing Explore the test framework and use tools Get started with development using X++ Develop object-oriented code Use RSAT tool Module 6: Data Migration Prepare data for migration Module 7: Frameworks Introduction Explore extensions and the extension framework Extend elements SysOperationSandbox framework Summary Module 8: Integration Identify data integration patterns and scenarios Implement data integration concepts and solutions Implement the data management package API Data integrations Integrate with Microsoft Azure Connecting to Power Platform services Consume business events Integrate Finance and Operations apps with Microsoft Dataverse Module 9: Reporting Explore the reporting tools Build reports Build workspaces Manage data sources with external data stores Module 10: Security & Performance Work with performance and monitoring tools Implement role-based security Apply basic performance optimization techniques Additional course details: Nexus Humans MB-500T00 Dynamics 365 - Finance and Operations Apps Developer training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the MB-500T00 Dynamics 365 - Finance and Operations Apps Developer course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

55371 Windows Server Administration
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for Information Technology (IT) Professionals who have some experience working with Windows Server and are looking for a single five-day course that covers core administration components and technologies in Windows Server. This course also helps server administrators from previous Windows Server versions to update their knowledge and skills related to Windows Server. The course is also for individuals from a service desk role who wish to transition into server maintenance. This five-day instructor-led course is designed primarily for IT professionals who have some experience with Windows Server. It is designed for professionals who will be responsible for managing identity, networking, storage and compute by using Windows Server, and who need to understand the scenarios, requirements, and options that are available and applicable to Windows Server. The course teaches IT professionals the fundamental administration skills required to deploy and support Windows Server in most organizations. Module 1: Windows Server Administration Overview Introducing Windows Server Windows Server Core Overview Windows Server administration principles and tools overview Module 2: Identity Services in Windows Server AD DS Overview Deploying Windows Server domain controllers Azure AD overview Implementing Group Policy Active Directory Certificate Services overview Module 3: Network Infrastructure services in Windows Server Deploying and managing DHCP Deploying and managing DNS service Deploying and managing IPAM Remote Access Services in Windows Server Module 4: File Servers and Storage management in Windows Server Volumes and File Systems in Windows Server Implementing sharing in Windows Server Implementing Storage Spaces in Windows Server Implementing Data Deduplication Implementing iSCSI Deploying Distributed File System Module 5: Hyper-V virtualization and containers in Windows Server Hyper-V in Windows Server Configuring VMs Securing virtualization in Windows Server Containers in Windows Server Overview of Kubernetes Module 6: High Availability in Windows Server Planning for failover clustering implementation Creating and configuring failover cluster Overview of stretch clusters High availability and disaster recovery solutions with Hyper-V VMs Module 7: Disaster recovery in Windows Server Hyper-V Replica Backup and restore infrastructure in Windows Server Module 8: Windows Server security Credentials and privileged access protection Hardening Windows Server JEA in Windows Server Securing and analyzing SMB traffic Windows Server update management Module 9: RDS in Windows Server Overview of RDS Configuring a session-based desktop deployment Overview of personal and pooled virtual desktops Module 10: Remote access and web services in Windows Server Implementing VPNs Implementing Always On VPN Implementing NPS Implementing Web Server in Windows Server Module 11: Server and performance monitoring in Windows Server Overview of Windows Server monitoring tools Using Performance Monitor Monitoring event logs for troubleshooting Module 12: Upgrade and migration in Windows Server AD DS migration Storage Migration Service Windows Server migration tools Additional course details: Nexus Humans 55371 Windows Server Administration training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the 55371 Windows Server Administration course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Search By Location
- Professional Skills Course (PSC) Courses in London
- Professional Skills Course (PSC) Courses in Birmingham
- Professional Skills Course (PSC) Courses in Glasgow
- Professional Skills Course (PSC) Courses in Liverpool
- Professional Skills Course (PSC) Courses in Bristol
- Professional Skills Course (PSC) Courses in Manchester
- Professional Skills Course (PSC) Courses in Sheffield
- Professional Skills Course (PSC) Courses in Leeds
- Professional Skills Course (PSC) Courses in Edinburgh
- Professional Skills Course (PSC) Courses in Leicester
- Professional Skills Course (PSC) Courses in Coventry
- Professional Skills Course (PSC) Courses in Bradford
- Professional Skills Course (PSC) Courses in Cardiff
- Professional Skills Course (PSC) Courses in Belfast
- Professional Skills Course (PSC) Courses in Nottingham