- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
503 Policy courses in Leeds delivered Live Online
F5 Configuring BIG-IP APM - Access Policy Manager v13.x
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is intended for network administrators, operators, and engineers responsible for managing the normal day-to-day operation and administration of BIG-IP Access Policy Manager Overview This course provides the skills to create and manage BIG-IP APM system. This course covers three typical deployment scenarios for BIG-IP Access Policy Manager (APM) and is broken into three individual lessons. In lesson one, you learn how to configure BIG-IP APM to provide Active Directory-based authentication for a load-balanced pool of web servers. In lesson two, you learn how to create a policy that provides an SSL VPN (Network Access) resource to users, but only when they log into BIG-IP APM using a corporate-issued PC. Finally, lesson three builds on the first two lessons to create a policy that provides a dynamic landing page with both SSL VPN as well as an OWA (Portal Access) resource, but only to users with special authorization. Setting Up the BIG-IP System Introducing the BIG-IP System Initially Setting Up the BIG-IP System Archiving the BIG-IP Configuration Leveraging F5 Support Resources and Tools Configuring Web Application Access Review of BIG-IP LTM Introduction to the Access Policy Web Access Application Configuration Overview Web Application Access Configuration in Detail Exploring the Access Policy Navigating the Access Policy Managing BIG-IP APM BIG-IP APM Sessions and Access Licenses Session Variables and sessiondump Session Cookies Access Policy General Purpose Agents List Using Authentication Introduction to Access Policy Authentication Active Directory AAA Server RADIUS One-Time Password Local User Database Understanding Assignment Agents List of Assignment Agents Configuring Portal Access Introduction to Portal Access Portal Access Configuration Overview Portal Access Configuration Portal Access in Action Configuring Network Access Concurrent User Licensing VPN Concepts Network Access Configuration Overview Network Access Configuration Network Access in Action Deploying Macros Access Policy Macros Configuring Macros An Access Policy is a Flowchart Access Policy Logon Agents Configuring Logon Agents Exploring Client-Side Checks Client-Side Endpoint Security Exploring Server-Side Checks Server-Side Endpoint Security Agents List Server-Side and Client-Side Checks Differences Using Authorization Active Directory Query Active Directory Nested Groups Configuration in Detail Configuring AppTunnels Application Access Remote Desktop Network Access Optimized Tunnels Landing Page Bookmarks Deploying Access Control Lists Introduction to Access Control Lists Configuration Overview Dynamic ACLs Portal Access ACLs Signing On with SSO Remote Desktop Single Sign-On Portal Access Single Sign-On Using iRules iRules Introduction Basic TCL Syntax iRules and Advanced Access Policy Rules Customizing BIG-IP APM Customization Overview BIG-IP Edge Client Advanced Edit Mode Customization Landing Page Sections Deploying SAML SAML Conceptual Overview SAML Configuration Overview Exploring Webtops and Wizards Webtops Wizards Using BIG-IP Edge Client BIG-IP Edge Client for Windows Installation BIG-IP Edge Client in Action Lesson Configuration Project Additional Training and Certification Getting Started Series Web-Based Training F5 Instructor Led Training Curriculum F5 Professional Certification Program F5 Instructor Led Training Curriculum F5 Professional Certification Program Additional course details: Nexus Humans F5 Configuring BIG-IP APM - Access Policy Manager v13.x training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the F5 Configuring BIG-IP APM - Access Policy Manager v13.x course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

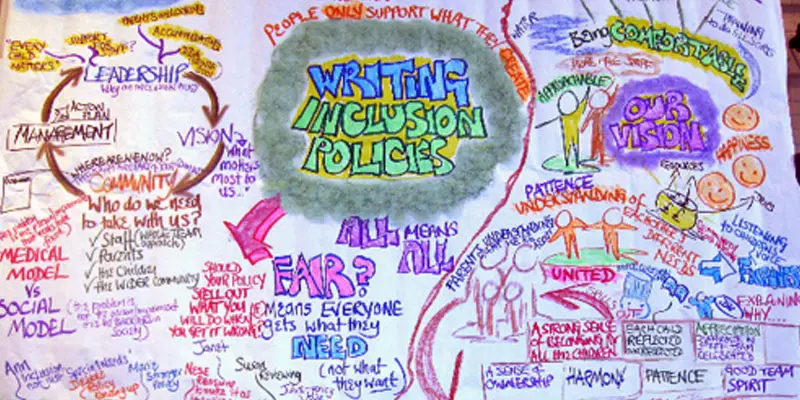
INCLUSION POLICIES
By Inclusive Solutions
This day is relevant to anyone involved in the task of developing an Inclusion Policy. How to create a real policy built around shared vision with true community commitment. Participate in this very practical workshop to take your first very real steps forward. The day gives those present opportunities to reflect on their attitudes and practice in relation to the inclusion of pupils who are different and the policy and practice which currently exist. Course Category Strategic Work Description This day is relevant to anyone involved in the task of developing an Inclusion Policy. How to create a real policy built around shared vision with true community commitment. Participate in this very practical workshop to take your first very real steps forward. The day gives those present opportunities to reflect on their attitudes and practice in relation to the inclusion of pupils who are different and the policy and practice which currently exist. Testimonials Be the first… Learning Objectives Increased confidence regarding developing an inclusion policy Understanding of essential steps to be taken to make inclusion policy a reality Deeper understanding of core values surrounding inclusion of disabled children Who Is It For? Anyone needing to create an inclusion policy Course Content The course answers the questions: Why an inclusion policy? What is the scope of an inclusion policy? How can an inclusion policy become a reality? How do I roll this out? We will cover: Legal and ethical background Local requirements Vision and Values Aims and Objectives Scope Evaluation and monitoring Complaints procedures Community involvement Consultation Implementation Practical steps If you like this you may like: KEYS TO INCLUSION
Advanced Junos Security training course description This course provides students with intermediate routing knowledge and configuration examples. The course includes an overview of protocol-independent routing features, load balancing and filter-based forwarding, OSPF, BGP, IP tunneling, and high availability (HA) features. Junos Intermediate Routing (JIR) is an intermediate-level course. What will you learn Demonstrate the understanding of integrated user firewall. Implement next generation Layer 2 security features. Implement virtual routing instances in a security setting. Utilize Junos tools for troubleshooting Junos security implementations. Implement IPS policy. Advanced Junos Security training course details Who will benefit: Individuals responsible for implementing, monitoring, and troubleshooting Junos security components. Prerequisites: Intro to the Junos Operating System Duration 5 days Advanced Junos Security training course contents Junos Layer 2 Packet Handling and Security Features Transparent Mode Security Secure Wire Layer 2 Next Generation Ethernet Switching MACsec Lab 2 Implementing Layer 2 Security Virtualization Virtualization Overview Routing Instances Logical Systems Lab 3 Implementing Junos Virtual Routing AppSecure Theory AppSecure Overview AppID Overview AppID Techniques Application System Cache Custom Application Signatures AppSecure Implementation AppTrack AppFW AppQoS APBR SSL Proxy Lab 4 Implementing AppSecure Working with Log Director Log Director Overview Log Director Components Installing and setting up Log Director Clustering with the Log Concentrator VM Administrating Log Director Lab 5 Deploying Log Director Sky ATP Theory Sky ATP Overview Monitoring Sky ATP Analysis and Detection of Malware Sky ATP Implementation Configuring Sky ATP Installing Sky ATP Analysis and detection of Malware Infected Host Case Study Lab 6 Instructor Led Sky ATP Demo Implementing UTM UTM Overview AntiSpam AntiVirus Content and Web Filtering Lab 7 Implementing UTM Introduction to IPS IPS Overview Network Asset Protection Intrusion Attack Methods Intrusion Prevention Systems IPS Inspection Walkthrough IPS Policy and Configuration SRX IPS Requirements IPS Operation Modes Basic IPS Policy Review IPS Rulebase Operations Lab 8 Implementing Basic IPS Policy SDSN SDSN Overview, Components & Configuration Policy Enforcer Troubleshooting SDSN Use Cases Lab 9 Implementing SDSN Enforcement, Monitoring, and Reporting User Role Firewall and Integrated User Firewall Overview User Role Firewall Implementation Monitoring User Role Firewall Integrated User Firewall Implementation Monitoring Integrated User Firewall Lab 10 Configure User Role Firewall and Integrated User Firewall Troubleshooting Junos Security Troubleshooting Methodology Troubleshooting Tools Identifying IPsec Issues Lab 11 Performing Security Troubleshooting Techniques Appendix A: SRX Series Hardware and Interfaces Branch SRX Platform Overview High End SRX Platform Overview SRX Traffic Flow and Distribution SRX Interfaces

Completing Client and Matter Risk Assessments Course
By DG Legal
Despite being a requirement under the Money Laundering Regulations 2017 (MLR 2017), in 2023/24 the SRA found that 19% of files reviewed did not contain a client and matter risk assessment (CMRA), with a further 12% of files containing ineffective CMRAs. At best, the firms conducting these files were putting themselves at risk of regulatory action for failure to comply with the MLR 2017. More seriously, firms may have been facilitating money laundering through their failure to adequately assess and address the risks posed by clients and matters. The SRA has issued a number of significant fines to firms with no, or insufficient, CMRAs in place. In the year August 2024 to July 2025, firms were fined over £950,000 where ineffective or missing CMRAs were noted. Although a firm’s MLRO, MLCO or its managers bear ultimate responsibility for ensuring its compliance with the MLR 2017, it is the responsibility of all those working on behalf of the firm to conduct and document the appropriate processes and checks on a day-to-day basis. Therefore, it is imperative that all staff understand not only how to complete a CMRA, but also the importance of doing so thoroughly and correctly. This course will assist fee earners and support staff in confidently and competently completing client and matter risk assessments, understanding the types of risks to be identified and the importance of correctly identifying these. Where the SRA has found failings at firms in respect of CMRAs, it has almost unanimously also found shortcomings in other areas of AML compliance. Where concerns are raised regarding a firm’s compliance with any aspect of the MLR 2017, the SRA will probe further and look into all areas of AML compliance. For information about DG Legal’s full range of AML training courses, please visit https://dglegal.co.uk/training/upcoming-premier-training-courses/. Target Audience This online course is suitable for staff of all levels, from support staff to senior partners. Resources Comprehensive and up to date course notes will be provided to all delegates which may be useful for ongoing reference or cascade training. Please note a recording of the course will not be made available. Speaker Paul Wightman, Consultant, DG Legal A qualified barrister, Paul graduated in Law from Birmingham University and was called to the Bar in 1994. He subsequently spent almost 20 years working for the Law Society of England and Wales, initially within the Office for the Supervision of Solicitors, then the Legal Complaints Service (LCS), and ultimately the Solicitors Regulation Authority (SRA). Paul is adept at undertaking audits and providing succinct reports on areas for improvement and can assist firms with advice on all aspects of SRA compliance and Anti-Money Laundering procedures.
55344 Identity with Windows Server
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is primarily intended for existing IT professionals who have some AD DS knowledge and experience and who aim to develop knowledge about identity and access technologies in Windows Server. This would typically include: ?AD DS administrators who are looking to train in identity and access technologies with Windows Server 2016, Windows Server 2019 or Windows Server 2022. ?System or infrastructure administrators with general AD DS experience and knowledge who are looking to cross-train in core and advanced identity and access technologies in Windows Server 2016, Windows Server 2019 or Windows Server 2022. Overview Install and configure domain controllers. Manage objects in AD DS by using graphical tools and Windows PowerShell. Implement AD DS in complex environments. Implement and administer Active Directory Rights Management Services (AD RMS). Implement AD DS sites, and configure and manage replication. Implement and manage Group Policy Objects (GPOs). Manage user settings by using GPOs. Secure AD DS and user accounts. Implement and manage a certificate authority (CA) hierarchy with AD CS. Deploy and manage certificates. Implement and administer AD FS. Implement synchronization between AD DS and Azure AD. Some exposure to and experience with Active Directory concepts and technologies in Windows Server. Experience working with and configuring Windows Server. Experience and an understanding of core networking technologies such as IP addressing, name resolution, and Dynamic Host Configuration Protocol (DHCP) Experience working with and an understanding basic server virtualization concepts. Monitor, troubleshoot, and establish business continuity for AD DS services. This five-day instructor-led course teaches IT professionals how to deploy and configure Active Directory Domain Services (AD DS) in a distributed environment, how to implement Group Policy, how to perform backup and restore, and how to monitor and troubleshoot Active Directory - related issues with Windows Server. Additionally, this course teaches students how to deploy other Active Directory server roles, such as Active Directory Federation Services (AD FS) and Active Directory Certificate Services (AD CS). Although this course and the associated labs are written for Windows Server 2022, the skills taught will also be backwards compatible for Server 2016 and Server 2019. The course and labs also focus on how to administer Windows Server using not only the traditional tools such as PowerShell and Server manager, but also Windows Admin Center. Prerequisites Some exposure to and experience with Active Directory concepts and technologies in Windows Server. Experience working with and configuring Windows Server. Experience and an understanding of core networking technologies such as IP addressing, name resolution, and Dynamic Host Configuration Protocol (DHCP) Experience working with and an understanding basic server virtualization concepts. 1 - Installing and configuring domain controllers Overview of AD DS Overview of AD DS domain controllers Deploying a domain controller 2 - Managing objects in AD DS Managing user accounts Managing groups in AD DS Managing computer objects in AD DS Using Windows PowerShell for AD DS administration Implementing and managing OUs 3 - Advanced AD DS infrastructure management Overview of advanced AD DS deployments Deploying a distributed AD DS environment Configuring AD DS trusts 4 - Implementing and administering AD DS sites and replication Overview of AD DS replication Configuring AD DS sites Configuring and monitoring AD DS replication 5 - Implementing Group Policy Introducing Group Policy Implementing and administering GPOs Group Policy scope and Group Policy processing Troubleshooting the application of GPOs 6 - Managing user settings with Group Policy Implementing administrative templates Configuring Folder Redirection, software installation, and scripts Configuring Group Policy preferences 7 - Securing Active Directory Domain Services Securing domain controllers Implementing account security Implementing audit authentication Configuring managed service accounts 8 - Deploying and managing AD CS Deploying CAs Administering CAs Troubleshooting and maintaining CAs 9 - Deploying and managing certificates Deploying and managing certificate templates Managing certificate deployment, revocation, and recovery Using certificates in a business environment Implementing and managing smart cards 10 - Implementing and administering AD FS Overview of AD FS AD FS requirements and planning Deploying and configuring AD FS Web Application Proxy Overview 11 - Implementing and administering AD RMS Overview of AD RMS Deploying and managing an AD RMS infrastructure Configuring AD RMS content protection 12 - Implementing AD DS synchronization with Microsoft Azure AD Planning and preparing for directory synchronization Implementing directory synchronization by using Azure AD Connect Managing identities with directory synchronization 13 - Monitoring, managing, and recovering AD DS Monitoring AD DS Managing the Active Directory database Active Directory backup and recovery options for AD DS and other identity and access solutions

Source of Funds and Source of Wealth Checks Course
By DG Legal
Source of funds and source of wealth are two important verification steps a firm can take to identify potential money laundering activities or other financial crime. The Money Laundering Regulations 2017 (MLR 2017) require firms, where necessary, to scrutinise the source of funds of a transaction to ensure they are consistent with their knowledge of the customer, their business and risk profile. In addition, where a matter is considered to be higher risk and therefore subject to enhanced due diligence, firms must also investigate the client’s overall source of wealth. Law firm staff must be able to differentiate between source of funds and source of wealth, having knowledge of how to verify each and identify any anomalies that do not align with their understanding of the client or the matter. Staff must have the knowledge and confidence to challenge clients and seek further clarification where the source may be unclear or highlight concerns. A number of firms who failed to sufficiently identify the source of funds and/or source of wealth have recently been fined by the SRA. In the year August 2024 to July 2025, fines in excess of £475,000 were recorded for AML breaches that included source of funds and source of wealth failings. This course will assist fee earners and support staff in understanding the difference between source of funds and source of wealth, enabling them to capably identify and verify funds in a matter. Where the SRA has found failings at firms in respect of source of funds or source of wealth, it has almost unanimously also found shortcomings in other areas of AML compliance. Where concerns are raised regarding a firm’s compliance with any aspect of the MLR 2017, the SRA will probe further and look into all areas of AML compliance. For information about DG Legal’s full range of AML training courses, please visit: https://dglegal.co.uk/training/upcoming-premier-training-courses/. Target Audience This online course is suitable for staff of all levels, from support staff to senior partners. Resources Comprehensive and up to date course notes will be provided to all delegates which may be useful for ongoing reference or cascade training. Please note a recording of the course will not be made available. Speaker Paul Wightman, Consultant, DG Legal A qualified barrister, Paul graduated in Law from Birmingham University and was called to the Bar in 1994. He subsequently spent almost 20 years working for the Law Society of England and Wales, initially within the Office for the Supervision of Solicitors, then the Legal Complaints Service (LCS), and ultimately the Solicitors Regulation Authority (SRA). Paul is adept at undertaking audits and providing succinct reports on areas for improvement and can assist firms with advice on all aspects of SRA compliance and Anti-Money Laundering procedures.

ADV-SDWAN-CT - Advanced Cisco SD-WAN Routing, Templates, Policy Configure, and Tshoot
By Nexus Human
Duration 5 Days 30 CPD hours Overview SDWAN Review Advanced Template Design and Troubleshooting Advanced Security Policies on vEdge and IOS-XE Platforms Advanced Local Policies on vEdge and IOS-XE Platforms Advanced Central Policies on vEdge and IOS-XE Platforms Advanced Troubleshooting of Policies on vEdge and IOS-XE Platforms In this Advanced Lab focused SDWAN Course, Students willExplore and Troubleshoot the initials environmentLearn Advanced Techniques to Deploy Templates with the theme of reusabilityDeploy and Troubleshoot Transport BridgingDeploy and Troubleshoot Routing including OSPF, BGP, EIGRPDeploy and Troubleshoot Multicast RoutingDesign, Configure, and Troubleshoot Advanced Security PoliciesDesign, Configure, and Troubleshoot Local PoliciesDesign, Configure, and Troubleshoot Application Aware RoutingDesign, Configure, and Troubleshoot Quality of ServiceDesign, Configure, and Troubleshoot Central Policies Including Hub Spoke, Full Mesh and Custom TopologiesDesign, Configure, and Troubleshoot Central Policies Including Service ChainingDesign, Configure, and Troubleshoot Central Policies Including Traffic Rules & CFLOW Cisco SD-WAN Overview Dashboard SD-WAN Architecture SD-WAN WAN Edges SD-WAN Controllers SD-WAN Fabric SD-WAN Advanced Settings Advanced Controller Settings Overlay and vEdge Recommended Settings Forward Error Correction (FEC) Packet Duplication System IP Design LTE Operation SD-WAN High Availability Controller High Availability Controller Scalability Active vManage, Backup Inactive vManage Clustering vManages Disaster Recovery SD-WAN Templates Template Overview Future Templates Device template using Future Templates Device template using CLI Templates Designing templates for Reusability Attaching Devices to Templates Bridging Transparent Bridging Bridging Template Configuration cEdge Bridging Template Configuration vEdge Bridging Template Configuration Monitoring Bridging Routing Protocols Static Routes Dynamic Routing Protocols Multicast Multicast Terms Requirements vEdge Multicast Support cEdge Multicast Support Multicast RPs Multicast Replicators PIM IGMP Network Optimization Optimization Overview TCP Optimization vEdge Optimization Requirements vEdge Optimization Implementation cEdge (IOS-XE) Optimization Requirements cEdge (IOS-XE) Optimization Implementation AppNAV Per Tunnel QoS Direct Internet Access (DIA) Overview SD-WAN Direct Internet Access (DIA) SD-WAN DIA Requirements SD-WAN Direct Internet Access Use Cases SD-WAN Direct Internet Access Design Components SD-WAN Direct Internet Access Design Considerations SD-WAN Direct Internet Access Failover Scenarios Cisco SD-WAN Direct Internet Access Monitoring Unified Communications Voice Integration in SD-WAN Voice Feature Templates Voice Policies IOS-XE UC Device Template SD-WAN Security Policy Authentication/Encryption/Integrity Firewall IPS (Snort) URL Filtering Web Layer Security Pairwise IPsec Keys SD-WAN Local Policy Policy Configuration Overview Policy Framework-Localized Policies Local Control Policy Local Control (Route) Policy Localized Control Policy Configuration Local Data Policy Configure Localized Data Policy for IPv4 SD-WAN Central Policy Policy Creation and Management Guidelines Centralized Data Policies Application Aware Routing Service Chaining Traffic Flow Monitoring with Cflowd Policy Construction Platform Support and Scalability SDWAN Migration Sequence of Migration Migration Planning DC/Hub Site Migration Branch/Spoke Site Migration Additional course details: Nexus Humans ADV-SDWAN-CT - Advanced Cisco SD-WAN Routing, Templates, Policy Configure, and Tshoot training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the ADV-SDWAN-CT - Advanced Cisco SD-WAN Routing, Templates, Policy Configure, and Tshoot course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Junos Operating System training course description This course provides students with the foundational knowledge required to work with the Junos OS and to configure Junos devices. The course provides a brief overview of the Junos device families and discusses the key architectural components of the software. The course then delves into foundational routing knowledge and configuration examples including general routing concepts, routing policy, and firewall filters. Delegates will gain experience in configuring and monitoring the Junos OS and monitoring basic device operations. This course is based on Junos OS Release 15.1X49. What will you learn Describe the design architecture of the Junos OS. Navigate within the Junos CLI and perform tasks within the CLI operational and configuration modes. Configure and monitor network interfaces. Navigate within the Junos J-Web interface. Identify where you might use firewall filters. Explain basic routing operations and concepts. Identify key factors in Juniper Networks' security. Junos Operating System training course details Who will benefit: This course benefits individuals responsible for configuring and monitoring devices running the Junos OS. Prerequisites: TCP/IP foundation for engineers Duration 3 days Junos Operating System training course contents Junos Operating System Fundamentals The Junos OS Traffic Processing Overview of Junos Devices User Interface Options-The Junos CLI User Interface Options The Junos CLI: CLI Basics The Junos CLI: Operational Mode The Junos CLI: Configuration Mode User Interface Options-The J-Web Interface The J-Web GUI Configuration Lab 1: User Interface Options Initial Configuration Factory-Default Configuration Initial Configuration Interface Configuration Lab 2: Initial System Configuration Secondary System Configuration User Configuration and Authentication System Logging and Tracing Network Time Protocol Archiving Configurations SNMP Lab 3: Secondary System Configuration Operational Monitoring and Maintenance Monitoring Platform and Interface Operation Network Utilities Maintaining the Junos OS Password Recovery System Clean-Up Lab 4: Operational Monitoring and Maintenance Interface Configuration Examples Review of the Interface Configuration Hierarchy Interface Configuration Examples Using Configuration Groups Routing Fundamentals Routing Concepts: Overview of Routing Routing Concepts: The Routing Table Routing Concepts: Routing Instances Static Routing Dynamic Routing Lab 5: Routing Fundamentals Routing Policy Routing Policy Overview Case Study: Routing Policy Lab 6: Routing Policy Firewall Filters Firewall Filters Overview Case Study: Firewall Filters Unicast Reverse-Path-Forwarding Checks Lab 7: Firewall Filters Class of Service CoS Overview Traffic Classification Traffic Queueing Traffic Scheduling Case Study: CoS Lab 8: Class of Service JTAC Procedures Opening a Support Case Customer Support Tools Transferring Files to JTAC Juniper Security Concepts Security Challenges Juniper's Security Focus Appendix A: IPv6 Fundamentals IPv6 Addressing Protocols and Services Configuration


