- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Delve into the mesmerising world of print through 'Mastering the Role of a Printing Worker: From Setup to Final Print'. This comprehensive course demystifies the core components of print production, taking you on a journey from the basic principles to intricate techniques. From grasping colour theory to exploring industry-standard software tools like Photoshop and Illustrator, each module has been meticulously designed to equip you with the knowledge to produce exceptional print outcomes. As the print industry continually evolves, this course ensures you are at the forefront, armed with the most up-to-date skills. Learning Outcomes of Mastering the Role of a Printing Worker: From Setup to Final Print course Understand the essential steps and processes involved in print production. Identify and utilise the right tools crucial for producing high-quality prints. Gain a deep knowledge of colour theory and its application in print. Acquire expertise in preparing raster images and the nuances of fonts in printing. Master software-specific techniques for optimal results in both Photoshop and Illustrator. Why buy this Mastering the Role of a Printing Worker: From Setup to Final Print? Unlimited access to the course for forever Digital Certificate, Transcript, student ID all included in the price Absolutely no hidden fees Directly receive CPD accredited qualifications after course completion Receive one to one assistance on every weekday from professionals Immediately receive the PDF certificate after passing Receive the original copies of your certificate and transcript on the next working day Easily learn the skills and knowledge from the comfort of your home Certification After studying the course materials of the Mastering the Role of a Printing Worker: From Setup to Final Print there will be a written assignment test which you can take either during or at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £5.99. Original Hard Copy certificates need to be ordered at an additional cost of £9.60. Who is this Mastering the Role of a Printing Worker: From Setup to Final Print course for? This Mastering the Role of a Printing Worker: From Setup to Final Print does not require you to have any prior qualifications or experience. You can just enrol and start learning. Individuals passionate about venturing into the printing industry. Graphic designers keen to extend their skill set into print production. Entrepreneurs aiming to set up their own print production unit. Art and design students looking to gain a competitive edge in the print world. Traditional printers seeking to update their knowledge with modern techniques. Prerequisites of Mastering the Role of a Printing Worker: From Setup to Final Print course This Mastering the Role of a Printing Worker: From Setup to Final Print does not require you to have any prior qualifications or experience. You can just enrol and start learning. This Mastering the Role of a Printing Worker: From Setup to Final Print was made by professionals, and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Career path Printing Technician: Average salary £24,000-£29,000 annually. Print Production Manager: Average salary £30,000-£40,000 annually. Graphic Designer (Print Specialisation): Average salary £25,000-£35,000 annually. Bindery Operator: Average salary £20,000-£26,000 annually. Colour Management Specialist: Average salary £28,000-£35,000 annually. Desktop Publisher: Average salary £23,000-£28,000 annually Course Curriculum Module 01: Fundamentals of Print Production Fundamentals of Print Production 00:13:00 Module 02: Process of Print Production Process of Print Production 00:17:00 Module 03: Tools of Print Production Tools of Print Production 00:16:00 Module 04: Understanding Colour Understanding Colour 00:15:00 Module 05: Binding and Finishing Binding and Finishing 00:11:00 Module 06: Preparing Raster Images Preparing Raster Images 00:15:00 Module 07: Understanding Fonts Understanding Fonts 00:12:00 Module 08: Photoshop Production Tips Photoshop Production Tips 00:14:00 Module 09: Illustrator Production Tips Illustrator Production Tips 00:13:00

SOLD OUT! 5th September Liza DeBlock #Agent121. Looking for: ADULT FICTION, NON-FICTION
5.0(3)By I Am In Print
LOOKING FOR: ADULT FICTION, NON-FICTION Liza represents a range of fiction and non-fiction. On the fiction side, she is looking for historical fiction that is well researched, immerses readers in the era, and looks at overlooked characters from the past, or perhaps gives a new spin on someone we think we know. On the literary and upmarket side, she is looking for novels infused with emotions that capture the human experience and make readers think. If your literary novel is something that A24 productions might turn into a movie, this is Liza’s taste. When it comes to fantasy, she loves urban and grounded fantasy (no sci-fi please!), and is always happy to look at anything with a vampire, werewolf, witches, warlocks, fairies, and perhaps a sinister selkie or two. She is also very much looking for romantasy and is the best person at the agency to submit that too. For thrillers, send her anything set in an exotic location, high-concept, or things with a speculative twist. She loves when characters are put in situations she would never want to be in, and then they have to get out of it. Her recent favourite fiction includes: Notes on an Execution, Lady Macbethad, Hamnet, A Discovery of Witches, House of Earth and Blood, The Starless Sea, Piranesi, Our Wives Under the Sea, The Pisces, Such A Fun Age. When it comes to non fiction, she is looking for books that teach her something new or reframe a topic from an alternative point of view. This can include cookery, pop science, and social history. Liza’s recent favourite non-fiction include: The Five, A History of Art Without Men, Messalina, The Authority Gap, Finding The Mother Tree, Cook This Book, Dessert Person. Liza would like you to submit a covering letter, 1 - 2 page synopsis and the first 5000 words of your manuscript in a single word document. (In addition to the paid sessions, Liza is kindly offering one free session for low income/underrepresented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Wednesday 27th August 2025

BOOKINGS CLOSE SOON! 5th September Florence Rees #Agent121. Looking for: ADULT FICTION, NON-FICTION
5.0(3)By I Am In Print
LOOKING FOR: ADULT FICTION, NON-FICTION Florence has been at A M Heath for five years and represents a range of commercial fiction and non-fiction. For fiction, comforting, funny and warm reads, as well as gripping page-turners, will always be Florence's cup of tea. Her favourite thing is to escape with a story she can’t put down. If you think your book fits that, then do send it to her. Books in this vein that really left her wanting one more chapter include Marian Keyes’s character, Rachel, from Rachel’s Holiday that left Florence with a compassion for addiction that only the most skilled of writers can conjure. Florence finds Catherine Newman to be a genius for making hospice care so funny in We All Want Impossible Things. Smart page turners such as Anatomy of a Scandal, Such a Fun Age, and Tomorrow, and Tomorrow, and Tomorrow, wowed her with clever, gripping prose and complicated, flawed characters she hadn't met before. She also loves older classics like the Cazalet Chronicles and Georgette Heyer’s Regency novels. Florence is actively looking for writers who are under-represented in the publishing world, through non-traditional channels, as well as her submissions. She’s keen to find non-fiction and fiction writers who speak to a millennial and younger audience, be that a journalist who is looking to expand an idea, a screenwriter who is looking to try their hand at fiction or perhaps an activist with a social media platform. She is also interested in environmental and social issues. The authors she represents include Jaspreet Kaur, Salma El-Wardany, Rachel Thompson, Annie Lord, Angelica Malin and Phil Ellis. Their books range from the heart-breaking and profound to the inspirational, funny and wise, with almost everything in between. Florence does not wish to receive, YA, Fantasy or Sci-fi. Florence would like you to submit a covering letter, 1 page synopsis and the first 5,000 words of your manuscript in a single word document. (In addition to the paid sessions, Florence is kindly offering one free session for low income/under-represented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Wednesday 27th August 2025

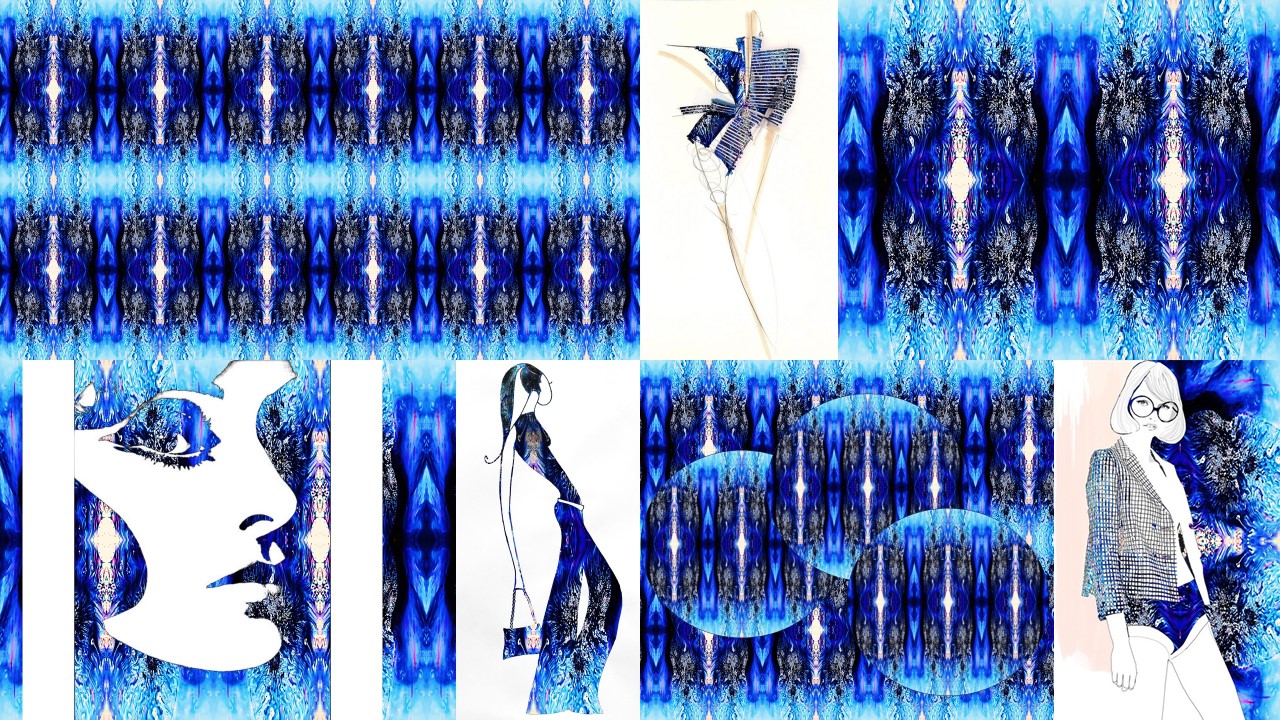
COMPUTER AIDED DESIGN + NICKY SIMPSON ONLINE ON-DEMAND FEES: FULL COURSE £35 WHAT THE COURSE IS ABOUT: A great short course, led by textile artist NICKY SIMPSON. This course introduces you to repeat patterning using PowerPoint, with video tutorials and comprehensive step-by-step guides. Whether you are using this in school, wanting to print for fashion or furnishing, or simply printing a T-shirt, this is a great way to get your own artwork or photographs into a repeat pattern for printing. It can also be used to print on paper for cards or letters and much more. This course shows how you can easily do repeat pattern designs, layering designs, inserting your designs into shapes and fashion illustration, with lots of exemplars and some inspirational designers. WHO IS THIS COURSE FOR: This course is suitable for anyone. You may be a teacher wanting to up-skill, a student who wants to further your current knowledge, or anyone who would like to be more creative with very limited equipment! All these tutorials can be used directly with students in schools. WHAT TO EXPECT: This comprehensive course offers a series of 6 short video tutorials, where you can practice alongside Nicky, working in your own time, at your own pace. Each video can be paused and rewound, using step-by-step guides. Introduction: Welcome to the training room Video Tutorial 1: How to use the Picture Format Tool Bar Video Tutorial 2: Creating Repeat Patterns Video Tutorial 3: CAD from your own primary images Video Tutorial 4: Layering images Video Tutorial 5: Inserting Your Repeat Patterns Into Shapes Video Tutorial 6: Fashion Illustration PDF: Designers & Exemplars LEARNING OUTCOMES: Learn and practice a new and exciting skill. Develop confidence and enhance your IT skills with free tools! Create exciting repeat patterns that can be used for fashion, interiors or stationary. A creative activity to get your own photographs into a repeat pattern ready for printing. YOUR TRAINER:
LOOKING FOR: ADULT FICTION, NON-FICTION Amanda Preston has been a literary agent for over 20 years and co-founded LBA in 2005. She won the RNA Literary Agent of the Year award in 2018. She represents commercial and reading group fiction, as well as a range of narrative non-fiction and memoir. She loves working with authors, championing them every step of the way, and works with them and their publishing teams to build them into brand names and award winning and bestselling authors in the UK and internationally. Whether commercial or reading-group, she loves innovative and well-written stories that hook her in from the start and whose voice stays with her. She is looking for novels that demand to be talked about and shared, whatever their genre, and that she is still thinking about days after finishing. She is on the hunt for a high-concept thriller which is character and plot driven, but also has a discussable issue at its heart i.e Elizabeth is Missing by Emma Healey and Girl A by Abigail Dean. She loves thrillers where the location is as integral to the plot as the crime i.e The Dry by Jane Harper and The Sanatorium by Sarah Pearse, and would love a good locked-room thriller but is only looking for fresh and unique ideas in this area. She is also on the hunt for a glorious book club love story that is doing something a bit different and special i.e Lessons in Chemistry by Bonnie Garmus or anything by Taylor Jenkins Reid or Liane Moriarty! Or smart, contemporary, observant romcoms with a very strong emphasis on diverse / own voices. Finally, she would love a historical that vividly brings that period to life as well as having a stunning plot i.e, The Familiars by Stacey Halls and The Doll Factory by Elizabeth MacNeal. Amanda would like you to submit a covering letter, 1 page synopsis and the opening three chapters (max 5,000 words). (In addition to the paid sessions, Amanda is kindly offering one free session for low income/under-represented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Monday 1st September 2025 by 12 noon UK BST

TWO SPACES LEFT! 9th September Jo Williamson #Agent121. Looking for: MG, ADULT FICTION
5.0(3)By I Am In Print
LOOKING FOR: MG, ADULT FICTION Jo Williamson has been in publishing for over 25 years. Having worked in Children’s books PR for Dorling Kindersley, HarperCollins and Orion, she started as an agent with Antony Harwood in 2008. She feels very privileged being with authors at the very start of their publishing journey and enjoys close working relationships with all her clients. From editorial help, general advice on the publishing world, guiding careers long-term and general cheerleading, she feels she has the perfect job. Although nothing is off limits and she loves being surprised by submissions. In middle grade children's fiction, Jo is particularly looking for books with heart, epic adventures with voice-led characters, and younger funny fiction with series potential. In adult fiction, page-turning Commercial Women’s and Book Club fiction are right up Jo's street, including psychological suspense, thriller, cosy crime and books that don’t quite fit the mould. Above all, she wants stories that linger long after the final page has been read. Jo is not the right fit for police procedurals. Jo would like you to submit a covering letter, 1 page synopsis and the first 5,000 words of your manuscript in a single word document. (In addition to the paid sessions, Jo is kindly offering one free session for low income/underrepresented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Wednesday 3rd September 2025

LOOKING FOR: YA, NA, ADULT FICTION Helen Lane has been an established agent for several years, formerly with the Booker Albert Agency before joining the Ki Agency. She has a BSc in Environmental Science from the University of East Anglia and a postgrad qualification in Acoustics. She lives in London with her family and the world’s naughtiest cocker spaniel. Helen represents (Adult) Fantasy, Sci Fi, Horror, Romance, Action & Adventure, and Thrillers. She also represents select YA Fantasy, Horror, and Sci Fi. Her tastes do run towards the dark and she is slightly obsessed with monster stories in general (especially if they have giant sharks or squids). And stories set in extreme environments such as the arctic, jungle, caves, ocean, and mountains. But she DOES NOT want to read about affairs or abuse in any genre. (Her husband likes her to add here that this is nothing to do with him, she just doesn’t like sad stories). Her favourite authors are Mira Grant, Greig Beck, James Rollins, Matthew Reilly, Darcy Coates, Andy Weir, Clive Cussler, R F Kuang, Patricia Briggs, and Kelley Armstrong. Her comfort movies are: Jaws, Outbreak, The Cave, Sanctum, Scream, Buffy, Grey's Anatomy, Charmed, Vampire Diaries. You can find her on: Bluesky: @helenlane.bsky.social Instagram: hflane_agenting Helen would like you to submit a covering letter, 1 page synopsis and first three chapters (Max 5,000 words) of your manuscript in a single word document. (In addition to the paid sessions, Helen is kindly offering one free session for low income/under-represented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Wednesday 3rd September 2025

SOLD OUT! 10th September Katie Blagden #Agent121. Looking for: MG, YA, GRAPHIC NOVELS
5.0(3)By I Am In Print
LOOKING FOR: MG, YA, GRAPHIC NOVELS Katie Blagden is a Literary Agent at The Ampersand Agency, representing authors and author-illustrators across various genres and age ranges. She previously worked with Arabella Stein at the Bright Agency, where she helped launch their Literary list. Her notable projects include the Arcana duology by Sam Prentice-Jones (Macmillan US / Hot Key Books) and The River Thief by Hannah Peck (Piccadilly Press). In all areas Katie seeks commercial, plot-driven ideas with a great hook. In adult fiction, Katie specialises in, and is drawn to, Science Fiction, Fantasy, Speculative Fiction, Magical Realism and Horror. She is particularly looking for works that cross genre lines or subvert reader expectations. She loves Babel by R. F. Kuang; Someone You Can Build a Nest In by John Wiswell; Spinning Silver by Naomi Novik; Chain-Gang All-Stars by Nana Kwame Adjei-Brenyah; Rivers of London by Ben Aaronovich; The Long Way to a Small Angry Planet by Becky Chambers; The City We Became by N. K. Jemisin; Legends & Lattes by Travis Baldree; The Rage of Dragons by Evan Winters; Jonathan Strange & Mr Norrel by Susanna Clarke; The Girl With All The Gifts by M. R. Carey; One Last Stop by Casey Mcquiston; Iron Widow by Xiran Jay Zhao; The Lies of Locke Lamora by Scott Lynch; The Night Circus by Erin Morgenstern; The Familiar by Leigh Bardugo; Kindred by Octavia E. Butler; Earthsea by Ursula K. Le Guin; all and anything by Terry Pratchett! Graphic Novels favoured by Katie are across all ages and include the likes of Homebody by Theo Parish; Lore Olympus by Rachel Smythe; Lumber Janes by N. D. Stevens et al; On A Sunbeam by Tillie Walden; Through The Woods by Emma Carrol; The Magic Fish by Trung Le Nguyen; Heartstopper by Alice Oseman; El Deafo by Cece Bell; Roller Girls by Victoria Jamieson; Skyward by Joe Henderson and Lee Garbett; Faith by Jody Houser. For Graphic Novels, Katie is currently only considering Author-Illustrators (or Author/Illustrator pairings). In children’s, Katie specialises in Middle Grade, YA and Crossover Fiction, She is looking for fast, funny and action-packed Middle Grade. In YA, she is drawn to grounded or contemporary SFF, queer stories and fairytale or folktale inspired works. Examples of books in this area Katie loves are All That's Left in the World by Erik J Brown; The Knife of Never Letting Go by Patrick Ness; Cemetery Boys by Aiden Thomas; Children of Blood and Bone by Tomi Adeyemi; The Deathless Girls by Kiran Millwood Hargrave; Holes by Louis Sachar; Six of Crows by Leigh Bardugo; Gone by Michael Grant; His Dark Materials by Philip Pullman; Impossible Creatures by Katherine Rundell; The Dark Lady by Akala; Percy Jackson by Rick Riordan; The Dark Is Rising by Susan Cooper; Artemis Fowl by Eoin Colfer. Katie is an advocate for centring traditionally underrepresented voices, and actively works to discover and develop authors and author-illustrators from diverse backgrounds. Katie’s previous experience includes marketing, bookselling and advertising. She also appeared as a contributor on the Graham Norton Book Club for Audible for all six seasons. When she’s not reading, you can find Katie playing Dungeons & Dragons, trying a new crafty hobby (before abandoning it for something new), or spoiling her dog Poe. Katie would like you to submit a covering letter, one page synopsis and the first three chapters (Max 5000 words) of your completed manuscript in a single word document. (In addition to the paid sessions, Katie is kindly offering one free session for low income/under-represented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Wednesday 3rd September 2025

11th September Emily MacDonald #Agent121. Looking for: ADULT FICTION, NON-FICTION
5.0(3)By I Am In Print
LOOKING FOR: ADULT FICTION, NON-FICTION Emily MacDonald joined 42 management and production company in 2019, working with Eugenie Furniss across her clients. She is now an agent in the Books Department, and is building her own list. Send Emily a story with characters that just won't leave her and a narrative that pulls her in, keeping her immersed in the world well after she has finished reading. She reads across a wide-range and has a particular interest in: book club, high-concept crime/thriller, upmarket and literary fiction. In fiction, Emily would love to find a crime/thriller set within a subcult: a modern retelling of British folklore (think Kamila Shamsie’s Home Fire); an unconventional love story; and a character led journey of self-discovery (especially one set within a diasporic community). Emily is also looking for narrative non-fiction which immerses the reader into an untold true story (personal or historical), exploring a new point of view, and providing a compelling social commentary, with an investigative twist. Think the obsessive vein of Kirk W. Johnson or personal/political dispatches of Aidan Hartley. Emily wants her horizons to expand while she reads. In both fiction and non-fiction, Emily loves stories woven into their surroundings, where the setting is as central a character as those who drive the narrative. In both spheres, she is keen to hear from Scottish and regional voices with stories to tell. Please note, Emily is not currently accepting submissions for Children's lit/YA and SFF. Emily would like you to submit a covering letter, 1 - 2 page synopsis and the first 5,000 words of your manuscript in a single word document. (In addition to the paid sessions, Emily is kindly offering one free session for low income/under-represented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Thursday 4th September 2025

TWO SPACES LEFT! 12th September Saskia Leach #Agent121. Looking for: ADULT FICTION, YA THRILLER
5.0(3)By I Am In Print
LOOKING FOR: ADULT FICTION, YA THRILLER Saskia Leach is a Junior Literary Agent at Kate Nash Literary Agency, where she has been working since 2021. She loves stories that features complex and dynamic characters and is fascinated by books containing document inserts or written from multiple perspectives. Saskia represents fiction for adults and young adults in the genres of crime, thriller, romance, historical/saga, horror, speculative and bookclub. She does not represent literary fiction, sci-fi, fantasy, non-fiction, action/adventure thrillers, non-fiction, picture books or chapter books for children younger than middle grade. Saskia is particularly looking for LGBTQIA+ romance, high concept psychological thriller with a unique hook or set in an unusual location, and bookclub fiction revolving around a moral dilemma - but she is open to reading submissions in all genres she represents. She is keen to hear from writers from underrepresented voices and perspectives. Saskia would like you to submit a covering letter, 1 page synopsis and the first 5,000 words of your manuscript in a single word document. (In addition to the paid sessions, Saskia is kindly offering one free session for low income/under-represented writers. Please email agent121@iaminprint.co.uk to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice given in your Agent121. The submission deadline is: Friday 5th September 2025 at 12 noon UK BST
